Schooled - [HTB]
![Cover Image for Schooled - [HTB]](/assets/images/blog/Schooled-htb/Schooled.png)

Introduction
Shcooled is a hard-medium linux machine from HackTheBox where the attacker will have to exploit several moodle vulnerabilities in order to obtain a reverse shell. Then, will have to crack the passwords stored in the moodle database in order to obtain the user flag. Finally, the attacker will have to craft a malign pkg package triggering a reverse shell during its installation.
Enumeration
As always, let's start finding all opened ports available in the machine with nmap.
Then, we continue gathering more information of each opened ports.
Because we need credentials for the mysql and ssh server, we should start looking at the web server.
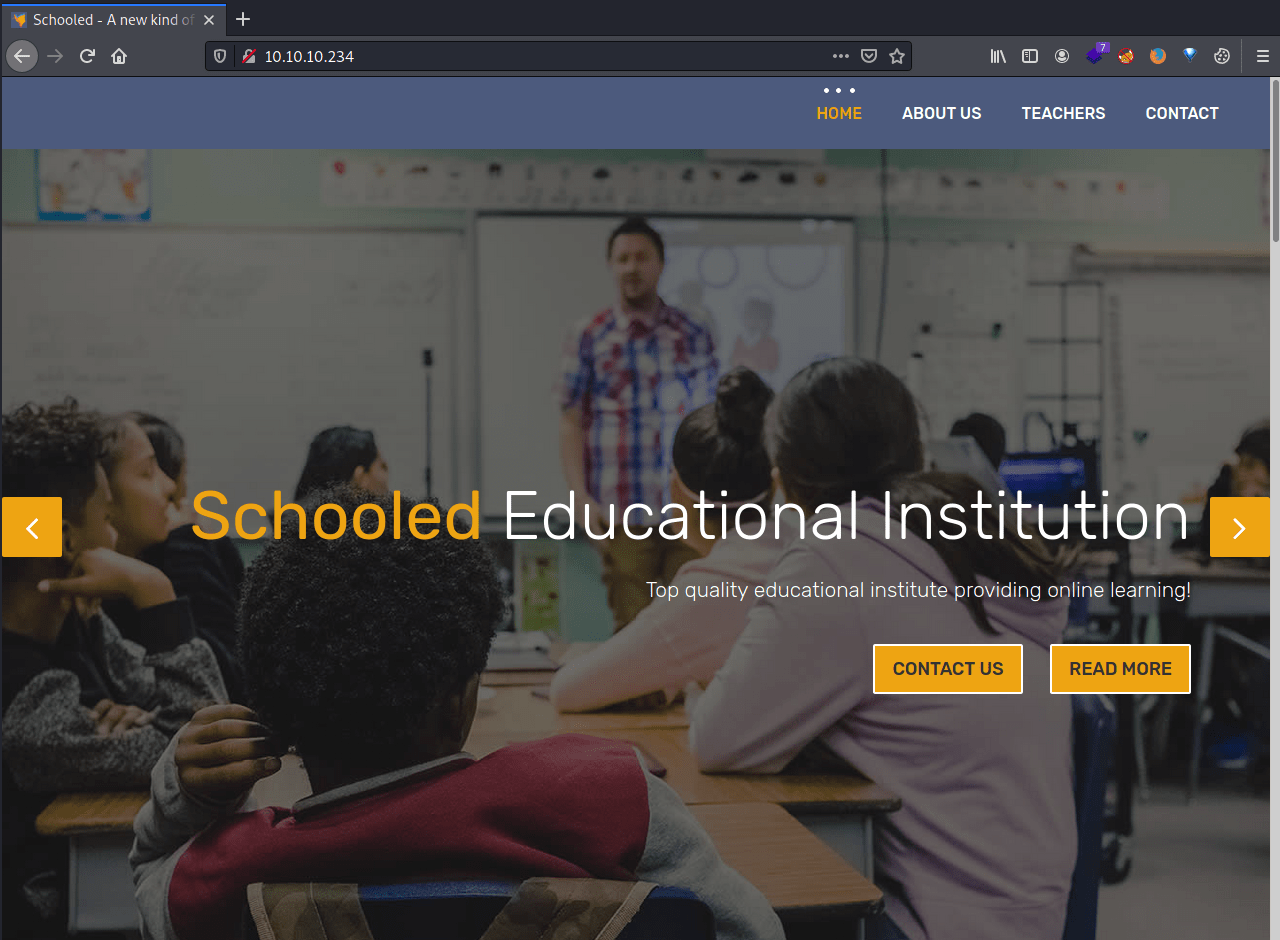
In the contact information we see the domain schooled.htb.
Because using the domain doesn't provide anything useful, let's find some sub-domains with ffuz
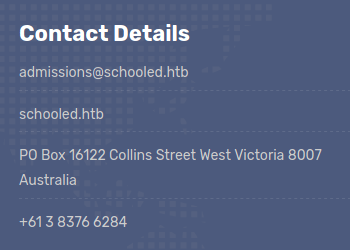
ffuf provide us a new sub-domain moodle.schooled.htb, that once added to our /etc/hosts file, we can get access to the moodle platform.
After creating an account in the moodle we can see that there are several courses available.
After digging between all the courses there is an announcement by Manuel Phillips in the mathematics course that seems like a hint for what we have to do.
Exploit 1
The field MoodleNet can be found editing our profile. Furthermore, it seems vulnerable to stored xss. Hence, we can retrieve the Manuel Philips' session cookie, by saving the following code into the MoodleNet field of our profile.
Note: Do not forget to change your IP address
After saving the changes we need to create a simple HTTP server so we can retrieve the cookie. After a couple of seconds, we retrieve the Manuel Phillips' cookie.
Exploit 2
Once, replaced our cookie with Manuel's we will become a teacher in the Maths course. Then, after searching on google appears to be an exploit (CVE-2020-14321) that uses the role teacher to upgrade privileges, obtaining the role Manager.
Note: You must do it pretty quickly, because the roles are reset after a while. So read these steps carefully before trying to exploit it.
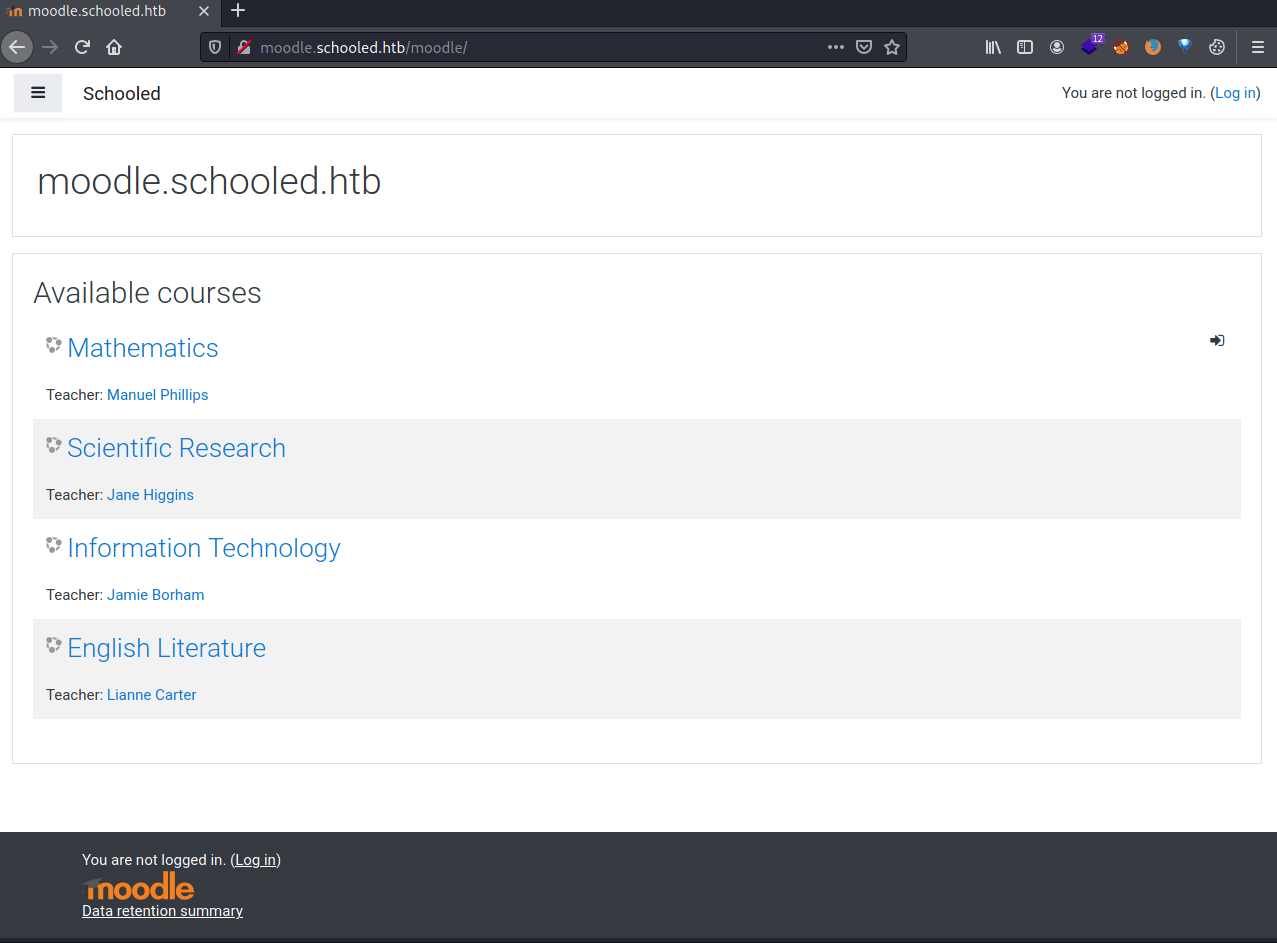
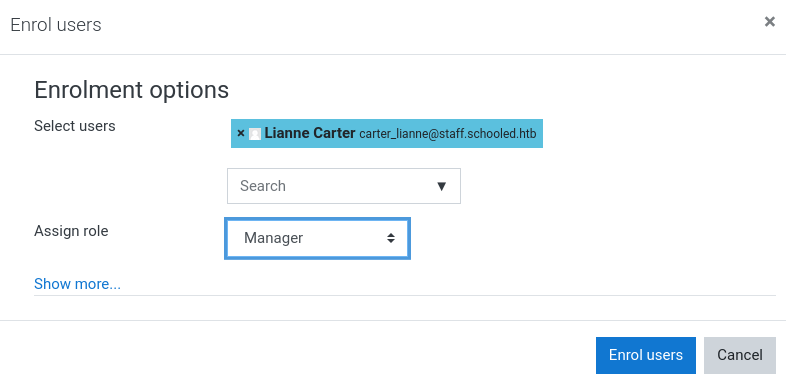
In order to do so, we need to enrol a user into the Maths course and intercept the request with Burpsuite.
Once in burpsuite, we must modify the parameter serlist%5B%5D=28 , changing its value to 24 (Manuel's id) and the parameter roletoassign=5 to 1 (Manager role).
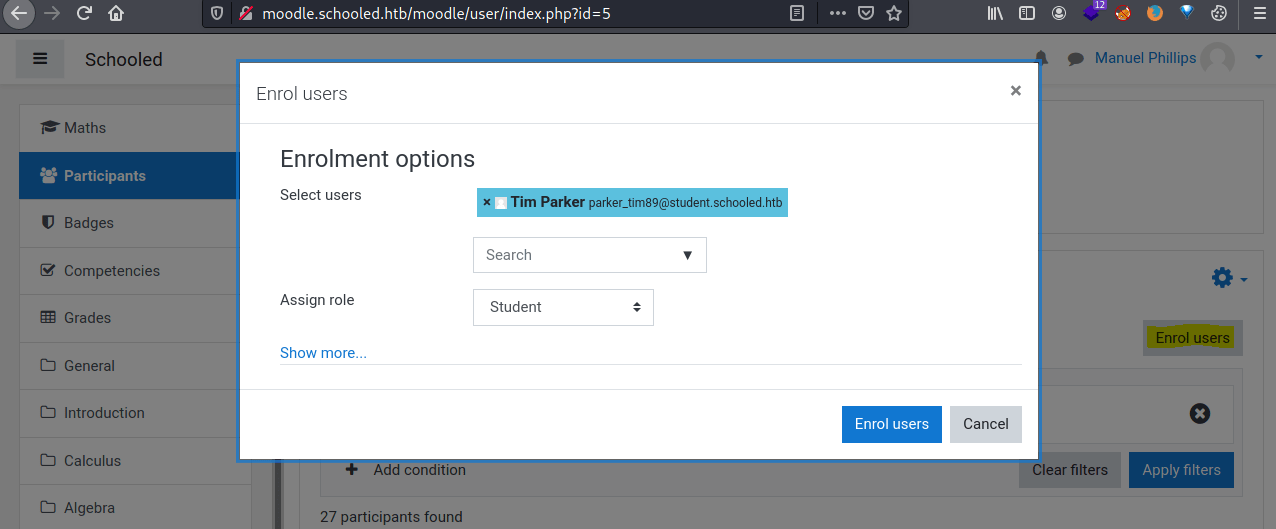
Now, we need to add Lianne Carter (The administrator of this moodle platform) as Manager of the Mathematics course, so we can login as her later on.
For doing so, we only have to enrol him selecting the Manager role.
Then, going to the Manuel Phillips profile for the mathematics course, we need to click in the Manager link
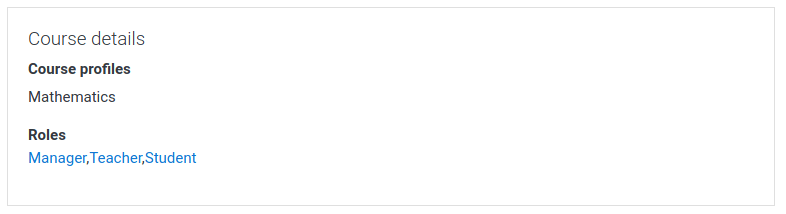
Then we need to click on Lianne Carter.
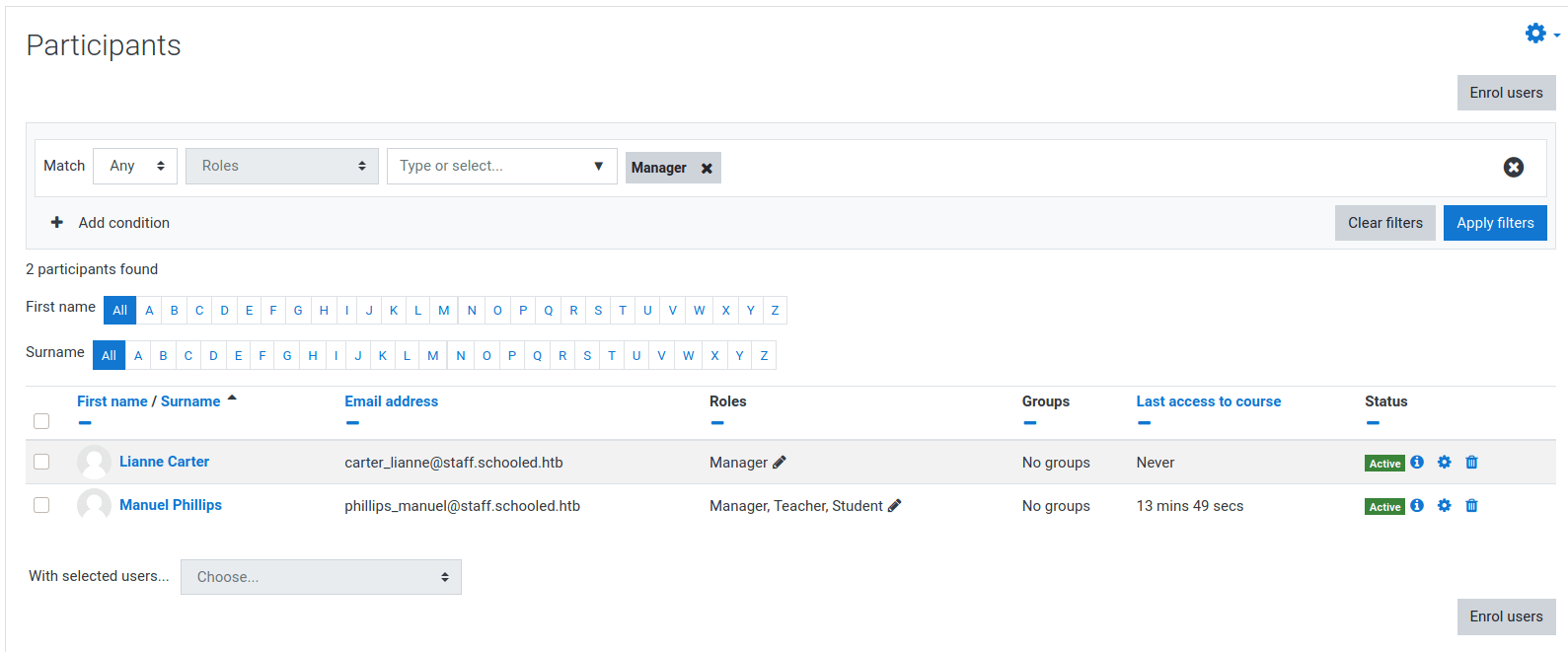
Then, clicking on "Log in as" we are able to login as him.
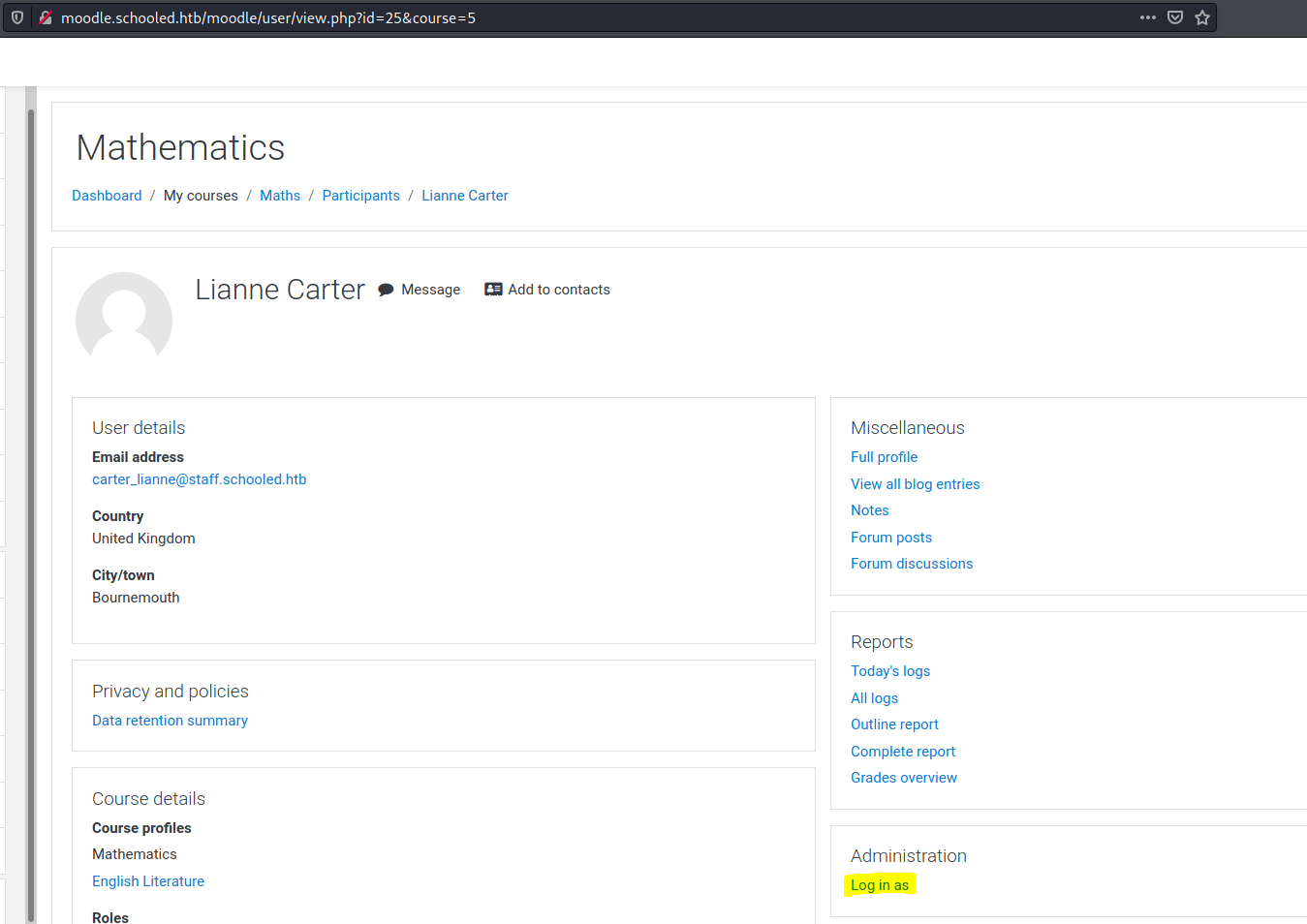
After that, we need to modify the Manager role permissions in order to be able to install a new plugin.
First, we need to access to Site administration/Users/Define Roles/Manager/Edit. Then, we intercept with burpsuite the request produced by clicking on "Save changes", editing the request as the following link (Do not replace the sseskey variable).
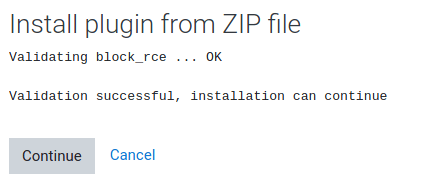
Now we can install a moodle plugin. The following plugin provide us with an RCE in the moodle web page. Once installed you will see the banner telling you, that it has been installed correctly.
Now you can execute commands through this link.
If you want a reverse shell, use this link, changing the IP and port.
Privilege escalation 1
Once obtained our reverse shell, we are user www, so we need to escalate privileges. In order to do so, we need some credentials for the moodle database, which are stored in the config.php file.
Now, with the database credentials in our hands we can extract the credentials from every registered user in the moodle platform.
All the passwords has been hashed using Blowfish, which is a very time consuming hash function.
Hence, we are going to focus on the admin's hash.
Trying the password !QAZ2wsx with the users in the system jamie and steve we discovered that we can get access through SSH as jamie.
Privilege escalation 2
The user jamie can install FreeBSD packages. So as we did with the machine Armageddon, we are going to use the installation hooks in order to obtain a reverse shell as root.
In order to create the package I followed this post. But here you have the modified script adding the execution of a reverse shell.
Note: Do not forget to change the IP and port.
Now we need to execute the script in the FreeBSD machine.
pkg by default checks the online FreeBSD repository catalogue before installing any package, it hangs until it updates the catalogue.
Hence, we need to add the flag --no-repo-update so it doesn't update the catalogue.
Now, the installation will hang, but it is due to our a reverse shell as root, getting the root flag.