Armageddon - [HTB]
![Cover Image for Armageddon - [HTB]](/assets/images/blog/Armageddon-htb/Armageddon.PNG)

Introduction
Armageddon is a CentOs easy machine from HackTheBox where you will have to exploit a famous vulnerable CMS. Then, will have to crack a credential stored in the CMS database to become brucetherealadmin. Finally, you will have to install a trojan snap package in order to trigger the snap install hook, obtaining a new account with root privileges.
Enumeration
As always let's begin looking for every opened port in the machine with nmap.
There are just two available services (SSH and HTTP) a deeper scan may provide more information.
AS we can see there is a robots.txt file composed of several not indexed URLs. Nonetheless, this will not help us at all in order to exploit the machine.
The web page seems pretty simple and there is nothing but a login pane.
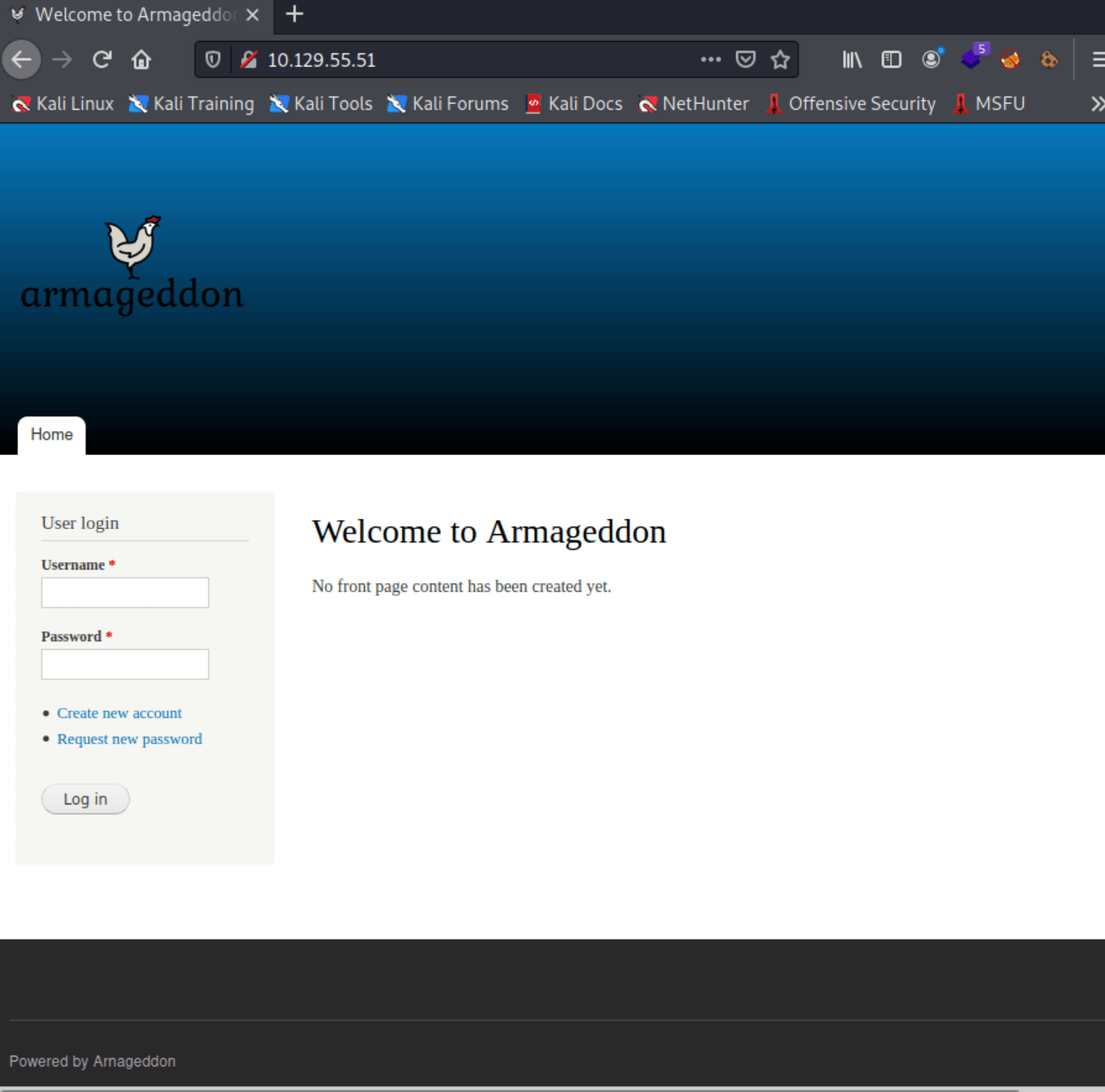
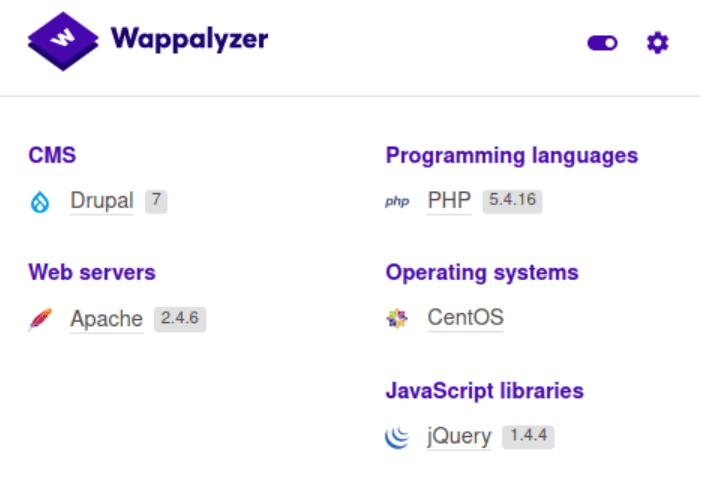
Looking at its technology we can see that uses Drupal 7 as CMS.
Explotation
This CMS has an associated exploit named Drupalgeddon, pretty similar to the machine name.
Using the exploit we can retrieve a shell as apache.
Note: If you can not execute the script, maybe is due to the highline plugin, which must be installed. In order to do so, execute the following command.
Because Drupalgeddon doesn’t provide an interactive shell, we can use python and netcat to obtain one.
Privilege escalation 1
We can read the mysql database credential from the settings.php Drupal file.
Using the credential, we can get the databases users and hashes.
Using Rockyou we can retrieve the password for the system user brucetherealadmin.
Now, we can use SSH in order to obtain the user flag.
Privilege escalation 2
Using sudo we can see that we can execute the command /usr/bin/snapd install as root.
Hence, we can craft a snap package that uses the install hook to create a new account with root privileges. However, there is no need to create any; we can obtain one from the following GitHub repository.
Inside the dirty_sockv2.py code you can find the trojan snap. In order to turn it into a file, you need to execute the following command. Then, you only need to install it.
This snap package creates a new system user with the following credential dirty_sock:dirty_sock. This user can use sudo with any command. Hence, we can become root, obtaining the root flag.