Writeup - [HTB]
![Cover Image for Writeup - [HTB]](/assets/images/blog/Writeup-htb/Writeup.png)

Introduction
Writeup is an easy Linux machine from Hack The Box where the attacker will have to exploit an SQLi vulnerability in a very simple CMS for a later password cracking becoming the user jkr. Then, will have to take advantage of being a staff member for a path hijacking in the ssh service.
Enumerations
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
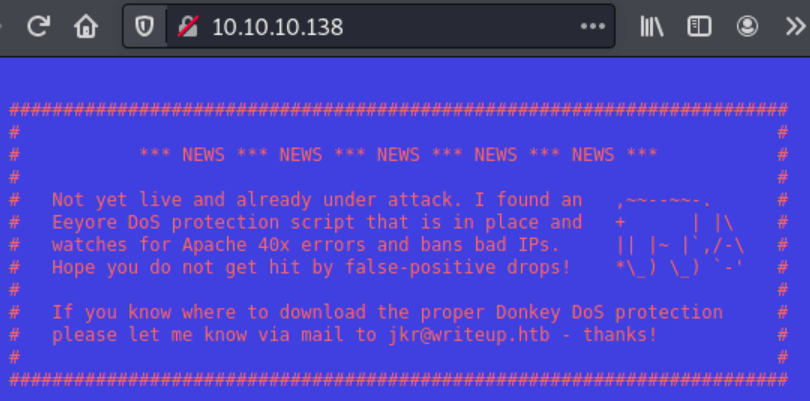
The first thing we encounter once we access to the Apache server, it is a text explaining that there is some type of DoS protection script, so any try to enumerate the web server is not viable.
The nmap output provide us with a web directory, which turns out to be a web page about Hack The Box write-ups. The web page uses CMS Made Simple which has a tone of found vulnerabilities in searchsploit.
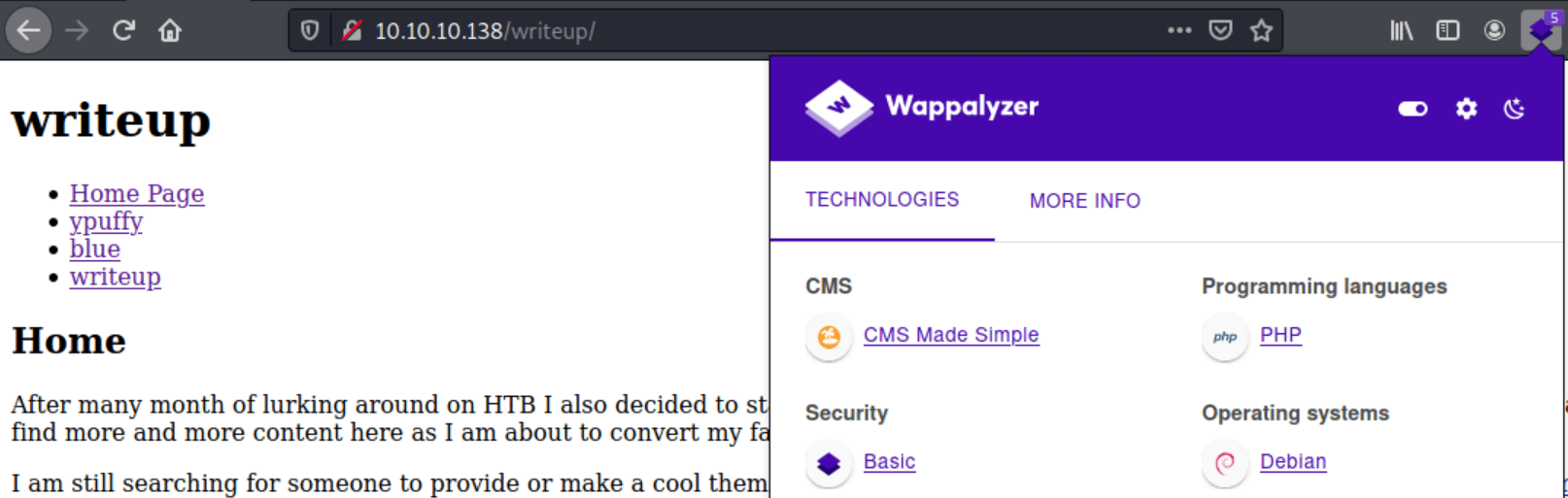
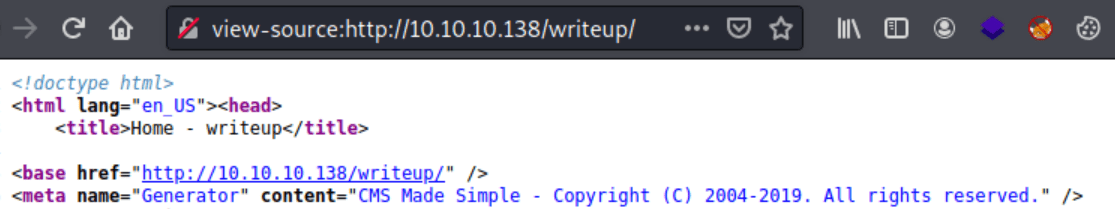
Looking in the HTML code we can find that the CMS version might be from 2019.
Adding this to the search in searchsploit we can find three different exploits, but the only one that doesn't require any kind of credentials is the SQLi exploit.
Exploitation
In order to obtain user credentials we need to execute the exploit as follows.
Note: In case you get any errors executing the python exploit execute the following commands.
In order to obtain the actual password we can use hashcat that is faster than the exploit.
Looking at the exploit we can know the mode needed for hashcat (20), obtaining jrk's password.
These credentials can be used for becoming jrk through SSH.
Privilege Escalation
Jkr is member of the staff group. Staff group allows users to add local modifications to the system (/usr/local) without needing root privileges. Hence, executables in /bin or /usr/bin may be "override" by the executables with the same name in /usr/local/bin because /usr/local/bin appears earlier in the PATH variable of any user.
So there must be some type of path hijacking in the machine that we need to find in order to get a shell as root.
Inside the file /etc/update-motd.d/10-uname there is the execution of the binary uname with a relative path (Is the same for every linux systems). The execution of this binary shows the same output as we showed earlier login as jrk through SSH.
Hence, we need to create a file named "uname" in the /usr/local/bin path. For doing so execute the following commands.
Note: Do not forget adding your id_rsa.pub
Finally, we only need to login as jrk through SSH triggering our script, then we login once again but as root, obtaining the root flag.
Note: If you can not see the text "Linux writeup 4.9.0-8-amd64 x86_64 GNU/Linux" once logged in the machine, that means the script was triggered.