Worker - [HTB]
![Cover Image for Worker - [HTB]](/assets/images/blog/Worker/Worker.png)

Introduction
Worker is a medium level Windows machine where the attacker first will have to face something similar to git in order to find a new domain, a user and a password. Then, using Azure devops will have to upload a reverse shell with the purpose of finding another user name and password getting the user flag with evil-Winrm. Finally, once again, using Azure devops the attacker will have to configure a pipeline, so at building time Azure will print the root flag.
Enumeration
As always start scanning all opened ports with nmap.
Then, I continue with a deeper scan obtaining a bit of information about each service.
In port 80 there is a Windows Server web page with just and image (Using gobuster didn't provide much information).
In the port 3690 there is a service named subversion (a software versioning and revision control system distributed as open source under the Apache License (Is like a GitHub Repository)), where we can retrieve a lot of information using subversion-cli tool and its specials syntax.
Let's First gathere some information like the repository like its author, the number of changes, its root repository ...
Secondly, which files are stored in the repository.
We can download them with the following commands.
In the movedt.txt file there is a new domain, where we can dig deeper in order to find more information.
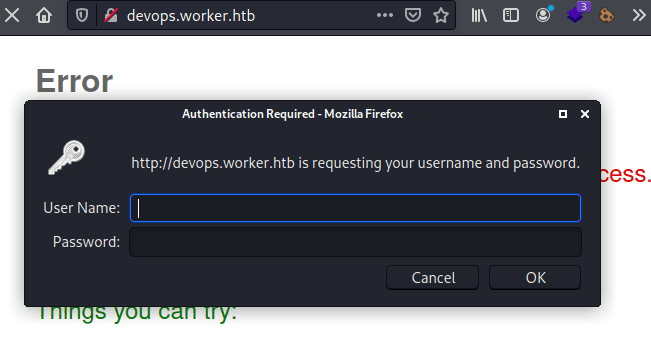
However, in order to get access we need to provide some credentials, but we don't have any.
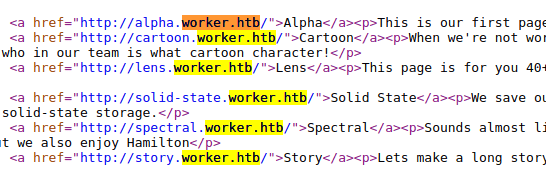
Inside the "dimension.worker.htb/index.html" we can find several domains. However, adding theme to the "/etc/hosts" file doesn't doesn't seem to be useful for now.
Looking into the different "revisions" there is a PowerShell file named "deploy.ps1", where we can find a user name and a password.
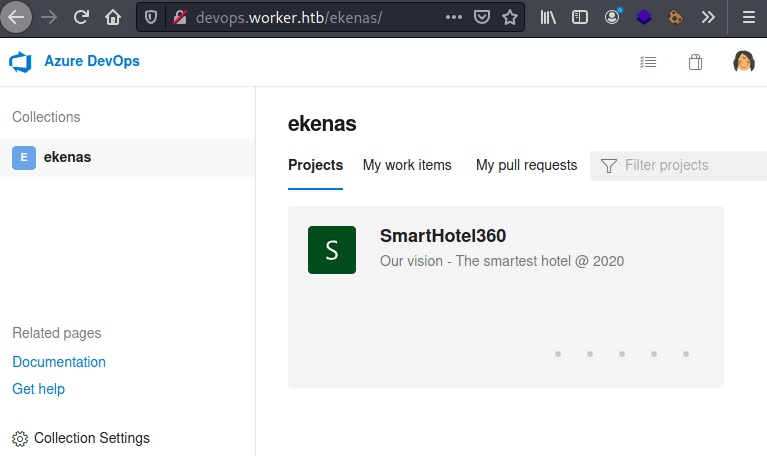
This credential is being used to access to the devops domain, where there is an Azure DevOps page (Azure DevOps is a Microsoft product that provides version control of files like Git). Inside the web page, we can see a repository about a "Smart hotel".
Explotation
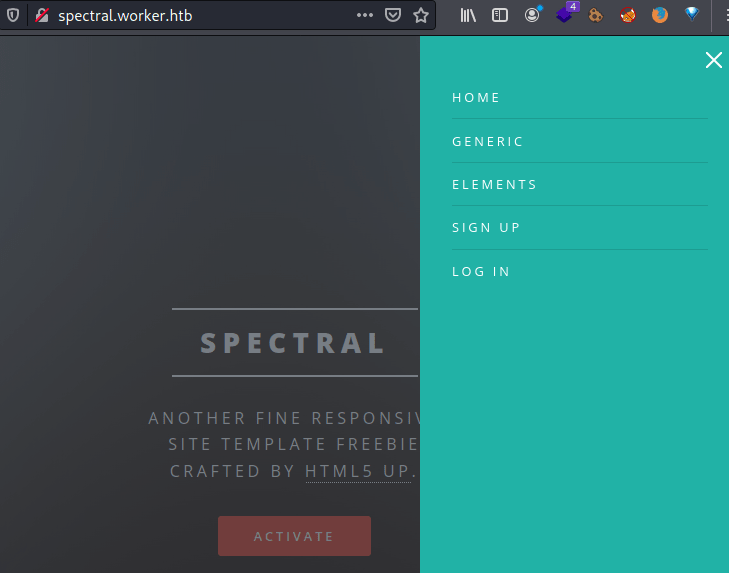
The files inside the repository are the same as the ones that we can find for the web http://spectral.worker.htb/.
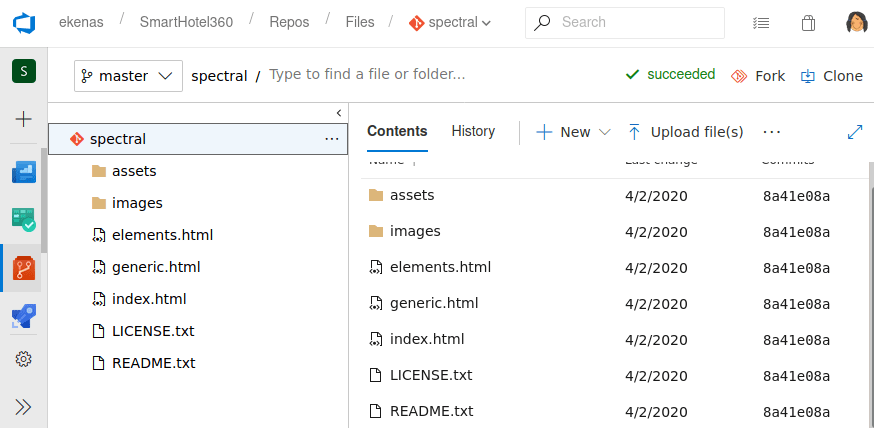
So, we could upload a web reverse shell for windows server so we can get access to the server internals. However, we can not upload a shell directly to the repository, we need to do a pull request.
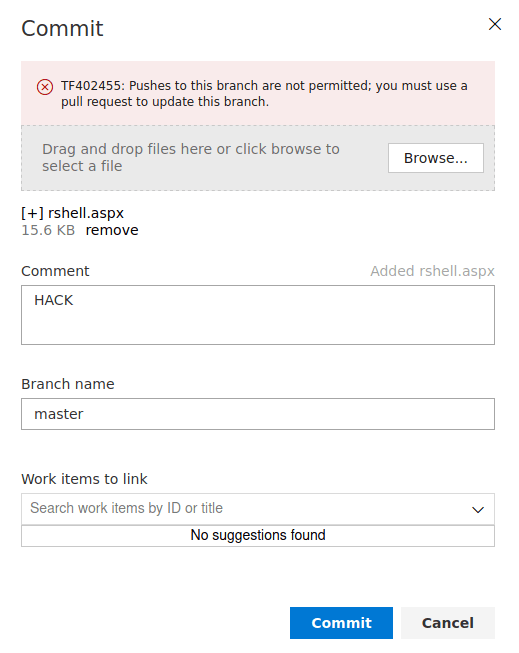
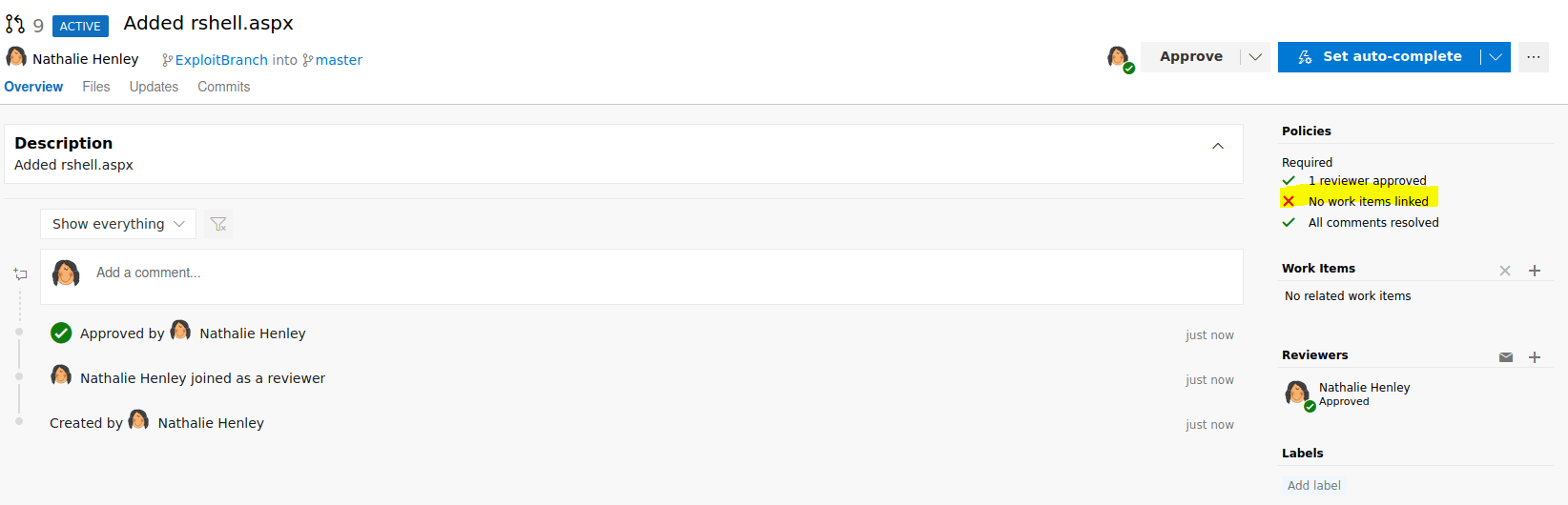
Furthermore, we can not create a branch followed by a pull request because the request will never be completed because we don't have any work items linked.
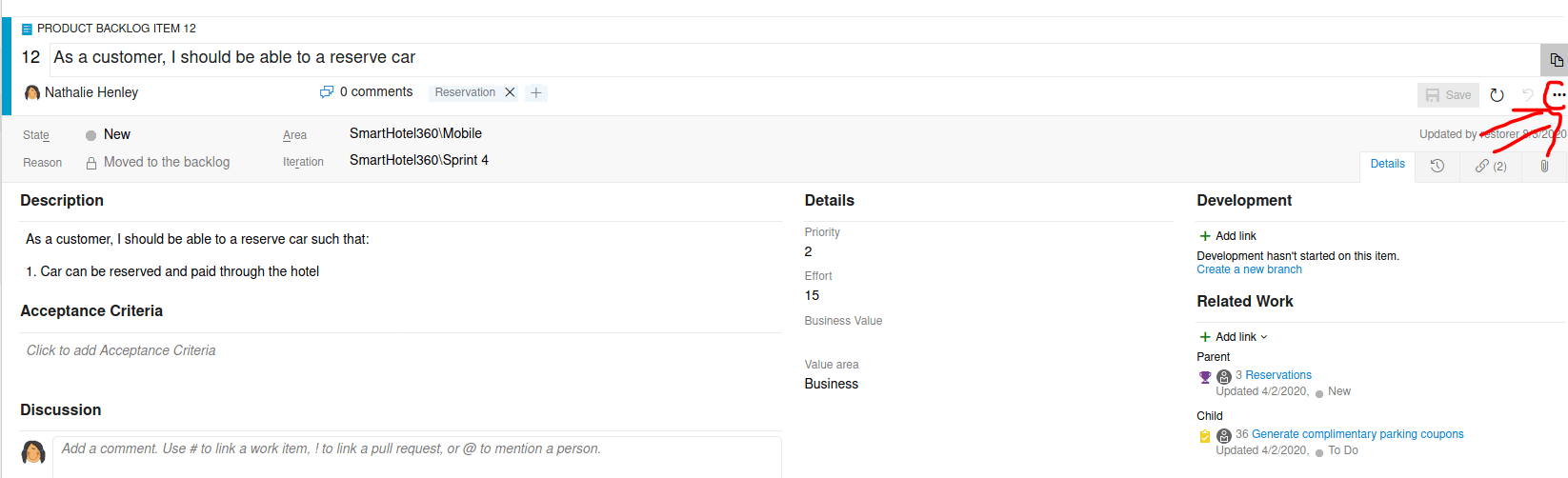
Finally, in order to upload a reverse shell we need to go to the "Boards" section clicking in one of the Work items.
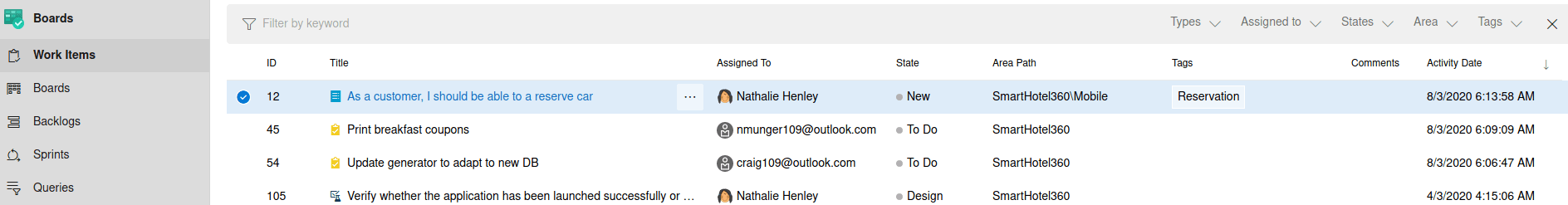
Then, we need to click on the 3 dots, clicking on new branch.
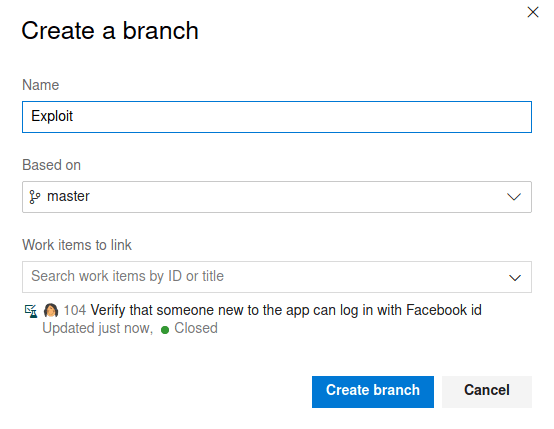
The appearing pop up should looks like this (Obviously, without the word exploit :V ).
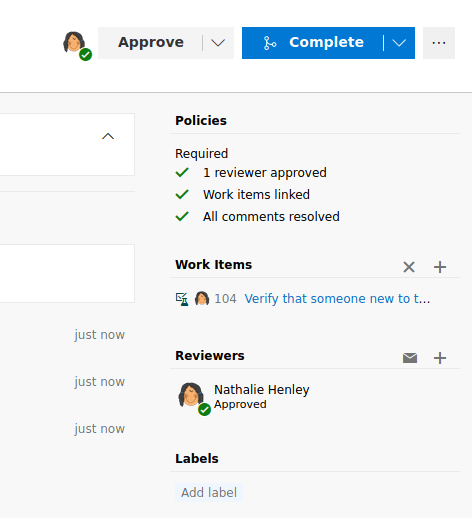
Once, our shell has been uploaded to the repository, we can create a pull request.
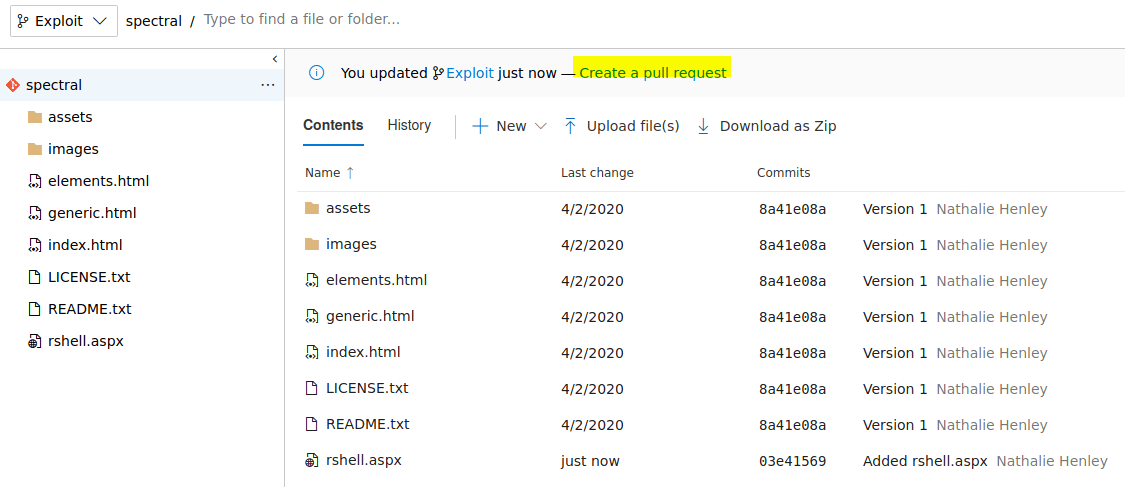
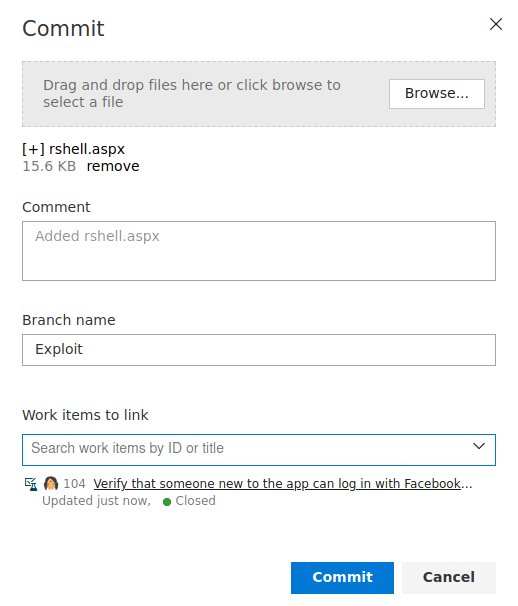
Click on "Create" and finally on "Complete" and our shell will be uploaded.
Now, we can create a listening port and when we access to http://spectral.worker.htb/rshell.aspx, we retrieve our reverse shell. However, you won't find anything useful on the C: drive, that is because this machine is composed with another hard drive.
Inside W:\ there is a file named passwd with a lot of users and passwords.
Between all of them, the one below works for accessing to the system using the winrm service (5985)
For that we can use evil-winrm as you can see with the following command.
Furthermore, this credential can be used to get access to the Azure DevOps web page. Finding a new repository.
Privilege escalation
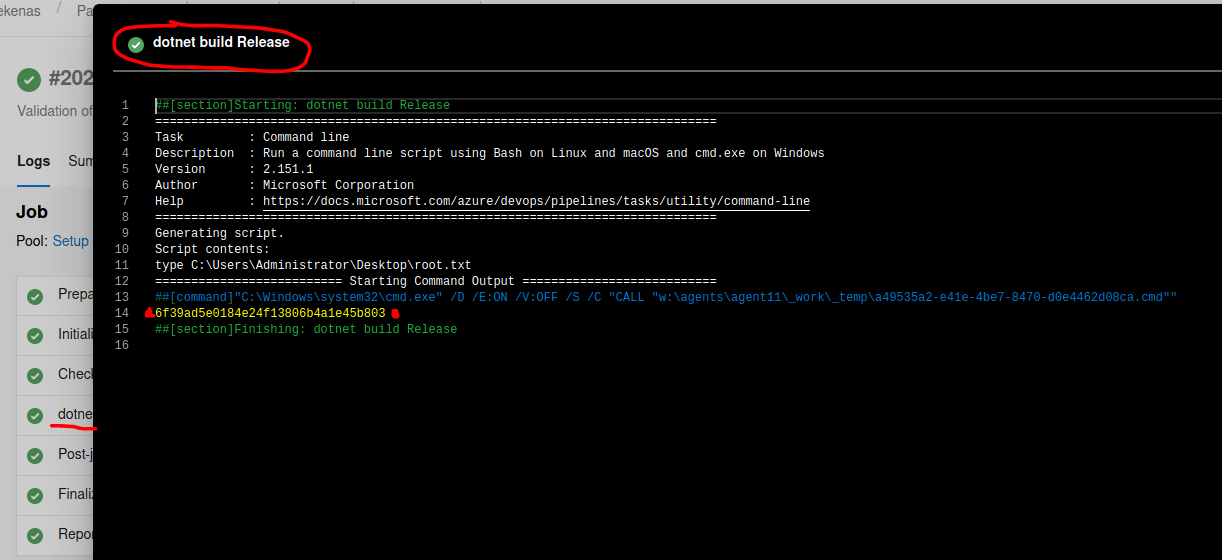
Because we have access to the repository, we can use the Azure Pipelines to execute code on the windows machine that will be executed once our pull request has been accepted. So in order to get our root flag, we need to access to the repository, press "Pipelines" and then "New pipeline".
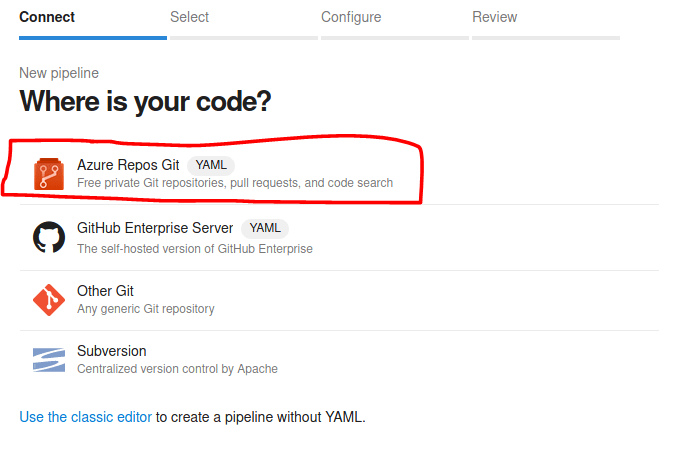
After that, click on "Azure Repos Git" as our platform for the repository.
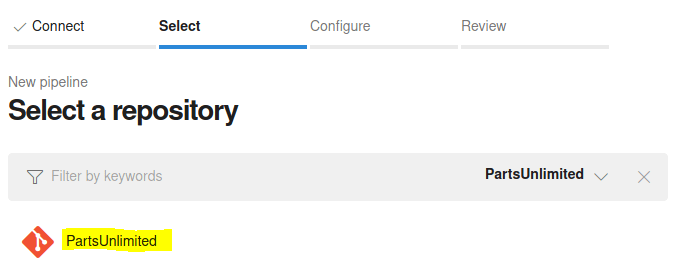
Select the repository "PartsUnlimited".
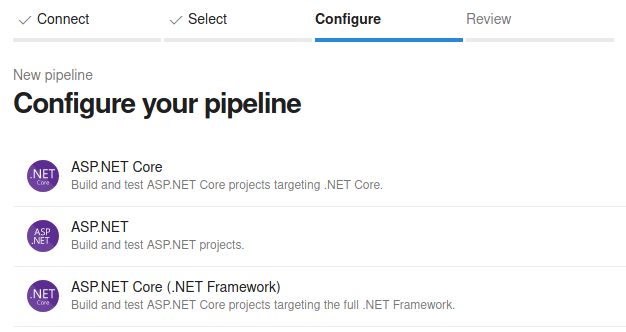
Click on "ASP.NET Core" for building and testing ASP.NET Core projects.
Modify the "azyre-pipelines.yml" file so during building time will be executed.
Note: Don't forget to remove the line pool: 'Default'
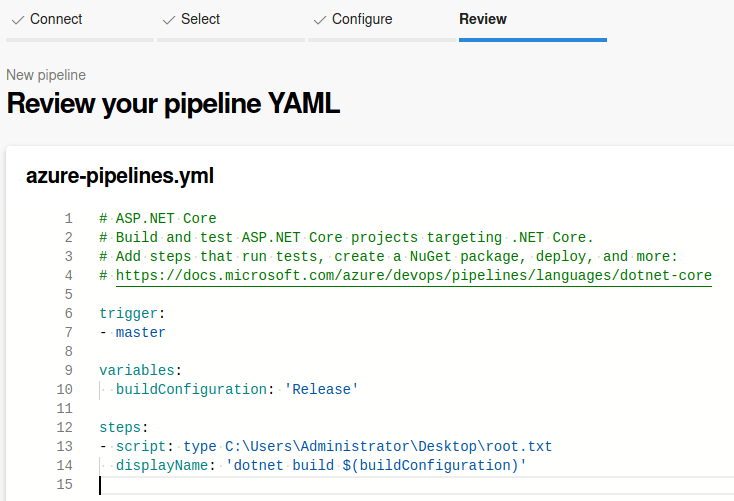
Then, click in the "Save and run" button and wait to pipeline to finish.
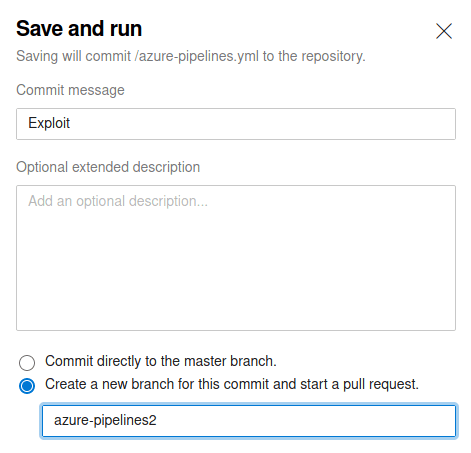
Finally, click on "dotnet build release" so you will see the root flag.