Trick - [HTB]
![Cover Image for Trick - [HTB]](/assets/images/blog/Trick-htb/Trick.png)

Introduction
Trick is an easy Linux machine from Hack The Box where the attacker will have to enumerate a DNS service to retrieve as many domains as possible. One of the domains can be used to access a web page vulnerable to SQLi. Furthermore, it will have to enumerate vhosts to find another web which is vulnerable to path traversal. Finally, it will have to escalate privileges due to a permission misconfiguration on the fail2ban service.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of each opened port, getting more information about each service.
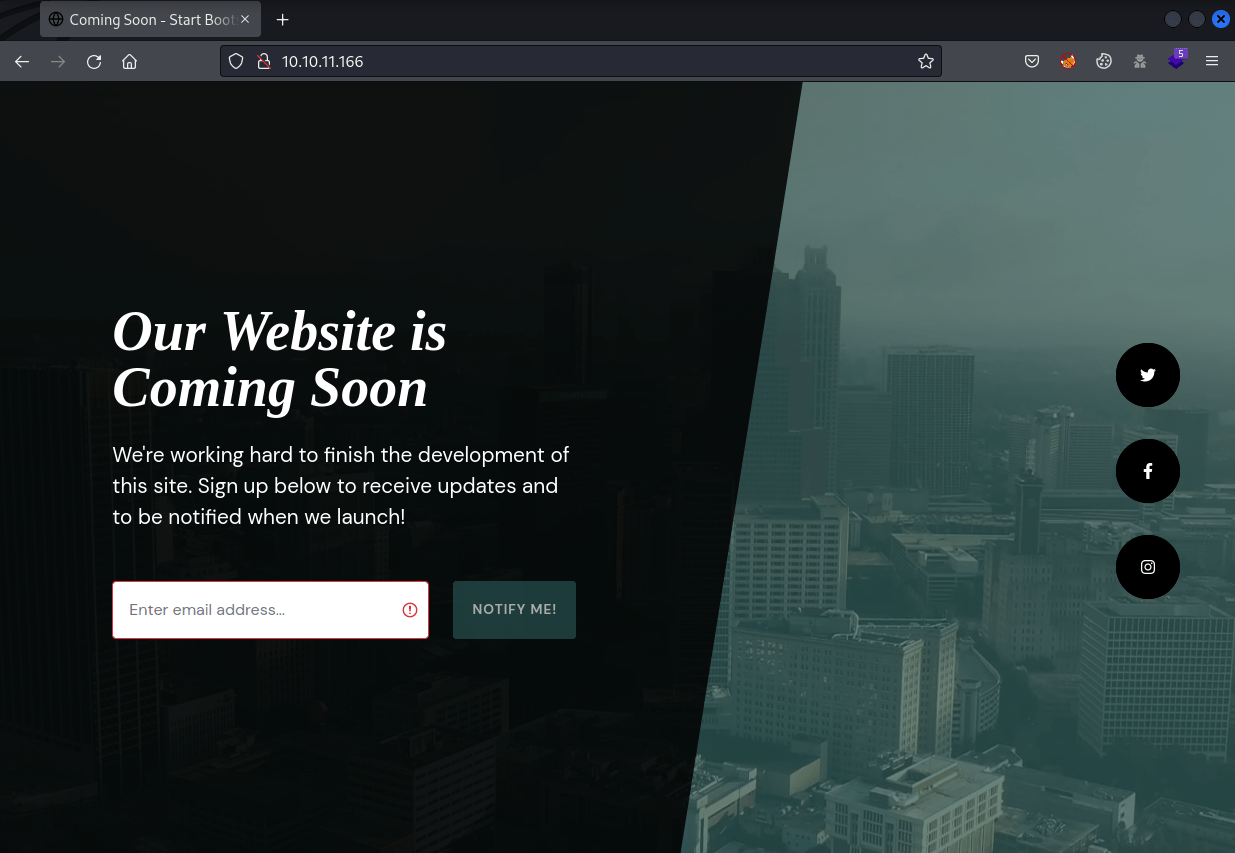
Starting at the web page, we can find a simple static web that doesn't have anything interesting.
So, continuing with the DNS service, we can do a reverse lookup of the IP, getting a domain.
Then, by doing more DNS enumeration, we can obtain more subdomains.
Finally, after doing a domain transfer with the domain trick.htb we can obtain a new subdomain.
Exploitation 1
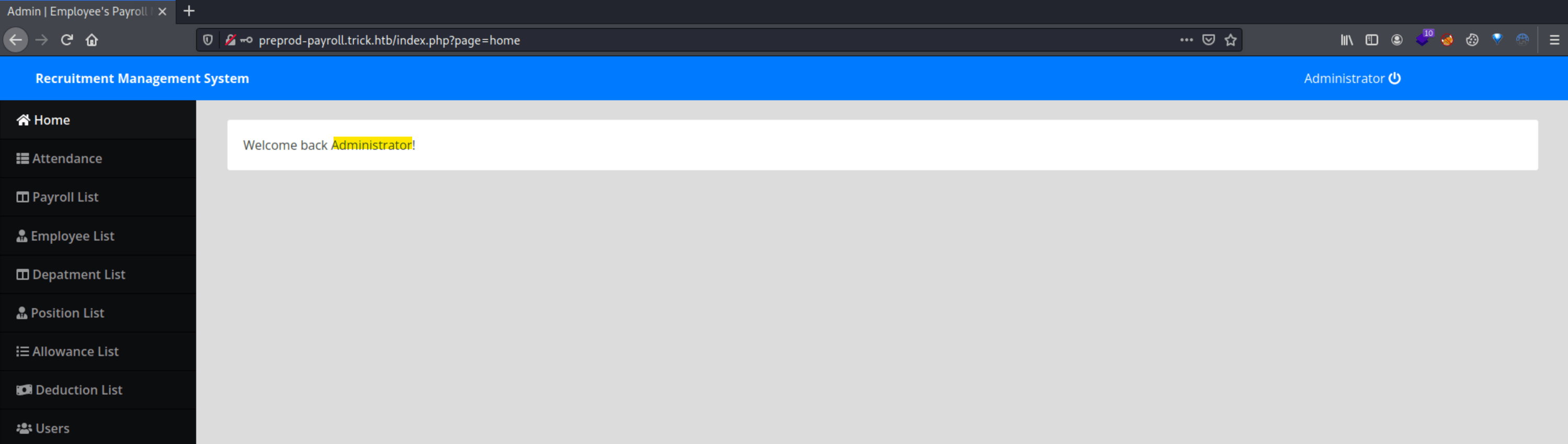
This last domain leads us to a payroll web page vulnerable to SQLi.
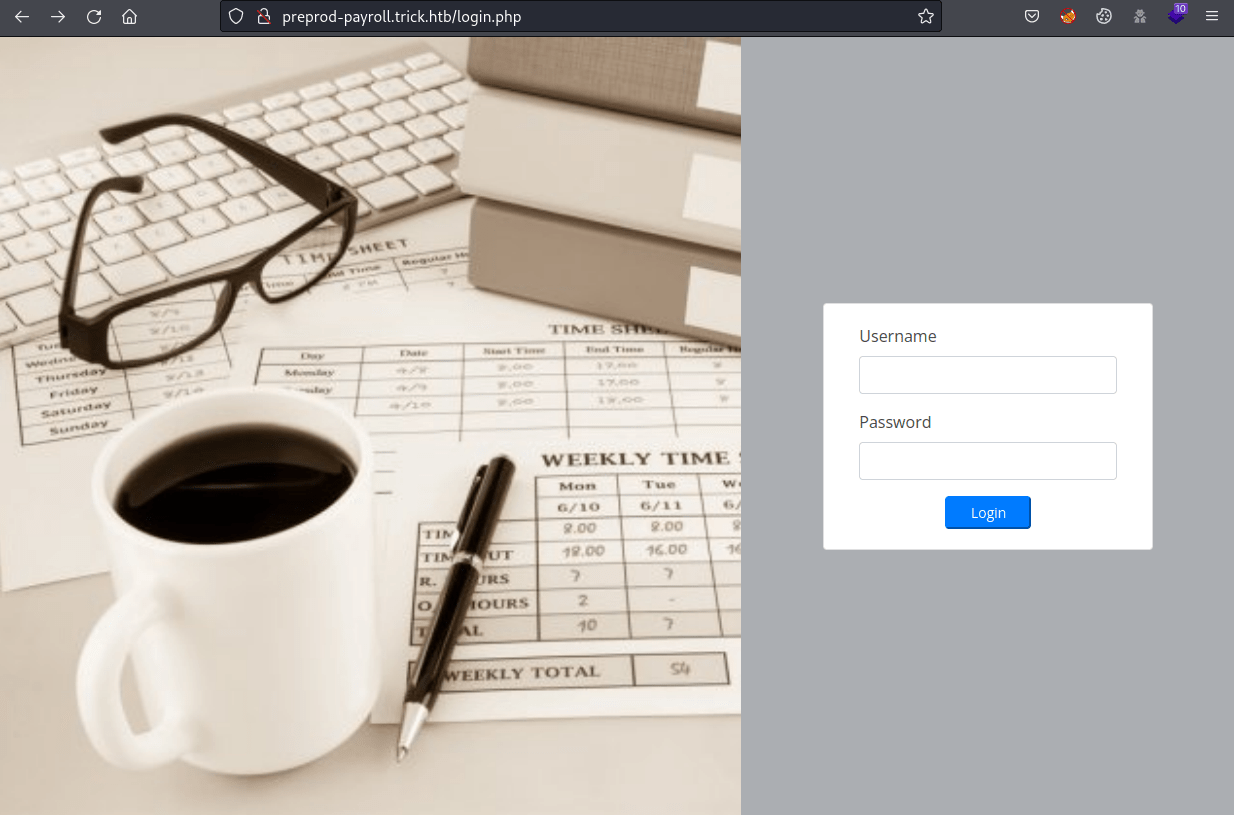
Using ' or '1'='1' -- - as password, we gain access to the web page as Administrator.
Using SQLMap, we can retrieve credentials from the database.
These credentials can't be used anywhere, but we can retrieve files from the system. However, we can not do much with the information of these files.
Hence, because this server has virtual hosts like "payroll", let's enumerate more virtual hosts.
As we can see, the page URL parameter is used to display files from the web server.
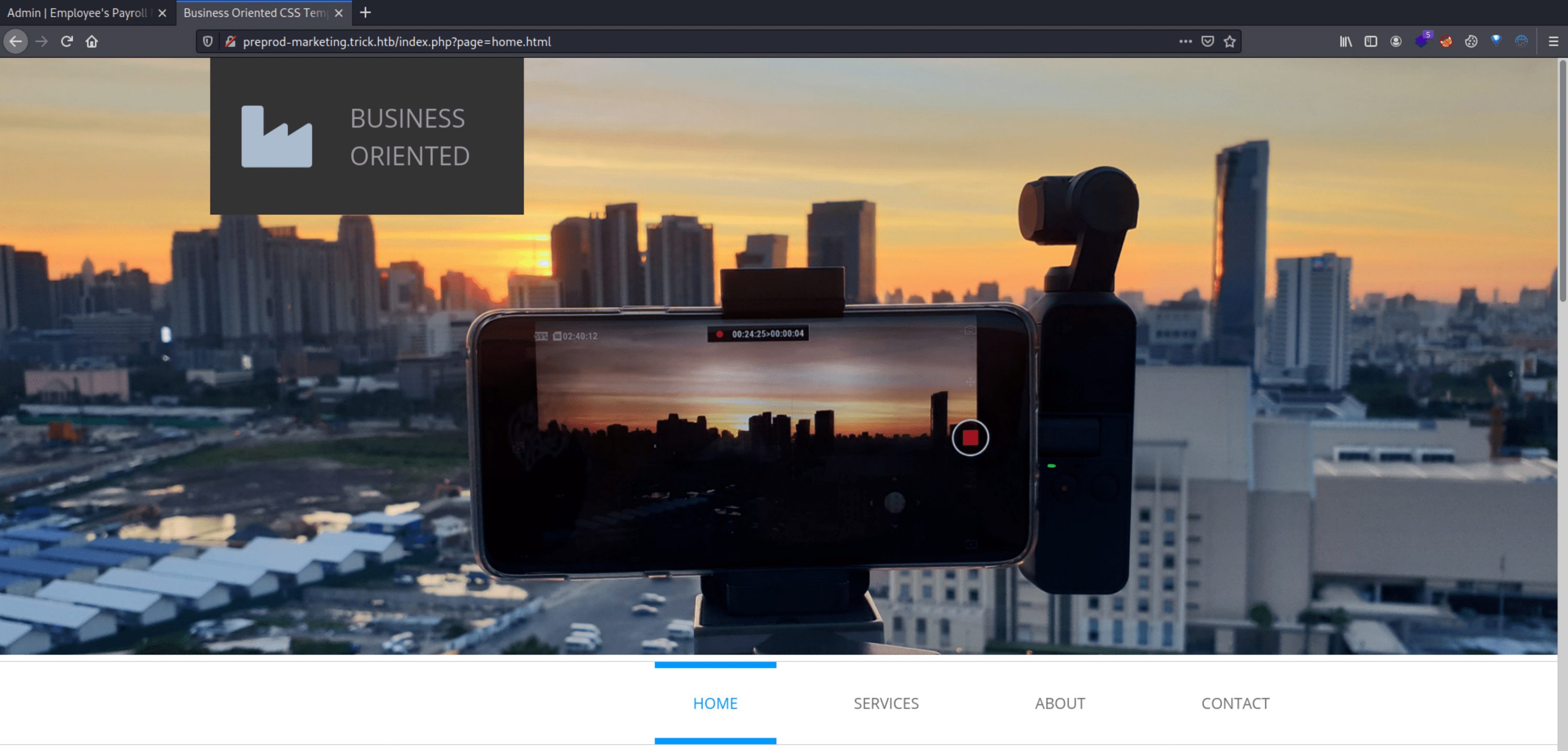
Using the previous SQLi, we can try to obtain the index.php to see the filter that doesn't allow us to perform path traversal attacks.
After some trial and error, we can obtain that the web is located at /var/www/market/, retrieving index.php.
As you can see, it deletes the string "../", but if we write "....//", the result will be "../".
Using this knowledge to our advantage, we can obtain files again from the system.
Exploitation 2
Taking advantage of this vulnerability, we can retrieve Michael's private key, which couldn't be retrieved with the SQLi vulnerability.
Using Michael's private key we can obtain the user flag.
Privilege Escalation
Enumerating the groups which Michael belongs, we can see a "security" group. This group has write permissions to the directory /etc/fail2ban/action.d. Hence, we can remove and create any file under this directory.
Furthermore, Michael is capable of restart the fail2ban service, installed on the machine.
Looking information about "fail2ban privilege escalation" appears this post which tell us what we have to do in order to escalate privileges.
Looking at /etc/fail2ban/jail.conf, we can see that if we perform in 10 seconds 5 failed login attempts the ban action "iptables-multiport" will be performed.
Because we do not have write file permissions we can not edit the file, but we have write directory permissions thus we can remove and create a similar file.
By default, iptables-multiport creates an iptable rule as action ban, so changing the actionban command we can obtain a reverse shell as follows-
I used hydra to trigger the SSH login fail attempts.
After waiting a bit, you should get a reverse shell as root.