Time - [HTB]
![Cover Image for Time - [HTB]](/assets/images/blog/Time-htb/Time.png)

Introduction
Time is an easy-medium Linux HackTheBox machine where the attacker will have to exploit a JSON Data Processor in order to obtain a reverse shell a pericles. Then, he or she will have to modify a custom service which runs a custom script with write permissions in order to obtain root the flag.
Enumeration
As always I started scanning all open ports in the machine.
There are just two open ports, so let's run nmap with default scripts to gather more information.
As expected, nmap doesn't provide useful information so looking into the web server appears this web site.
Exploiting
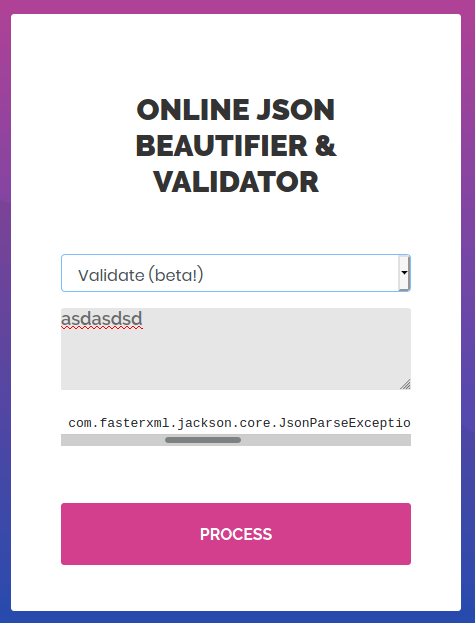
Submitting random data into the "Validate (beta)" beautifier appears the following error.
Looking in Google appears a post about Jakson gadgets, inside the post there is a sql file named as inject.sql, that can be modified so at execution time can provide us a reverse shell. The file is the following: (Change the IP)
In order to execute the exploit we need to create an HTTP server using python in the same directory where the payload (inject.sql) is stored, so the payload can be uploaded.
Then, we need to put a listening port using netcat.
Finally, we only have to submit the following payload and a shell will appear as the user "pericles". (Change the IP)
Privilege escalation
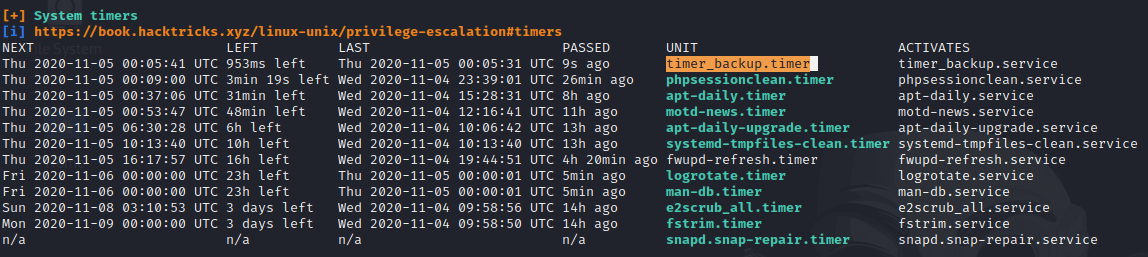
Using Linpeas shows a weird timer named "timer_backup.timer" which appears to be a service "timer_backup"
Looking inside the "timer_backup.service", it restarts the service "web_backup.service ". Looking in the web_backup.service file, seems that the service execute a custom script named timer_backup.sh.
As it seems, the user "pericles" can modify this file.
Hence, the file can be modified so it creates a reverse shell as it has been done before.
Firstly, create a listing port at 4445 using netcat.
Secondly, we need to execute the following command so we can append the reverse shell using bash. (Don't forget to change the IP)
Finally, you only have to wait to the script to execute getting a reverse shell as root.