TheNotebook - [HTB]
![Cover Image for TheNotebook - [HTB]](/assets/images/blog/TheNotebook-htb/TheNotebook.png)

Introduction
Thenotebook is a medium linux machine from HackTheBox where tha attacker will have to modify a JWT cookie in a notes web page becoming administrator. Then, the attacker will have to upload a php reverse shell, so he or she can extract the user's ssh key from a backup file. Finally, in order to become root the attacker will have to exploit a docker vulnerability.
Enumeration
As always let's begin looking for every opened port in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Because SSH never is vulnrable let's jump to the weppage.
Using gobuster we can fin the following directories.
Trying to access to the /admin return a 403 FORBIDDEN status code, so there must be a way to get access to it.
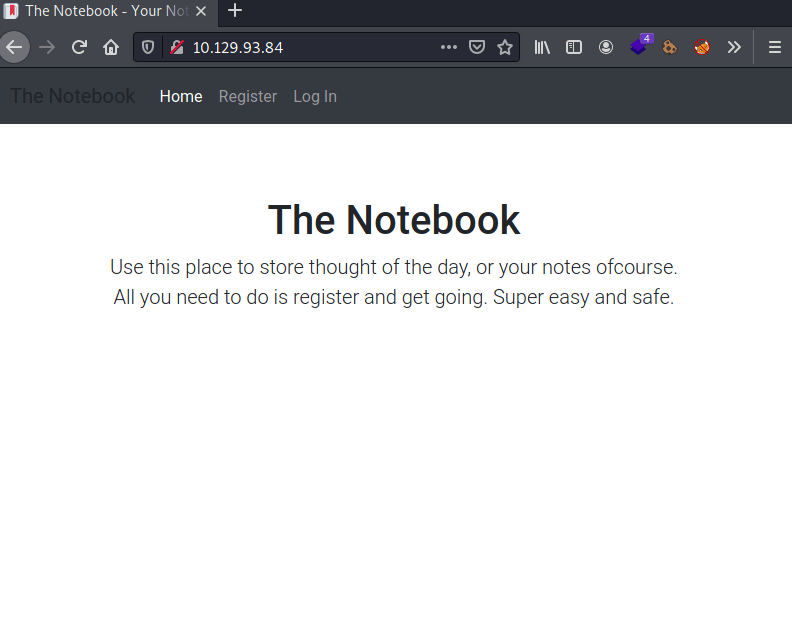
Once we are registered and logged into the NoteBook web page, we can see a that there are two cookies, which one seems to be encoded in base64.
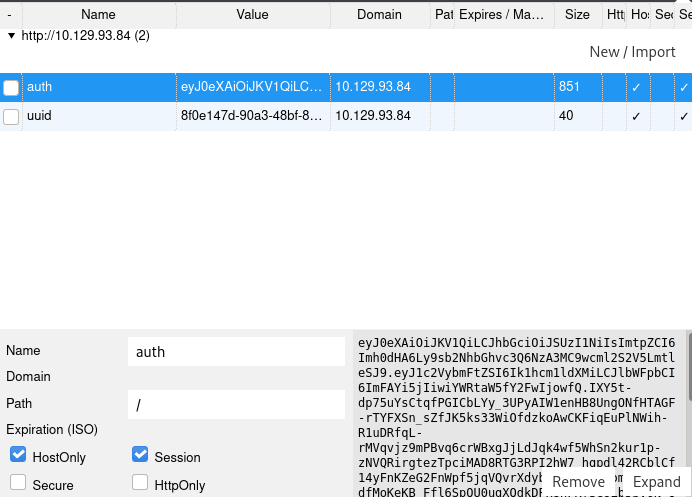
Trying to decode it with cypherchef I got the following result.
This cookie seems to be like a JSON Web Token, JWT for short, which has an admin_cap set to 0. A JWT token is an Internet proposed standard for creating data with optional signature and/or optional encryption whose payload holds JSON that asserts some number of claims. The tokens are signed either using a private secret or a public/private key. For example, a server could generate a token that has the claim "logged in as admin" and provide that to a client.
Explotation
Hence, we can create our own JWT token with the admin_cap parameter set to 1, using our machine as the server that validates the key, used for generating the HMAC in the cookie.
To tackle this problem, first I generated an ssh key used for generating the HMAC.
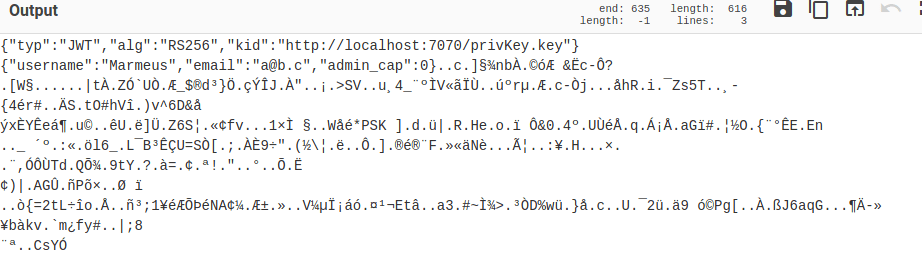
Then, we can generate the cookie using jwt.io and the following parameters.
HEADER
PAYLOAD
VERIFY SIGNATURE
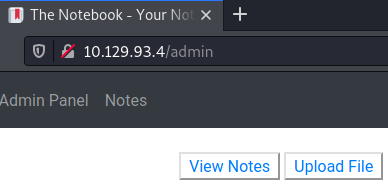
Finally, we only have to create a python web server at port 7070, that is being executed in the same folder as where the key has been stored; change our auth cookie and access to http://10.129.93.4/admin.
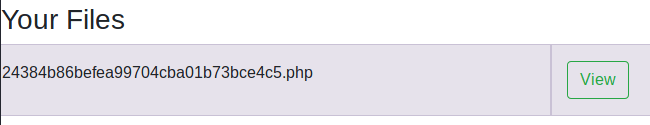
Now, we are able to upload a php reverse shell to the web page in order to get access into the machine.
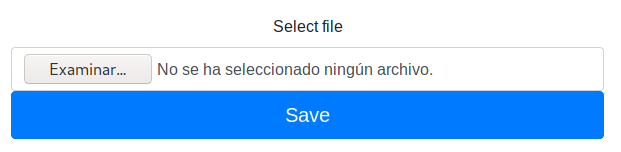
Then, once uploaded the file we need to create a listening port with nc and click in "View" to obtain our reverse shell.
Privilege escalation 1
Enumerating inside the machine, we can find the file home.tar.gz in the /var/bakcups folder. Coping it to the /tmp/ folder and extracting its contents we can retrieve noah's SSH private key.
Privilege escalation 2
Executing the command sudo -l noah can execute any command inside the docker container webapp-dev01* .
In order to become root in this machine we need to exploit a vulnerability associate with the docker's version.
Searching online vulnerabilities for docker exec 18.06 we can obtain the vulnerability CVE-2019-5736 which has several exploits associated. However, the only that works is written in go and you can find on this GitHub repository.
Note: This exploit has dangerous side effects on the machine, thus if the exploit doesn't work you will need to reset the machine.
In order to obtain the root flag we need to download the file main.go which is available in the aforementioned GitHub repository. Then, modify the var payload as follows.
After that, we need to compile the file with go build main.go obtaining a file named main.
Note: If you do not have the go compiler you can install it with sudo apt install golang-go -y.
Now, we need to get a shell in the docker container.
Create a python web server for downloading the exploit into the container.
Command: sudo python3 -m http.server 80
At this point, you need to open another terminal inside the container ASAP.
Then , you will obtain the following output in the terminal where the exploit has been executed. Meaning, that the execution of the exploit has been completed.
Finally, we only have to exit from the container so we can obtain our flag at /tmp/flag.