Tenet - [HTB]
![Cover Image for Tenet - [HTB]](/assets/images/blog/Tenet-htb/Tenet.png)

Introduction
Tenet is a easy-medium Linux machine from HackTheBox where the attacker will have to find some files in the web server in order to exploit an unserialise vulnerability in order to get an RCE. Then, will have to find some credentials in a file to get the user flag and finally will have to produce a race condition in order to become root.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
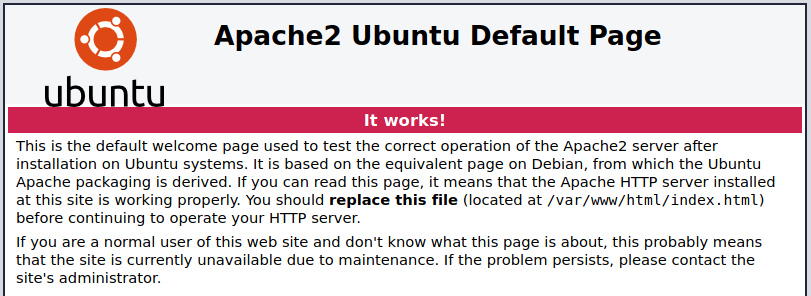
Nmap tell us that there is the default Apache web page at the root direcotry in the port 80.
Using the machine name as domain tenet.htb, adding it to the /etc/hosts file we can access to a wordpress page.
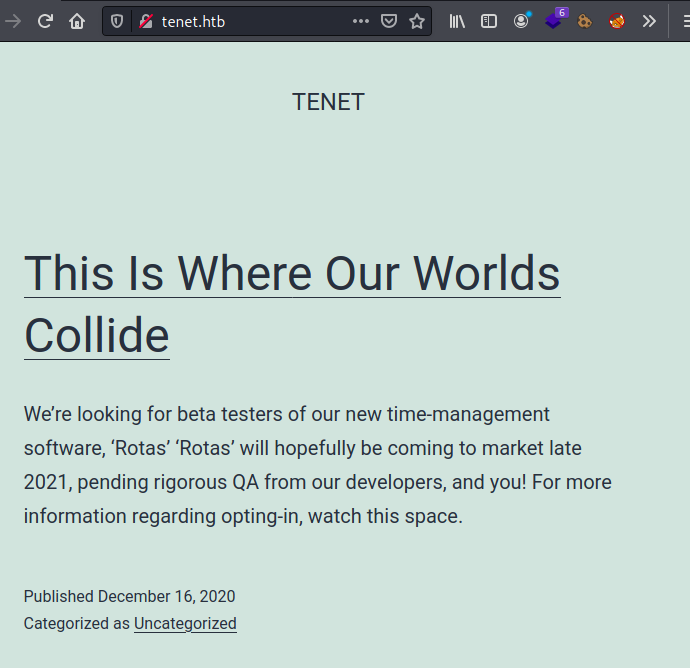
In one of the three posts there is a comment by neil, giving us a hint about what we have to find.
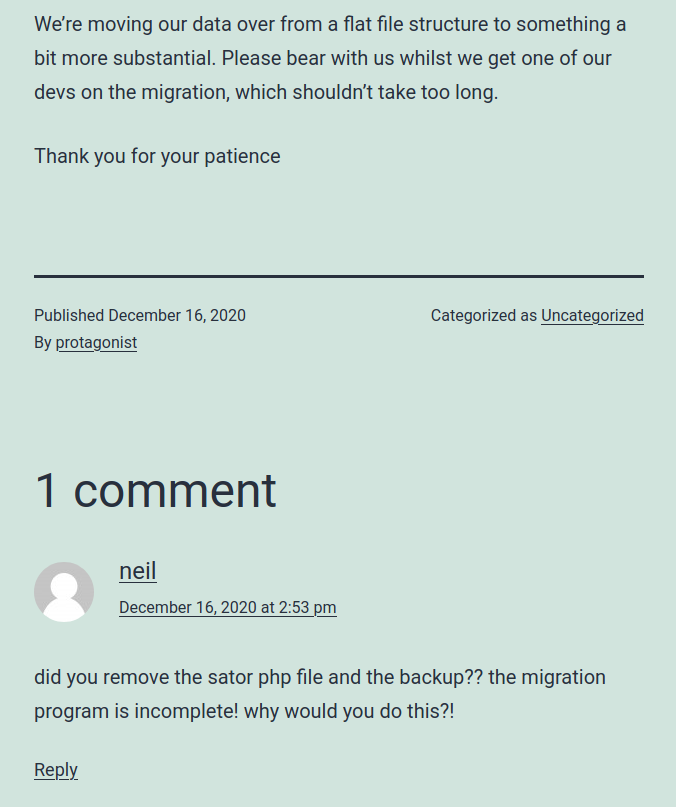
So we have to find sator.php and sator.php.bkp files in the web server.
After some time, it seems that the files are at http://10.10.10.223/sator.php and http://10.10.10.223/sator.php.bak.
The sator.php file says that is grabbing the user from some file.
Looking in the sator.php.bak file we can see that the program is unserialising the values we are passing through the arepo variable and saving the value "Success" in the users.txt.
Explotation
What we can do to exploit this code is creating a class DatabaseExport which saves a simple PHP code into another file so we can get a reverse shell by just accessing to that file.
What are we doing is creating our own class DatabaseExport which $user_file is initialised to cmd.php and $data to the code we want to execute once we access to cmd.php. The output is encoded in order to be passed directly to the arepo variable.
The code will be will interpreted like a new DatabaseExport replacing the values already initialised in the server.
Finally, we only have to access to this link, obtaining our reverse shell.
Privilege escalation 1
Because we are www-data, we need to escalate privileges in order to get the root flag.
Looking into the wordpress file wp-config.php, where the database credentials are stored, appears to be the neil's credential, that can be used in SSH, getting the user flag.
Privilege escalation 2
As the user neil we can execute the script enableSSH.sh as root.
The code is the following.
Basically, what is doing is creating a temporal file named /tmp/ssh-XXXXXXXX where every user has write privileges, then adds the root public key and removes the temporal file.
Due to the use of umask 110 allows to create any file where every user can write but just "others" can execute, as we can see in the example.
Hence, we need to produce a race condition so we can write into the temporal file once it has been created.
To tackle this problem, I created a key.pub file in the /tmp/ folder storing my public key on it.
Then, using tmux open two terminals in the /tmp folder. In the first terminal run the first command, creating an infinite loop looking for ssh* files; if there is any it appends the public key into it. In the second terminal execute the second line, where is running the script infinitely.
Finally, after a couple of seconds we can stop both commands, access as root with ssh, obtaining the root flag.