StreamIO- [HTB]
![Cover Image for StreamIO- [HTB]](/assets/images/blog/StreamIO-htb/StreamIO.png)

Introduction
StemIO is a medium Windows machine from HackTheBox, where the attacker will have to perform some Time-based SQLi to obtain some credentials for getting access to an admin panel. Then, it will have to perform a parameter enumeration, finding an LFI in a debug parameter, which can be used to retrieve the web's source code. After that, it will have to analyse the source code to find an RCE. Subsequently, it will have to dump a Firefox database to obtain some credentials. Finally, it will have to use the obtained credentials to obtain, through LAPS, the admin password.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Thanks to Nmap, two domains have been found.
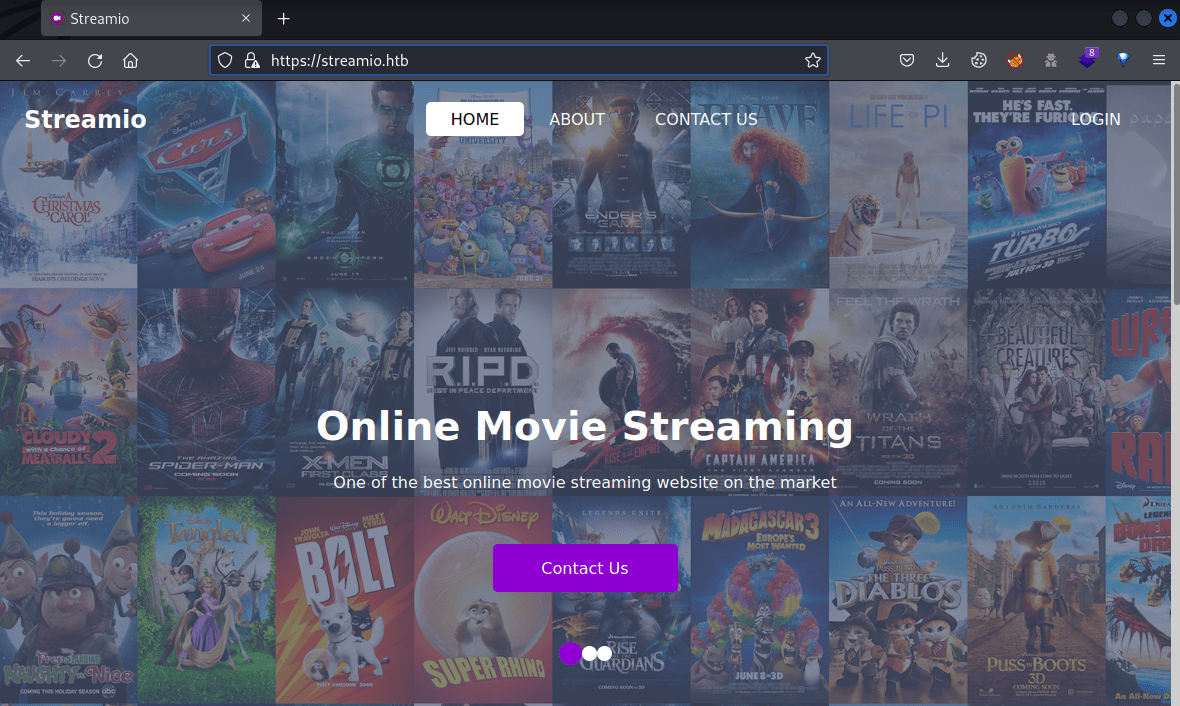
At port 80, there is only a default IIS Express page, but at port 443 appears a web page about online movie streaming.
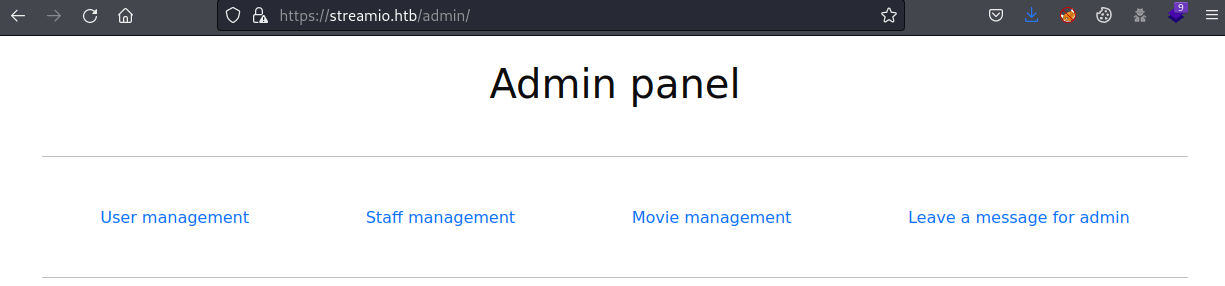
Enumerating the web page appears an admin page but it is forbidden.
Inside the login panel, it is possible to sign up users despite not being allowed to log in later.
Exploitation 1
Because the web server is an IIS Windows Server, there is a high chance that the database management system used in the web page is MSSQL. So trying different payloads from PayloadAllTheThings, it is possible to confirm that the database is MSSQL and vulnerable to Time-based attacks.
This can also be confirmed with SQLMap.
Now, let's obtain the database information.
Note: This process takes a VERY VERY long time.
To crack most of the hashes, the online tool Crackstation can be used.
Of all the users, only it is possible to log in with the user "yoshihide" with its password 66boysandgirls...
Now, it is possible to access the /admin panel.
Then, a new parameter can be obtained after some parameter enumeration.
Also, the debug parameter seems to be vulnerable to LFI.
To obtain the PHP code of the web page, it is necessary to use PHP wrappers and then decode it.
Exploitation 2
Some credentials can be obtained, but they are not used by any user.
Enumerating the /admin/ directory appears a new file.
Using the PHP wrapper again, it is possible to obtain its source code.
Analysing the code, the following conclusions can be obtained. The application checks if the included variable is set, stopping the execution if it is not. Then, at the bottom of the file, there is a POST variable named include which will retrieve the contents of any file passed as an argument.
Exploitation 3
Hence, using the LFI vulnerability, the file master.php can be included in the index.php file, which defines the included variable to true, allowing to obtain the contents of any arbitrary file.
Furthermore, to avoid hosting a web shell, we can use another PHP wrapper to obtain code execution.
Note: To obtain a proper reverse shell, you can URL encode the PowerShell base64 from revshell.com.
Now, it is possible to access the database, enumerating inside the streamio_backup.
After, cracking the hashes, it is possible to obtain nikk37's password, getting access to the machine through winrm and obtaining the user flag.
Privilege Escalation 1
Running Winpeas as nikk37, it is possible to find a Firefox database which might contain some credentials.
The tool firepwd can be used to decrypt the password from the Firefox database, but the files key4.d and logins.json must be downloaded.
Once, the tool is executed the following passwords can be retrieved.
Privilege Escalation 2
Making some enumeration with the new obtained users, it is discovered that the password JDg0dd1s@d0p3cr3@t0r can be used for accessing through SMB or LDAP as the user JDgodd.
On SMB, there is not much that can be obtained.
Nonetheless, the DC's LAPS password can be obtained using LAPSDumper.
Now, it is possible to access the machine as Administrator.