Shocker - [HTB]
![Cover Image for Shocker - [HTB]](/assets/images/blog/Shocker-htb/Shocker.png)

Introduction
Shocker is a pretty easy linux machine from HackTheBox where the attacker will have to exploit the famous vulnerability ShellShock obtaining the user flag and execute the perl binary as sudo to become root.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
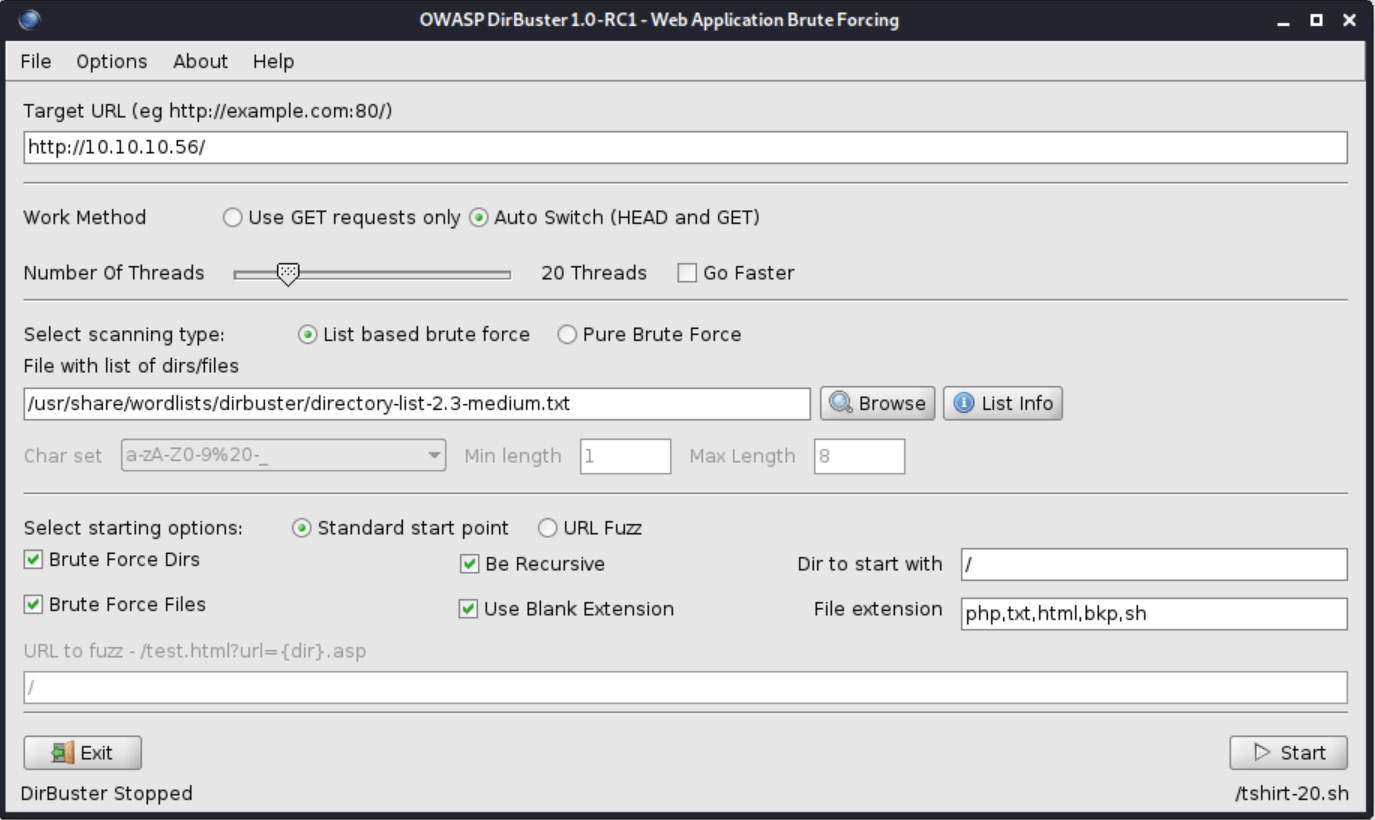
Fuzzing the the apache server with the following DirBuster configuration.
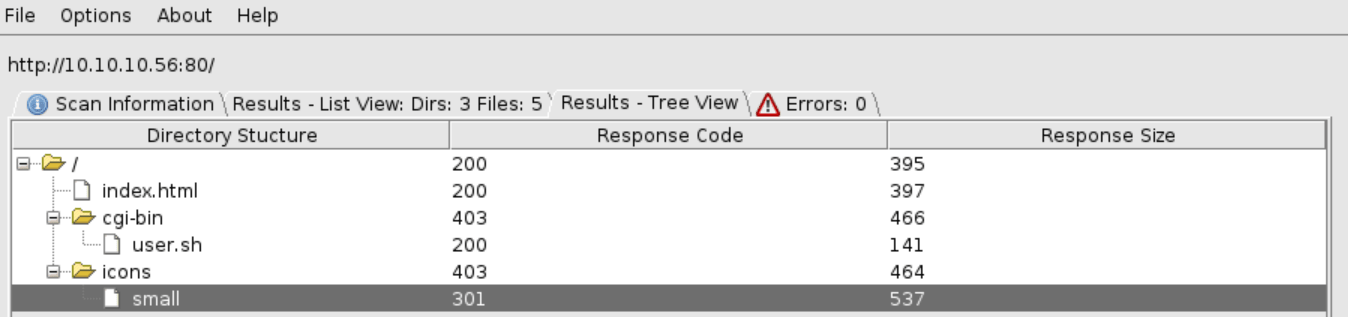
We can obtain the following structure.
Accessing to the file user.sh, we obtain what it seems the uptime command output.
Looking for "apache 2.4.18 cgi-bin vulnerability" on Google appears this link about the ShellSock vulnerability, that can be used to check if this machine is vulnerable.
Exploitation
For doing so, we need to listen for any icmp package with tcpdump . Then, executing the following command we obtain an icmp reply.
Now, if we want a reverse shell we need to execute the following command, being able of obtaining the user flag.
Privilege escalation
Using sudo we can execute the perl binary.
In order to become root we only need to execute this command.