Secret - [HTB]
![Cover Image for Secret - [HTB]](/assets/images/blog/Secret-htb/secret.png)

Introduction
Secret is an easy Linux machine from HackTheBox where the attacker will have to create its own JWT token in order to exploit an API for obtaining a reverse shell. Then, will have to force a core dump of a SUID binary to obtain the contents of the root flag.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port getting more information about each service.
Having a look at port 80 there is a web page where we can find a ton of information about an API in development.
With the following link, we can download the API's source code, and in this other link, we can retrieve information about the API functions.
| Function | Method | URL | Body | Header |
|---|---|---|---|---|
| Register user | POST | http://10.10.11.120:3000/api/user/register | {"name": "", "email": "","password": "" } | |
| Login user | POST | http://10.10.11.120:3000/api/user/login | {"email": "","password": "" } | |
| Access Private Route | GET | http://10.10.11.120:3000/api/priv | auth-token: <JWT_TOKEN> |
Once the source code is downloaded, we can analyse how the API works internally
To access the endpoint /priv, our JWT token must contain the name "theadmin", as we can see in routes/private.js.
Furthermore, we require the TOKEN_SECRET that is being used at routes/verifytoken.js
Looking at the source code commits we can see that .env was removed. But, going to the previous commit we can obtain it.
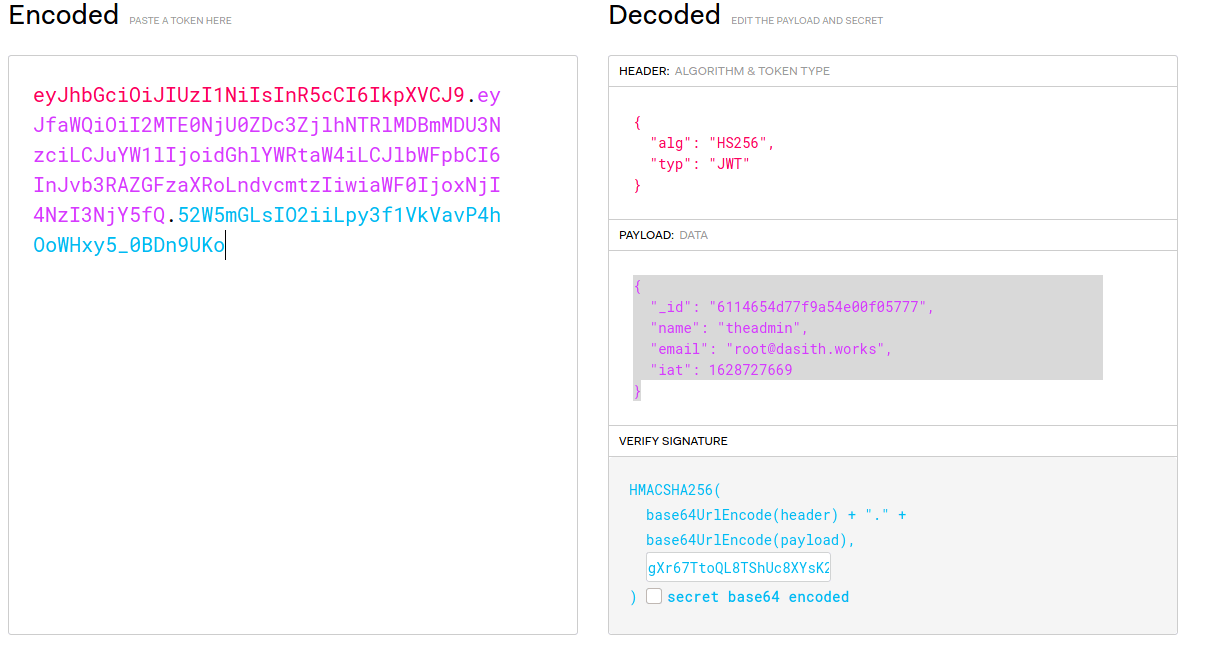
As we can see, .env contains the TOKET_SECRET needed to craft our own JWT token.
Exploitation 1
In order to do so, we can use jwt.io.
Thanks to curl we can see if that really worked.
Exploitation 2
Looking again at the git commits we can see that there is a new feature in order to see logs. This feature is located at ./routes/private.js, where we can see that executes the git command without previous sanitation.
Because this function requires a GET method we need to pass the file name parameter through the URL.
In order to obtain a reverse shell, we can use python3.
Note: Do not forget to change the IP.
Now, we are able to obtain the user flag.
Privilege escalation
At /opt there is a SUID binary which source code can be found at /opt/code.c.
Essentially this code is an implementation of the wc command which counts the number of characters, words and lines of a file. Furthermore, core dumps are enabled so we can retrieve everything that is stored in memory during its execution like the contents of a read file.
To do this, we need to execute the program and live it running after the file has been read.
Then, using another reverse shell we need to kill the program execution by sending a SIGNAL ABORT.
Then, in the former terminal, you will see the message "Aborted (core dumped)".
The core dump will be located at /var/crash/.
Finally, in order to obtain the contents of the root flag, we need to execute the following commands.