OSCP Walktrhough - [Secarmy20]
![Cover Image for OSCP Walktrhough - [Secarmy20]](/assets/images/blog/secarmy20/Secarmy.png)

Introduction
SecarmyOSCP is one challenge of the many CTF challenges that there were in the SecarmyVillage 2020. In this challenge you will have to get 10 flags correspoding each one to a different challenge covering different topics from web to pwn.
Enumeration
First of all, it is needed to scan all open ports that there are in the machine.
In order to know more in depth which services are running inside each port, the next command has been executed.
Based on the previous results the following information has been gathered.
- FTP allows to login clients anonymously.
- SSH service for Ubuntu.
- HTTP stores a web site named "Totally Secure Website".
- 1337 seems to be a Password recovery service.
Flag 1
Accessing to the website appears the following title.
Using gobuster provides the following directories.
Looking inside http://192.168.226.138/anon/ appears another title.
However, at simple view doesn't seem something like a flag, but looking into the HTML (Ctrl+U) code appears the credentials for user uno,which can be used to access to the machine via SSH, where the flag is stored at the home folder.
Flag 2
Reading the "readme.txt" file appears the credentials for the second user. After becoming the user "dos" there is another "readme.txt" file with a quest inside.
To solve it you can use the following commands.
This long string turn out to be an "application.zip" file that you can get using the following website. In order to unzip the file you can use the following command.
Inside the file "todo.txt" there is a special token.
Flag 3
As it has been previously said, there is a service which requires a token to retrieve a password that can be accessed using netcat .
These credentials are used for the FTP service, where there are two files despite the flag.
Flag 4
These files can be downloaded using the following commands.
The hint for the next flag is the following.
Using the tool strings provides the password for the user cuatro.
However, the actual password for user cuatro is "p3dr00l1v4r3z".
Flag 5
In the "todo.txt" file there is the next challenge for the flag 5.
It is a web site with a bunch of QR codes.
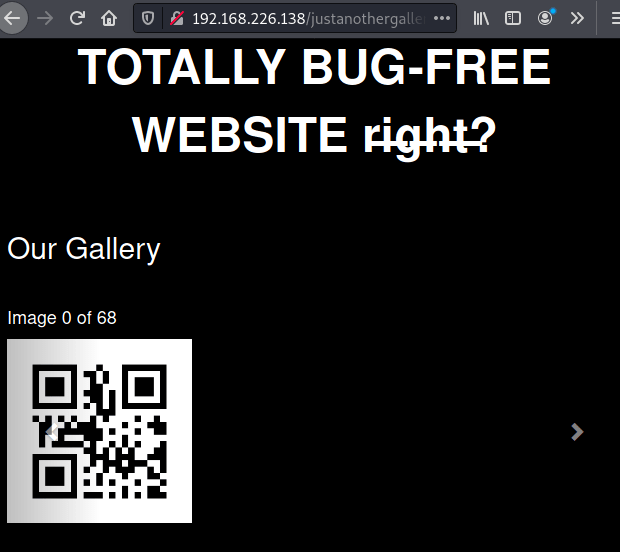
In order to download all of them you need to execute the following command.
Now, in order to decode them you can execute this script.
Between all these lines that appear on the screen, you can get the user cinco's credentials for SSH.
Flag 6
Doing cat in cinco's home directory shows the information for the next challenge.
There is a file in /cinco-secrets/ named shadow.bak owned by cinco but with just write permissions, so in order to read its contents its permissions must be changed using the following command.
The last line can be copied into a new file on our machine so we can extract seis's password using JohnTheRipper. The command will be the following.
Flag 7
The web site looks like this, where we need to find some credentials to access to the Shell CMS.
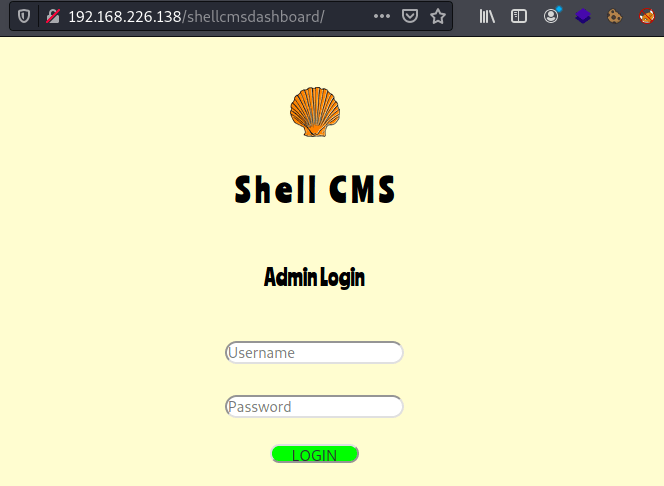
The credentials are stored at the robots.txt file in the following URL http://192.168.226.138/shellcmsdashboard/robots.txt
Introducing the credentials appears a text saying "head over to /aabbzzee.php", accessing to that file appears a users searcher.
It appears to be executing bash commands, because sending "echo 'HOLA' " shows "HOLA" on the we web page, so we can create a reverse shell getting access to the virtual machine. In order to do that we need to write the following command in our virtual machine
and sending this command through the web form (You need to change the IP address).
In the /var/www/html/shellcmsdashboard folder there is a file named readme9213.txt owned by www-data but without read permission. However, changing its permissions we can retrieve the password for user siete.
Flag 8
In the siete's home directory there are several files.
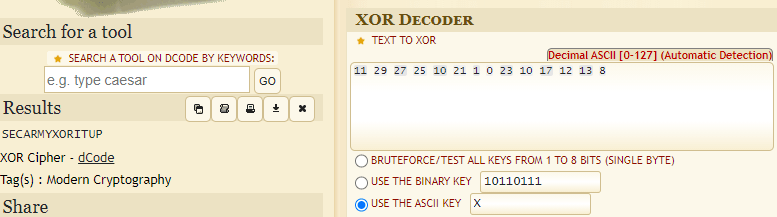
The password.zip file requires a password to get the file password.txt for that you need to decrypt the message.txt using the key "x" (inside the key.txt file). To do so you need to visit the following page.
Flag 9
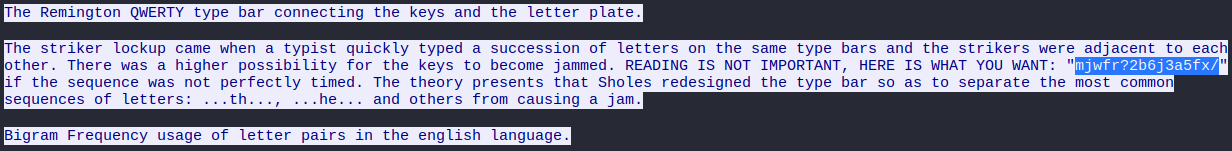
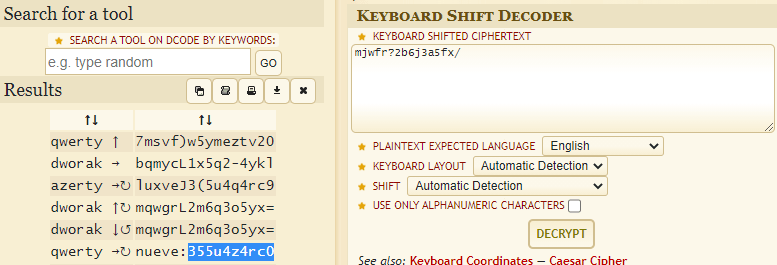
In the ocho's home directory there is a *keyboard.pcapng * that you need to download in order to look what is inside with wireshark. Applying the filer "tcp.stream eq 200".
Then right click into some "GET" package and lick /Follow/HTTP Stream/
Reading the text appears some encrypted stuff which can be decrypted with the following link.
Flag 10
Inside the nueve's home directory there is a binary with SETUID as root.
Using ghidra we can see the source code of the program.
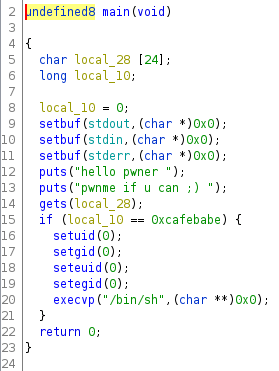
As we can see in the code, in order to get a shell as root we need to write the value 0xcafebabe in the variable local_10. In order to do so we need to produce a Buffer Overflow in the variable local_28 through the method gets. The creation of the payload should look like this. (Python 2)
Then, upload it to the secarmy machine using scp and execute it with the following command, becoming root }:)
Note: If you want to learn more information about **Binary Exploitation I encourage you to read this post.