Seal - [HTB]
![Cover Image for Seal - [HTB]](/assets/images/blog/Seal-htb/Seal.png)

Introduction
Seal is an easy-medium linux machine from HackTheBox where the attacker will have to search for credentials in a gitbucket repository used in a bypass of an URL parser logic from the tomcat service. Then, in order to become root the attacker will have to create symbolic links to obtain luis' ssh private key. Finally, the attacker will gave to create an ansible playbook in order to retrieve the root flag.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
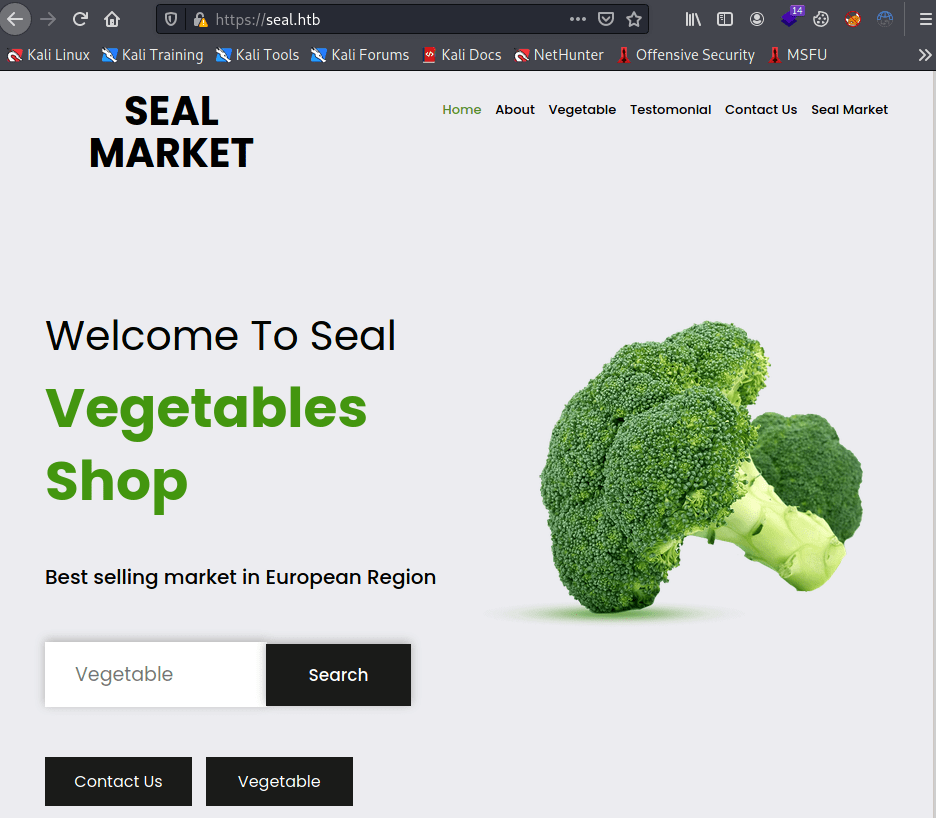
Thanks to nmap we can add seal.htb to /etc/hosts so you will be able to access to the seal market despite not having nothing interesting.
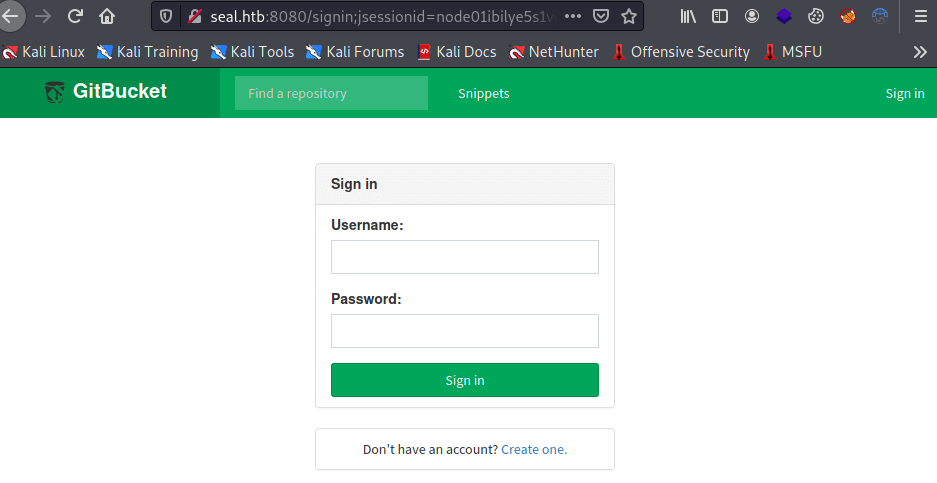
Then, in the 8080 port there is a gitbucket page running. We need to register in order to see what is inside.
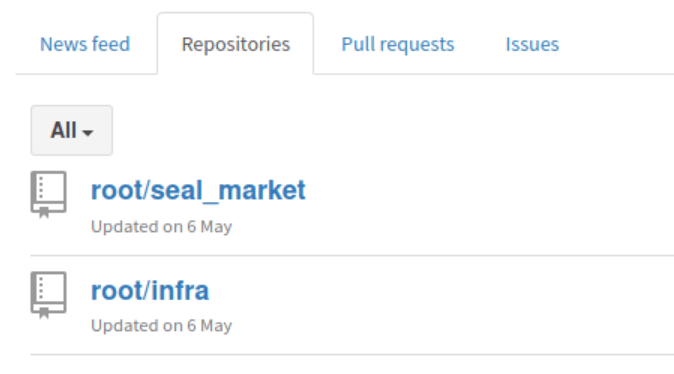
In gitbucket there are two repositories Seal_market and infra.
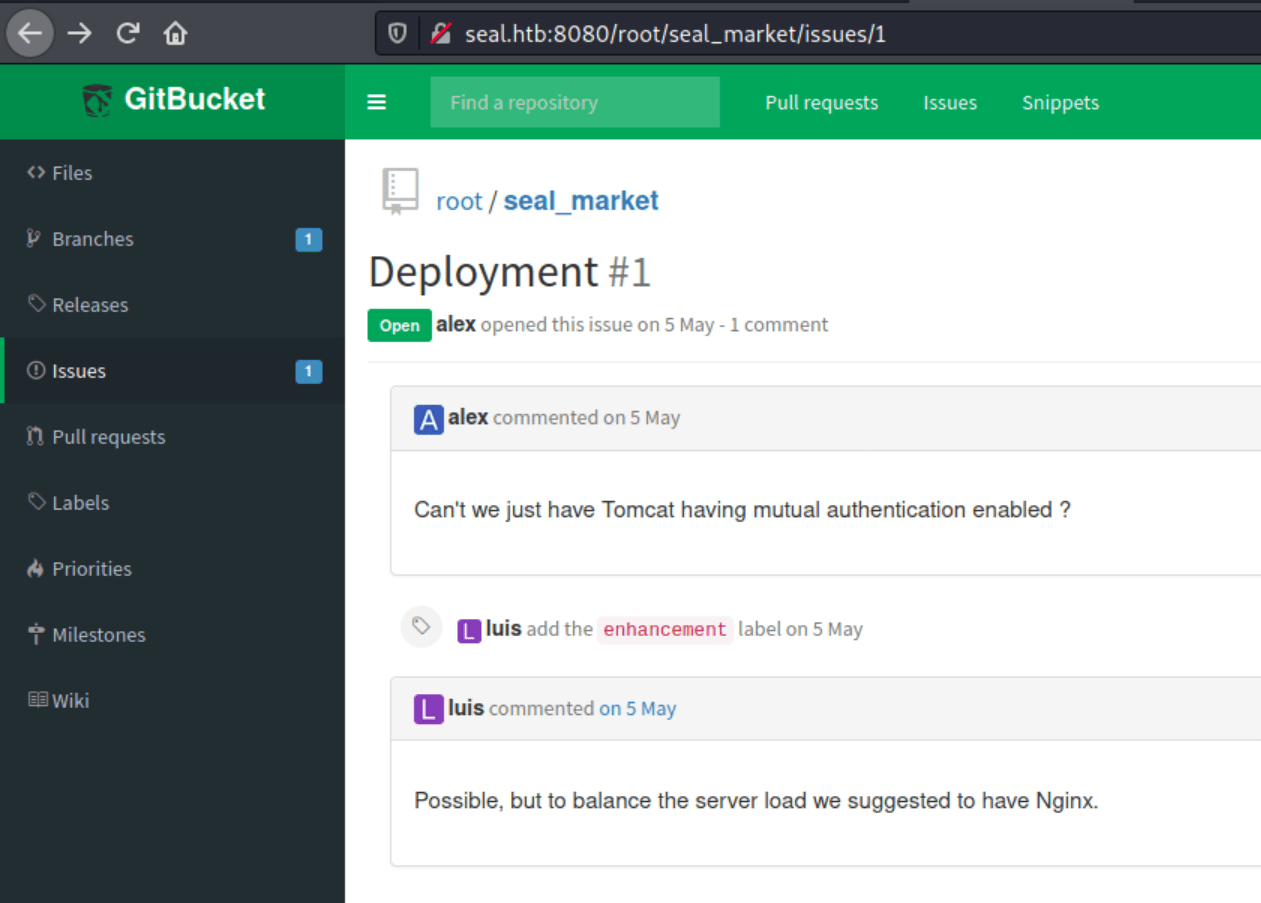
In seal_market there is a issue where we can find another issue about mutual authentication.
Searching through every commit we can find in the commit "Adding tomcat configuration" the credentials for the tomcat manager.
However, we are not able to access to the tomcat's directories: /manager/html and/host-manager/html, due to the following configuration.
Exploitation
Nonetheless there is a way to break the tomcat URL parser logic, as we can see in a blackhat presentation, but basically we can bypass the parser with https://seal.htb/manager/..;/manager/html.
Furtheremore, there is a metasploit module that we can use in order to obtain a reverse shell as tomcat.
Privilege escalation 1
Enumerating the file system there is a special folder /opt/backups where we can find backup files and a run.yml file.
Looking inside run.yml, the script copies each file in the /var/lib/tomcat9/webapps/ROOT/admin/dashboard folder into a gzip file.
Furthermore, inside the dashboard folder there is another folder upload where we have write permissions.
Hence, symbolic link files can be added to the uploads folder retrieving the actual files once the run.yml is being executed.
The commands are the following.
As we can see in the picture below we obtained successfully both files.
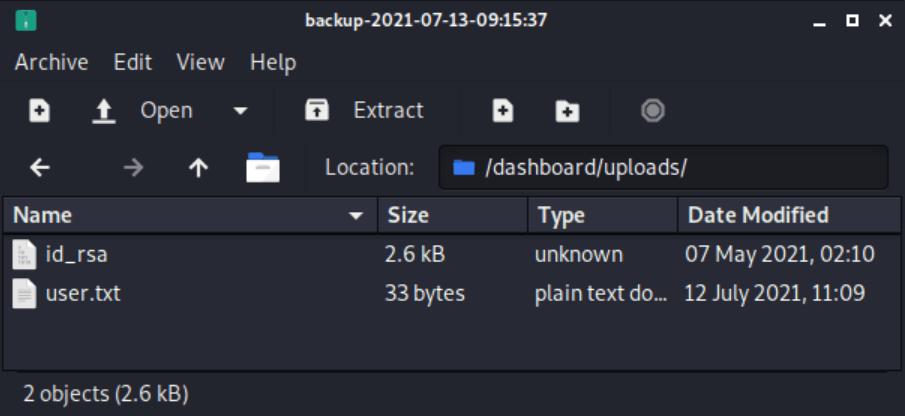
Once the id_rsa file has been extracted,it can be used for getting access as luis through SSH.
Privilege escalation 2
The user luis can execute the following python script as root.
Thanks to the examples in this post we can create our own run.yml which will allow us to connect to the machine as the root user through ssh.
Note: Create you own ssh id_rsa.pub key in order to add it to the file.
In order to obtain the root flag, execute the script and then connect to the machine as you can see below.