ScriptKiddie - [HTB]
![Cover Image for ScriptKiddie - [HTB]](/assets/images/blog/ScriptKiddie-htb/ScriptKiddie.png)

Introduction
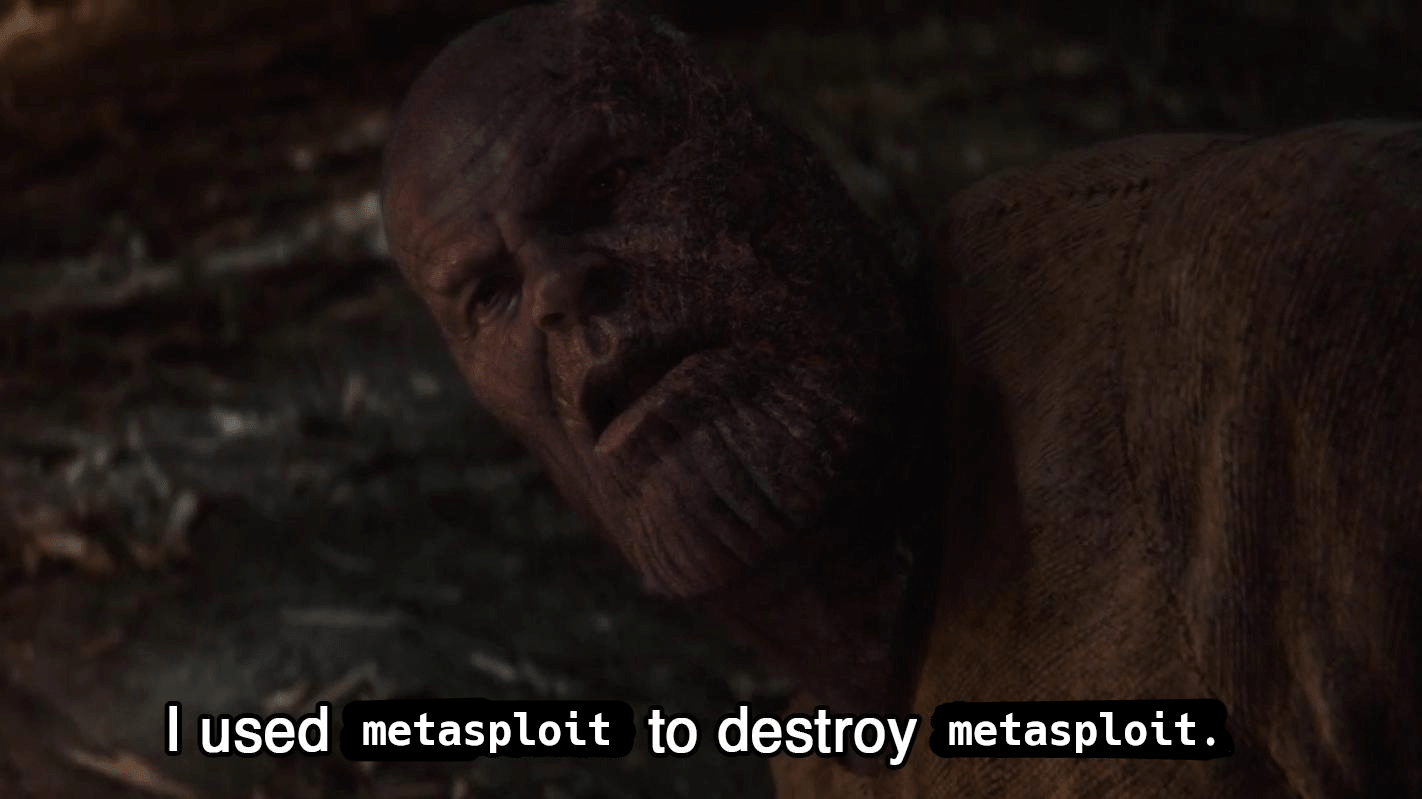
Script kiddie is an easy Linux machine from Hack The Box where the attacker will have to exploit a vulnerability for msfvenom inside the service Werkzeug to become the user **kid^. Then, will have to modified the behaviour of a script via improper input validation in order to get a shell as the user pwn. Finally, will have to execute metasploit to become root.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
As we can see, there are two opened ports and one of them seems to be an http service.
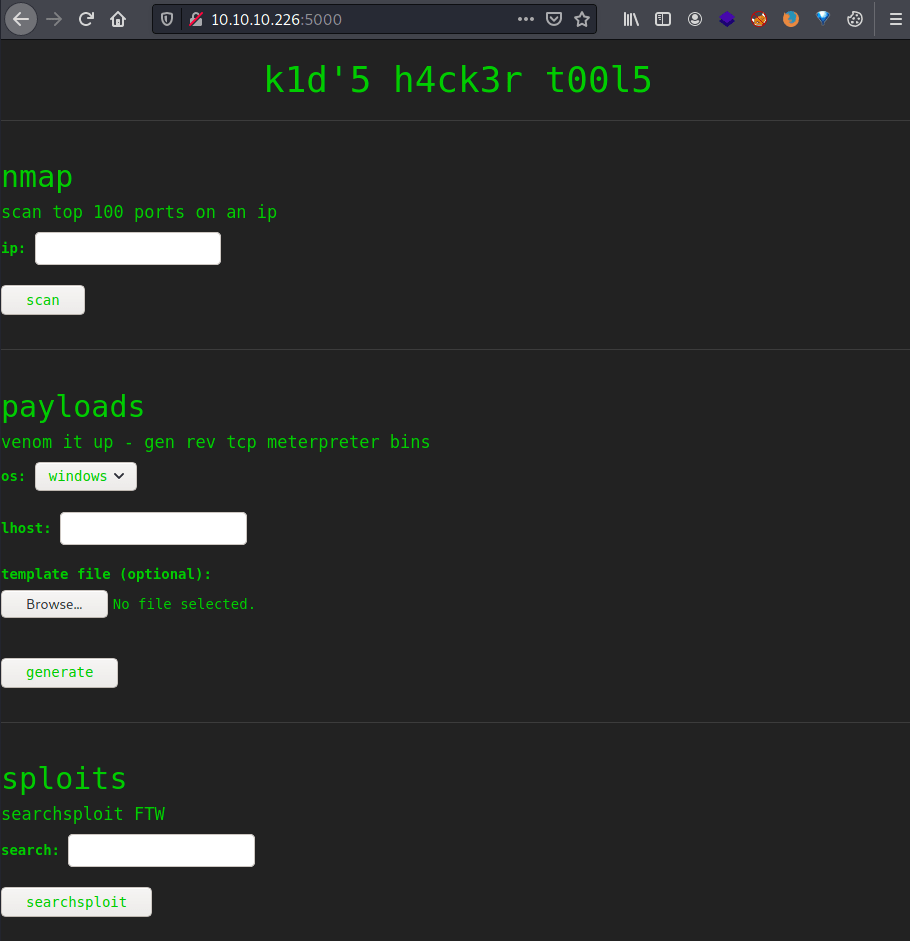
It seems like the web page is being used for doing attacks against the specified IP.
After a while, it seems that it isn't vulnerable to any kind of command injection in any kind of the forms. However, it uses the template file as a parameter for the msfvenom, which has an associated vulnerability in exploit-db which has an associated metasploit module.
Explotation
Using msconsole we can create an infected template apk file that we can upload to the web page in order to retrieve a reverse shell. The only parameter we have to change is the LHOSTand LPORT(4444 by default).
Then, we need to upload the file indicating the specified os as android and introducing a valid IP.
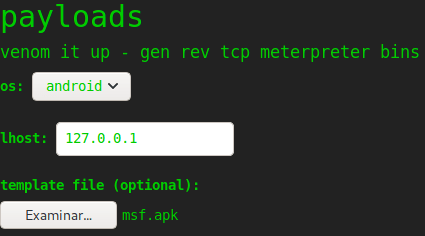
Finally, we obtain a reverse shell as the user kid.
Privilege escalation 1
Inside the home folder there are two users: kid and pwn.
For one side, inside the kid's home directory there is a folder named logs with an empty file named hackers.
For the other side, in the pwn's home directory there is a script named scanlosers.sh with the following content.
Using pspy64 we obtain that the script is being executed by the user id 1001 (pwn) once we modified the hackers file.
Furthermore, the input of the file isn't checked so we can put anything we want in it. Hence, if we put a ; at the beginning and a # the end of our command; the script will execute cat without parameters, so our command (Reverse shell) and nothing else.
Privilege escalation 2
Once we got our reverse shell as the user pwn we need to become root.
In order to do so, I upgraded my shell in order to see if the user pwn can execute any command as root, which turns out to be true.
Finally, we only have to execute the metasploit framework, executing a shell once inside.
I hope you liked this easy box if you need to ask me anything contact me through my social networks :P