Scrambled- [HTB]
![Cover Image for Scrambled- [HTB]](/assets/images/blog/Scrambled-htb/Scrambled.png)

Introduction
Scrambled is a medium Windows HackTheBox machine where the attacker will have to enumerate usernames on a DC to get an account with default credentials. This account can be used to retrieve a TGT from a SPNService, giving the attacker access to an MSSQL database with credentials on it. Furthermore, it will have to execute commands on the database to obtain a reverse shell.
Finally, the attacker will have to find an object deserialization on a .NET application, that can lead it to get a reverse shell as administrator on the machine.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Inspecting port 80, there is a web page talking about an intranet site.
Then, at the "IT Services" tab, there is the following text. Giving us a hint that the machine is not NTLM hash stuff, so it could be related with Kerberoes.
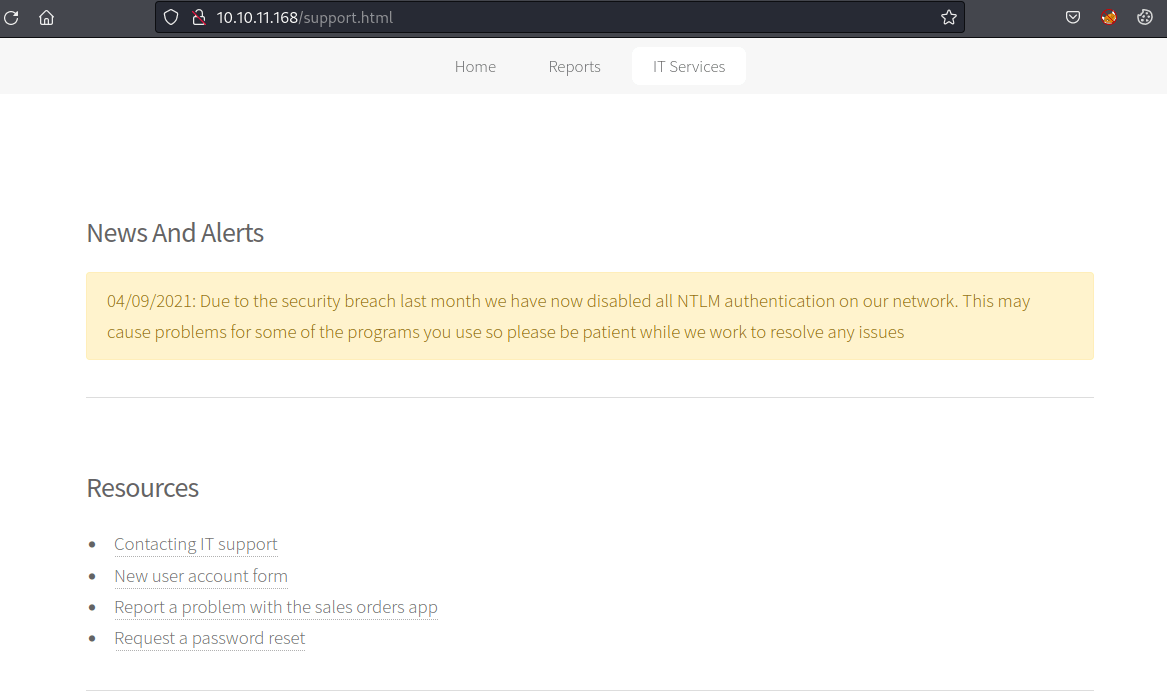
Furthermore, on the same page, there is a text talking about a password reset system which requires a username.
In order to find a username, we can use kerbrute and a good username wordlist.
Then, trying each username as a password, we can find that the user "KSIMPSON" its username it's also its password.
Because NTLM Authentication has been disabled, let's try to obtain a TGT.
Using the ticket, we can obtain the Service Principal Name of the account, which is an MSSQL service.
Note: The GetUserSPNs has an unfixed issue when using Kerberos credentials from a ccache file. So, to fix this error you need to edit the file GetUserSPNs.py changing target = self.__kdcHost by target = self.getMachineName(). Moreover, you need to use the domain in the -dc-ip parameter to make it work.
Then, using john, we can crack the password, which will get us handy in the future.
Furthermore, we can gain access to the shares available in the domain.
The only share that we have access to is the "Public" share, where we can obtain a pdf file.
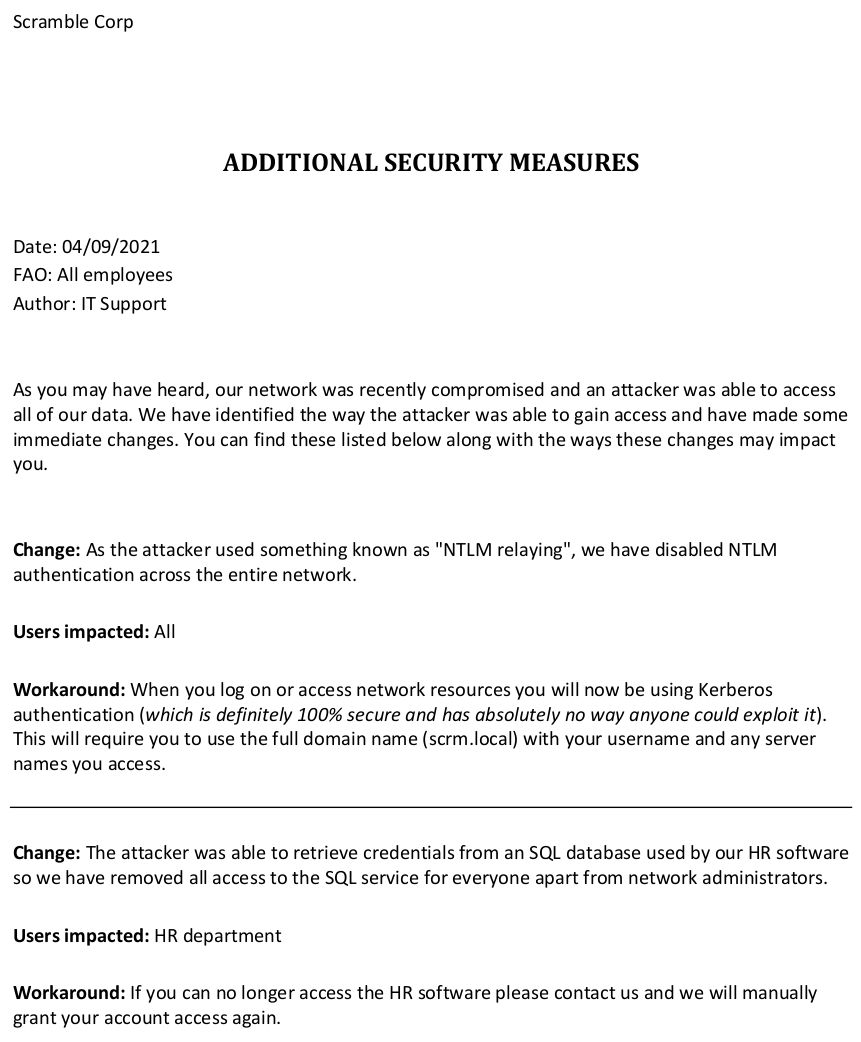
The PDF exposes the following:
Exploitation 1
As it says in the document, the attacker was able to access the SQL service using the NTLM relay. So, they have disabled the use of NTLM, allowing only Administrators using tickets to access the SQL service.
Because we were able to obtain the password for the SQL service earlier, we can create a Silver Ticket as the user Administrator. However, we need to obtain the SID of MSSQLSVC.
For doing so, there are two alternatives:
Then, we need to convert the cracked password into NTLM format.
Finally, we can create the Silver Ticket with the following command.
Now, we should be able to access the database.
Enumerating the database, we find other user credentials.
Exploitation 2
In addition, if we enable the de xp_cmdshell module, we can execute commands on the machine.
In order to get a reverse shell, you can use the "PowerShell #3 (Base64)" from revshells.com.
Now, we need to create another reverse shell in order to become MiscSvc, obtaining the user flag.
For doing so, execute the following commands:
Privilege Escalation
Looking in the Shares folder appears the following application.
For doing so, we can use Powercat to download the files. Then, to check if the files were downloaded successfully we can use sha256sum.
Using dnSpy to decompile the DLL we can find the codes used by the application at port 4411.
As we can see there are two special commands LIST_ORDERS and UPLOAD_ORDER.
Decoding the base64 seems to be an object (Do it by yourself because there is a lot of junk data). This can be confirmed based on the following tests.
After some trial and error, we could use the ysoserial.net payload to ping our host.
Finally, in order to obtain a reverse shell, we can use the same payload from revshell and execute the same command.