RouterSpace - [HTB]
![Cover Image for RouterSpace - [HTB]](/assets/images/blog/RouterSpace-htb/RouterSpace.png)

Introduction
Router Space is an easy Linux machine from Hack The Box where the attacker will have to perform dynamic analysis of an Android application to discover an endpoint vulnerable to Remote Code Execution. Finally, it will have to exploit the baron (CVE-2021-3156) vulnerability for becoming root.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Looking at port 80 appears a web page where we can download an application.
Using [dex2jar](https://sourceforge.net/projects/dex2jar/files/dex2jar-2.0.zip/download?use_mirror=jztkft\&r=https%3A%2F%2Fsourceforge.net%2Fprojec ts%2Fdex2jar%2Ffiles%2Flatest%2Fdownload) for static analysis is not useful for this machine. So we need to continue with a dynamic analysis.
To do so, we can use anbox to emulate an Android device and install the application.
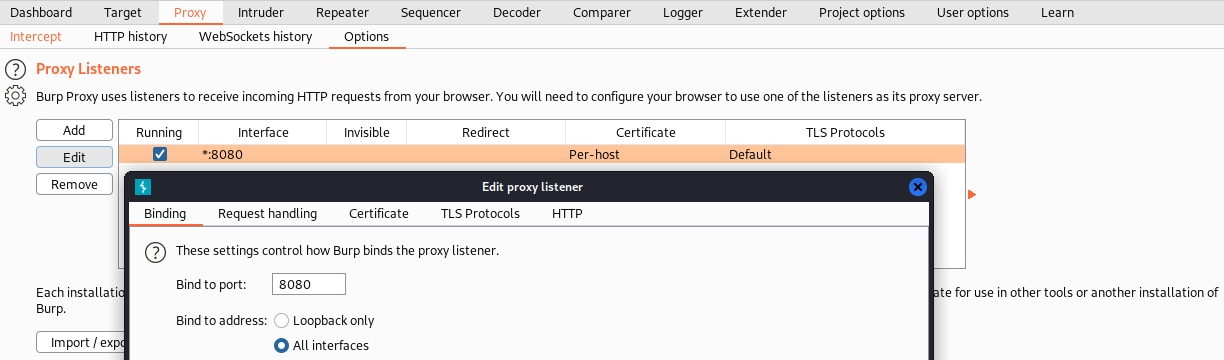
After installing anbox, we can install the application on the emulator and proxy all web requests through Burp Suite.
Finally, we need to set up burp suite to listen on all interfaces.
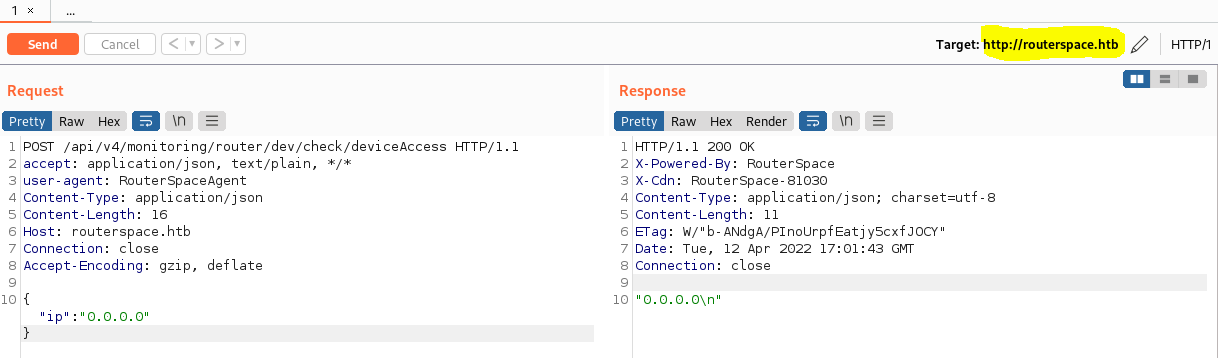
After accessing the application, we receive a web request with a JSON string, which responds an IP.
Exploitation
After some trial an error we can see that is vulnerable to command injection.
Request:
Response:
In order to obtain a shell, we need to append our public ssh key into paul's authroized_keys file.
Then we can access the machine as Paul through SSH.
Privilege Escalation
To escalate privileges we can use linux-exploit-suggester in order to find vulnerabilities on the system.
In this case, the machine is vulnerable to CVE-2021-3156.
After compiling and executing the exploit we become root.