Reel2 - [HTB]
![Cover Image for Reel2 - [HTB]](/assets/images/blog/Reel2.assets/Reel2.png)

Introduction
Reel2 is a hard Windows HackTheBox machine where the attacker will have to craft some credentials for a phishing attack. Then, he or she will have to crack a NTLMv2 hash to get login in the machine, obtaining the user flag. Finally, in order to become root, the attacker will have to play with a powershell session and symbolic links in order to get access to the root's desktop.
Enumeration
As always, let's start checking if there are some opened ports.
Then, we continue scanning all open ports.
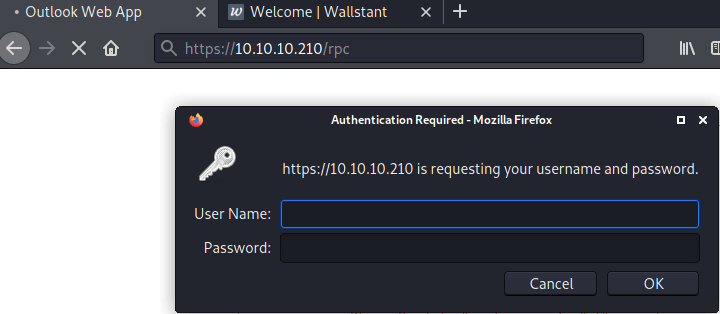
Launching dirbuster to port 443, we can discover several directories.
However, the only ones that we should care about are /rpc and /owa.
Furthemore, at the 8080 port there is a social network application.
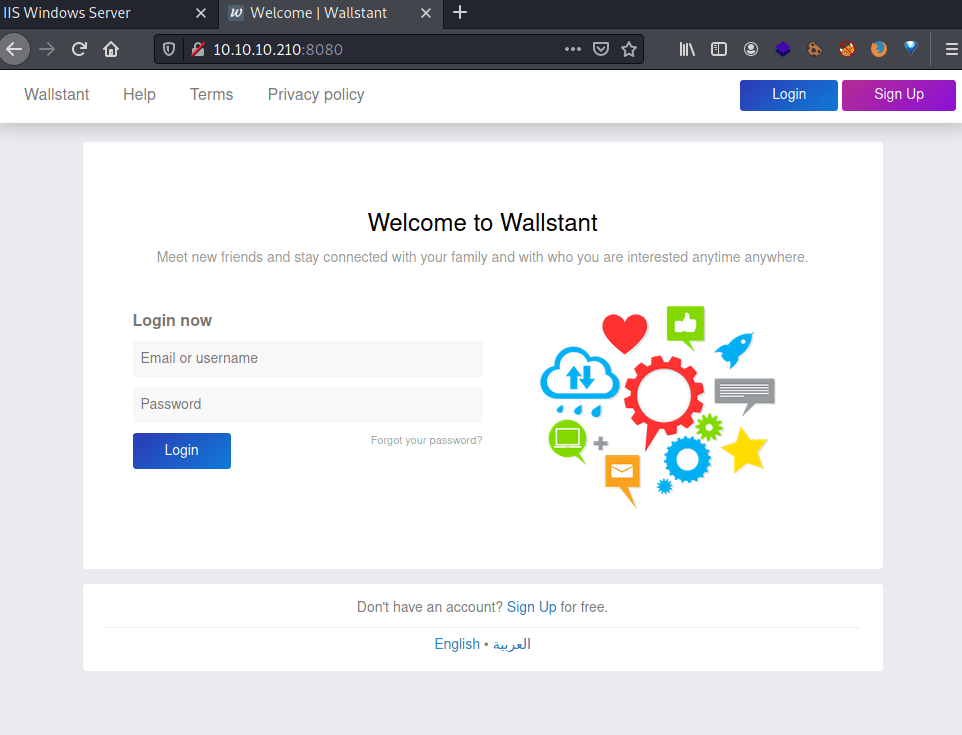
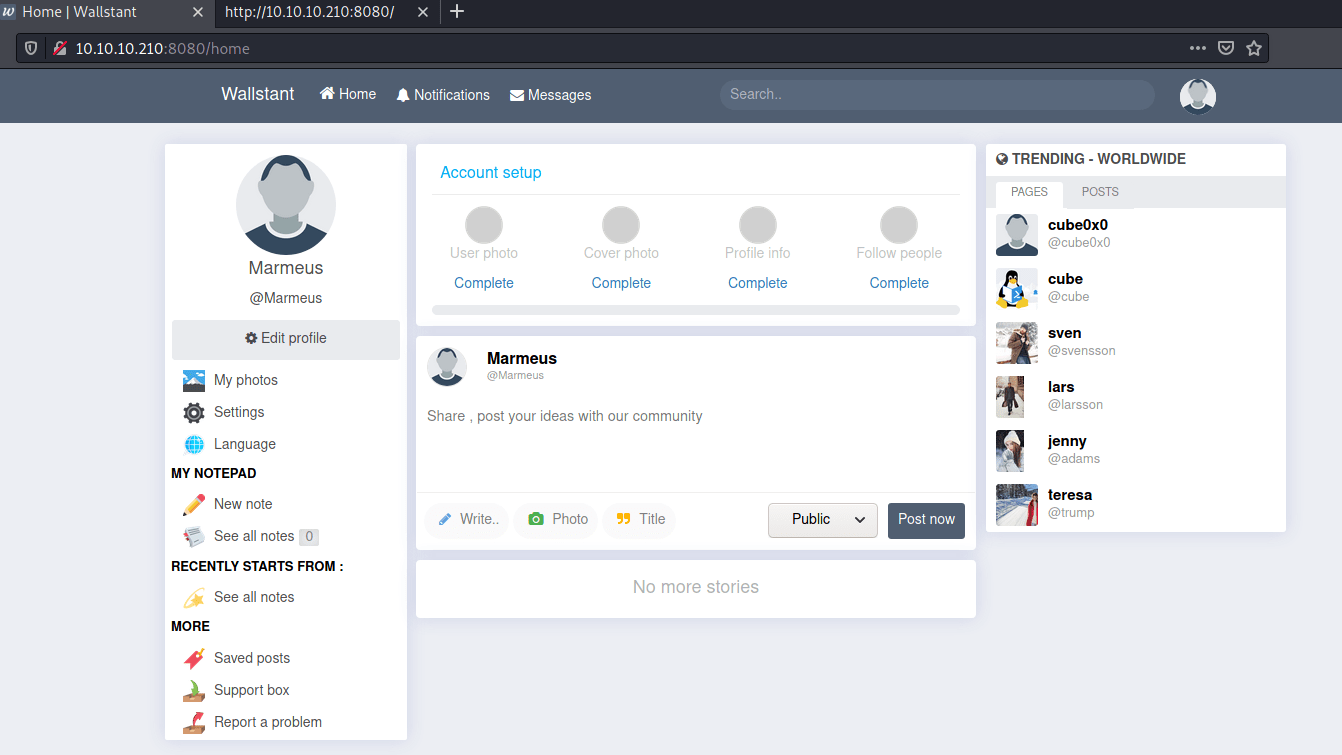
Because, the machine's icon show some fishing rods, it seems that we need to do some kind of fishing attacks in order to impersonate somebody. Moreover, the social network application doesn't seem vulnerable to any kind of exploit. Hence, let's try obtaining some credentials by gathering information at "Wallstant".
At http://reel2.htb:8080/search we can obtain all users registered at "Wallstant", with the following JavaScript.
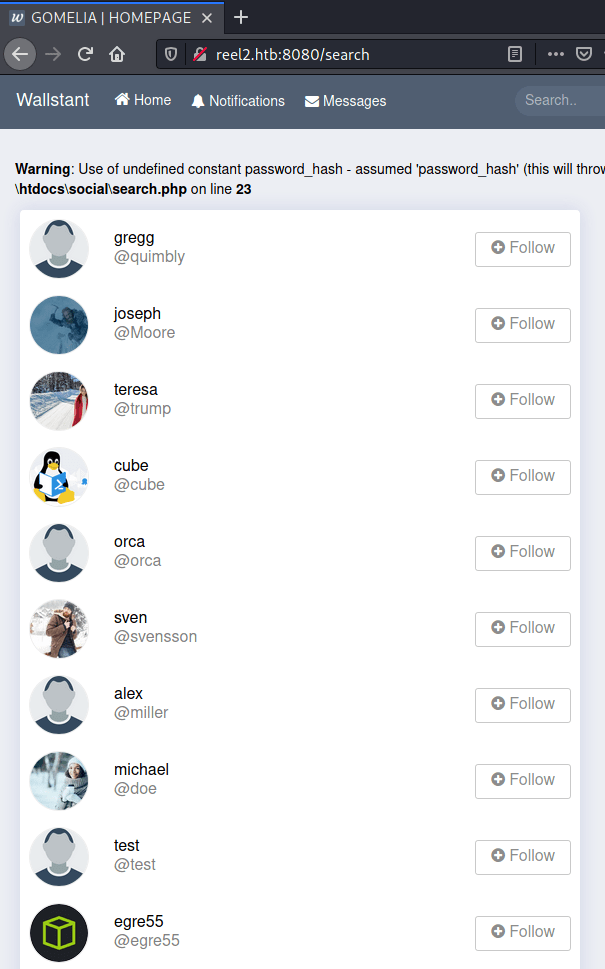
However, we are only going to keep the usernames who have an associated post on the social network, because they seems to be active in the machie. These usernames are going to be used to create a username list with hashcat.
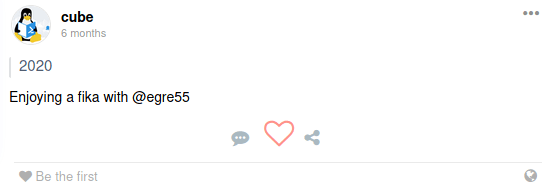
Furthermore, we are going to use the words inside each post with the purpose of creating possible passwords with hashcat that would be used against the users before mentioned.
Obtaining credentials
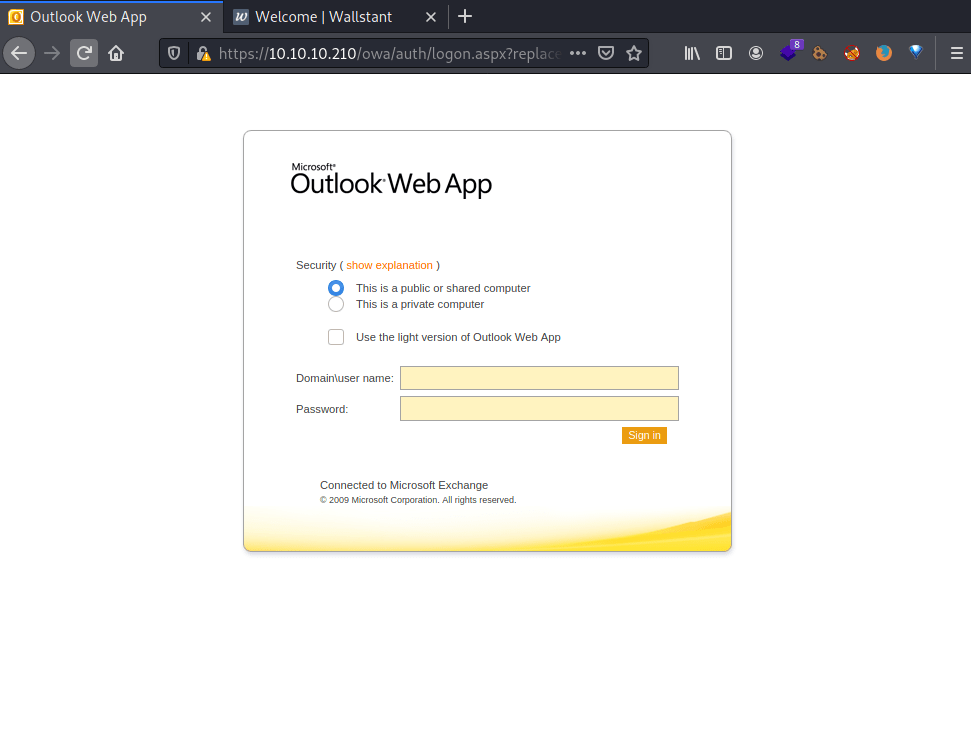
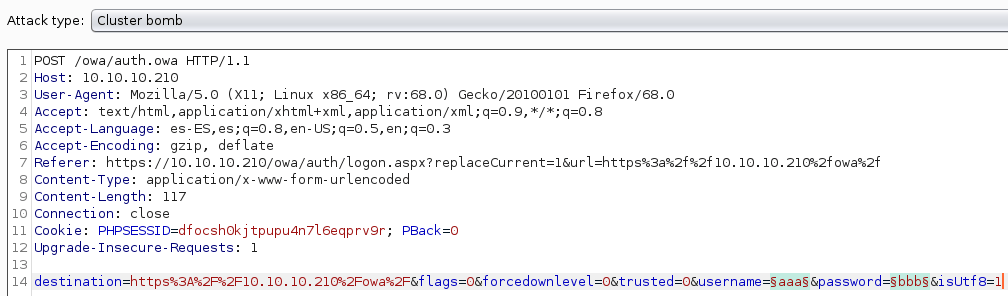
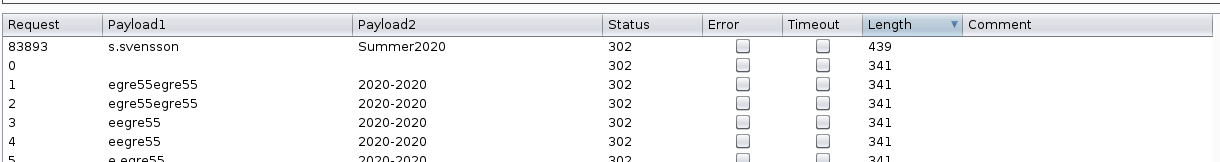
Using the generated credentials and the Cluster Bomb attack of the tool Burpsuite against the URL /owa/auth.owa, we obtain the credentials:
Phishing attack
Note: The Outlook Wep App is in Swedish, but do not worry I will guide you so you will be able to do the attack as well.
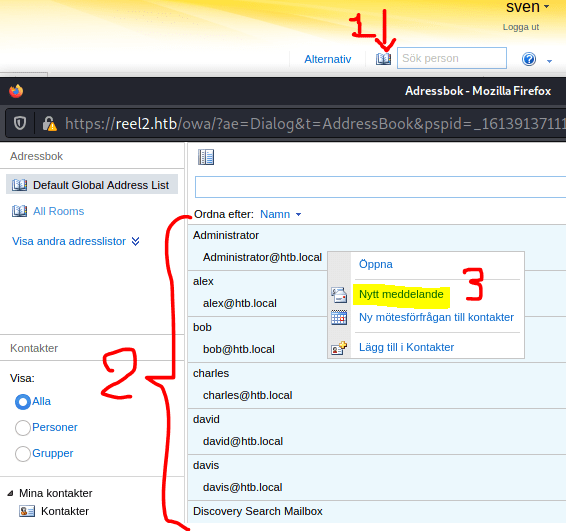
The attack in question is an Outlook phishing attack used by attackers to obtain the victim's NetNTLMv2 hash. Moreover, clicking in "Address Book" we obtain a lot of email addresses, that they will be our victims in this attack.
Note: In order to send an email: first, click on the "Book"; secondly, select all the users using Ctrl or Shift, thirdly, right click in a contact and finally click on "Nytt meddelande" and "Ja".
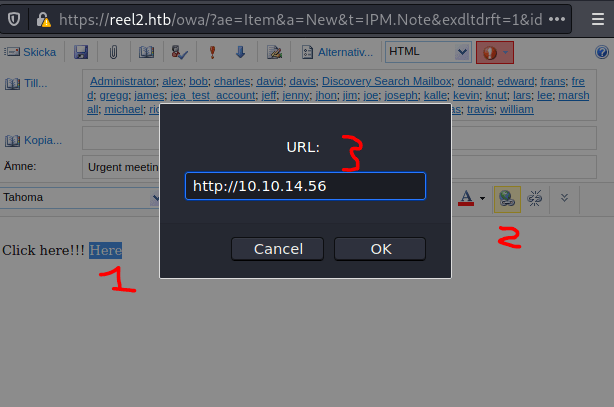
Execute responder with the VPN interface.
Finally, send an email with a attached link that points to your machine.
The result is an NTLMv2 credential.
Using hashcat we can retrieve the actual password.
Remote Code Execution
The port 5985 is opened so we can use evil-winrm, but it shows the following error.
Nonetheless, we can use Powershell in order to execute commands remotely on the machine, obtaining the user flag.
Note: You can install powershell with following command.
Note1: The powershell commands must be written inside a script block.
Post explotation
Because, I didn't want to write every time the script block I uploaded a 64 bit windows netcat using the python http module and powershell.
Inside the k.svenssons's desktop there is a windows sticky note, thus going to the sticky notes local storage appears to be a log file named 000003.log.
Using Get-Content shows to little despite the quantity of bytes it has.
Hence, I encoded it using base64 so I could download it to my machine, for a later analysis with the command strings.
Now, we have another pair of credentials, that can also be used for login with powershell.
However, we need to do it in an alternative way.
Furthermore, we can not execute any command due to no-language mode.
Nevertheless, there was a couple of config files at the k.svensson' s Documents folder.
For one side, in the jea_test_account.psrc file we can see the definition of the function Check-File which checks if exists any file in the D: drive, which doesn't exists, or in the C:\ProgramData folder, which exists, and shows its contests.
For the other side, in the jea_test_account.pssc file we can see: why the jes_test_account is being executed as administrator and the set up of no-language mode.
Therefore, we can deduce that we can read as Administrator any file inside the C:\ProgramData folder using the jea_test_account powershell account.
Privilege escalation
Because we have write permissions with the user k.svensson we can create a symbolic link of the Administrator's desktop, thus we can read the root.txt file.
To tackle this problem we are going to use the cmd terminal, so we can create a folder symbolic link.
Then, we only have to come back the powershell session as jea_test_account, executing the function Check-File passing as argument the path of the root.txt file, obtaining the root's flag.
Finally, I would like to thanks xavilok, who helped me completing the machine.