RedPanda - [HTB]
![Cover Image for RedPanda - [HTB]](/assets/images/blog/RedPanda-htb/RedPanda.png)

Introduction
RedPanda is an easy Linux machine from HackTheBox where the attacker will have to find a Java SSTI on a search engine. Then, it will have to analyse a Java program, which is being executed every two minutes by root. Finally, it has to exploit an XXE vulnerability to obtain the root's SSH private key.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
At port 8080, there is a little search engine for different types of pandas made with Spring Boot.
Furthermore, through some file enumeration, appears a statistics page.
On this page, the statistics of the authors woodenk and damian can be obtained and exported in XML format.
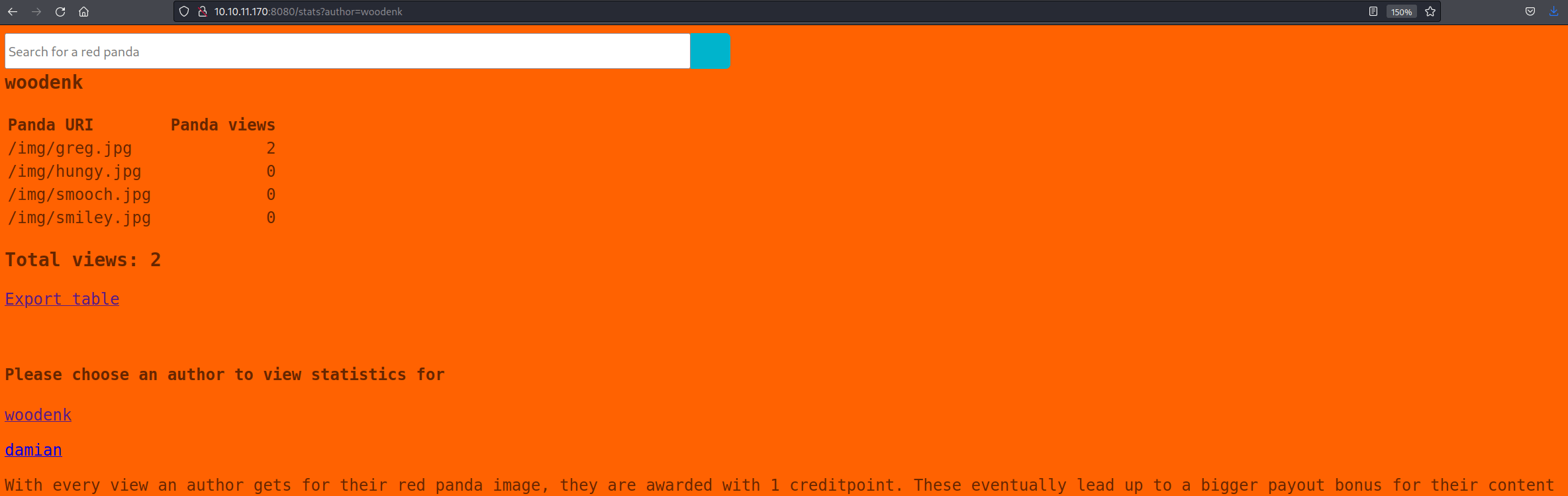
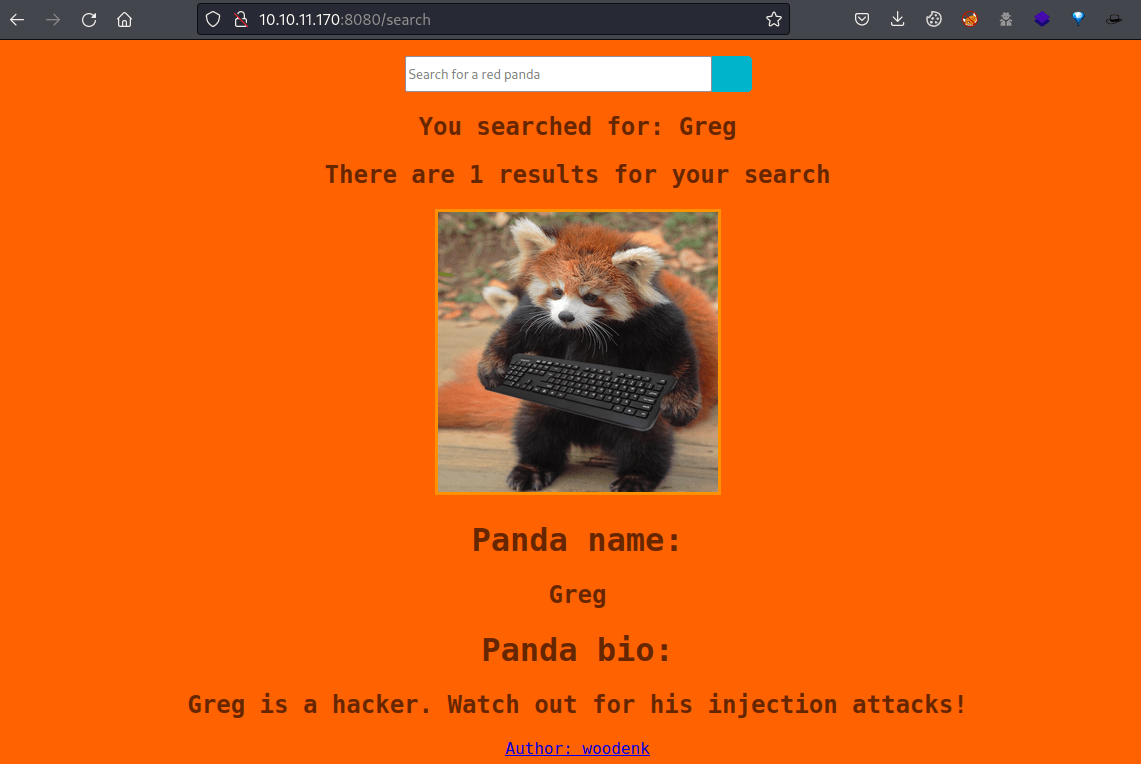
Finally, the Greg panda appears if no input is inserted, telling that the search engine might be vulnerable to injection attacks.
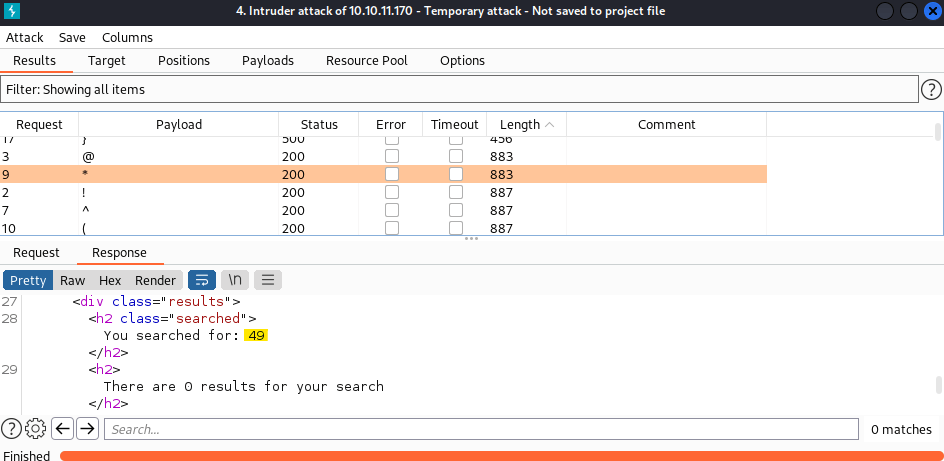
After fuzzing the search engine using the wordlist special-chars.txt from SecLists and URL encoding its characters, the following output is obtained.
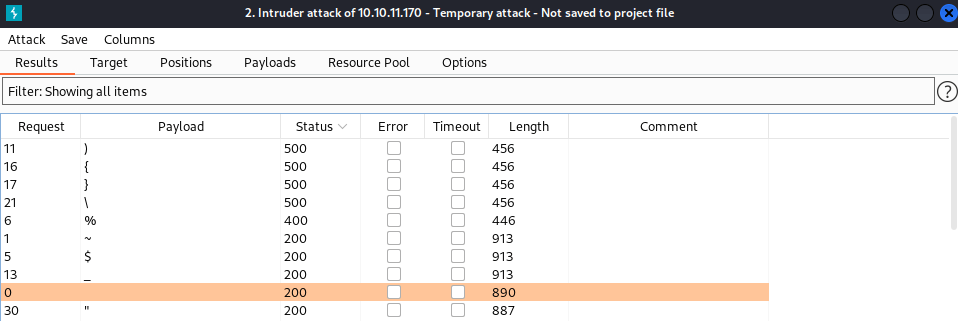
Because the characters ){}\% produced errors when sent to the server, and the characters ~$_ are banned for the engine, it might be vulnerable to SSTI.
To verify that, the following payload was used §character§{7*7} (encode characters before executing intruder). As a result, it seems that the code inside *{<CODE>} is being executed.
Exploitation
Then, because Spring boost is made with Java, STTI Java payloads are needed. These payloads can be found on PayloadAllTheThings.
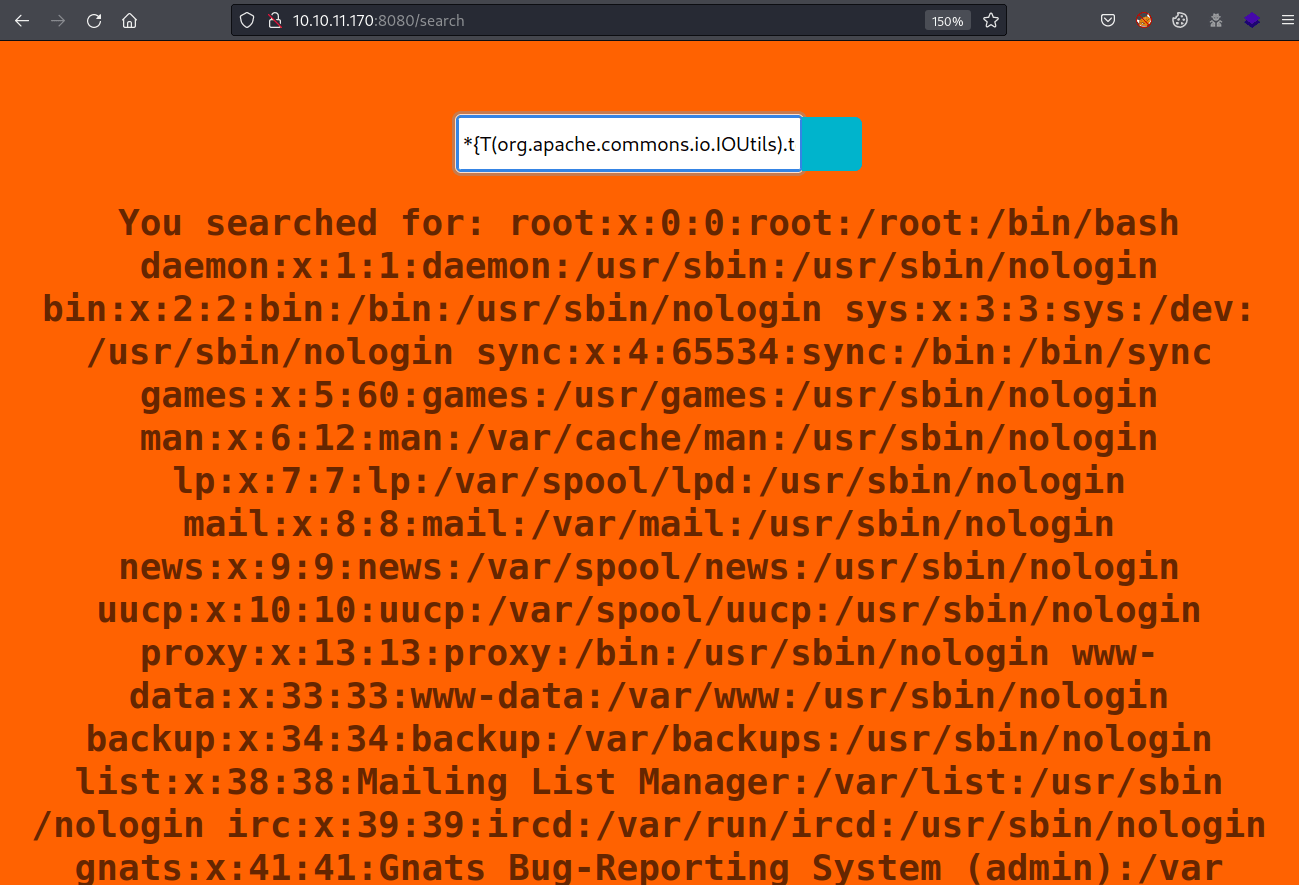
Because this payload requires encoding every single character to be executed, to facilitate the work, the tool SSTI-PAYLOAD is used.
Note: I changed the script to always return *{ instead of ${.
Because no reverse shell can be obtained, manual enumeration of the machine must be performed using the web form.
Looking inside the Panda search source code, there are some database credentials.
These credentials can be used for getting access to the machine through SSH, obtaining the user flag.
Privilege Escalation
Using pspy we can see that every two minutes the Java file final-1.0-jar-with-dependencies.jar is being executed as root.
This Java application file has the source code located at /opt/credit-score/LogParser/final/src/main/java/com/logparser/App.java .
Starting from the main function, we can see that it reads the log file /opt/panda_search/redpanda.log, parses some data and then reads an XML file.
A look at the log parser; the program splits a log line into a string using || as a separator. So, because the attacker has control over the User-Agent HTTP parameter, the uri value can be overwritten.
The uri value is used in the function getArtist, appending the value to an image path for reading the Artist metadata attribute.
Finally, the artist value is appended to another path, which is being used at the function addViewTo.
This function reads the file, updates the counter of each image view and then overwrites the file with the new values.
Because there is no measure to avoid XXE and we have control over the parameters user_agent, uri ,artist and xmlPath; maybe we can create an XML file with XXE to read the root's private key.
First, obtain an image and update its metadata.
Then, we need to edit a statistics XML file to add the XXE payload.
Finally, update all the files and send a request with the malicious user agent.
After two minutes, the script will be executed, and the XML will be modified, adding the root's private key.
Finally, it is possible to access the machine as root, obtaining the root flag.