Ready [HTB]
![Cover Image for Ready [HTB]](/assets/images/blog/Ready-htb/ready.png)

Introduction
Ready is a medium Linux Docker GitLab machine from HackTheBox where the attacker will have to exploit a SSRF in order to get a reverse shell, then will have to do some enumeration to get the Docker's root password for a later generation of a file system or produce a command execution in order to get the root flag.
Enumeration
As always, let's start finding all opened ports in the machine.
There are just two opened ports. Let's do a deeper about the opened ports.
The port 5080 seems to be a web server, which turns out to be an Git Lab web page.
Creating an account and looking at the GitLab version we can see that it isn't updated.

With a quick search on Google, you can arrive to the following exploit, explained by the famous YouTuber LiveOverflow.
Explotation
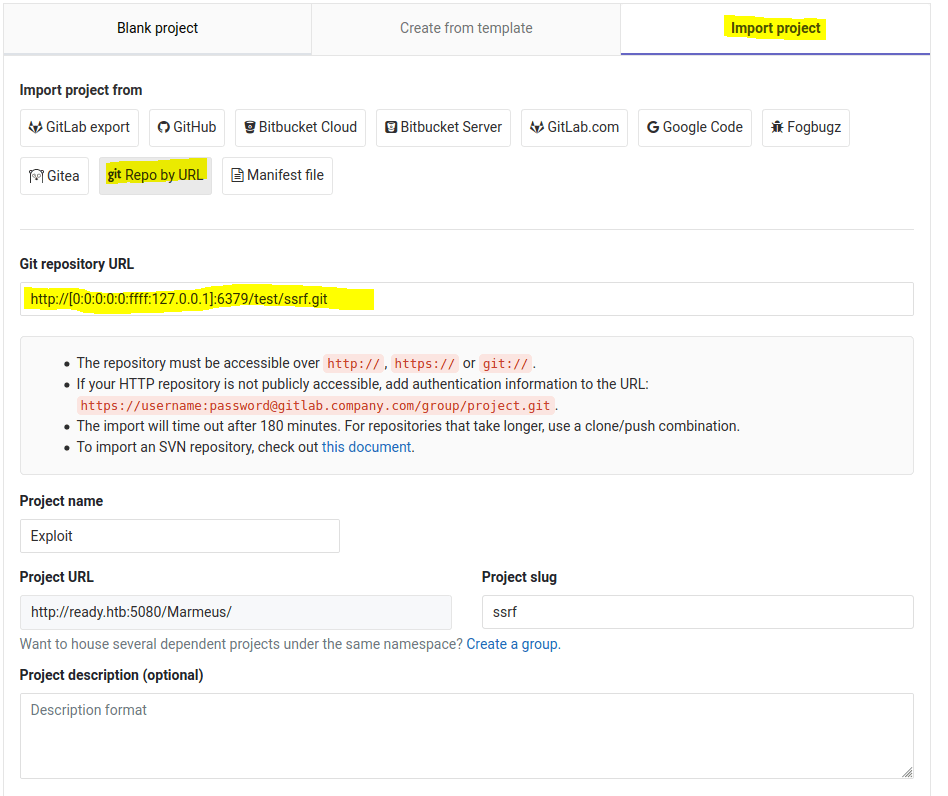
In order to get a reverse shell, we need to create a new project by importing it using an URL (Create new project/ Import project / Repo by URL). Then, we fill the gaps in the form, adding the following Git repository URL git://[0:0:0:0:0:ffff:127.0.0.1]:6379/test/ssrf.git, as you can see below.
After that, we need to intercept the form request using Burpsuite.
In order to get a the reverse shell we need to encode the following payload like an URL, changing the IP and port where the reverse shell will connect to.
The result is the following.
Now we have to overwrite the data in the variable import_url%5D= by the payload we have just created. The resulting request will look like this.
Finally, we just have to create a listening port and forward the request in order to get the shell.
Privilege escalation
Shell upgrade
Because the shell isn't tty, we have to upgrade it manually to get it work properly. For that you just need to execute these commands.
Enumeration
Looking for passwords in the /opt/backup directory, we can find a password for an SMTP service.
These credential can be used to become root in the Docker container.
Escaping the container
Reading the docker-compose.yml we can see that this container has been created setting the privileged flag to true. This means that this container has root capabilities in the host machine, allowing us to access resources which are not accessible in ordinary containers.
There are several ways to get the root flag from despite being in the container, we are gonna cover both.
Command execution
Thanks to this post we can find a way to execute commands on the host machine, obtaining the the output of the commands, in our case the cat command. To do so, you only have to execute the following commands.
Furthermore, this exploit can be used to get a reverse shell as the root host.
Mounting a file system
The easiest way to get the root flag is by mounting the host file system in a folder we have just created, so we can navigate all over the Linux file system as root. The commands are the following.