Previse - [HTB]
![Cover Image for Previse - [HTB]](/assets/images/blog/Previse-htb/Previse.png)

Introduction
Previse is an easy linux machine from HackTheBox where the attacker will have to intercept web server responses in order to create an administration account, allowing to download a web service backup file. Later will have to analyse the web application finding a path for an RCE. Then, will have to crack the credentials stored in a mysql database so you can obtain the root flag. Finally, the attacker will have to use the path hijacking technique in order to become root.
This machine has an unintended way through SQLi so you do not need RCE. If you want to see how is done check xavilok's post.
Enumeration
As always let's start scanning all opened ports in the box witth nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
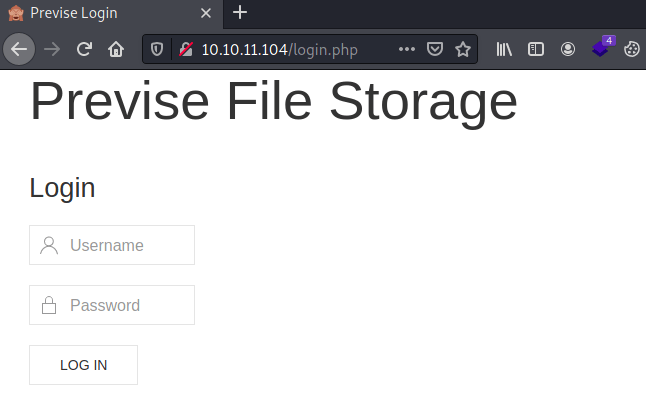
Trying to access to port 80 the web service always redirect us to login.php.
Using gobuster we can obtain the following files, that if trying to access them redirect us again to login.php.
Exploitation 1
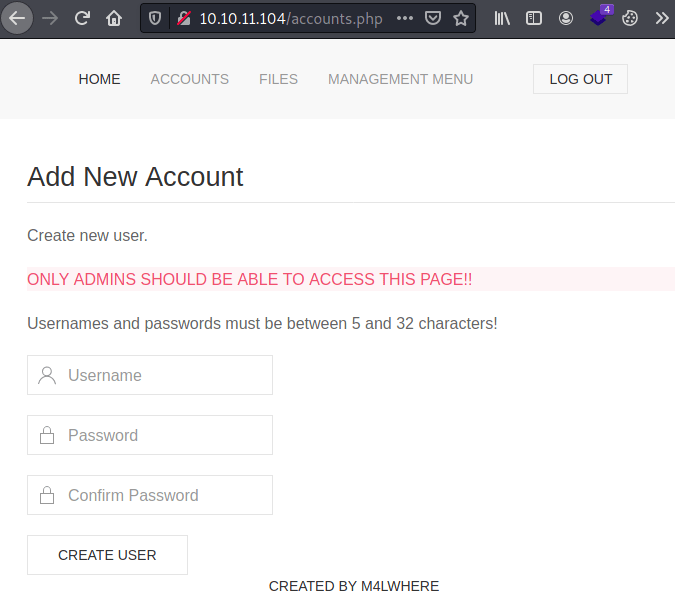
However, trying to access to accounts.php we can intercept the server's response with BurpSuite (Right click request / Do intercept / Response to this request), observing the existance of the Location header responsible for always rederecting us to login.php.
Removing the header and forwarding the request we can see the contents of accounts.php, allowing us to create an administrator account.
Now, we can access to files.php where we can obtain a file named SITEBACKUP.ZIP.
Once downloaded, extracted and analysed the web contents. At config.php we can obtain the mysql credentials.
Inside the file logs.php we can see that its executing a python script passing as a parameter the contents of the post form from file_logs.php.
Exploitation 2
Intercepting the post request we can add the following command, obtaining a reverse shell as www-data.
Privilege escalation 1
Because we have the mysql credentials we can obtain the registered users from the web page.
In order to decrytpt the password we can use hashcat.
The credentials can be used to access to the machine as m4lwhere, obtaining the user flag.
Privilege escalation 2
We can execute as sudo the script access_backup.sh.
As you can see above, the command date doesn’t have a hard path.
Hence, we can modify our PATH variable and create our own file named date contining our code obtaining a shell as root.