Pit - [HTB]
![Cover Image for Pit - [HTB]](/assets/images/blog/PIT-htb/PIT.png)

Introduction
Pit is a medium-hard CentOs machine from HackTheBox where the attacker will have to enumerate through an SNMP service finding a new web application for an RCE. Later, he or she will have to use the information from the SNMP service to find a vulnerable script which allow the attacker to retrieve the root flag.
Enumeration
As always, let's start finding all opened ports in the machine, but this time we will also need enumerate the UDP openend ports.
There are four openend ports, let's continue with a deeper scan.
Thanks to nmap we obtain two domains pit.htb and dms-pit.htb
After a ton of enumeration on each service, finally enumerating the the private enterpise numbers of the SNMP service wer can find a web directory and some usernames.
Note: Posts about SNMP enumeration.
In order to access to the web page we can do it through this URL. However, we need some credentials
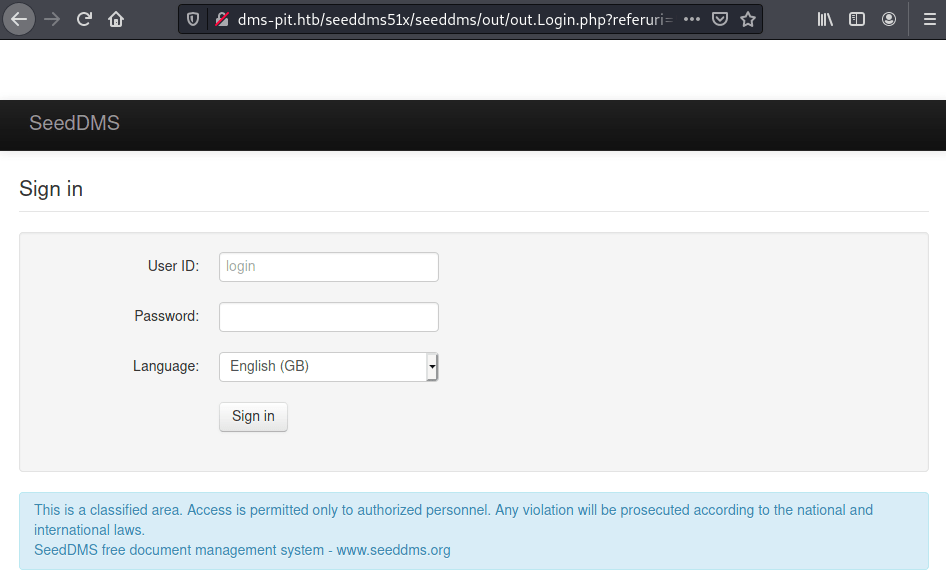
It turns out that the credentials for the login page are michelle:michelle.
Explotation
Looking at the "Upgrade Note" we can figure it out that they are using a SeedDMS v5.1.15.
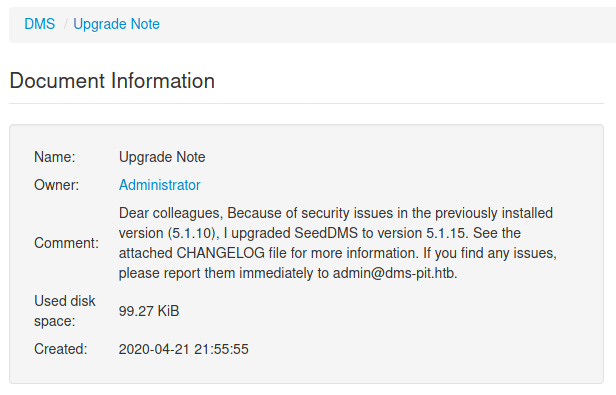
This version has an exploit associated it, allowing us to execute commands on the machine. Nonetheless, we need to do it manually.
Accesding to DMS/Docs/Users/Michelle/ we can a "Add Document" to the server. In my case the file was the following.
Note: After 5 minutes every file is deleted so you will have to uploaded it several times.
Now, we need to figure out the documentid of our file, as you can see in the following image.
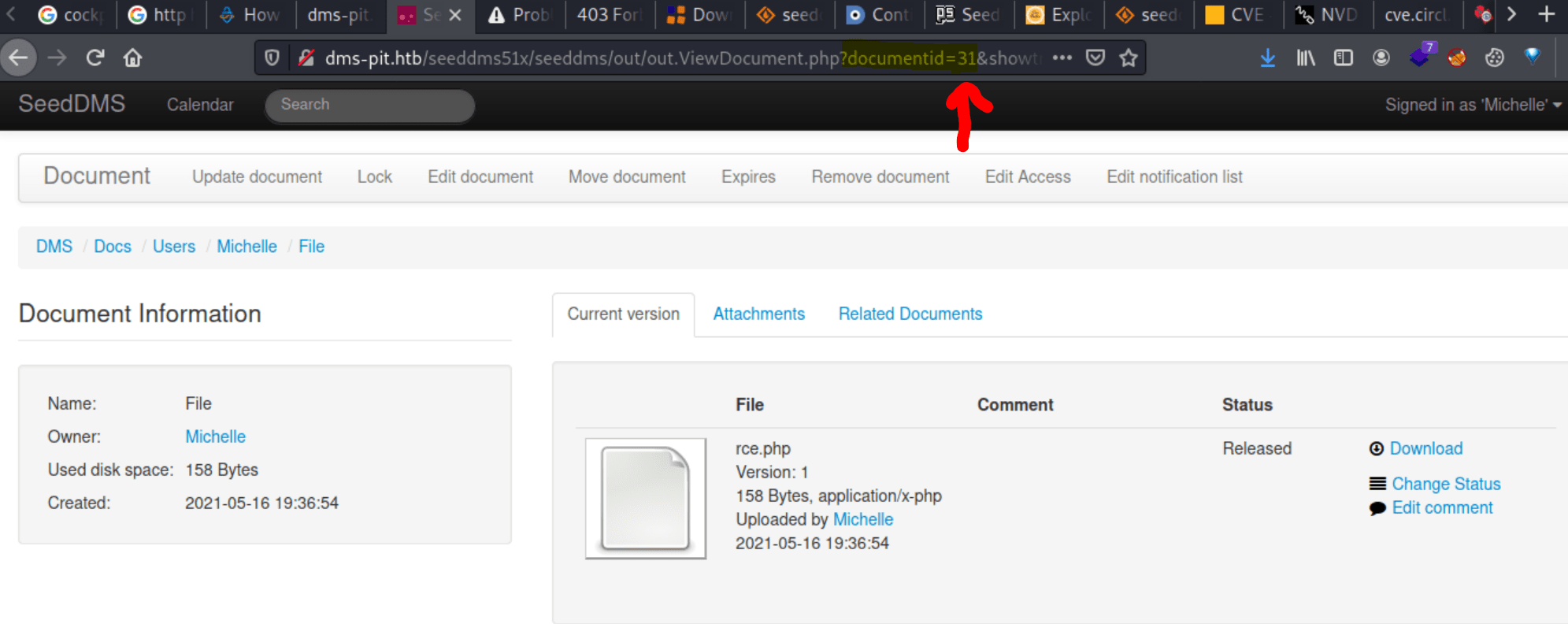
After that, we can access the file with the following URL, obtaining our reverse shell.
Inside the file /var/www/html/seeddms51x/conf/settings.xml there are the credentials for the database which passsword can be used for getting access as michelle to the <strong data-reactroot="">Cockpit</strong> web page at port 9090.
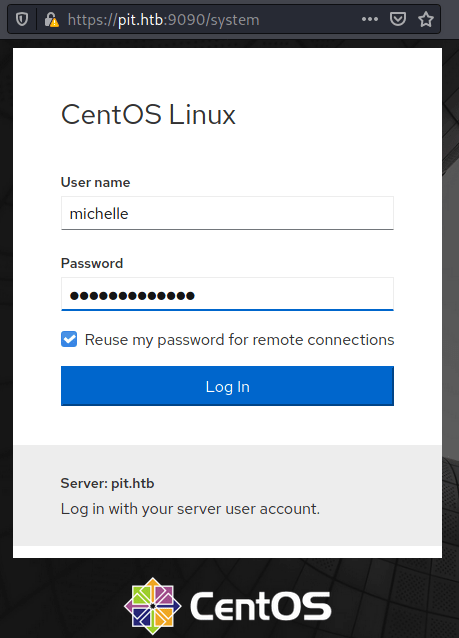
Using the terminal we can obtain the user flag.
Privilege escalation
Looking once again in the snmpwalk service we can see a weird file.
Looking its contents we can seee that executes every file named check+<whatever>+sh stored at /usr/local/monitoring/.
In order to obtain a shell as root we have to appent our pub SSH key into the /root/.ssh/authorized_keys. To do so you can execute the following command.
Finally, in order to execute the monitor file we only need to execute the snmpwalk command one final time and access to the machine through SSH as root.