Passage - [HTB]
![Cover Image for Passage - [HTB]](/assets/images/blog/Passage/Passage.png)

Introduction
Passage is a medium linux machine where the attacker will have to deal firstly with Fail2Ban in order to find the news login portal. Secondly, find a user's credentials in the web page files. Thirdly, using a pair of ssh keys to become another user. And finally, the attacker will have to exploit the USBGenerator service in order to escalate privileges.
Enumeration
As always I start scanning all open ports in the machine.
Then a further scan for obtaining more information about each service.
Because, nmap doesn't provide helpful information, let's see what there is in the Apache Server.
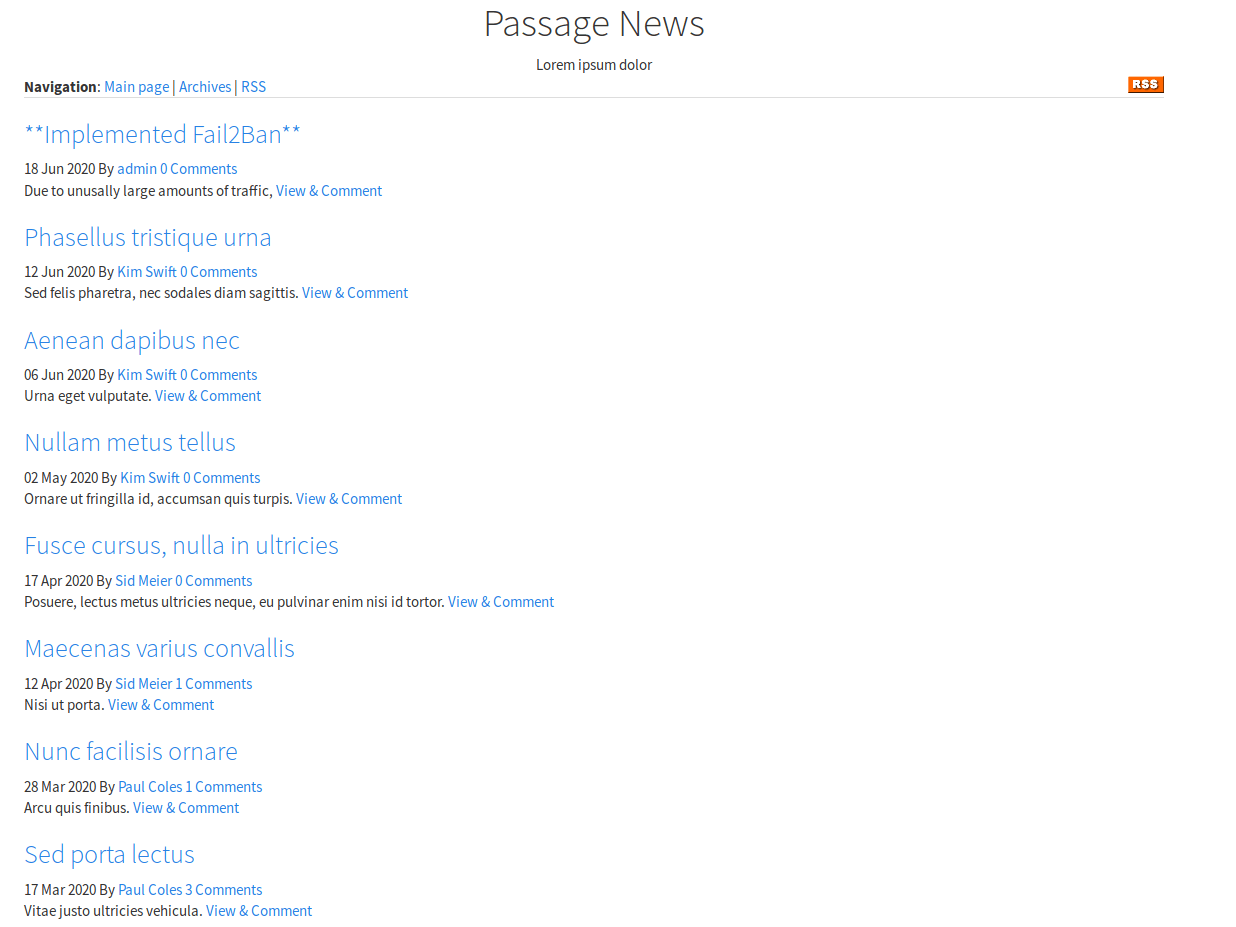
It seems like a blog with several authors. In one of the posts, tells that Fail2Ban (Intrusion prevention software framework that protects computer servers from brute-force attacks.) has being installed to avoid website attacks, so for this machine tools like gobuster or dirbuster are not feasible due to the huge amount of request they do, so our IP will be banned pretty easily.
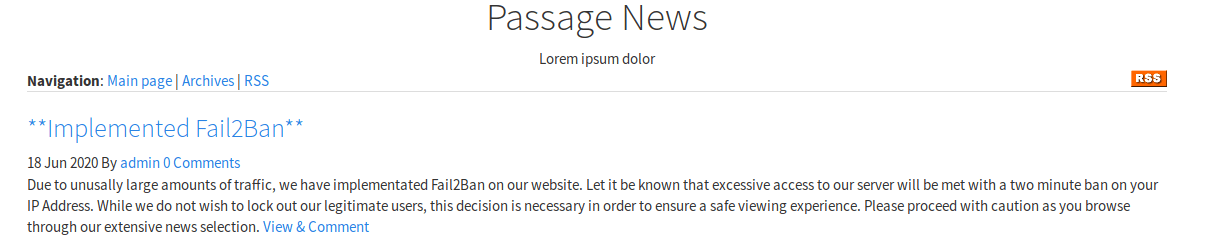
Having a look at the rss link (Really Simple Syndication is a web feed that allows users and applications to access updates to websites in a standardized, computer-readable format.) seems like there is another directory named CuteNews.
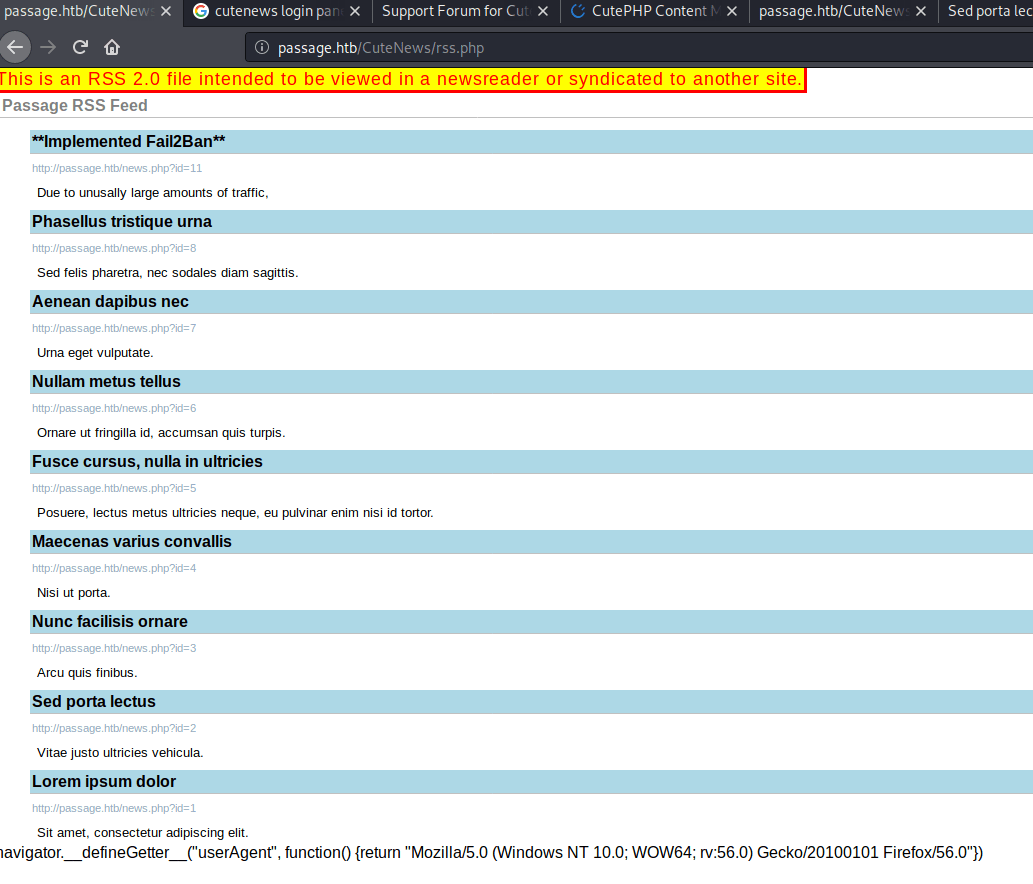
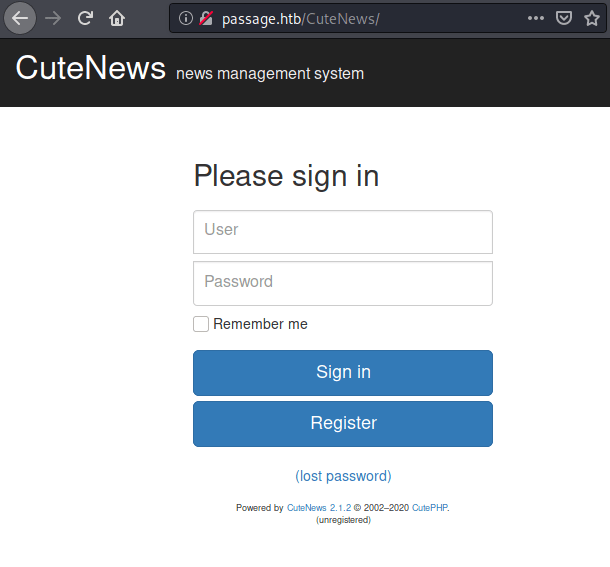
Accessing to the directory appears a login portal for CuteNews , a News manager.
Exploit
Having a look at searchploit appears several exploits for this version.
The valid one is "CuteNews 2.1.2 - Remote Code Execution" which has a post associated to it at medium.com so you can learn how to use it. (You only have to execute it with python3 and enter the specified URL http://passage.htb/ )
Using netcat we can get our own reverse shell so we can travel for the directories more easily.
First, we need to put a listen port.
Then, we need to execute the reverse shell using the exploit.
Finally, in order to use our reverse shell like a proper shell we need to upgrade it, typing the following commands.
The one thing remaining is that the reverse shell has to have the same number of rows and columns as your terminal, so we can use programs like vim,nano, etc. is running the following commands (The number of rows and columns will vary from computer to computer).
Inside the /etc/paswd file there are two registered users, which credentials must be found in order to get the user flag.
Privilege Escalation 1
Looking in to the folder /var/www/html/CuteNews/cdata/users there are a lot of files with 64 encoded information on them. Using trial and error inside the files "21.php" and "b0.php" are stored the credentials for the users nadav and paul.
21.php
b0.php
Credentials
However, passwords are hashed. Using crackstation the Paul's password can be obtained.
Then, with the paul's credentials we can obtaine the root.
Privilege Escalation 2
Inside the paul's ssh folder there is a pair public-private keys, which can be used for getting access to the machine through SSH as nadav.
Privilege Escalation 3
In the nadav's viminfo file there are two paths, one of them containing the name USBCreator.
Looking for privilege escalation on the Internet for USBCreator appears this post talking about how to exploit it.
Finally, executing the following commands we add our ssh keys to the root's authorized keys files so we can ssh to the machine as root obtaining the flag.