Meta - [HTB]
![Cover Image for Meta - [HTB]](/assets/images/blog/Meta-htb/Meta.png)

Introduction
Meta is a medium Linux machine from HackTheBox, where we will have to find a developer subdomain vulnerable to a new ExifTool vulnerability and obtain RCE. Later, we will have to escalate privileges by exploiting a vulnerability for ImageMagick, getting the user's private key. Finally, we will have to change Neofetch's config file in order to become root.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of each opened port, getting more information about each service.
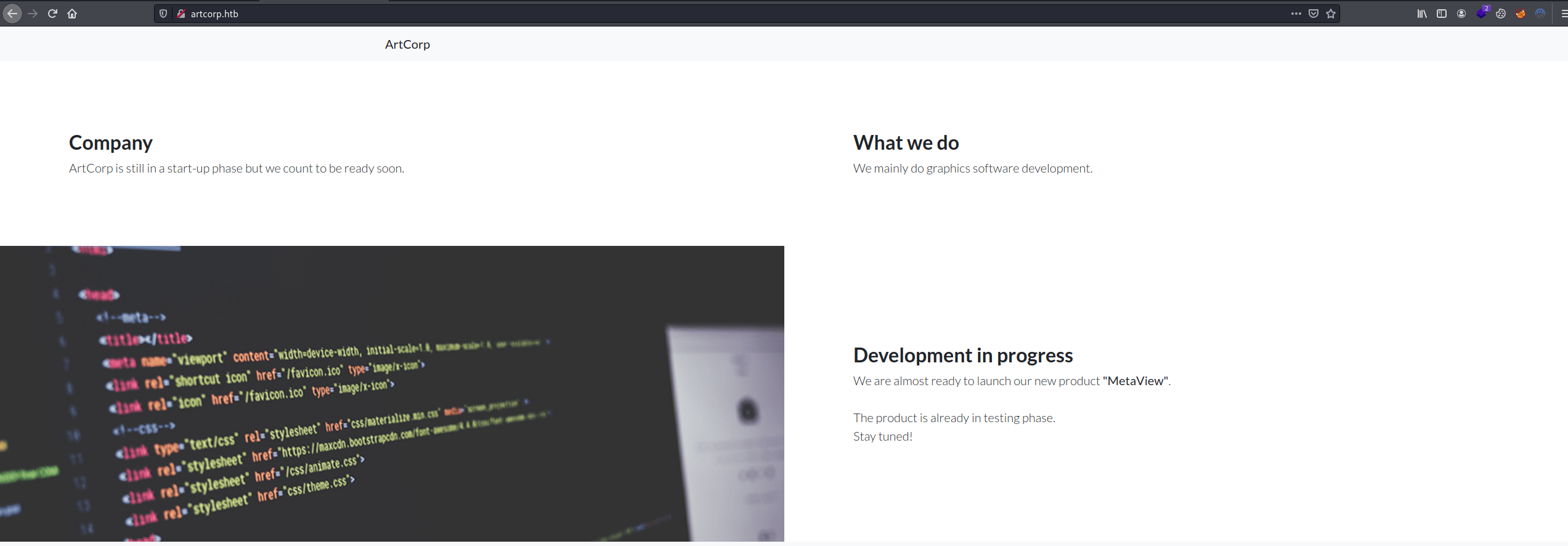
As we can see in the Nmap output, there is a "follow redirect" to the domain artcorp.htb. Adding it to /etc/hosts we get access to this page.
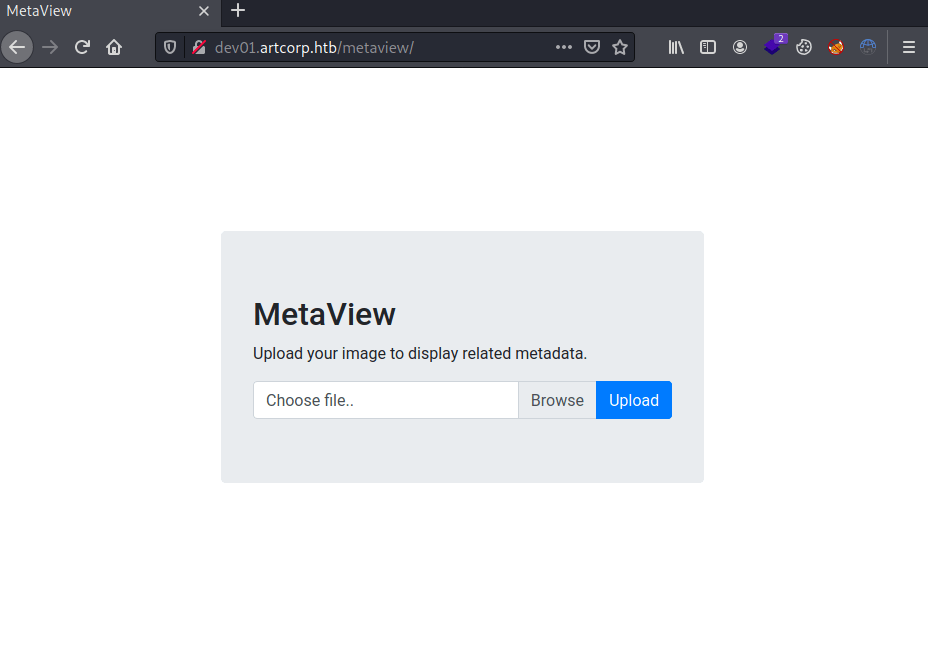
Enumerating domains with Gobuster, we obtain a subdomain for developers.
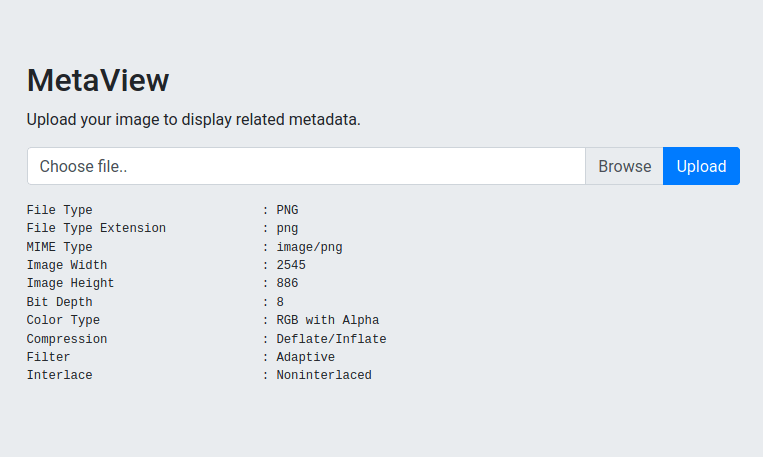
In this subdomain, we can upload images that will be processed showing its metadata.
Exploitation
After uploading a picture, ExifTool seemed to be retrieving the metadata. So, I looked for new CVEs for ExifTool, finding a GitHub repository for the vulnerability CVE-2021-22204 that allows an attacker to obtain RCE by uploading a malicious image.
Executing the following commands, we obtain a reverse shell as www-data.
Privilege Escalation 1
After executing pspy for a while appears a script named convert_images.sh that is being run by the user Thomas and the root user deletes each file under /tmp/.
Having a look at it, it is executing a file named mogrify.
Looking for the version, it seems that it is an ImageMagick binary.
Looking for vulnerabilities, I found this post to format a malicious SVG image file obtaining arbitrary code execution.
After much trial and error, we can not obtain a reverse shell with the exploit, but the following error appears if we try to access as Thomas through SSH.
Hence, we need to copy Thomas' SSH private key into a different folder rather than /tmp/. An alternative will be /dev/shm/, where every user has read and write access.
Once we created the exploit, we need to wait three minutes to be executed.
After sanitizing the exploit's output, we obtain Thomas' SSH private key.
Privilege Escalation 2
Thomas is able to execute Neofetch as root, keeping the XDG_CONFIG_HOME environment variable where the neofetch's config file is located. Hence, we can modify the file in order to obtain a shell as root.