Love - [HTB]
![Cover Image for Love - [HTB]](/assets/images/blog/Love-htb/Love.png)

Introduction
Love is an easy Windows machine from HackTheBox filled with some rabbit holes and some tricks that wouldn't allow you to escalate privileges, but for the shake of simplicity I am not gonna tell. First of all, we need to obtain some credentials via a SSRF in a File Scanner web for a later RCE explotation in a voting system. Finally, in order to become Administrator we only to install a malign crafted msi package.
Enumeration
As always let's start scanning all opened ports in the box.
Then, we continue with an exhaustive scan of each port.
As we can see in the nmap output there are several HTTP servers running on the machine. Furthermore, we can find the domain staging.love.htb.
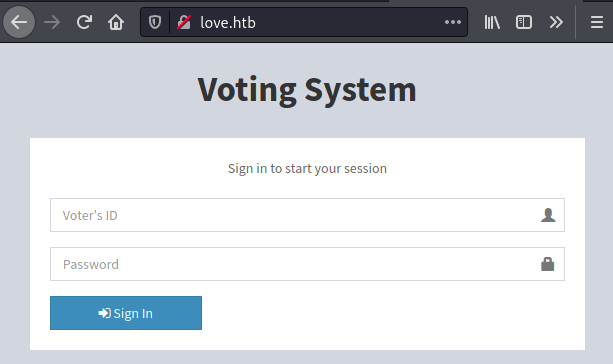
In the port 80 there is a Voting System.
Looking in searchsploit there are several exploits. One of them allow us to obtain an RCE in the machine (We are gonna exploit it manually), but we need some credentials.
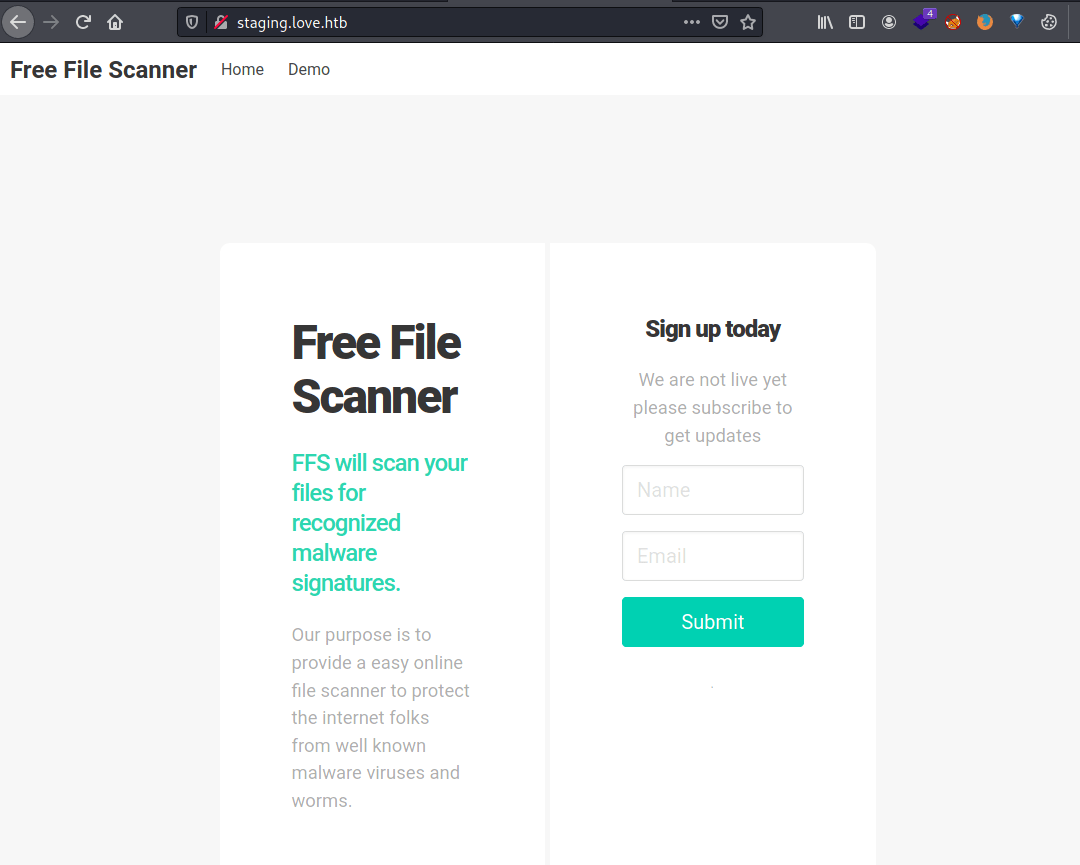
In the http://staging.love.htb/ URL there is a Beta File Scanner with a demo page where we can submit URLs.
The scanner uses an internal web browser which shows the contents of the URL we indicate in the form. Hence, we can access to the HTTP server at port 5000 which doesn't allow foreign connections.
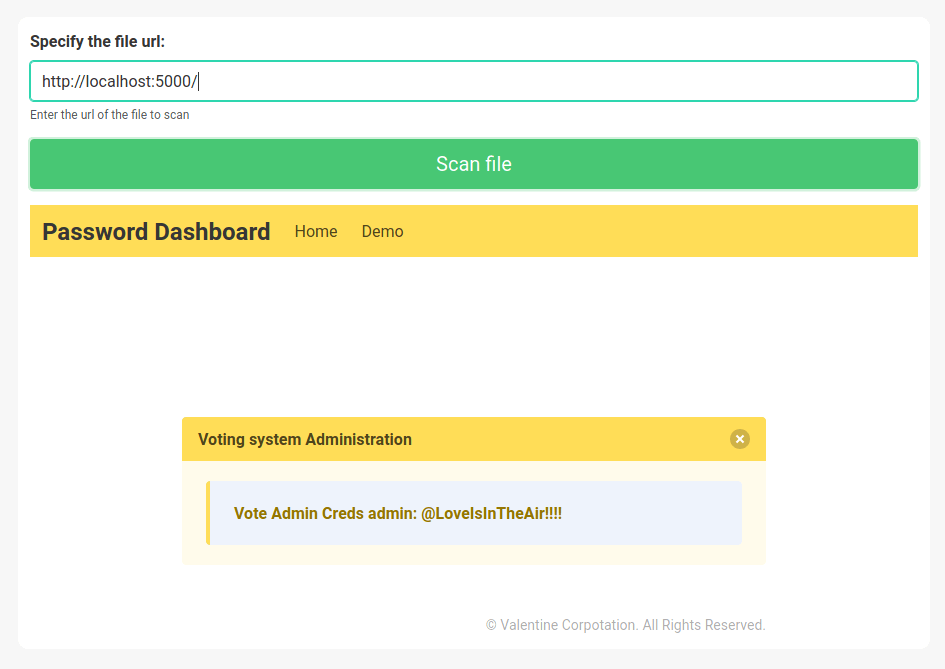
admin:@LoveIsInTheAir!!!!
Explotation
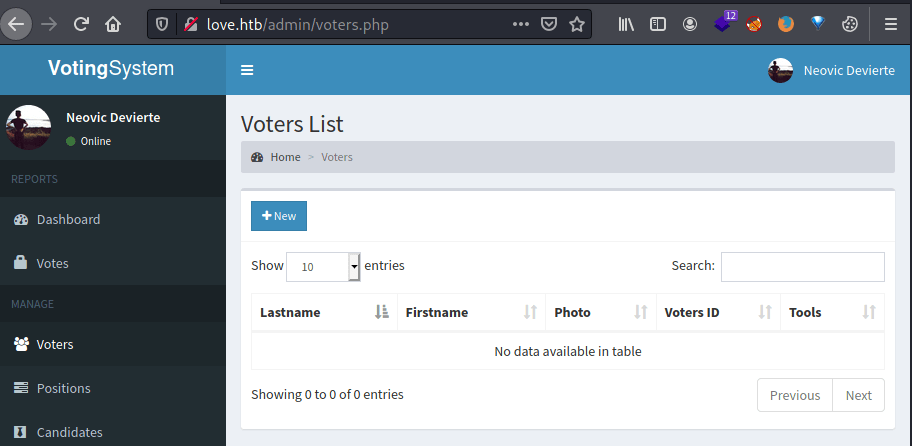
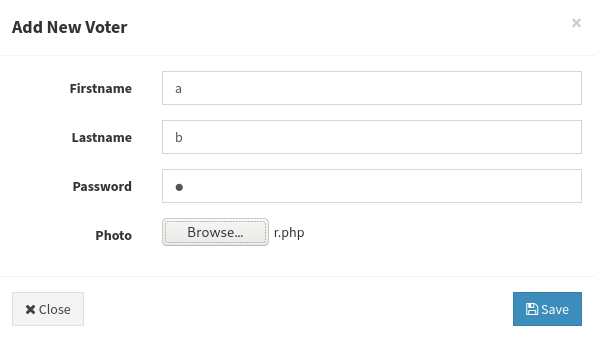
Once we have the credentials we can access to the voters list in the admin panel of the voting system.
In order to obtain our RCE we need to create a new voter, uploading a web shell as image. The web shell I used is the following.
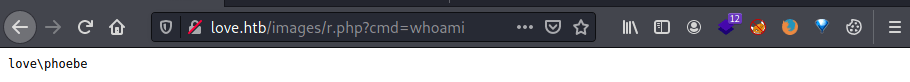
Watching the image through this link we obtain the RCE.
Privilege Ecalation 1
Now, we can convert our web shell into a meterpreter shell that wll get us handy for the privilege escalation.
For that we need to generate a meterpreter reverse shell with msfvenom
Then, we need to use the multi/handler from metasploit in order to put a listenning port.
Finally, we need to download and execute the shell in the machine.
The result is a meterpreter shell as phoebe.
Privilege Escalation 2
In order to enumerate inside the machine I have uploaded and executed WinPEASx86.
Between all the lines, winPEAS alert us that can install msi packages as Administrator. Hence, we can uploaded a crafted msi package in order to obtain a reverse shell as Administrator.
Nonetheless, there is a metasploit module that does everything for us and it just needs a meterpreter session. The commands you need to execute in order to become Administrator are the following.