Late - [HTB]
![Cover Image for Late - [HTB]](/assets/images/blog/Late-htb/Late.png)

Introduction
Late is an easy machine from HackTheBox where the attacker will have an SSTI vulnerability on an OCR application to obtain the user's SSH private key. Finally, to become root, it will have to check a bash script being executed as root each time someone connects through SSH. But for that, it will have to check the file attributes to discover that only data can be appended to the file.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
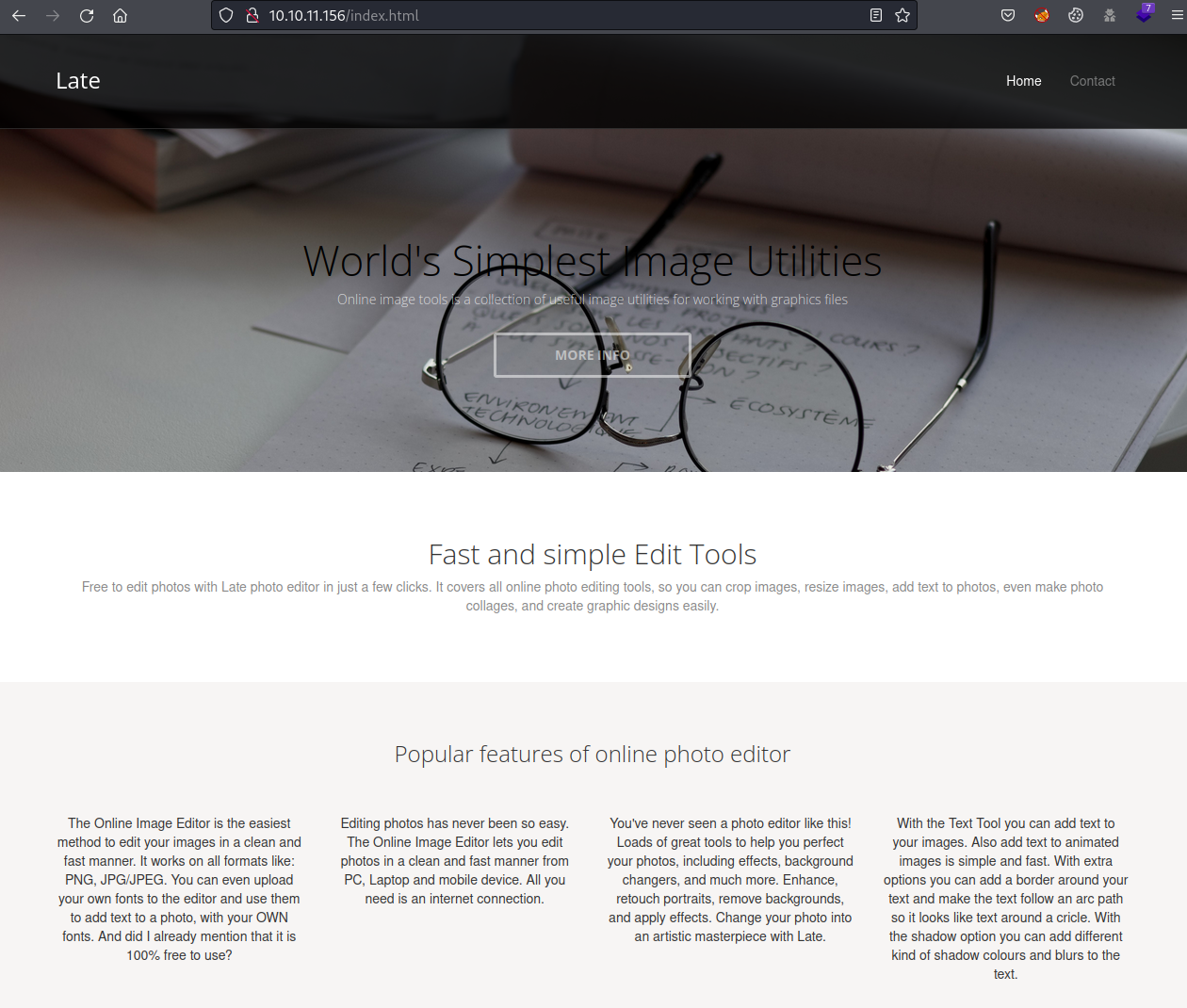
Starting at port 80, there is a web page about a photo editor.
Scraping the web, a new subdomain can be found.
In this subdomain, there is an Optical Character Recognition (OCR) application powered by Flask.
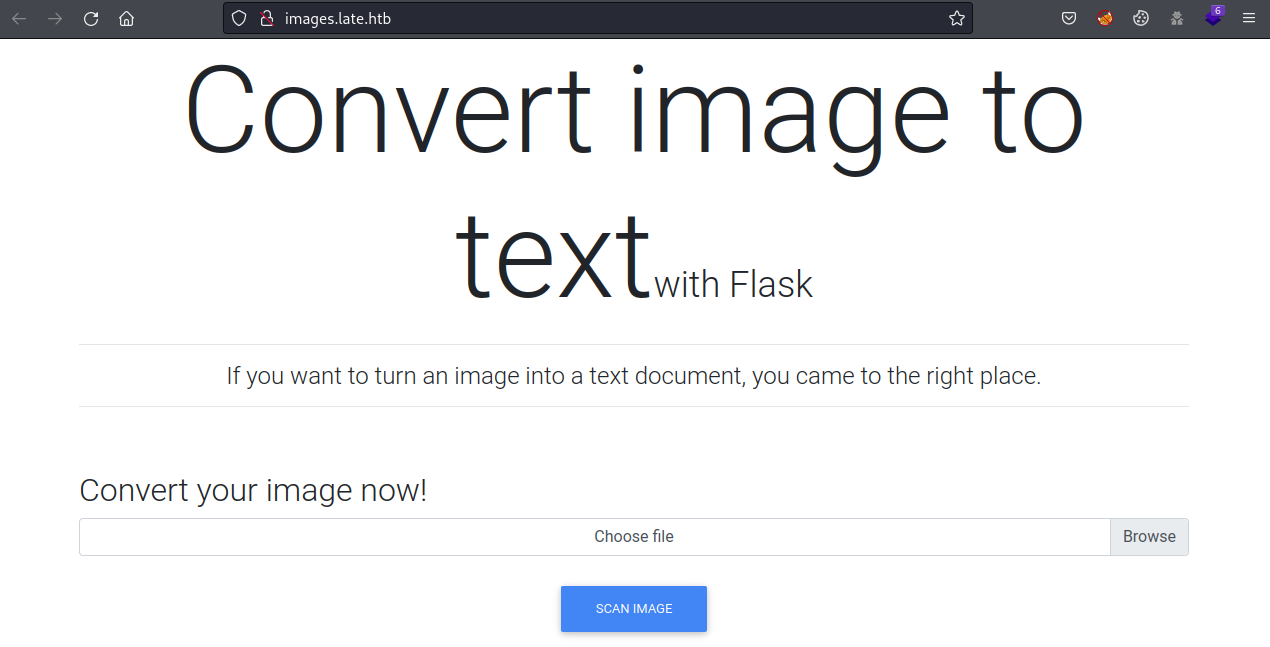
Because it says so, maybe it is vulnerable to Server Side Template Injection (SSTI).
Exploitation
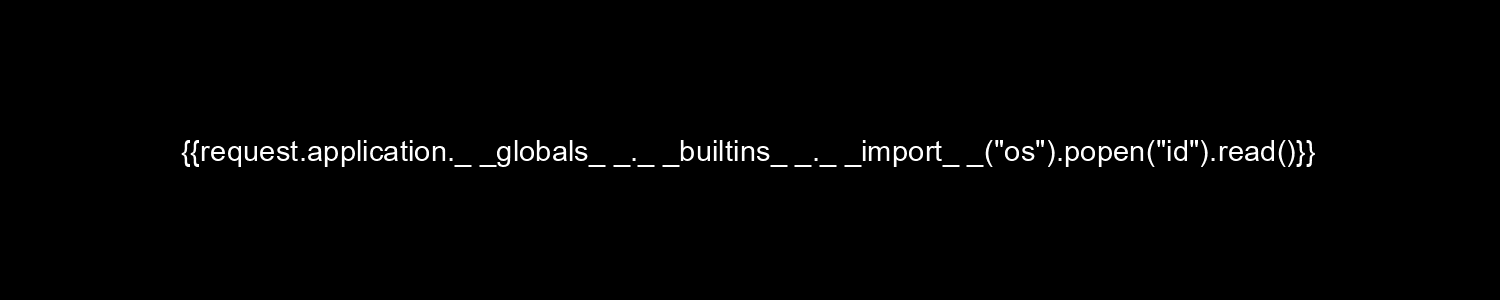
Trying payloads from PayloadAllTheThings, it appears that no result is obtained by sending the payload {{7*7}} because it is executing the code.
To verify that Jinja2 is being used, sending the payload {{ 7*"7" }}, the result<p>7777777</p> is obtained.
After a lot of trial and error, with different desktop and online tools, text2image is the one that best work.
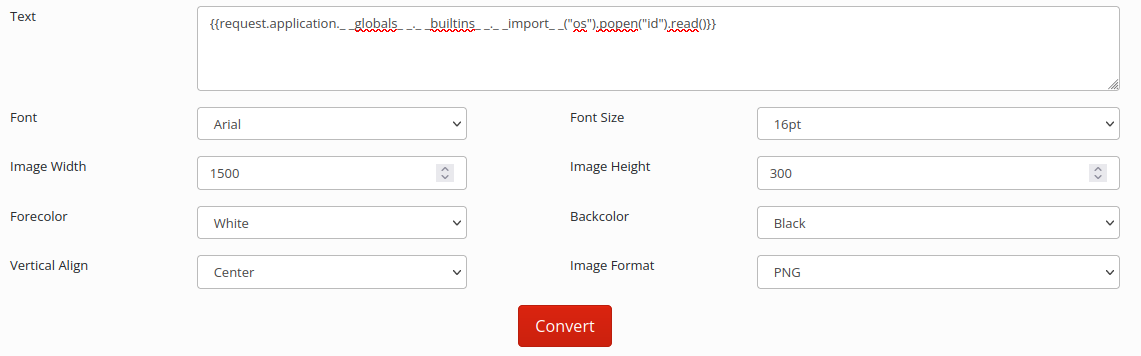
With this image, the user id can be obtained.
Then, with this image the user's SSH private key can be obtained.
Obtaining the user flag.
Privilege Escalation
Finally, to escalate privileges there is a script named ssh-alert owned by the user of this machine, with the following content.
Based on the information of the script, the script is triggered once someone logs to the machine through SSH. However, checking the file attributes we can only append text to the file, so it is not possible to edit the file.
Then, to obtain the root flag, the following one liner can be executed.