Jewel - [HTB]
![Cover Image for Jewel - [HTB]](/assets/images/blog/Jewel/jewel.png)

Introduction
Jewel is a medium Linux machine where the attacker will have to find information in a web git repository about the technology of a web page, and use it to find a exploit to get a reverse shell. Then, the attacker will have find some hashed credentials in a database and a google key authenticator to execute a ruby binary as root.
Enumeration
As always, let's start with a wide scan in order to detect all open ports in the machine.
Then, continue with a scan more in depth scan for all open ports.
Nmap provides a domain name jewel.htb that we can add to /etc/hosts and a URL for a git web page http://10.10.10.211:8000/gitweb/
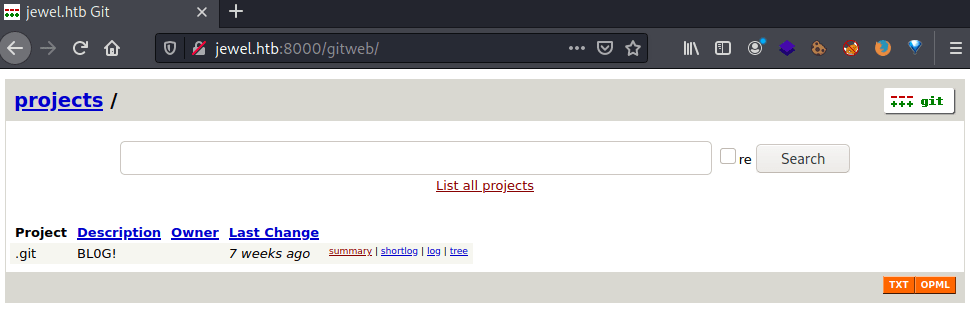
In this web repository is stored all the source code of the web site for the port 8080.

Based on the file .git/config.ru the web page seems to run under ruby on rails.
Inside the .git/Gemfile file we can find the rails version which has a exploit associated to it.
Exploit
The exploit is named "Unmarshalling of user-provided objects in MemCacheStore and RedisCacheStore" and there is a GitHub repository where you can find how to create your payload. However, it is mandatory to execute this commands once you have download the repository.
The script is the following: (Do not forget to change the IP and port).
Then execute it, obtaining the payload.
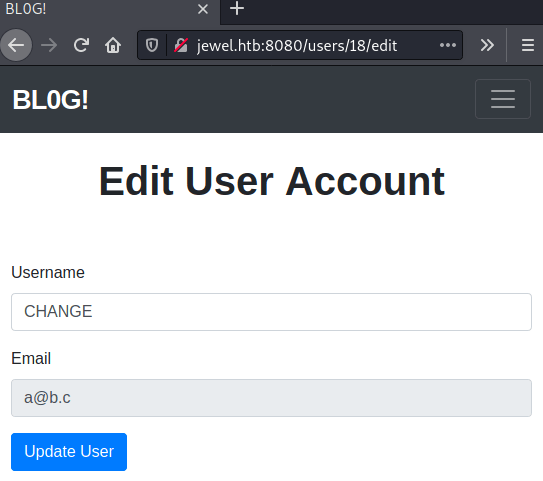
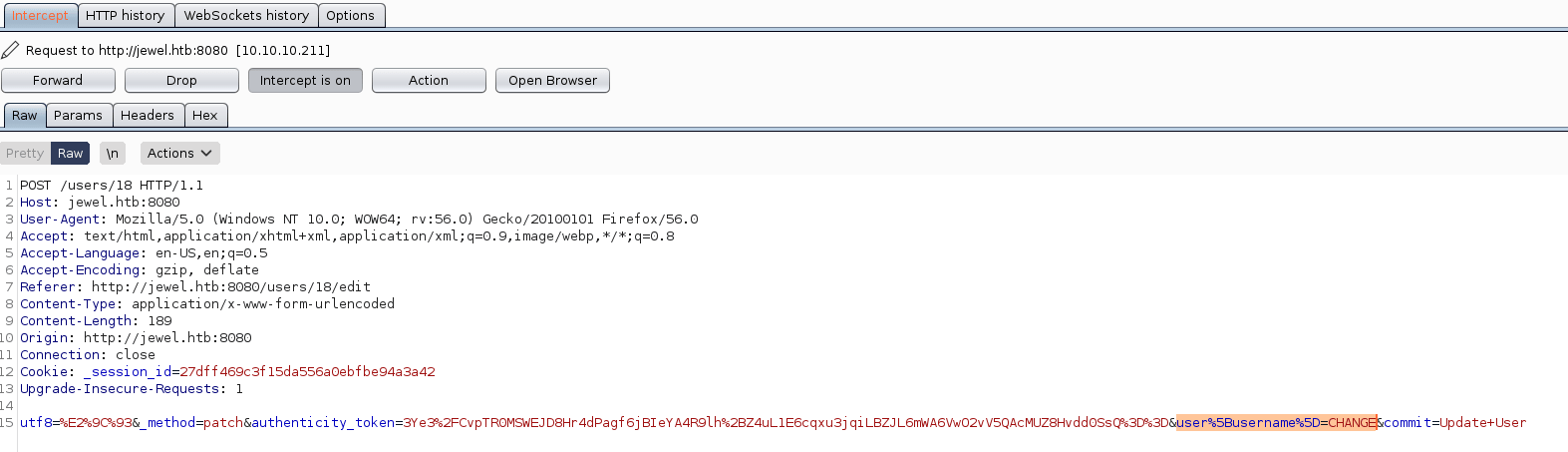
In order to send the payload you need to create an account and log in. Then, click in "Profile" change your user name and intercept the request using burp.
Once you have received the request, you need to change the HIGHLIGHTED part for the the payload that has been generated previously and forward it.
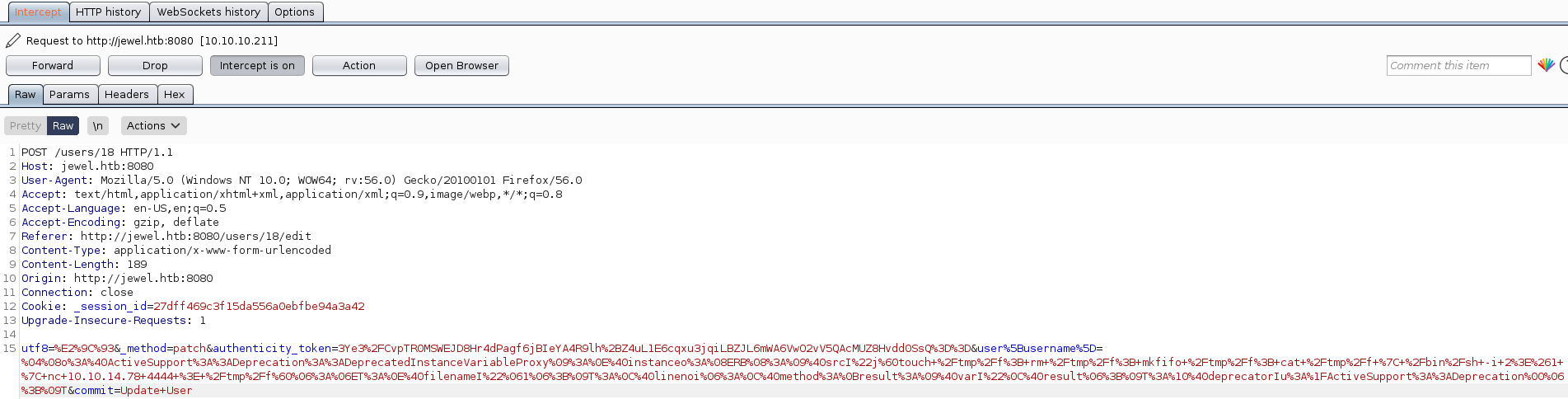
Finally, put a listening port with netcat and refresh the web page.
Privilege escalation
Inside the cat /var/backups/dump_2020-08-27.sql there are the Jennifer's and bill's credentials.
Using hashcat we can retrieve bill's password.
However, we need a verification code in order to list the allowed (and forbidden) commands for the invoking user.
Listing all the directories in the bill's home directory appears a special file .google_authenticator.
Looking inside there is a secret code used for generating OTP codes with the following link.
Note: The Jewel's machine date and your machine's date where you are using the OTP generator must be the same
Once, you got the code you will see that you can execute the gem command as root.
In GTFObins there is a command of how to create a shell as root using gem and the rdoc module, getting the root's flag.