Intelligence - [HTB]
![Cover Image for Intelligence - [HTB]](/assets/images/blog/Intelligence-htb/Intelligence.png)

Introduction
Intelligence is a Windows Active Directory machine from HackTheBox where the attacker will have to enumerate public files in order to find some users and the credentials for obtaining the user flag. Then, will have to add a fake DNS into the domain DNS for obtaining Ted's creds. Finally, the attacker will have to obtain a GSMA password allowing it to impersonate the Admin Domain obtaining the root flag.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
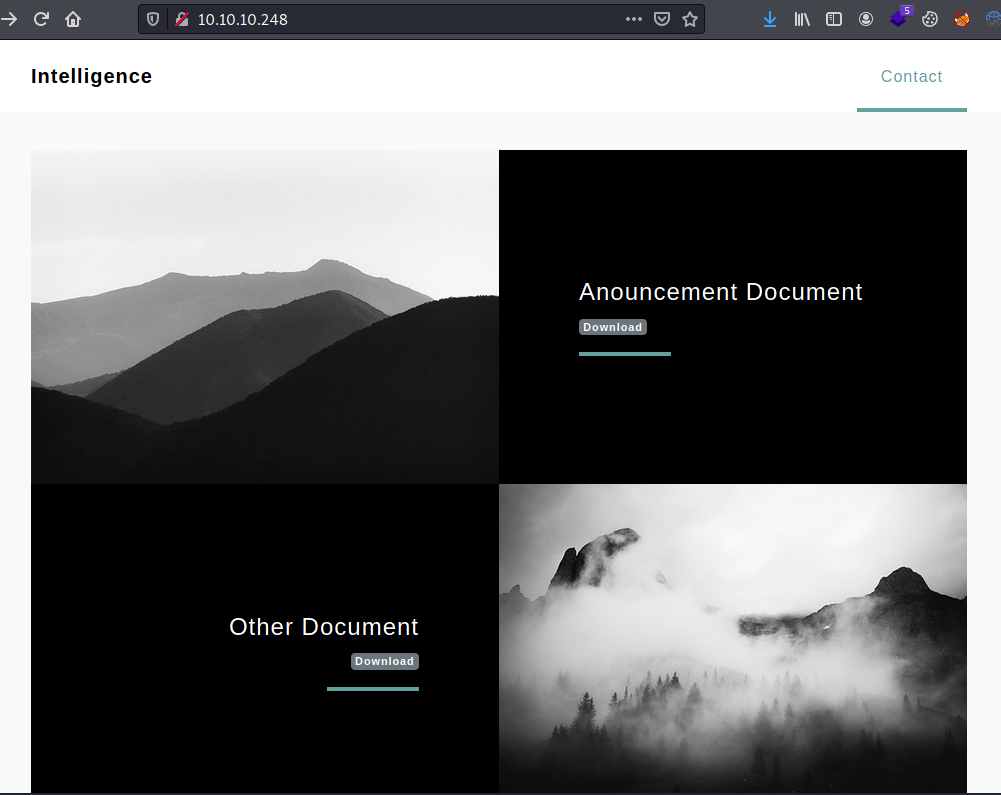
Looking at the web page there are some documents that we can download.
Both of theme have usernames stored in the metadata fields. However, we can not do much with them.
Nonetheless, under the documents directory seems to be are more files, following the same syntax but changing the date.
In order to download them all, I created the following script.
You only need to execute the following commands in order to obtain a list with all the users.
Furthermore, inside the document 2020-06-04-upload.pdf there is the following text.
Exploitation
We can find out which user the password belongs to thanks to crackmapexec.
Now we can access to all shared folders.
Under the Users share we can retrieve the user flag.
Privilege escalation 1
Under the share IT we can retrieve a powershell script.
The script execute an Active Directory query in order to obtain all DNS domains under the Active Directory domain. Then, tries to access them sending the user credentials.
Hence, we can add a our own domain in order to retrieve the user credentials with responder.
In order to add a domain we need to synchronise the kali's clock with the server's clock and execute dnstool.py.
Then, we need to execute responder waiting up to 10 minutes in order to retrieve the credential.
With hashcat we can retrieve the actual NTLM password.
Privilege escalation 2
After trying a lot of stuff, we can retrieve a GMSA password with Ted's credentials.
The service svc_init has the primitive msDS-AllowedToDelegateTo which could allow us to impersonate Domain Admins.
In order to impersonate the service as Administrator we need synchronise the clocks once more and execute getST.py.
Now, we are able to execute any commands as nt authority\system, obtaining the root flag.