Horizontall - [HTB]
![Cover Image for Horizontall - [HTB]](/assets/images/blog/Horizontall-htb/Horizontall.png)

Introduction
Horizontall is an easy linux machine OSCP like, where you will have to find an API subdomain, where is located a strapi web page. Then, you will have to concatenate several exploits in order to obtain a reverse shell as user. Finally, you will have to do port forwarding in order to exploit a laravel vulnerability obtaining the root's flag.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of each opened port, getting more information about each service.
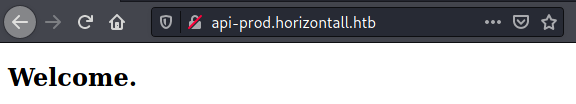
The nmap output provides us with the domain horizontall.htb, adding this to the /etc/hosts we have access to the web page.
Because finding files inside this web page didn't seem to work out, I tried enumerating subdomains with gobuster.
This new domain provides access to an API web page.
With further enumeration, we obtain the following directories.
Inside the /admin directory there is an strapi login page.
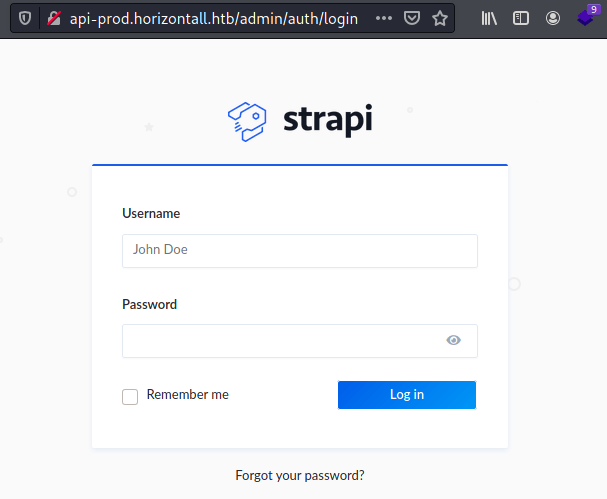
With the following command, we can check the strapi version for a later CVE search.
Exploiting
Looking on google there is a post about how to exploit the <strong data-reactroot="">CVE-2019-18818</strong>, resetting the administration password knowing the admin's email.
Note: I guessed the admin's email and it worked out :D
In order to obtain a reverse shell we need another CVE that looking on google again web appears this exploit for the CVE-2019-19609.
Now, we can become the user strapi using the JWT token from the previous exploit, obtaining the user's flag.
Privilege Escalation
Enumerating the machine we can see that there are some services running on localhost.
The one we should care about is port 8000. In order to access the localhost we need to do port forwarding. For doing so, I used chisel.
Now, we can access to the laravel web page.
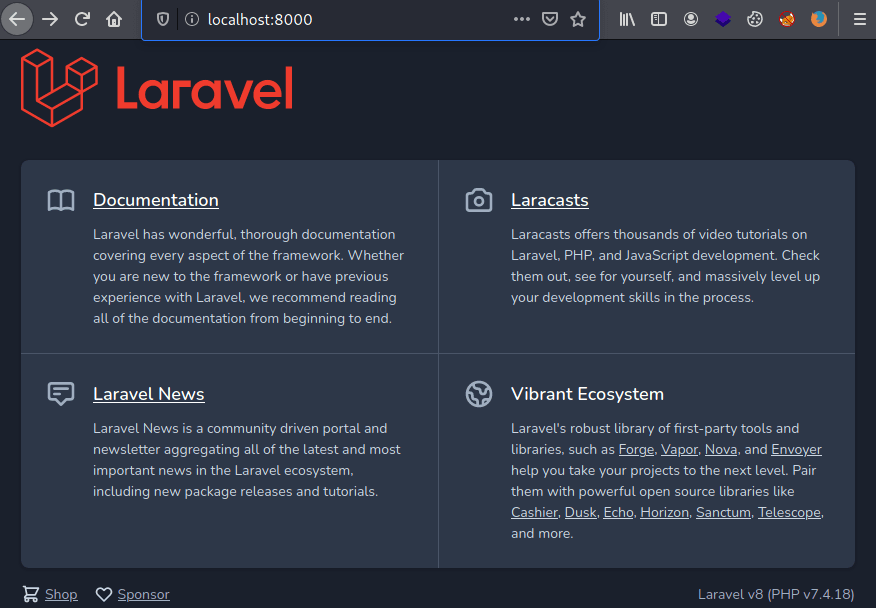
Looking exploits for Laravel v8 appears the vulnerability CVE-2021-3129 with the following exploit. Nonetheless, we need the library PHPGGC to create our payload. In this case, our payload obtains the root flags.
Finally, we need to execute the exploit obtaining the root's flag.