Holo - [THM]
![Cover Image for Holo - [THM]](/assets/images/blog/Holo-thm/Holo.png)

Introduction
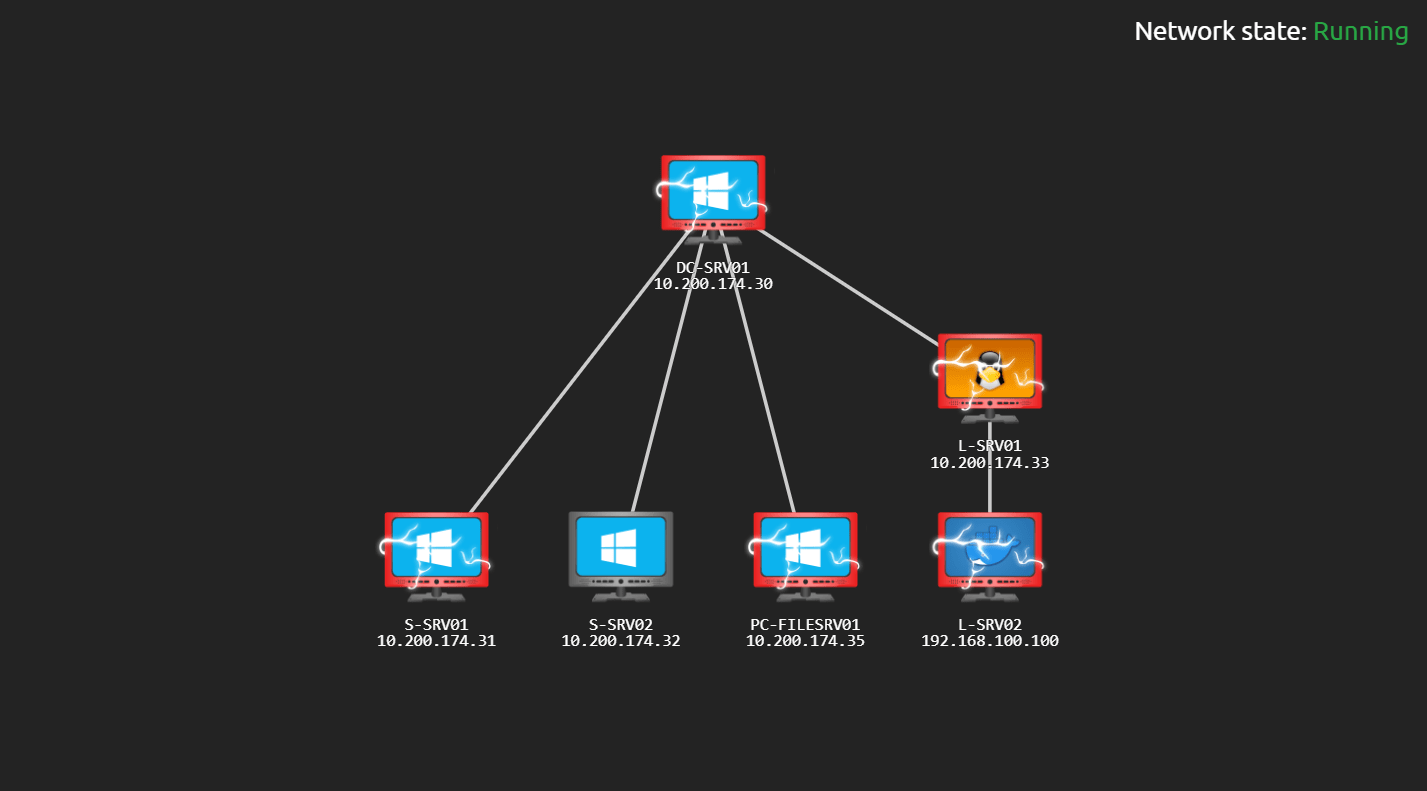
Holo is an Active Directory and Web Application attack lab that "teaches" web and active directory attacks. In this write-up you will see step by step how I got to every-single flag so you do not have to suffer the same as I did ;)
Task 4 - [Flag Submission] Flag Submission Panel
What flag can be found inside of the container?
What flag can be found after gaining user on L-SRV01?
What flag can be found after rooting L-SRV01?
What flag can be found on the Web Application on S-SRV01?
HOLO{bcfe3bcb8e6897018c63fbec660ff238}
What flag can be found after rooting S-SRV01?
HOLO{50f9614809096ffe2d246e9dd21a76e1}
What flag can be found after gaining user on PC-FILESRV01?
HOLO{2cb097ab8c412d565ec3cab49c6b082e}
What flag can be found after rooting PC-FILESRV01?
HOLO{ee7e68a69829e56e1d5b4a73e7ffa5f0}
What flag can be found after rooting DC-SRV01?
HOLO{29d166d973477c6d8b00ae1649ce3a44}
Task 8 - [Initial Recon] NOT EVERY GEEK WITH A COMMODORE 64 CAN HACK INTO NASA!
What is the last octet of the IP address of the public-facing web server?
33
How many ports are open on the web server?
3
What CME is running on port 80 of the web server?
Wordpress
What version of the CME is running on port 80 of the web server?
5.5.3
What is the HTTP title of the web server?
holo.live
Task 9 - [Web App Exploitation] Punk Rock 101 err Web App 101
What domains loads images on the first web page?
What are the two other domains present on the web server? Format: Alphabetical Order
admin.holo.live, dev.holo.live
Task 10 - [Web App Exploitation] What the Fuzz?
What file leaks the web server's current directory?
robots.txt
What file loads images for the development domain?
img.php
What is the full path of the credentials file on the administrator domain?
/var/www/admin/supersecretdir/creds.txt
Task 12 - [Web App Exploitation] What is this? Vulnversity?
What file is vulnerable to LFI on the development domain?
img.php
What parameter in the file is vulnerable to LFI?
file
What file found from the information leak returns an HTTP error code 403 on the administrator domain?
/var/www/admin/supersecretdir/creds.txt
Using LFI on the development domain read the above file. What are the credentials found from the file?
admin:DBManagerLogin!
Task 19 - [Docker Breakout] Going out with a SHEBANG
Obtain a shell on L-SRV01 and submit the user flag on Task 4.
Task 20 - [Privilege Escalation] Call me Mario, because I got all the bits
What is the full path of the binary with an SUID bit set on L-SRV01?
What is the full first line of the exploit for the SUID bit?
sudo install -m =xs $(which docker) .
Escalate privileges and submit root flag to Task 4.
Task 21 - [Post Exploitation] From the Shadows
What non-default user can we find in the shadow file on L-SRV01?
Task 22 - [Post Exploitation] Crack all the Things
What is the plaintext cracked password from the shadow hash?
Task 28 - [Web App Exploitation] Hide yo' Kids, Hide yo' Wives, Hide yo' Tokens
What user can we control for a password reset on S-SRV01?
Gurag
What is the name of the cookie intercepted on S-SRV01? Request:
Response:
user_token
What is the size of the cookie intercepted on S-SRV01?
It is 110
What page does the reset redirect you to when successfully authenticated on S-SRV01?
reset.php
Task 35 - [AV Evasion] Wrapping the burrito
Submit flags on S-SRV01 to Task 4.
Upload the following web shell.
Then, you can obtain the S-SRV01 root flag.
Task 36 - [Post Exploitation] That's not a cat that's a dawg
Executing the following commands in the webshell we can obtain watamet's credentials
What domain user's credentials can we dump on S-SRV01?
watamet
What is the domain user's password that we can dump on S-SRV01?
Nothingtoworry!
Task 37 - [Post Exploitation] Good Intentions, Courtesy of Microsoft: Part II
What is the hostname of the remote endpoint we can authenticate to?
PC-FILESRV01
Task 39 - [Situational Awareness] So it's just fancy malware?
rdesktop -u 'holo.live\watamet' -p 'Nothingtoworry!' 10.200.174.35
What anti-malware product is employed on PC-FILESRV01?
AMSI
What anti-virus product is employed on PC-FILESRV01?
Windows Defender
Task 40 - [Situational Awareness] SEATBELT CHECK!
What CLR version is installed on PC-FILESRV01?
4.0.30319
What PowerShell version is installed on PC-FILESRV01?
5.1.17763.1
What Windows build is PC-FILESRV01 running on?
17763.1577
Task 43 - [Privilege Escalation] WERE TAKING OVER THIS DLL!
What is the name of the vulnerable application found on PC-FILESRV01?
kavremover.exe
Submit the root flag from PC-FILESRV01 in Task 4.
Create the payload with the following name. Detailed information about the dll hijacking in this link.
Download kavremoverENU.dll into C:\Users\watamet\Applications\.
Then use metasploit to set up a listener.
Finally, wait a minute so the file is being executed by the administrator.
Task 44 - [Persistence] WERE TAKING OVER THIS DLL! Part: II
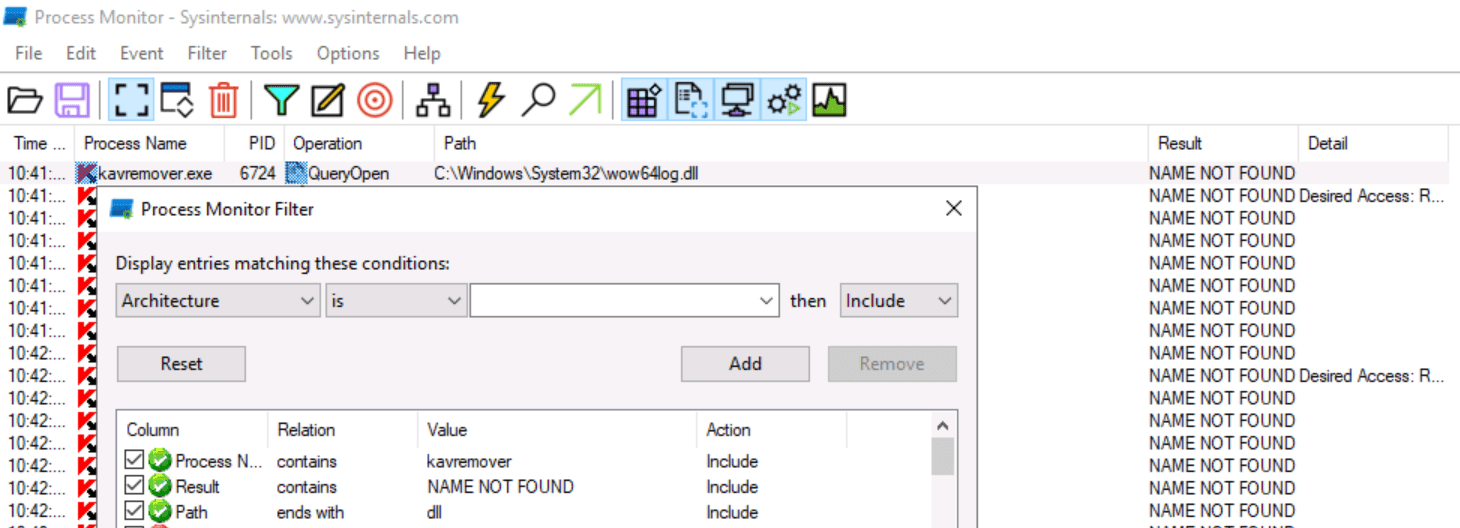
What is the first listed vulnerable DLL located in the Windows folder from the application
wow64log.dll
Task 46 - [NTLM Relay] Now you see me, now you don't
What host has SMB signing disabled?
Despite both showing the same message is the machine 10.200.174.30 (DC-SRV01).
Task 47 - [NTLM Relay] Why not just turn it off?
Read the above and exploit Net-NTLM with remote NTLM relaying and move on to weaponizing the relay.
With the meterpreter shell as the user nt authority/system, we need to change the Administrator's password so we can access later, stop the smb service and reboot the machine.
While the machine is rebooting we need to append the following line to the proxychains configuration file and execute ntlmrelayx.
Then, we need to obtain another meterpreter shell as administrator so we can do port forwarding the port 445.
Once the port forwarding has been completed successfully we need to wait up to 3 minutes. If you do not receive anything reboot the machine and execute the same commands as before, It took me 6 trials.
Finally, while ntlmrelay is receiving connections we need to execute smbexec obtaining the last flag.