Forge - [HTB]
![Cover Image for Forge - [HTB]](/assets/images/blog/Forge-htb/Forge.png)

Introduction
Forge is a medium linux machine where the attacker will have to exploit an SSRF (Server Side Request Forgery) on an images web page in order to retrieve the user's SSH private key. Finally, the attacker will have to raise an exception for a python server triggering a debugging console and becoming root.
Enumeration
As always, let's start finding all opened ports available on the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
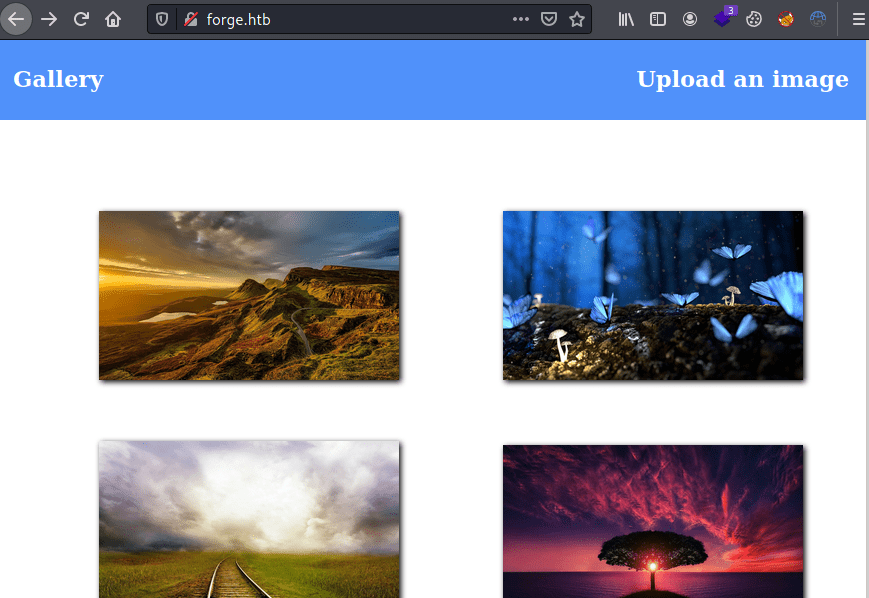
As we can see above nmap provide us with a domain forge.htb, adding it to the /etc/host file we can access a gallery web page where we can upload our own images.
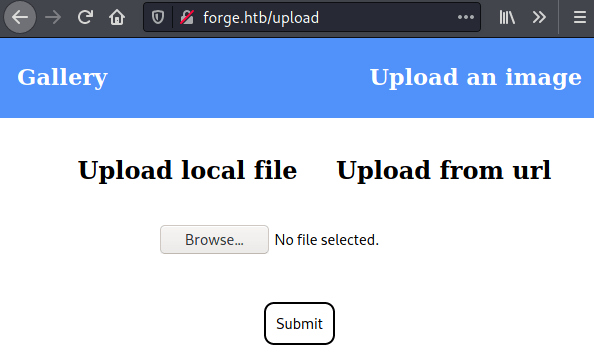
The web page provide us with two ways of uploading images via file or from URL.
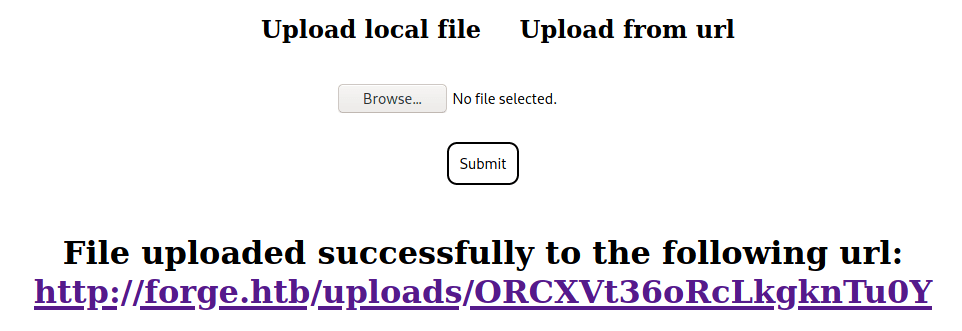
Every file uploaded to the web page is stored under the uploads directory with a random name without extension.
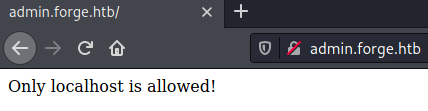
Furthermore, by enumerating subdomains with ffuz we can retrieve the subdomain admin.forge.htb.
However, trying to access this subdomain appears a text saying "Only localhost is allowed!".
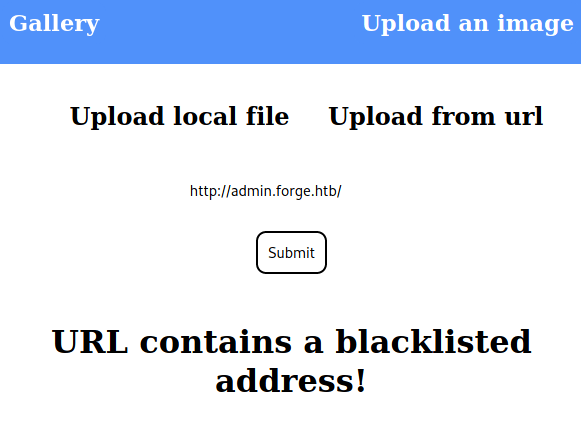
Trying to submit this subdomain to the URL image form an error appears.
Exploitation
Nonetheless, this filter can be easily bypassed by writing the domain in capital letters http://ADMIN.FORGE.HTBobtaining the contents of the admin web page.
As we can see above there is also an/announcements directory where we can retrieve more information.
Using the same procedure we can retrieve the following page.
As the text says, there is an endpoint under /upload where we can retrieve files through the ftp protocol.
After some trial and error we are able to retrieve the user flag.
Moreover, we can get access to the machine obtaining the users's ssh private key.
However, we still need to know the username's private key. This can be easily obtained by downloading the public key.
Finally, we are able to get access through ssh into the machine.
Privilege Escalation
As we can see, user is able to execute the python script remote-manage.py.
This file creates a server on a random port where the client will have to send the password "secretadminpassword" in order to access the several options that it provides. Finally, everything is wrapped under a try-catch executing the Python Debugger console in case an exception occurs.
The easiest way to raise an exception in this code is by simply sending any letter in the options menu. Once, catched the python exception, a debugger console will appear allowing us to execute any command as root, obtaining the root flag.