Faculty - [HTB]
![Cover Image for Faculty - [HTB]](/assets/images/blog/Faculty-htb/Faculty.png)

Introduction
Faculty is a medium Linux machine from HackTheBox where the attacker will have to exploit a simple SQL injection and then exploit a vulnerability on the library mPDF in order to retrieve the web page's source code with the purpose of obtaining the database credentials. Then, to escalate privileges, you need to exploit a vulnerability on meta-git. Finally, the GDB binary has the sys_ptrace capability, which can be used to become root.
Enumeration
As always, let's start scanning all opened ports in the box with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Enumerating directories with ffuf the following results are obtained.
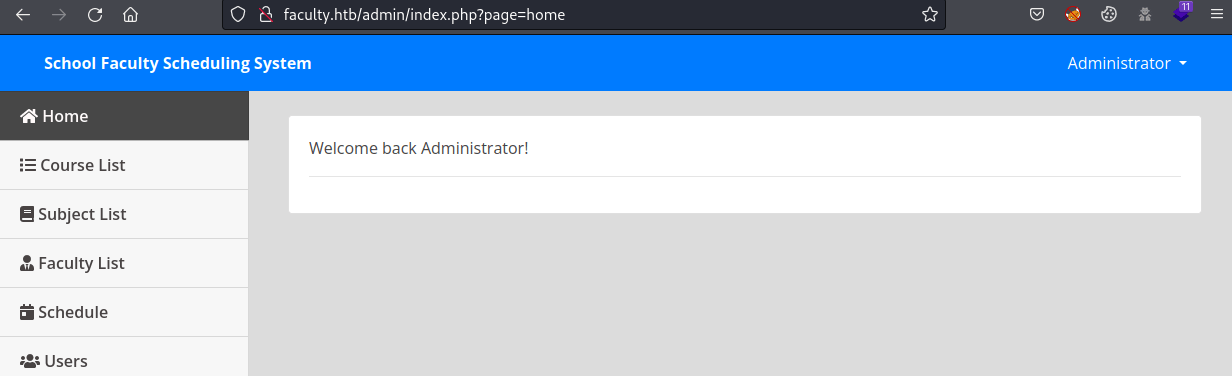
Inside the amdin/ folder there is a login panel.
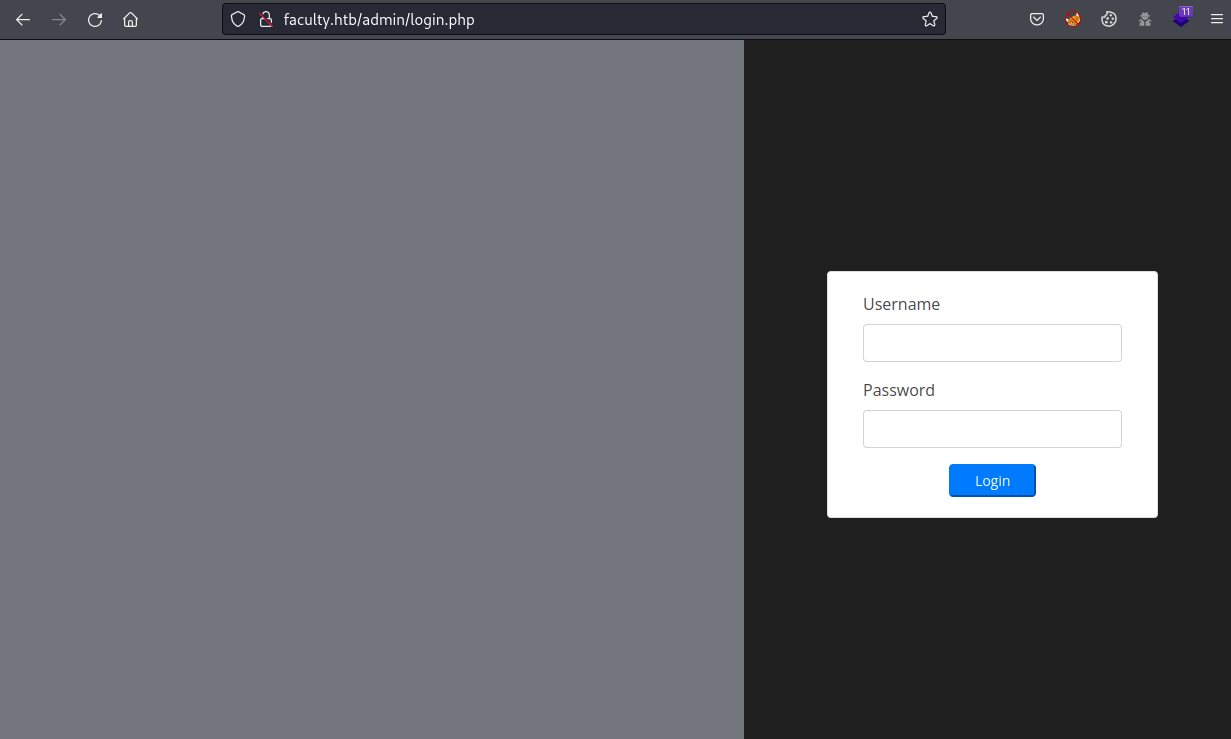
It is possible to bypass the authentication by writing ' or '1='1' -- -# as username and whatever value as a password. Login us as Administrator.
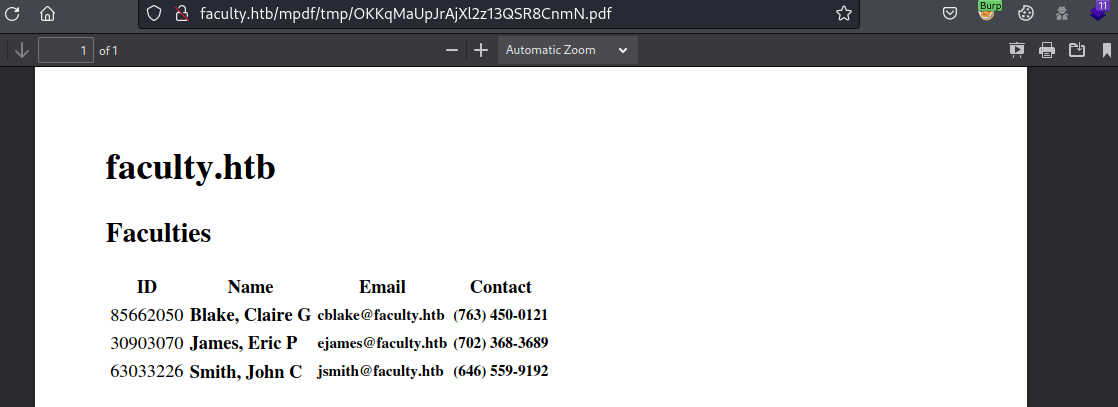
Furthermore, in the "Faculty List" section there is a download PDF button.
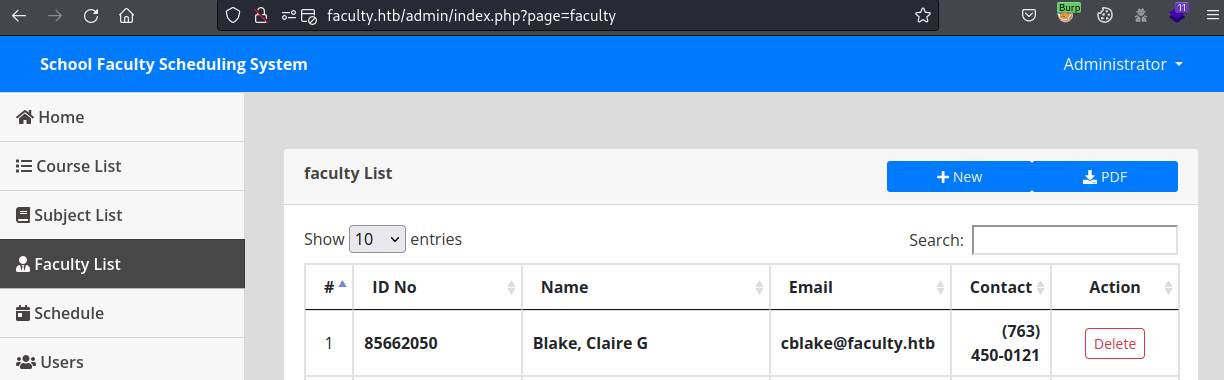
Clicking on download, we obtain the following request.
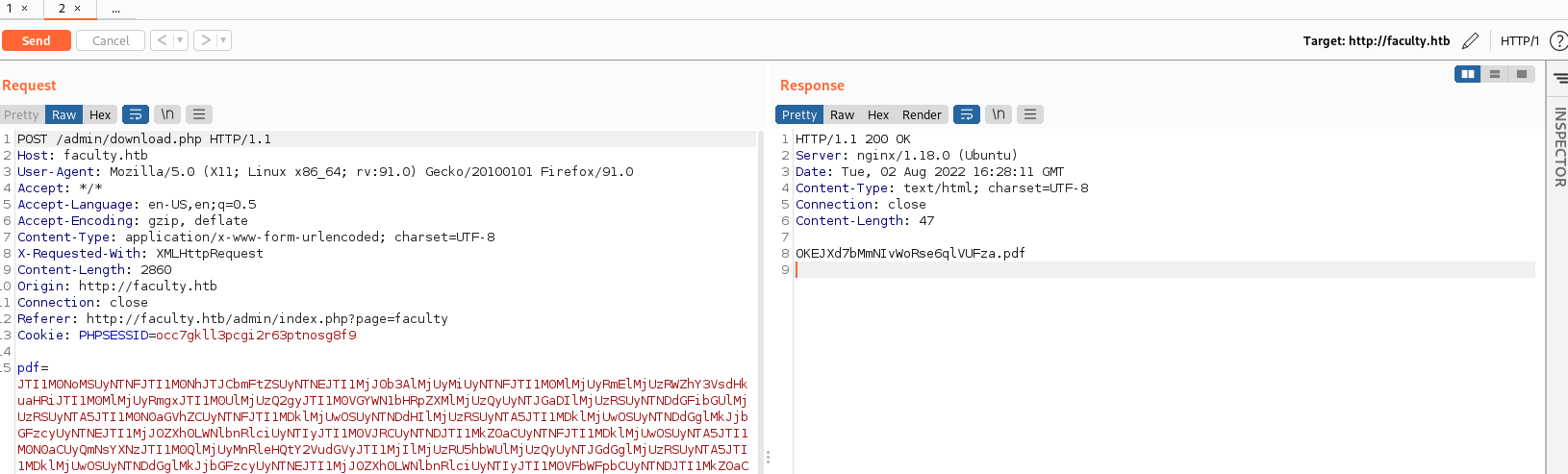
Once the information is decoded, has the following HTML output.
Then, the following file is obtained once the request has been forwarded.
Exploitation
Based on the URL, the PDF is generated using the library mPDF for PHP. This library has an issue where an attacker can include files from the system as attachments.
With the following payload, you can extract the file /etc/passwd, obtaining the next users.
After analysing the login.php code from the web, it is known the existence of the db_connect.php file.
Again, after analysing that file, it is possible to obtain some credentials.
The password can be used to get access the machine as the user "gbyolo" through SSH.
Privilege escalation 1
The user gbyolo has permission to execute the node module meta-git as the user "developer".
This module has an associated vulnerability, allowing arbitrary code execution.
Note: By default, it doesn't work if you are in a directory which the user developer doesn't have access.
To access the machine as developer, it is necessary to retrieve the developer's SSH private key.
Finally, it is possible to obtain the user's flag.
Privilege Escalation 2
The user is a member of the debug group, allowing it to execute gdb.
Furthermore, enumerating with linpeas, it seems that the gdb binary has the sys_ptrace capability, inspecting any processes.
In order to exploit this weakness, it is needed to be attached a process to process which contains the system function.
After a lot of trial and error, the python3 program is the best candidate to exploit this weakness.
Note: The function system doesn't provide any output, so commands as "id" or "cat" won't show anything.