Explore - [HTB]
![Cover Image for Explore - [HTB]](/assets/images/blog/Explore-htb/Explore.png)

Introduction
Explore is a very easy Android machine from HackTheBox where the attacker will have to exploit a vulnerability for the application Es File Explorer in order to obtain RCE on the machine, obtaining the user credentials. Later, the attacker will have to use a SSH tunnel in order to access to the device using adb and becoming root.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port getting more information about each service.
Looking on google about information for each port we discover that the port 59777 is used by the application ES File Explorer and has an CVE with a PoC on GitHub.
Exploitation
Executing the PoC we can obtain the pictures stored in the device.
Between all of them there is a file named creds.jgp that we can download with the following command.
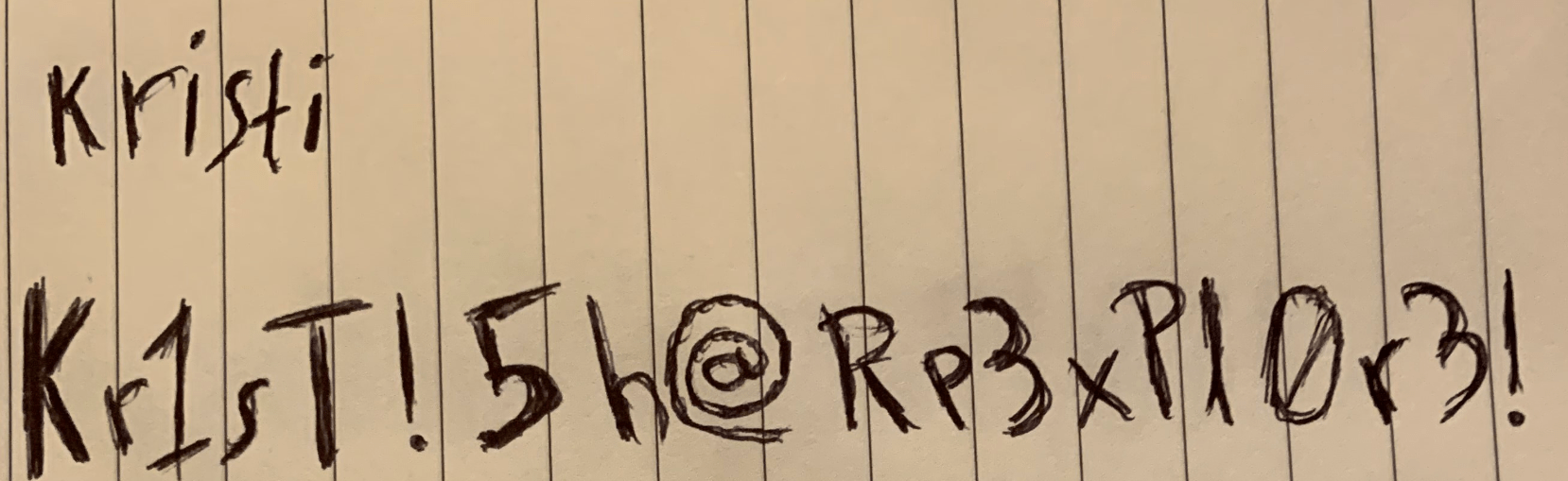
In this photo we can read the user kristi and the password Kr1sT!5h@Rp3xPl0r3! that can be used for getting access through ssh.
The user flag can be found at /sdcard/user.txt.
Privilege Escalation
Looking inside the file/etc/init.sh we can see that the port 5555 is being blocked by iptables so we can not access to the device using adb unless we create an SSH tunnel.
In order to create that tunnel we need to execute the following command.
- The flag
-Lcreates a link in the local port 5555. - The flag
-fputs SSH in the background so we can keep executing commands in the terminal. - The flag
-Ntells SSH that we do not want execute any command.
Once the tunnel has been created we can connect to the device using adb, becoming root pretty easily.
The commands are the following.