Dynstr - [HTB]
![Cover Image for Dynstr - [HTB]](/assets/images/blog/Dynstr-htb/Dynstr.png)

Introduction
Dynstr is a medium linux machine from HackTheBox where the attacker will have to execute some code on a DDNS API which doesn't sanitise its input in order to obtain a reverse shell. Then, will have to create subdomain with nsupdate in order to get access through the machine with an already created SSH certificate. Finally, will have to exploit a cp wildcard script in order to obtain SUID bash which will lead her or him to become root.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port getting more information about each service.
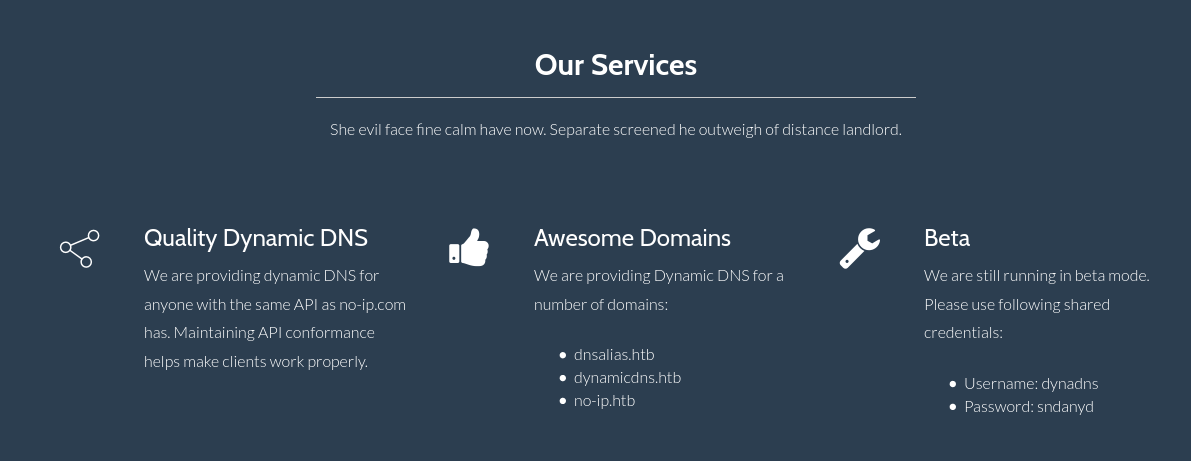
Having a look at the web page we can get information about the company Dynamic DNS API with its domains and credentials.
Using gobuster we can retrieve an unusual directory.
Accessing to the web page we obtain nothing but a blank screen, but searching on Google about the NO-IP API we can find a post explaining everything about how to perform queries to the API.
In order to update a domain we need to specify in the request URL the domain and the ip with the parameters hostname and myip. Furthermore, we need to add the basic Authorization header and modify the User-Agent to identity our request.
The request would be the following.
Obtaining the following result.
Looking at the no-ip response documentation it seems that we have and error.
| Status | Description | |
|---|---|---|
| 911 | Error | A fatal error on our side such as a database outage. Retry the update no sooner than 30 minutes. A 500 HTTP error may also be returned in case of a fatal error on our system at which point you should also retry no sooner than 30 minutes. |
After fooling around with the subdomains in the hostname parameter we got the following result.
Request:
Response:
Looking on google about nsupdate seems that is a linux binary for dynamic DNS updates, so maybe the user input isn't sanitised.
Explotation
Injecting "; id # as subdomain we obtain RCE.
Request:
Response:
In order to obtain an reverse shell we need to encode the following command in Base64 so there isn't any dot in the payload that could intercept the program as a subdomain.
Then we need to add the following commands to decode and execute our payload.
Finally, we only need to URL encode the exploit.
The final request is the following:
Response:
Privilege Escalation 1
Inside the folder /home/bindmgr/support-case-C62796521/ there are several debugging files.
In the file C62796521-debugging.script we can find the following command where we can see the debugging execution of the curl command.
Furthermore we can find the bindmgr's private key in the same file.
The sanitised key is the following.
However the private key needs a password that we can not obtain via john or hashcat.
Looking at authorized_key we can see that we have access from any infra.dyna.htb subdomain.
Looking at the php code we can retrieve an example of how to update domains in this machine.
Furthermore, inside the /etc/bind/named.conf.local we can find information about the infra.key which will be needed for updating the zone 10.in-addr.arpa (Hack The Box network).
Using this webpage we can create a DNS registry with the subdomain .infra.dyna.htb.
Note: For some reason I could not comprehend creating a registry for the subsubdomain "sftp.infra.dyna.htb" does not work, so you need to use other.
Now, we are able to access to the machine as bindmgr through SSH.
Privilege Escalation 2
The user bindmgr can execute the script /usr/local/bin/bindmgr.sh as sudo.
Analyzing the script we can see that it checks for a .version file, compares its version with the one at /etc/bind/named.bindmgr/.version, then copies every single file in the current directory to /etc/bind/named.bindmgr using wildcards.
Thanks to this post and looking at the cp documentation we can any any file keeping its privileges (--preserve=mode ) . In this scenario we will be coping a SUID bash binary that once executed we will become owned by root.
In order to do so we need to execute the following commands.