Driver - [HTB]
![Cover Image for Driver - [HTB]](/assets/images/blog/Driver-htb/Driver.png)

Introduction
Driver is an easy windows machine from HackTheBox where the attacker will have to craft a unique windows shortcut to obtain an NTLM hash that can be used to access the machine, obtaining the user flag. Finally, the attacker will have to exploit the PrintNightmare vulnerability to create a system account as Administrator, getting the root flag.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Looking at port 80, we get prompted for some credentials, which turned out to be admin:admin. Once inside the web page, we obtain the domain driver.htb.
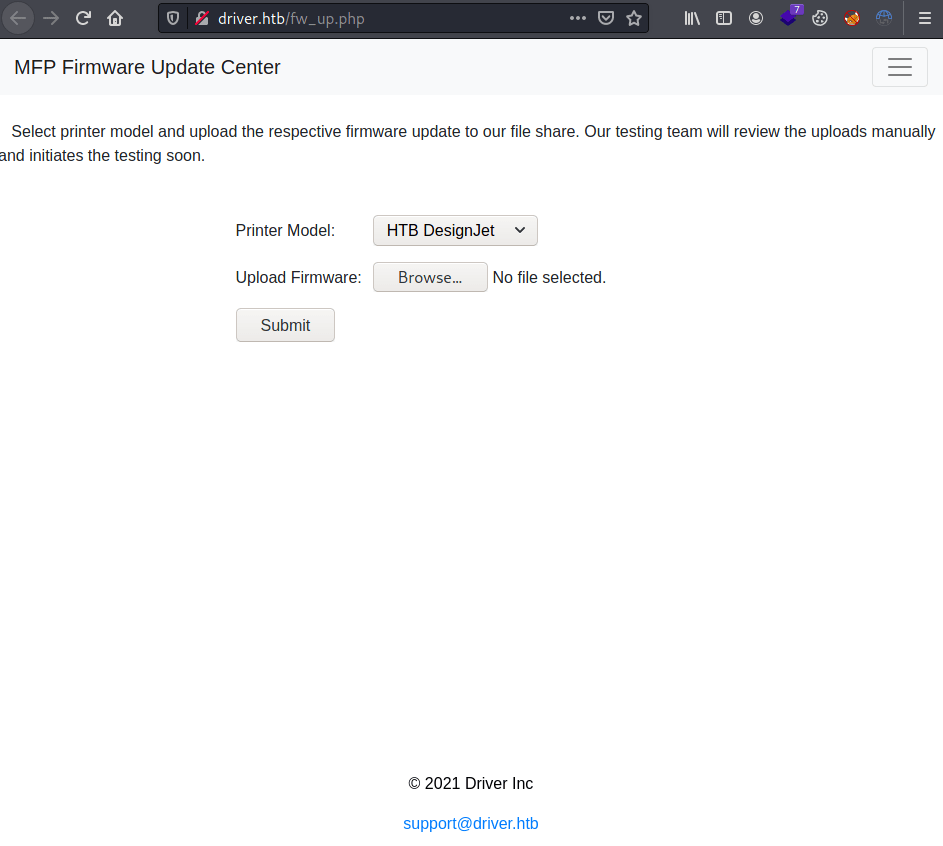
Looking around, we top us with this form where each file we upload will be stored into their file share and will be manually tested.
Exploitation
Because the files are going to be reviewed manually and they are stored on a file share, there is a way to obtain an NTLM hash by crafting a windows shortcut and the responder tool.
In order to craft a windows shortcut on Linux, we can use mslink as follows.
Now, we get Tony's NTLM hash starting the responder and uploading the shortcut.
Using john, we can obtain its password.
Because port 5985 is opened, we can access the machine through evil-winrm, getting the user flag.
Privilege Escalation
Because the machine is entirely related about printers and it is a windows machine, I thought it might be vulnerable to PrintNightmare, which turned out to be true.
Because running PowerShell scripts are not allowed, we need to bypass it by executing the script directly from memory.
To do so, we need to execute the following command.
Once executed, now we can log in as Marmeus through evil-winrm getting the root flag.