Doctor - [HTB]
![Cover Image for Doctor - [HTB]](/assets/images/blog/Doctor/Doctor.PNG)

Introduction
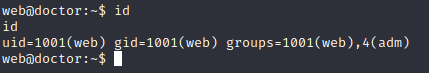
Doctor is an easy Linux HackTheBox level machine. Where the attaker will have to do some python injection in a certain form to reproduce a RCE due to a template vulnerability. Then, he or she will have to look for a special log file which contains a password required to do the final privilege escalation using the exposed API.
Enumeration
As always I start scanning all ports so I see every single hidden service on the machine.
Then I continue with a more in depth scan of all of every listed service shown in the previous scan.
There are three services: two HTPP and a SSH.
For one side, there is a clinic web page in the port 80.
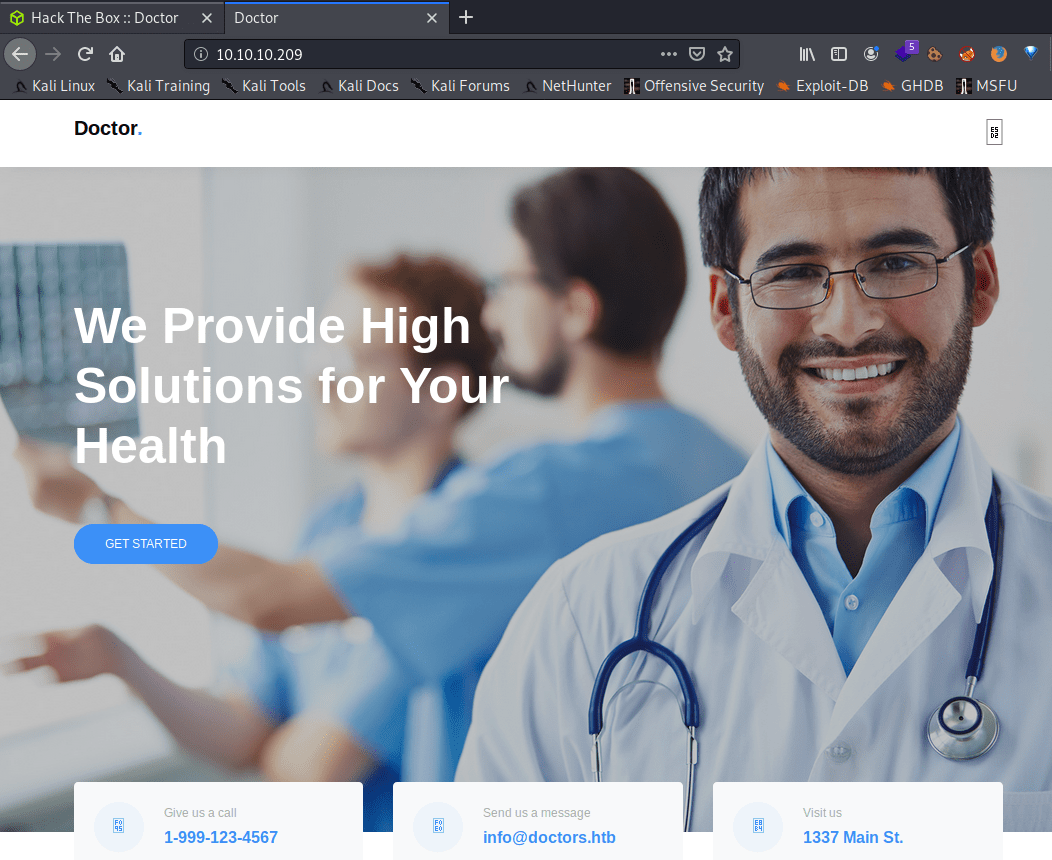
Using dirb doesn't provide any helpful information.
For the other side, there is an API in the splunkd service (The system process that handles indexing, searching, forwarding, and (as of Splunk Enterprise version 6.2) the Web interface that you log into Splunk Enterprise with).
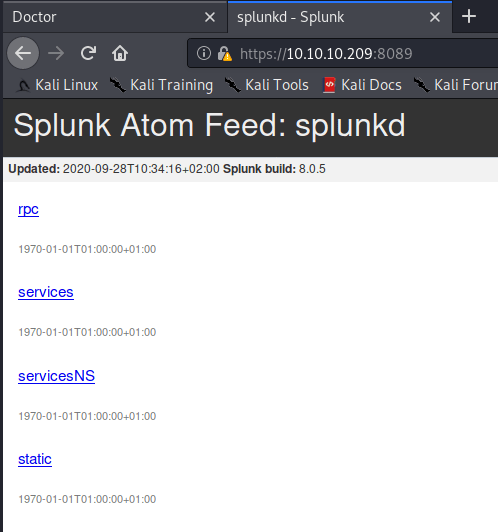
Dirb doesn't provide any useful information, just some pages that require user's credentials.
Looking closely to the clinic web page you can find a new domain "doctors.htb". Adding this domain to the /etc/hosts file, allow us to access to a login panel.
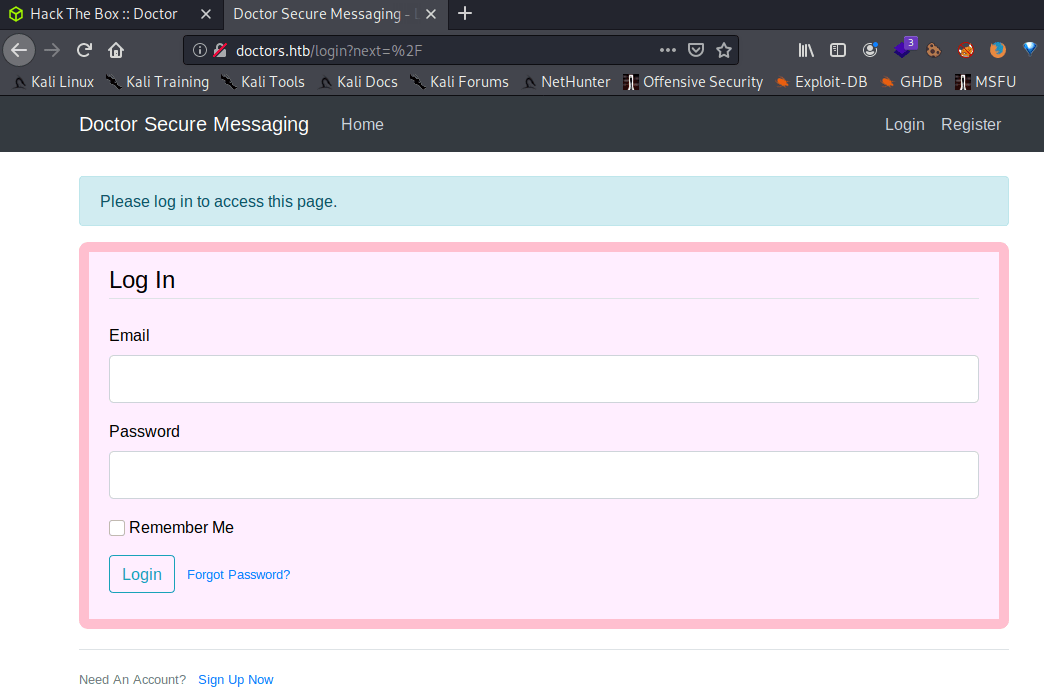
Furthermore, inside the HTML code you can find the following comment.
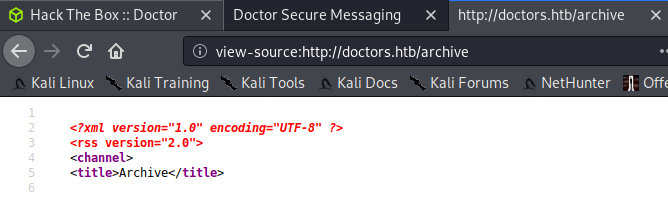
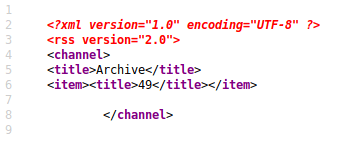
Browsing to that URL you can find a hidden page, that will be useful later on.
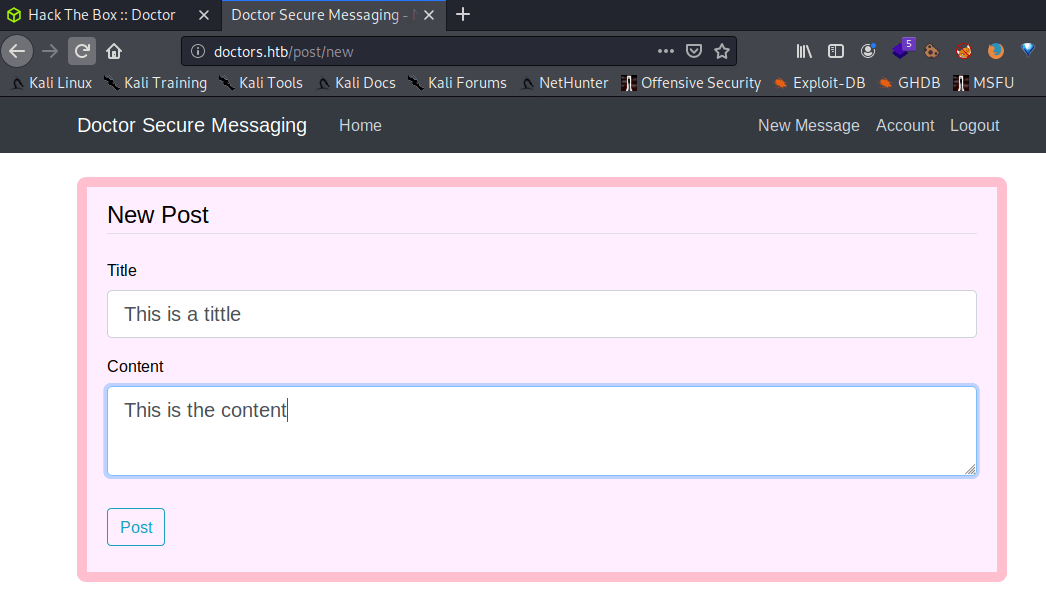
In order to access to the web application you need to create an account. Then, you will be able to create messages that will appear in the main panel.
Note: The session only last for 20 minutes, so every payload that you have create will be removed.
Explotation
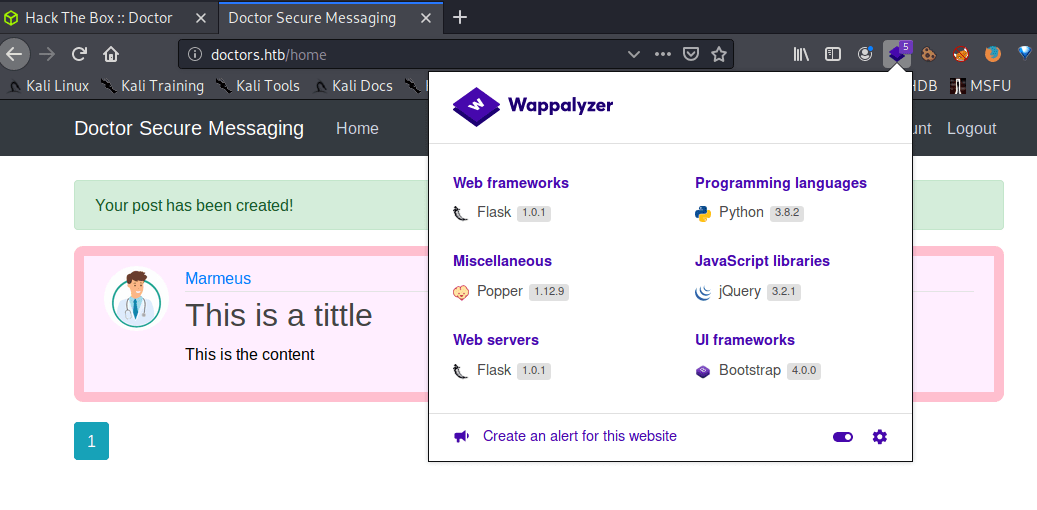
As you can see in the previous section, this web page is using Flask as framework (Flask is a micro web framework written in Python. It is classified as a microframework because it does not require particular tools or libraries. It has no database abstraction layer, form validation, or any other components where pre-existing third-party libraries provide common functions.) that can execute an RCE introducing python instructions inside the input forms. Following this article you will find essential information about python injection.
Inserting {{7 * 7}} in the tittle form, we can see how we get the result once the message has been submitted. However, you will not see the result in the main panel. Do you remember the hidden web page I said earlier? Well, the results appear there.
There is a GitHub repository named PayloadAllTheThings where you can find the code that you have to insert in the title input in order to create a reverse shell.
Note: You need to visit "http://doctors.htb/archive" in order to get the reverse shell.
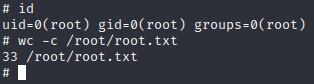
Privilege escalation 1
Usually, hack the box machine icons illustrate what the machine is about, in this case there is a log so would be interesting look for some logs with credentials. In the apache2 log folder there is a backup file /var/log/apache2/backup. Doing a search with grep we can find a possible password.
This password belongs to user "shaun". Also, this password can be used to gain access to the splunkd service web page that was mentioned earlier.
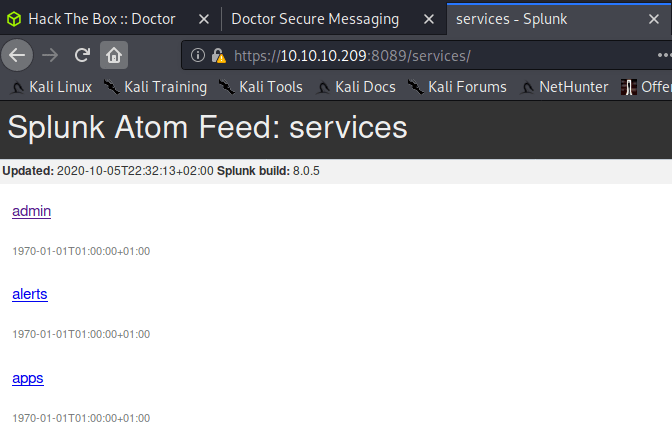
Searching on google about splunkd you will find a GitHub repository to elevate privileges. But before executing our exploit I am going to improve my shell generating a ssh key and then adding the public key to the .ssh/authorized_keys file.
Then, you need to add the id_rsa.pub file to the .ssh/authorized_keys file.
Lastly, you only have to ssh as the user web.
Privilege escalation 2
The exploit I am going to use is PySplunkWhisperer2_remote.py so I can create a reverse shell without accessing to the virtual machine.
Firstly, I am going to use netcat and rlwrap to create a listening port.
Finally, in order to become root, you will only have to execute the following command, changing the IP address of your local machine to gain a root reverse shell.
Note: The payload was found in this web page.