Delivery - [HTB]
![Cover Image for Delivery - [HTB]](/assets/images/blog/Delivery-htb/Delivery.png)

Introduction
Delivery is a very easy Linux machine from HackTheBox where the hacker will have to find the way to validate an email using two instaled services on the machine, in order to get the user flag. Later, will have to find the root hash, stored in a web page databaseFinally, in order to obatin the root password will have to crack the hash using hashcat rules.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Inside the port 80 there is an static web page named "DELIVERY" with a "Contact us" button.
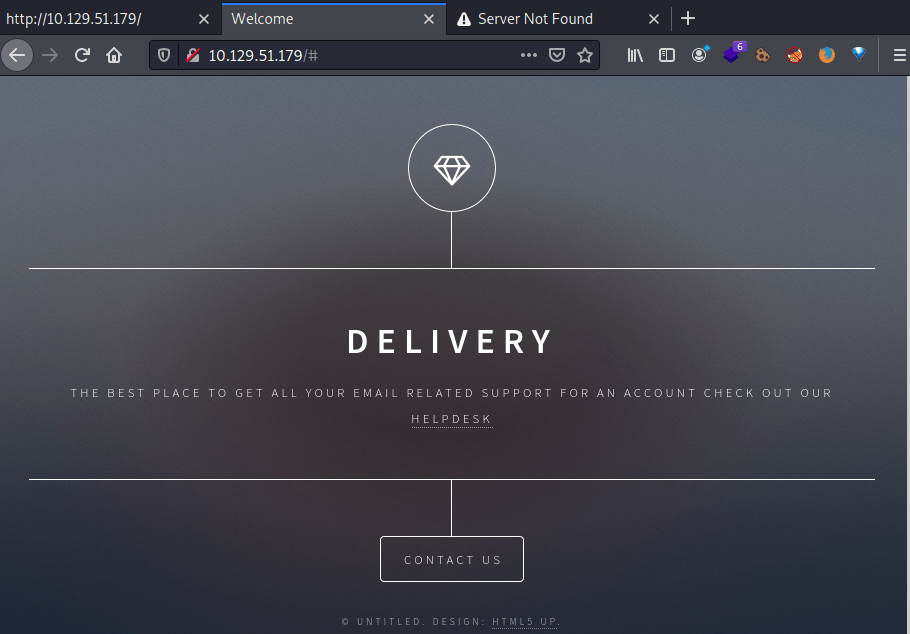
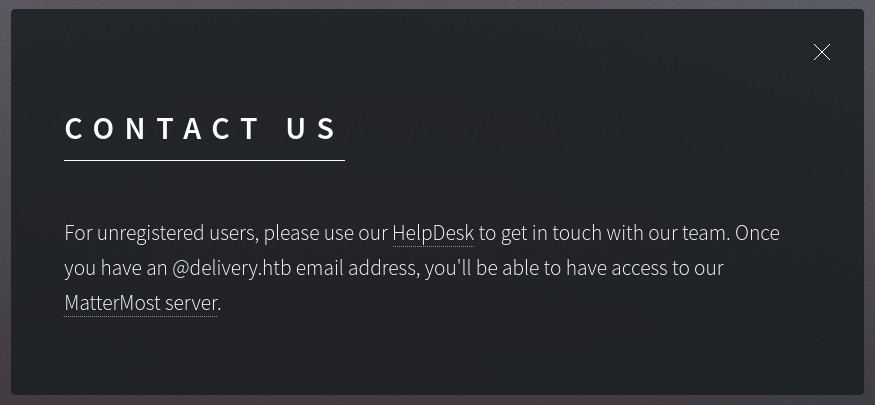
Clicking on it, we can see two links: http://helpdesk.delivery.htb/ and http://delivery.htb:8065/. Both pointing to two different services and domains.
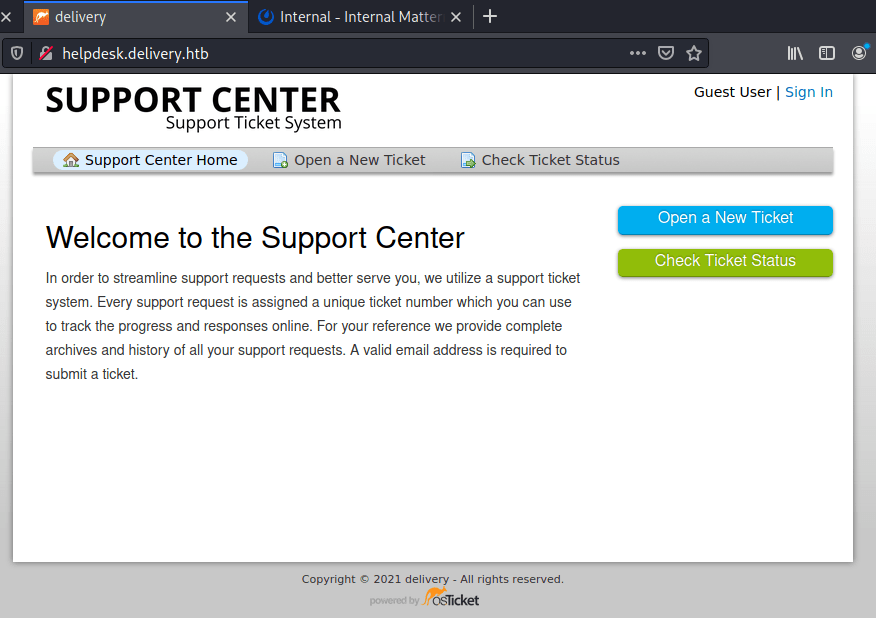
For one side in, helpdesk.delivery.htb we can find a Ticket System developed by osTicket, where we can create tickets for getting in contact with the support center.
In order to create and account we need to verify an email. This is impossible because HTB machines doesn't have access to the Internet, so we can not receive any eamil to our personal accounts.
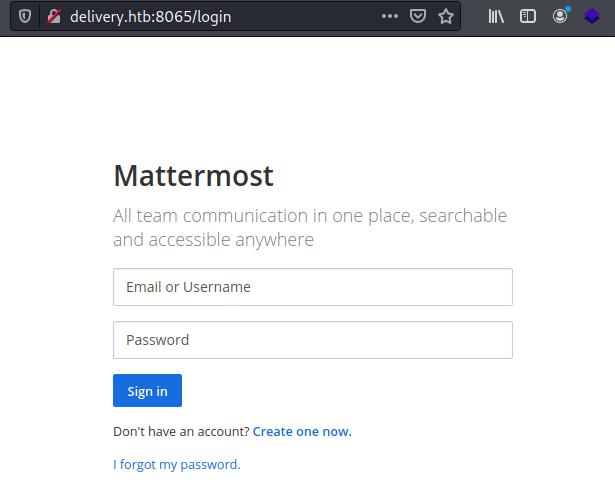
For the other side, delivery.htb:8065 turns out to be a Mattermost service (an open-source, self-hostable online chat service) that also requires validating the email for signing up.
Explotation
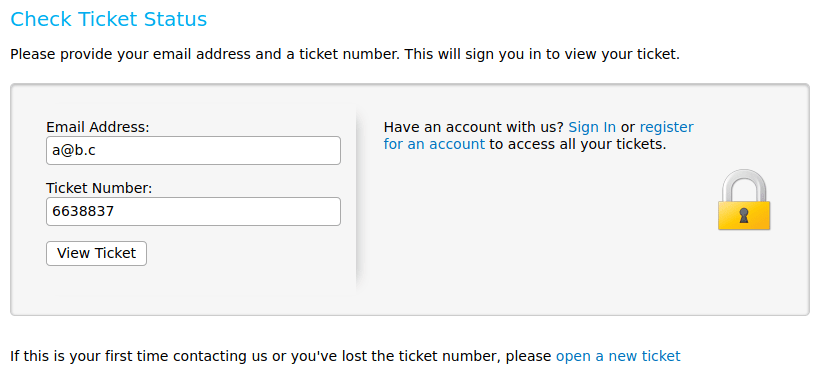
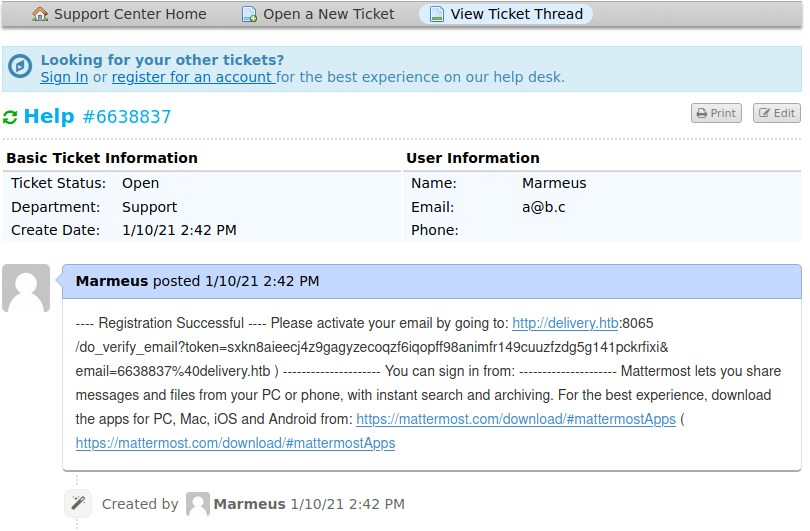
We can obtain an email creating a ticket in Help Desk.
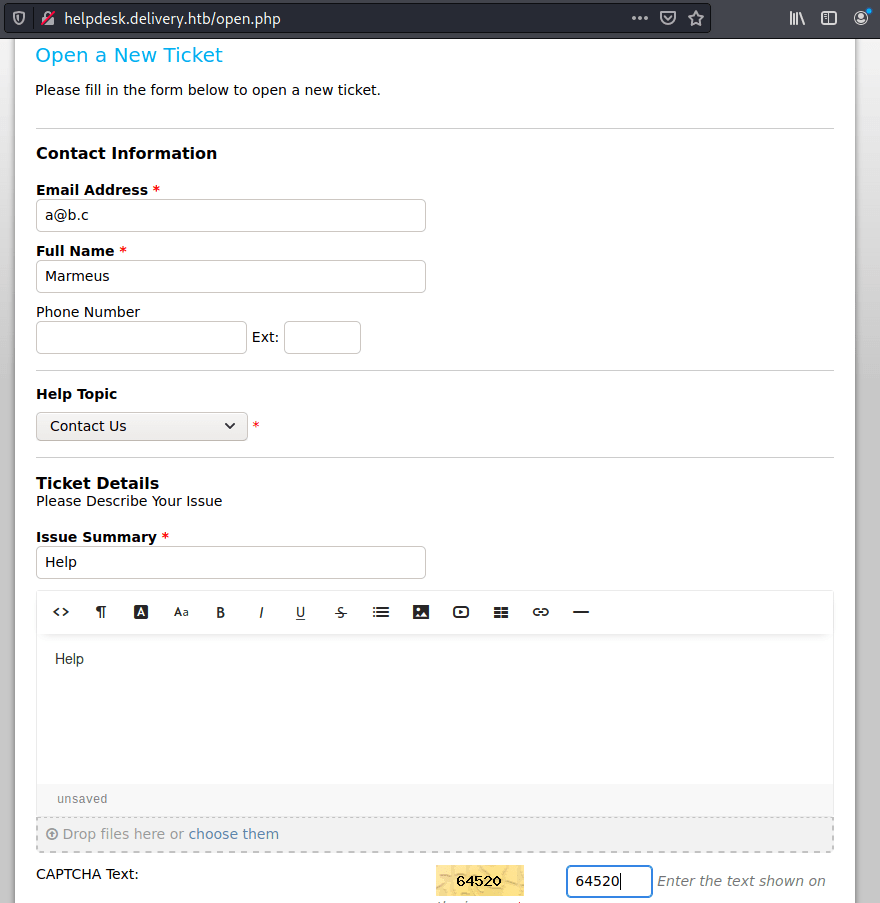
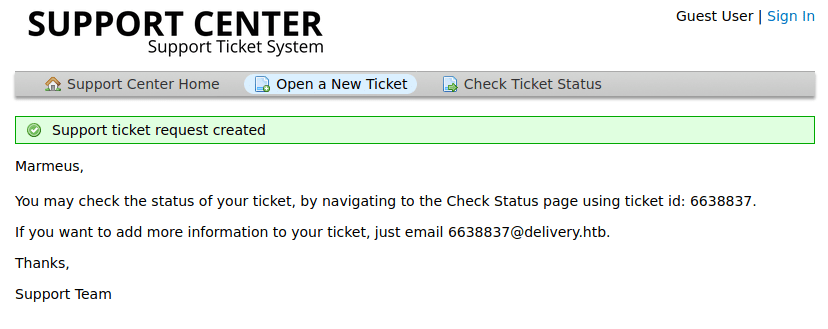
The email address can be used to send information to the ticket. Hence, we can use the address to verify the email in the Mattermost service.
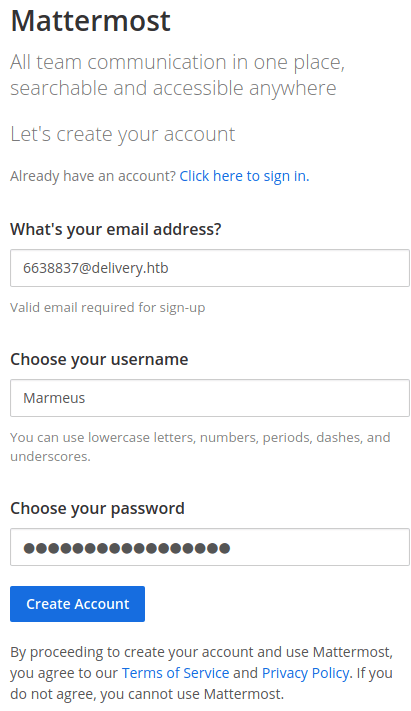
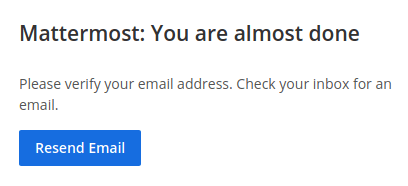
Then, we need to check the ticket, obtaining the verification link.
Note: You need to provided the email address used to open a ticket.
Finally, sign in with the user you created, skip the tutorial and click on "Internal" and you will get the credential for accessings to login into the machine as maildeliverer through SSH (Getting the user flag). Furthermore, these credentials can also be used for signing in http://helpdesk.delivery.htb/scp/users.php
Privilege escalation
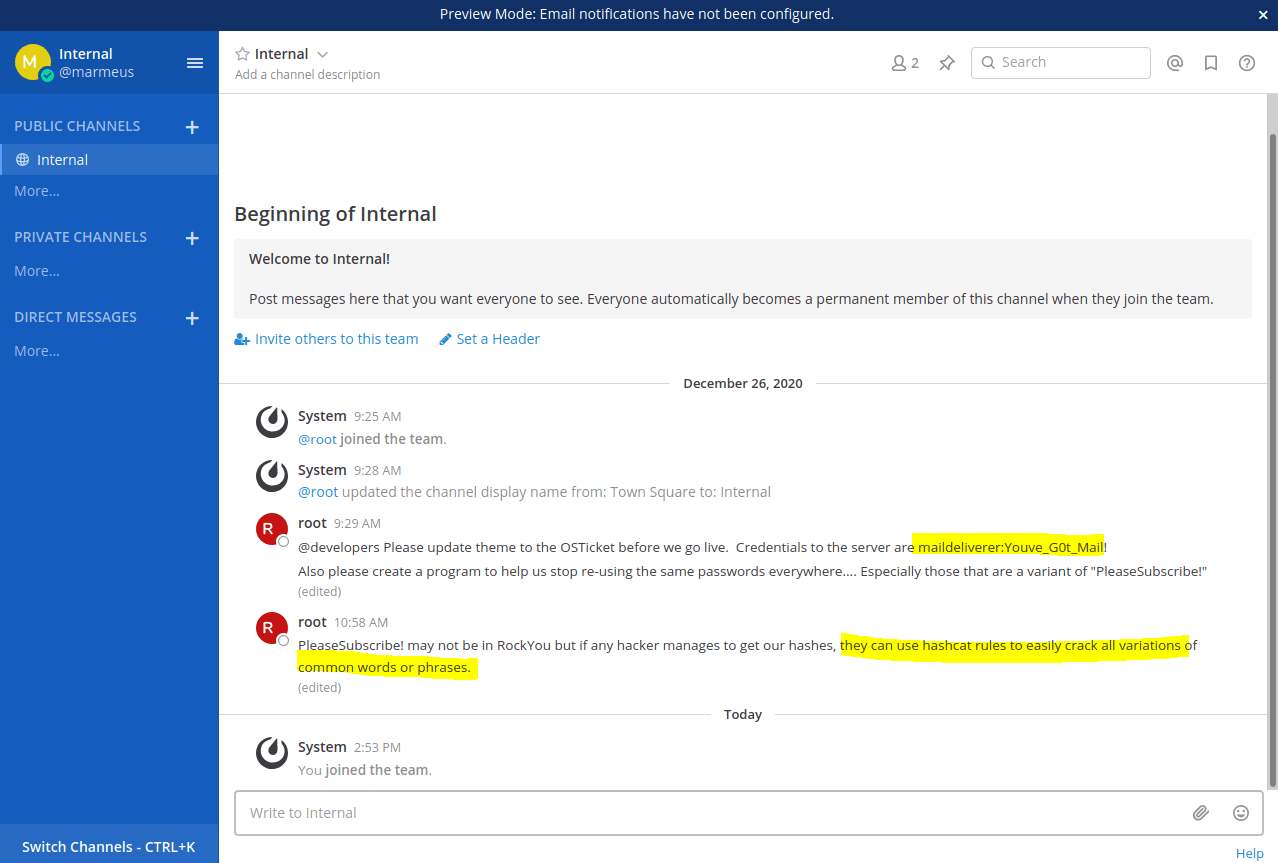
In the previous picture the root user is telling that if an attacker get all the hashes from the web page, he or she will be able to retrieve the password using HashCat. So, looking in the Mattermos documentation the mysql credentials are stored at /opt/mattermost/config/config.json.
The credentials are:
Now we can extract all the hashes from the database.
Now, we can use HashCat to get the root's password. For that I used hashcat for windows that you can download it here. But first we need to identify which type of hash are we working with, so I am using hashid.
Based on what the user "root" said in the mattermost chat, I created my own mask which tries numbers, lower and upper case letters at the end of PleaseSubscribe!, retrieving the password in a couple of seconds.
Note: You could try obtaining the root password by applying predetermined hashcat rules such us base64.
Finally, we can use this password to become root, getting the root flag.