Catch - [HTB]
![Cover Image for Catch - [HTB]](/assets/images/blog/Catch-htb/Catch.png)

Introduction
Catch is a medium HackTheBox machine where the attacker will have to do a static analysis of an Android application in order to obtain a Let's chat API token. Then, it will have to use the API to exfiltrate messages from some chat rooms obtaining some credentials for Cachet platform. After that, it will have to exploit a Cachet vulnerability to obtain the database's credentials, access the machine and get the user flag. Finally, it will have to exploit an improper input validation on a crontab script, compiling a malicious application, to obtain a reverse shell as root.
Enumeration
As always, let's start finding all opened ports in the machine with Nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
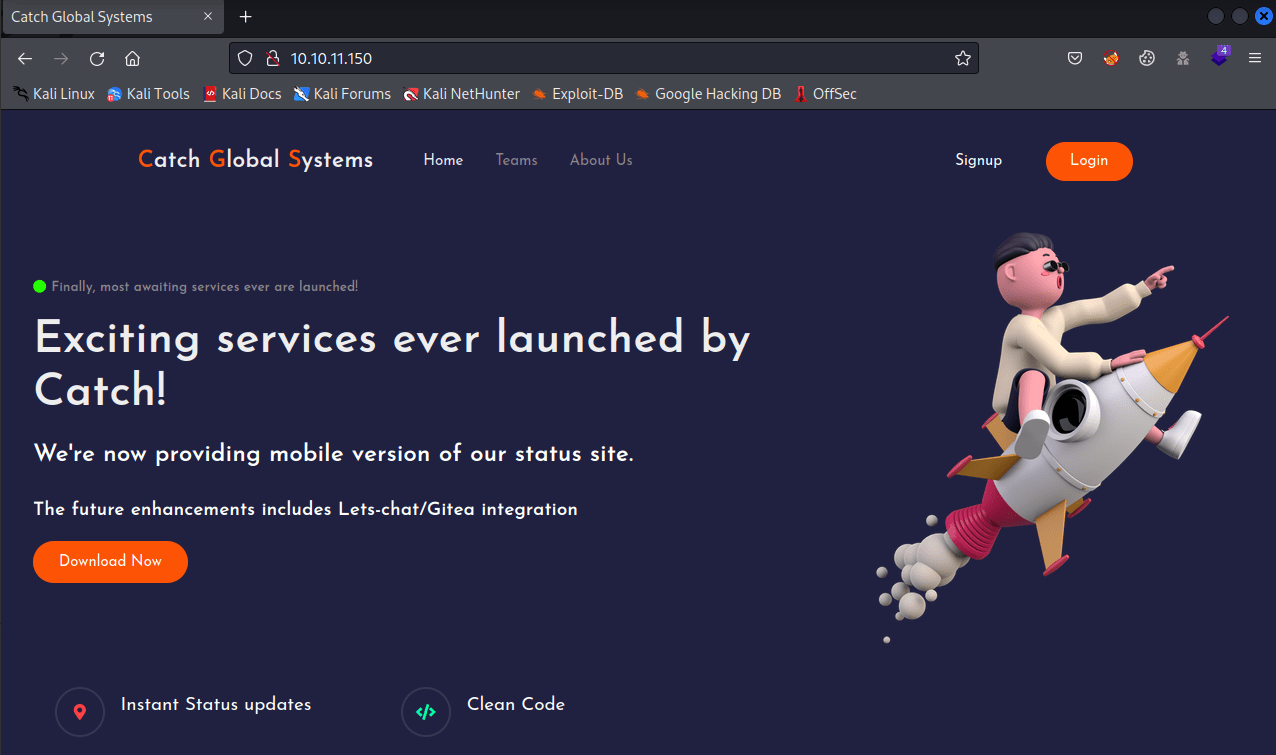
Starting with port 80 there is a web talking about two technologies Let's chat and Gitea. Furthermore, we can download the APK "catchv1.0".
Proceeding with port 3000, there is a Gitea web page.
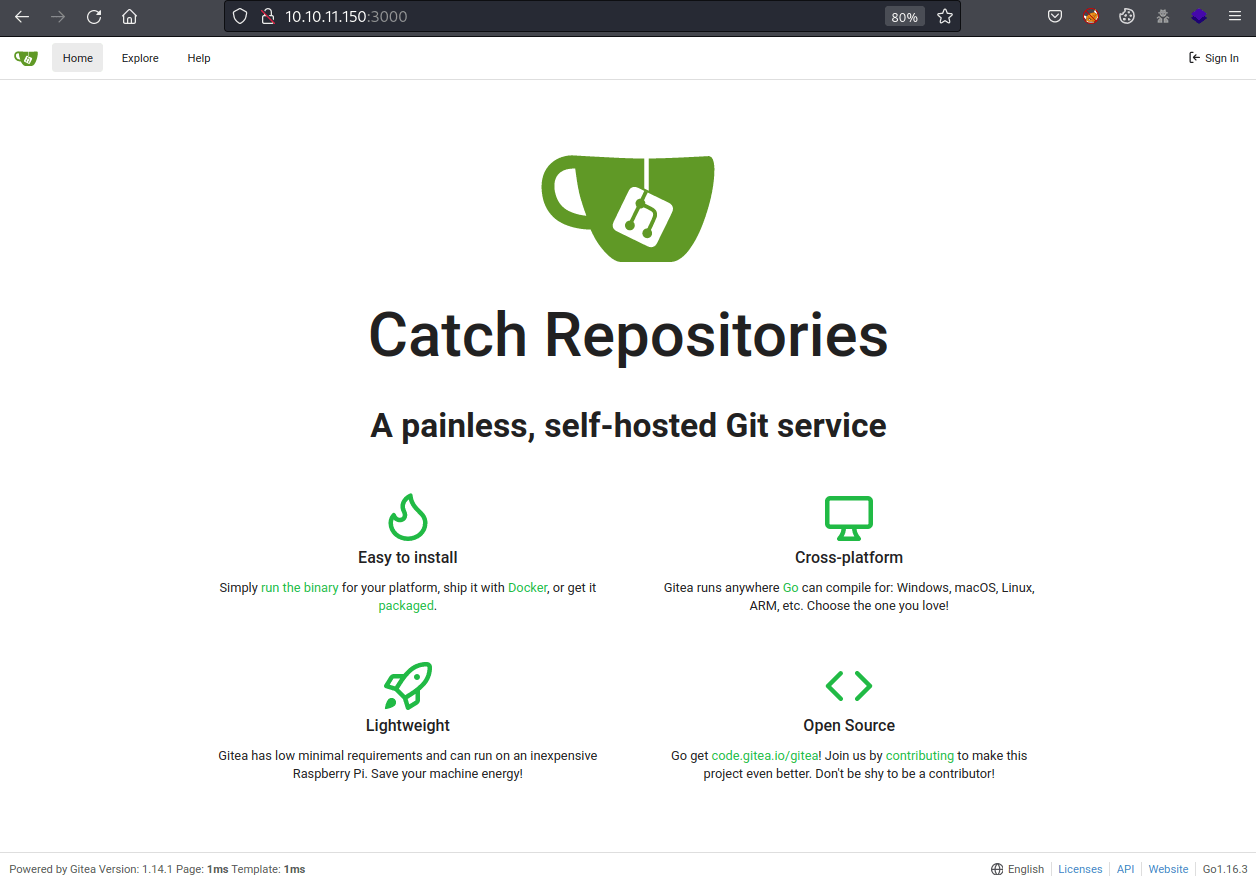
In there, a new subdomain can be found.
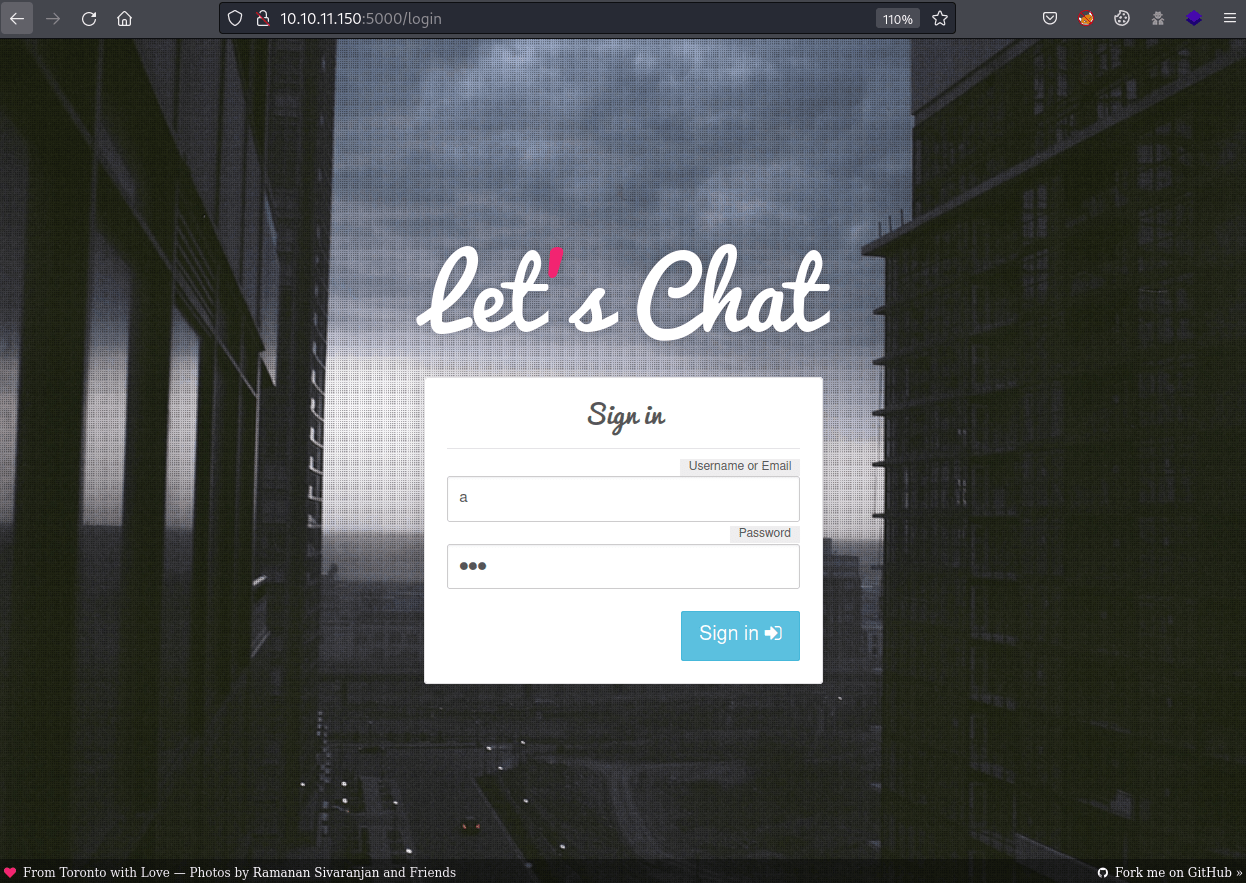
Then, at port 5000, there is the Let's chat web page.
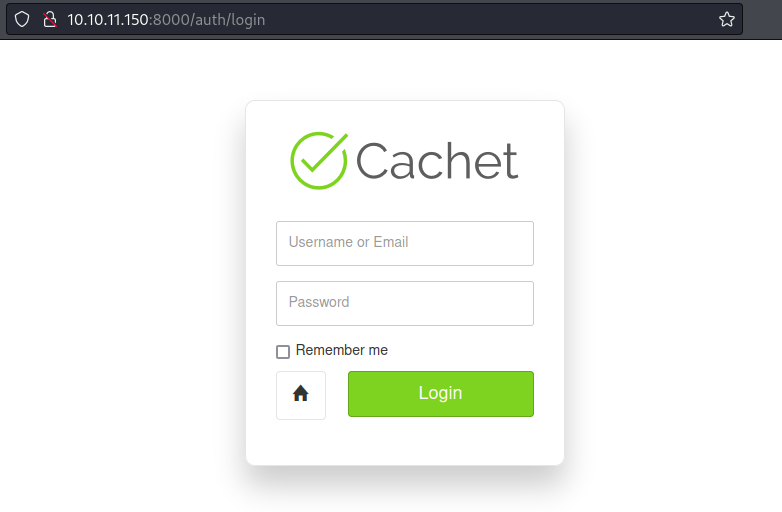
Finally, at port 8000, there is a Cachet portal.
Now, let's start analysing the APK.
Looking for domains, the subdomain status.catch.htb can be found.
Then, looking for tokens, the lets_chat_token can also be found.
Exploitation 1
Looking at the let's chat API, there is an Authentication section showing how to log in. To do so, let's try to obtain the current account, executing the following command and using the lets_chat_token as an authentication token.
Some credentials can be obtained by looking at the messages for each open room.
The credentials john:E}V!mywu_69T4C}W can be used on the cachet login panel.
Exploitation 2
The catchet's version can be obtained by accessing the settings panel.
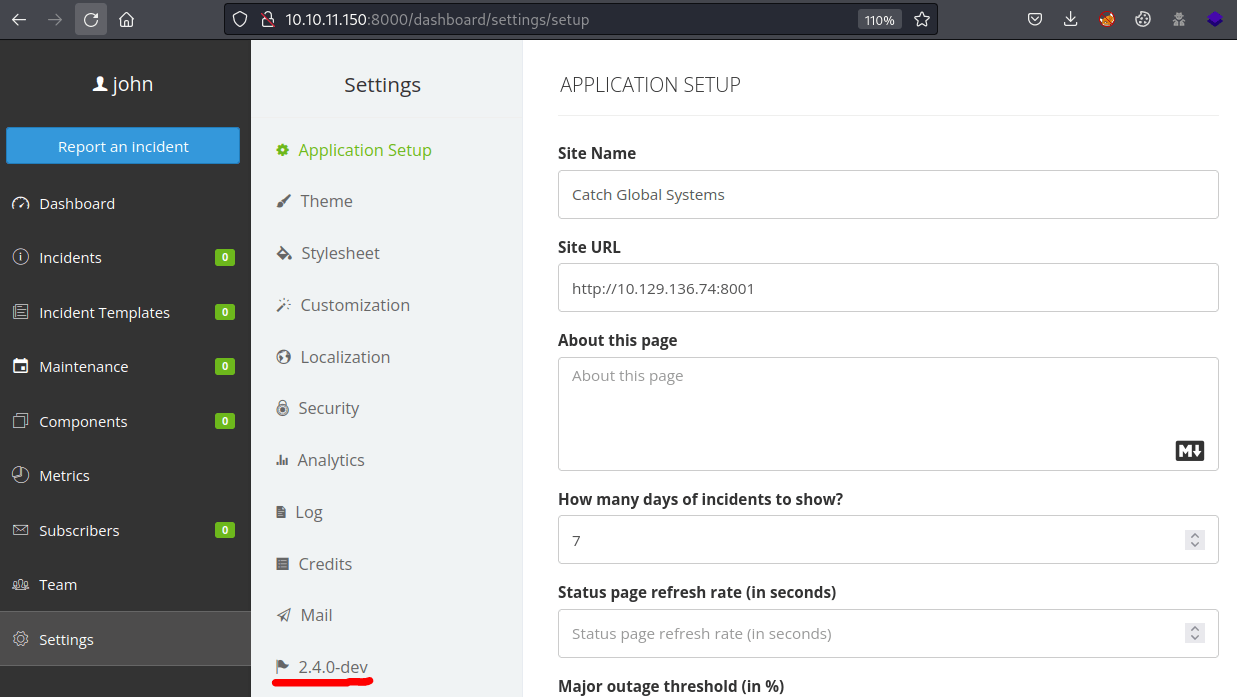
This version is vulnerable to CVE-2021-39174, which allows retrieving the database's password, as seen in this post.
To exploit this vulnerability, go to the mail settings, select the mail driver Log (Testing), click save and intercept the request with BurpSuite. Finally, change the config[mail_address] attribute by ${DB_USERNAME}.
After refreshing the page, you will obtain the user will. Doing the same procedure but changing the mail address attribute by ${DB_PASSWORD}, we get the password s2#4Fg0_%3!.
These credentials can be used for gaining access to the machine through SSH, obtaining the users' flag.
Privilege Escalation
Executing pspy, you can see that the script verify.sh is being executed each minute or so.
Analysing the /opt/mdm/verify.sh , we can see that the function app_check is vulnerable to improper input validation so we can execute code.
As you can see below, the function retrieves the value of the app_name variable. Then, if the string "Catch" appears on the application name, the name is piped to the mkdir command.
For example, the string "Catch; echo Hello" will create the directory Catch and execute the echo command.
Hence, using a malicious application's name can lead to escalate privileges.
Then, it is needed to recompile the application following this tutorial.
Note: Use the latest apktool version, or it will not work.
After that, if the application was signed successfully with the following command:
Finally, upload your malicious APK, waiting for the script to be executed.