Cap - [HTB]
![Cover Image for Cap - [HTB]](/assets/images/blog/cap-htb/cap.png)

Introduction
Cap is an easy linux machine from HackTheBox where we will have to know the natural numbers in order to obtain the user's credentials. Finally, in order to escalate privileges we will need to exploit a setuid capability for a python binary.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
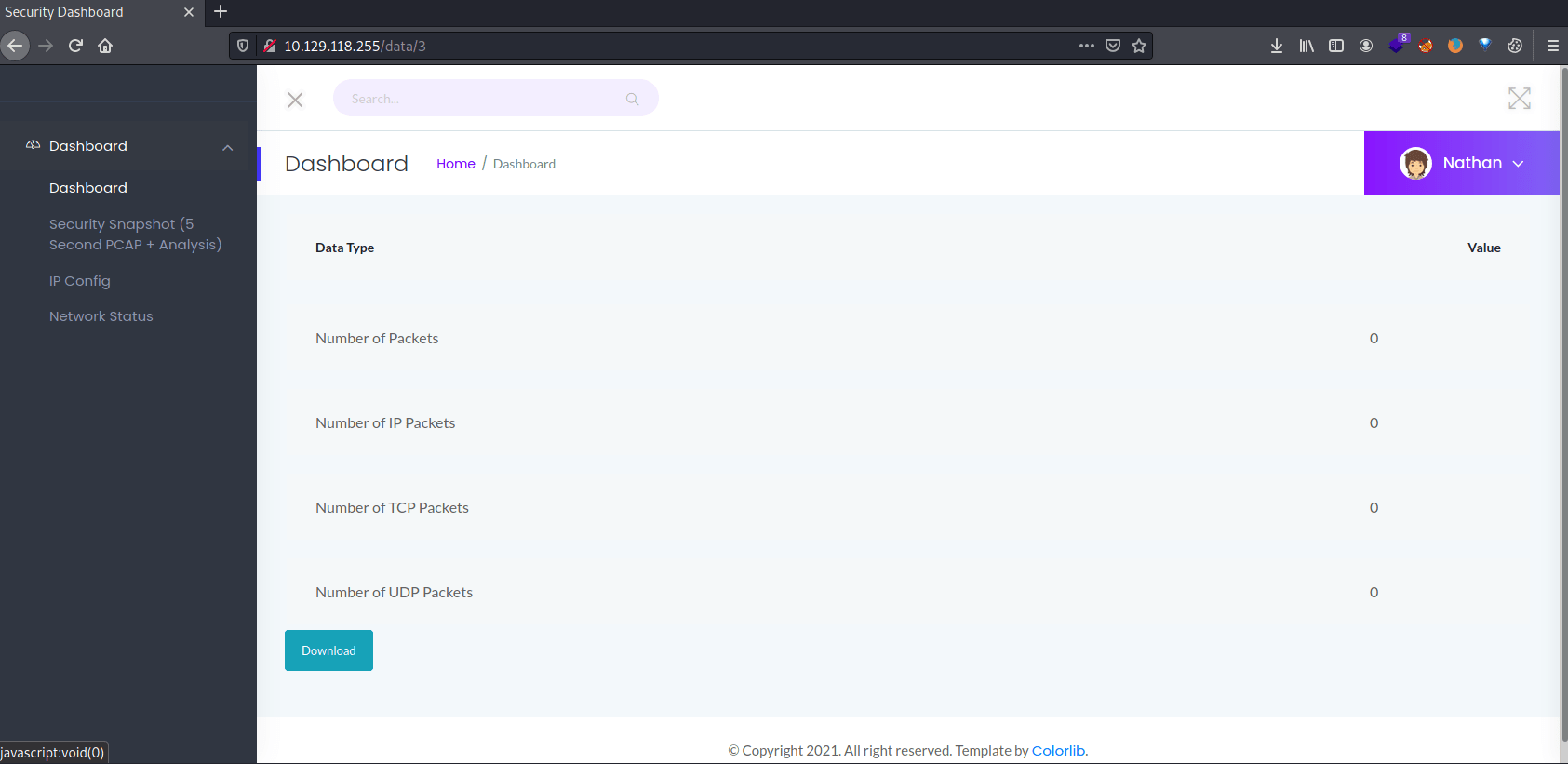
Inside the web page there is a meny with several functions where the commands ipconfig and netstat are being executed. Plus, there is another which provides us with a pcap file that we can download.
Explotation
If we look closely, we can see that the pcap files are identified with numbers (I.e. /data/X).
After some trial and error, it seems that the pcap identifier starts from 0 provide, so we can download a new pcap file, whcih looking inside with wireshark we can obtain FTP login credentials.
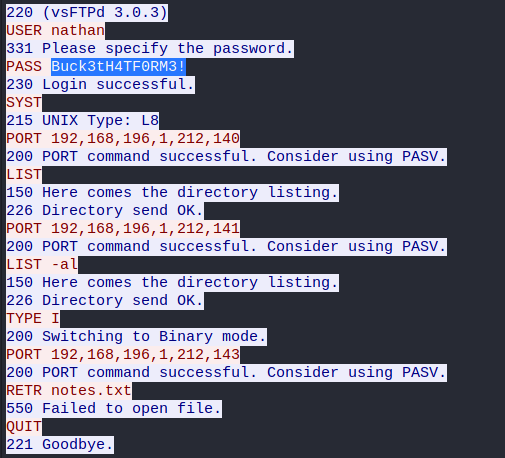
Accesing to the FTP service we can obtain the user flag, but we can also use the same credentials for the SSH service.
Privilege escalation
After executing linpeas we can see in the Capabilities section, python has setuid capabilities, hence we can escalate privileges as root following this post.
For doing so, we need to execute python as follows.
I hope you liked this easy box and if you need to ask me anything do not hesitate to contact me through my twitter account :P