Cache - [HTB]
![Cover Image for Cache - [HTB]](/assets/images/blog/cache-htb/Cache.PNG)

Introduction
Cache is a medium level Hack The Box Machine, in which you have to "hack" into a hacker's website, that lately will become a medical login portal in order to get a user. Then, you will have to enumerate several local services to find a special credentials, which allow you to become root through docker containers.
Enumeration
As always I start scanning all open ports so I know every single service running.
Then, I execute a more in depth scan against all services that were found in the previous scan.
Because there is only two services and one of them is SSH, which never has vulnerabilities associate to it, I don't have any no option but start analyzing the HTTP service.
Web
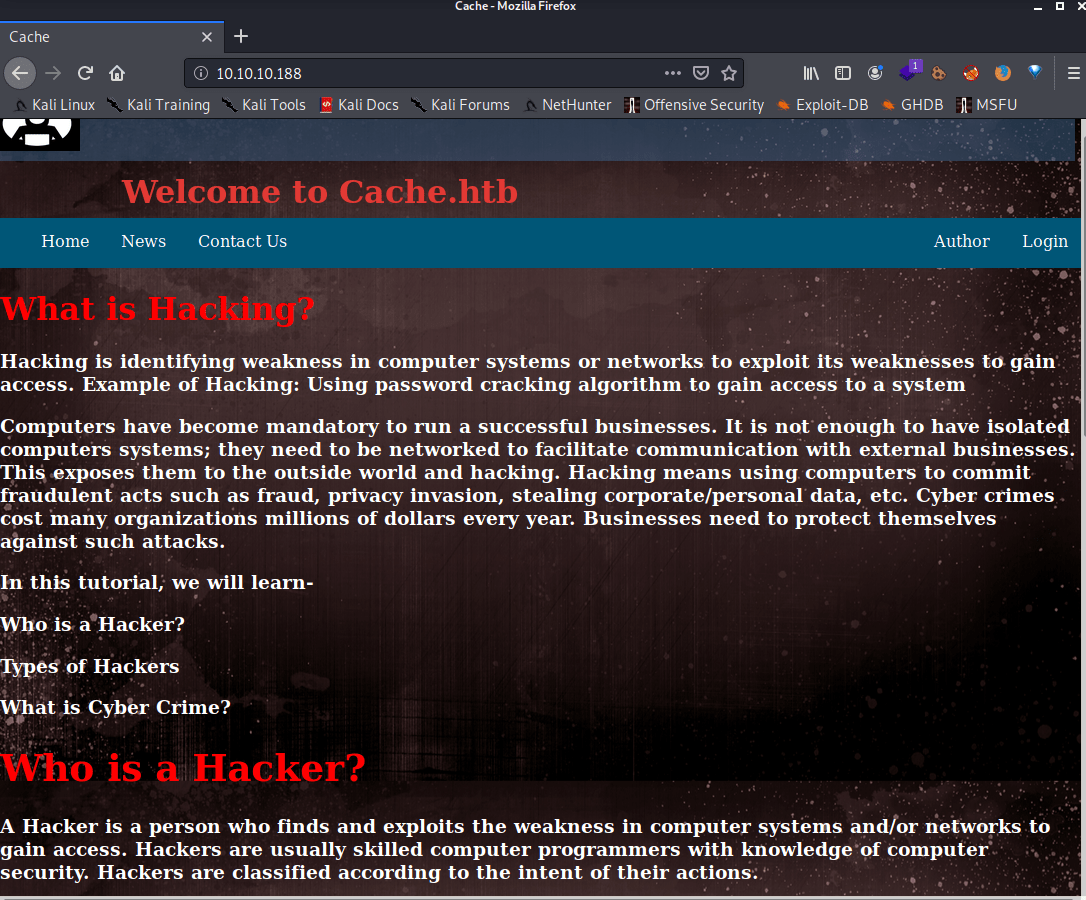
At first view I don't see anything interesting, so I used gobuster to find any hidden folder.
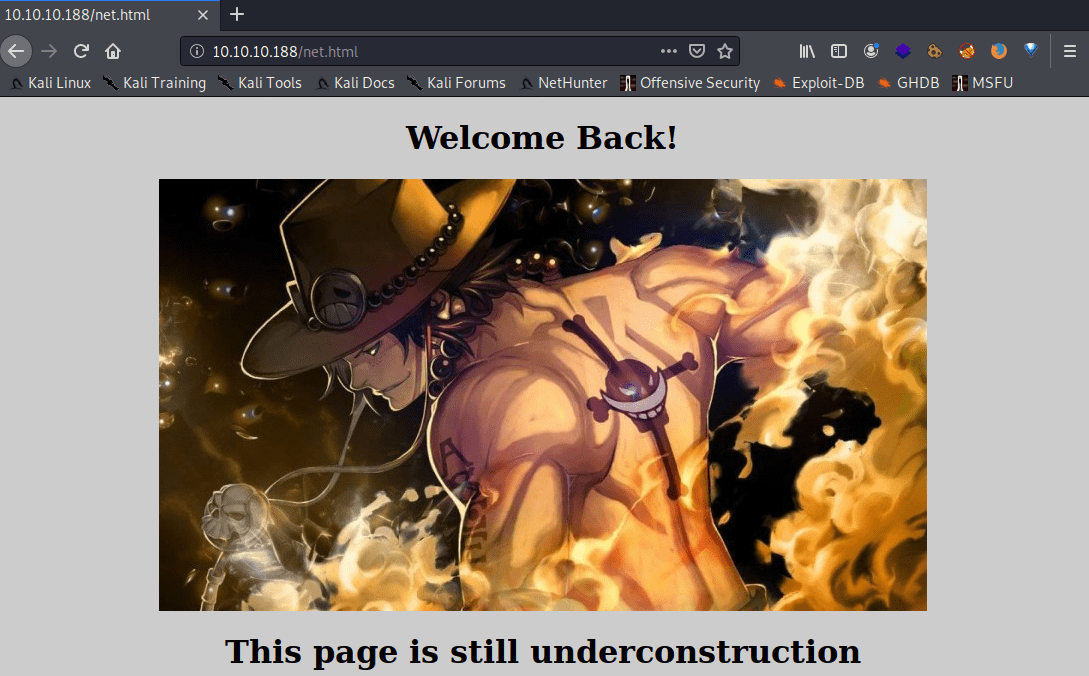
Inside the /jquery folder there is functionality.js file.
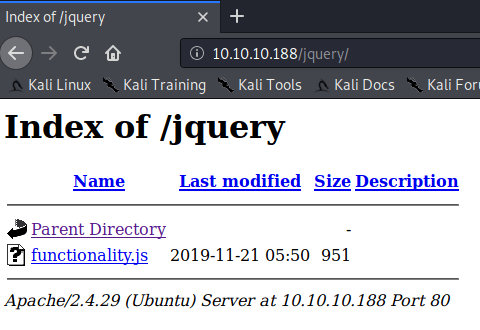
Looking at the code there are some hard written credentials, that can be used in the "login" section of the main web page.
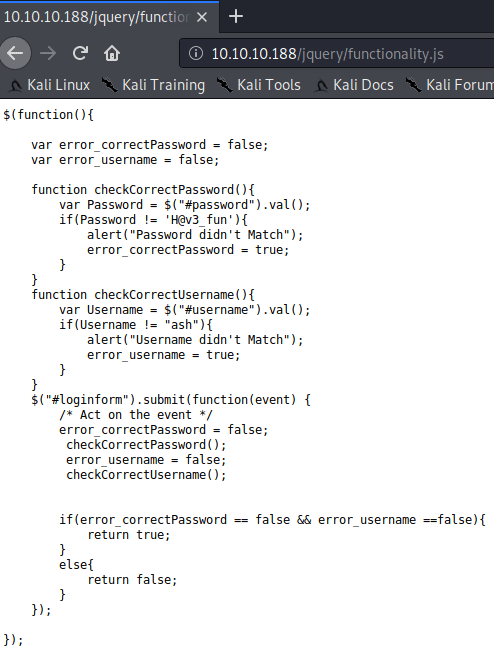
As you can see this page is under construction and there isn't anything useful.
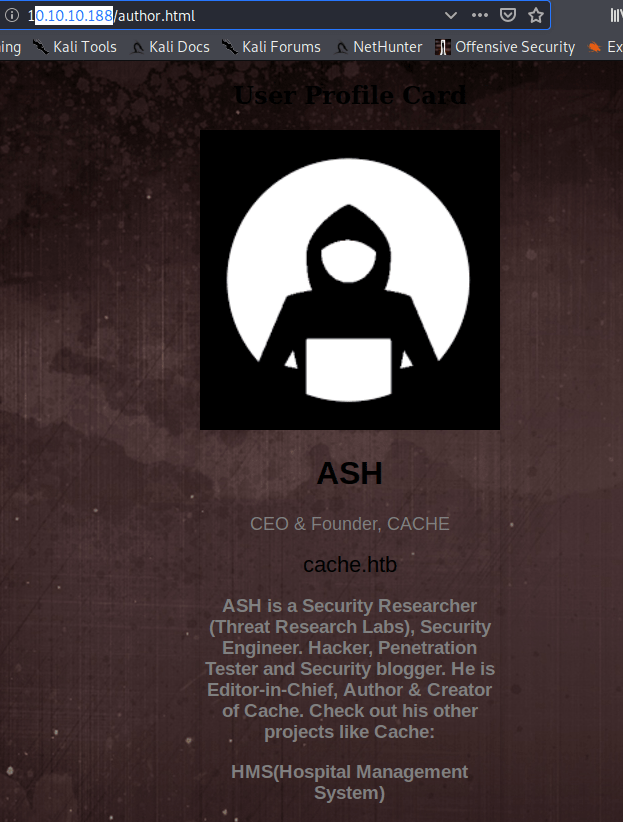
However, in the author page the "hacker" is talking about two projects: One named cache with its corresponding domain "cache.htb" and another project "HMS" (Hospital Management System).
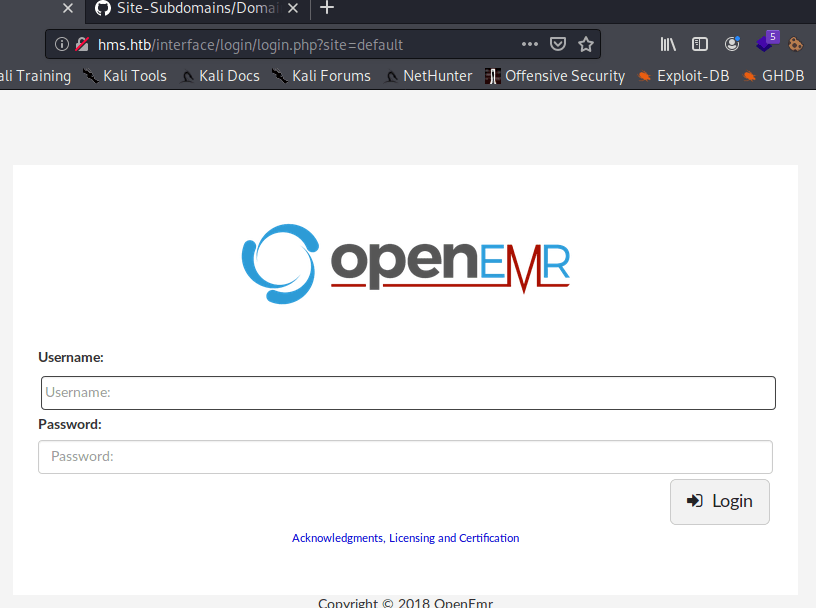
Using "hms.htb" as domain, appears an openEMR login portal. (OpenEMR is an open-source electronic medical record and practice management software.)
Explotation
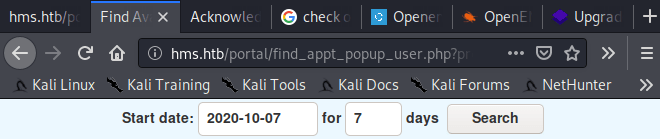
Through this document you can see that openEMR is vulnerable to several SQLi attacks, starting with the find_appt_popup_user.php file I got this page.
Note: In order to perform the sql injection attack you need to create an account at http://hms.htb/portal/index.php?site=default\&w
I stored the HTTP request in a txt file using burp.
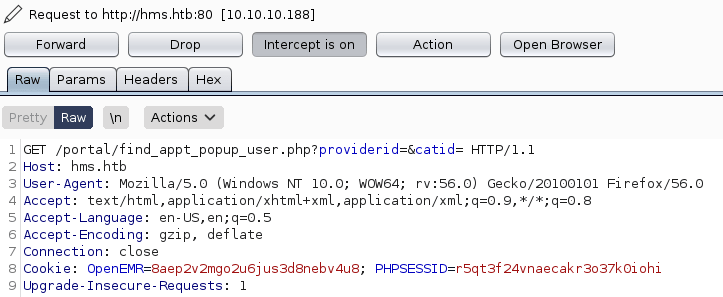
This request can be used with sqlmap in order to do sql injections obtaining the databases.
Note: The --batch is used for never ask for user input, using the default sqlmap behavior
Then, using sqlmap we can get the tables inside the openemr database.
Finally, the user information is at the users_secure table, so using nmap we can dump it.
The password can be cracked using John The Ripper (the hash.txt file looks like this "openemr_admin:$2a$05$l2sTLIG6GTBeyBf7TAKL6.ttEwJDmxs9bI6LXqlfCpEcY6VF6P0B.")
This credentials can be used with the exploit "5.0.1 - (Authenticated) Remote Code Execution" in order to get a reverse shell.
Later on, we can use python and ash credentials to get the user.txt flag.
Privilege escalation 1
Using netstat we can find a weird listening port "11211".
A quick search on San Google appears a penetration article for the service memcached. (Memcached server is used by corporations in order to increase the speed of their network as it helps to store frequently used data. This helps to take the load of the hardware and decrease the time taken.)
Following the article steps we can get the user "luffy" with a password "0n3_p1ec3".
This credentials can be used inside the linux machine to becoming the user luffy.
Privilege escalation 2
This user can run docker containers. Hence, taking a quick view to the gtfobins web page there is a command to get an interactive shell as root of the file system. However, the "alpine" image doesn't exists in this system, so we have to use ubuntu that is the one installed already.