Bucket - [HTB]
![Cover Image for Bucket - [HTB]](/assets/images/blog/Bucket-htb/Bucket.PNG)

Introduction
Bucket is a medium-hard HackTheBox machine where you will have to learn AWS buckets in order to upload a reverse shell, then in order to get the user's credentials you will need to learn about AWS DynamoDB so you can retrieve some users and passwords. Finally, you will have to exploit a service running inside a private AWS web service under construction to extract the root flag.
Enumeration
As always let's start scanning all opening ports in the box.
Then, continue with an exhaustively scan of each port.
Because there is nothing interesting let's have a look to the web page.
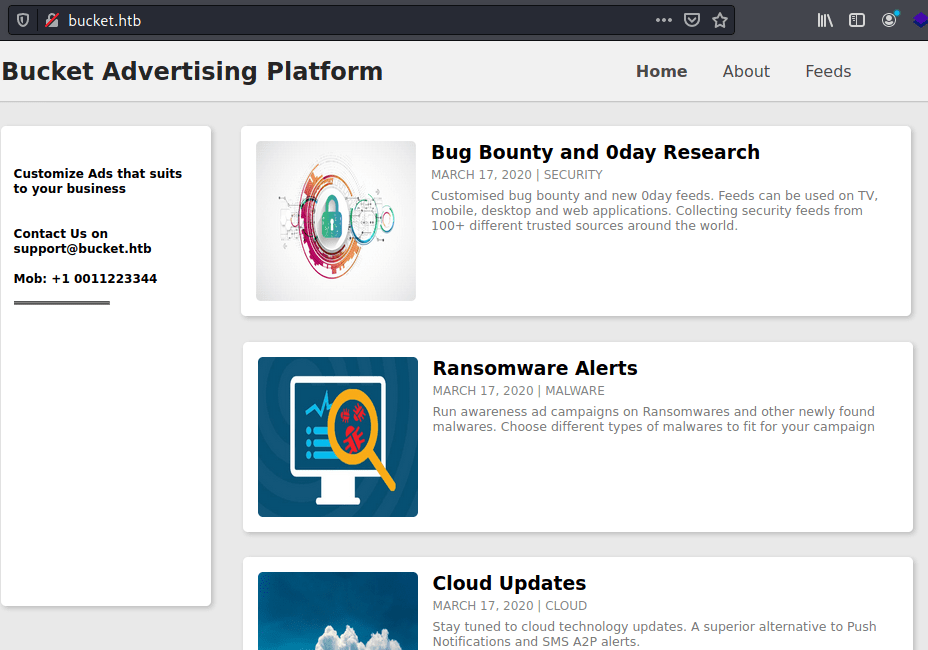
It seems like an informative page about cybersecurity. Looking inside the code there is a piece of code with a different domain where images are stored.
Once added the domain to the /etc/hosts file, we can get access to the domain, finding the following page.
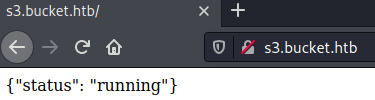
This is because we are getting access to a s3 aws bucket.
Amazon Simple Storage Service is an object storage service that you can interact using the command line, doing things like uploading files.
In order to do so, you need to install aws-cli. You can find the aws-cli documentation in this link.
Exploit
Once installed the program, it must be configured running the following command (It doesn't matter what you write).
Then, in order to upload a PHP reverse shell file you need to run the following command (Must be edited before uploading it) :
The cp parameter is to copy and --endpoint-url specify the bucket where the command will be executed.
After that, you need to put a listening port with netcat and access to the following direction
Privilege Escalation 1
Before becoming the user roy , I think it is mandatory to upgrade our shell.
To do so you need to write the following commands:
No we are able to use Ctrl+c, Ctrl+L and the keyboard arrows.
Coming back to the machine, we have read permissions in the roy's folder, where there is a folder named project. Having a look inside there is a php file with information about a dynamo data base (Amazon DynamoDB is a NoSQL database).
This database is listing in the 4566 port, using netcat we can retrieve all listening ports.
The port 53 corresponds to a DNS service, 22 to SSH, 80 to Apache, 35109 no clue XD. In order to access to ports 8000 and 4566 from our kali machine I am using socat.
To upload socat you need to execute these commands.
Thanks to socat we are able to redirect all the incoming data from port 4445 to 4566 and we can do the same for port 8000 with port 4446.
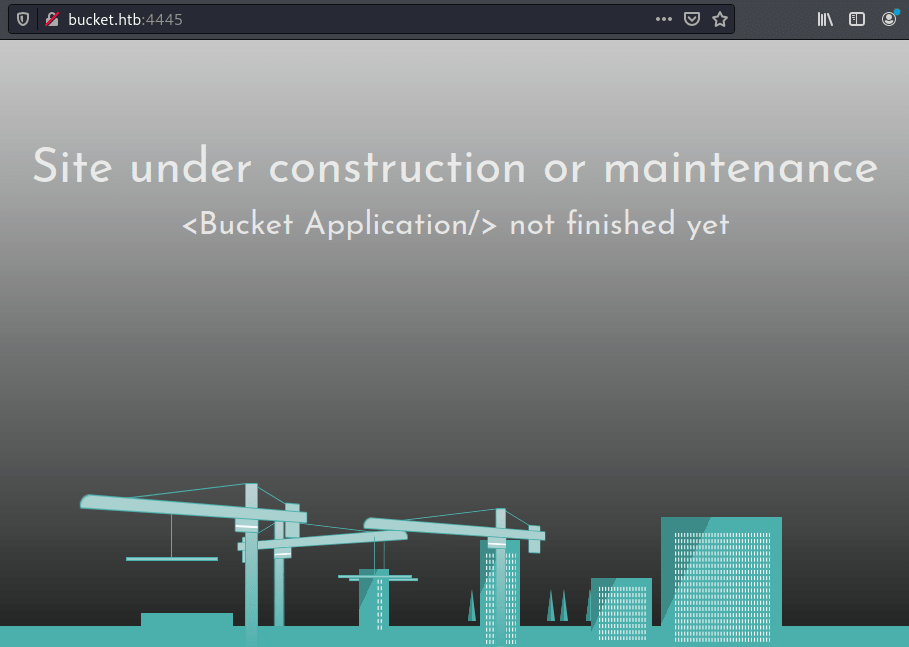
For one side, accessing to http://bucket.htb:4445/ from our kali machine we get this website under construction.
From the other site, using aws cli we can get retrieve all the tables int the site's dynamo database.
Then, we can get all the information inside the users table.
With try and error, the password n2vM-<_K_Q:.Aa2 is also used by roy to login to the machine.
Privilege Escalation 2
Now, we can access to the directory bucket-app located in /var/www/.
Inside the index.php file there is the following php code.
What the code does is to handle post requests with the name parameter "action" and the value get_alerts, then takes all rows with title "Ransomware" from the table alerts of the dynamoDB. Finally, for each row creates a random HTML file with the contents of the columnc data from the alerts, creating a PDF file in the files directory named as resuld.pdf using p4dml_demo.jar.
PD4ML is a Java library, which makes possible to create PDF documents from Java and JSP applications using HTML as template language.
Looking into the PD4ML documentation there is an HTML tag <pd4ml:attachment\> which embeds external resource as PDF attachment.
In order to retrieve the user flag, you need to write an script to do all the following tasks as soon as possible; because there is a cron job which erase everything from the database and the files folder.
The script is the following.
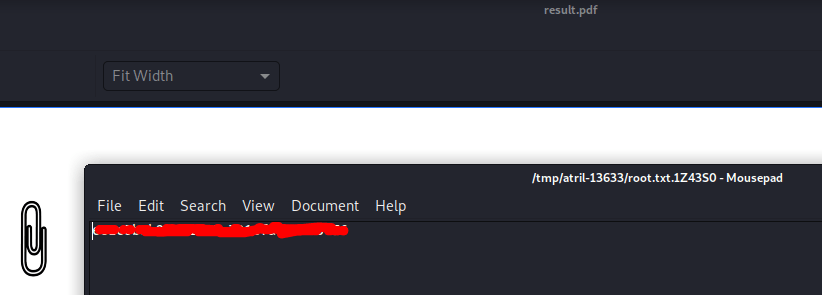
Finally, you must execute the script inside the box, download the resulting pdf, open it and click in the image and obtain the root's flag.