BountyHunter - [HTB]
![Cover Image for BountyHunter - [HTB]](/assets/images/blog/BountyHunter-htb/BountyHunter.png)

Introduction
BountyHunter is an easy linux machine from HackTheBox where the attacker will have to find an XXE injection on a web form, for obtaining the user credentials, and execute code on a ticketing program due to improper input validation.
Enumeration
As always, let's start finding all opened ports in the machine with nmap.
Then, we continue with a deeper scan of every opened port, getting more information about each service.
Having a look at port 80 there is static web page with a portal link.
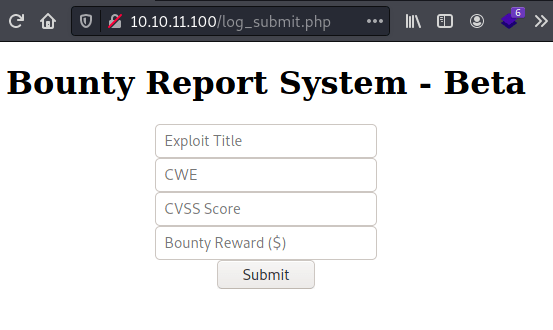
In the portal page there is a text pointing to a bounty tracker ("Portal under development. Go here to test the bounty tracker."), where appears an html form.
Using burpsuite we can intercept its content that is encoded in base64.
Once the decoded appears an xml structure.
Exploitation
Through XXE injection we can retrieve files from the remote system, like the following.
Sending the previous xml code in base64 allow us to retrieve the users in the system.
Thanks to gobuster we can discover new hidden files like db.php.
With the same technique as before we can obtain its content.
It turns out that we can access to the machine as the user development with the database password through SSH.
Privilege Escalation
The user "development" is able to execute the following python script as root.
Basically, the script asks for an .md file with the following lines and containing a number which module of 7 is equals to 4 .
Nevertheless, there is a vulnerability in the validation number, because it uses the function eval executing everything that is in the ticket code.
Hence we can create the following ticket, gaining a shell as root.