AWS Red Team Expert (ARTE) - HackTricks


Introduction
On February 21, 2026, I successfully achieved the AWS Red Team Expert (ARTE) certification by HackTricks. Following my tradition with previous certifications, this review aims to provide a cohesive and unified overview of the course structure, lab environment, and exam experience, along with practical tips for those looking to conquer this AWS-focused challenge.
What to expect from the ARTE Certification
The ARTE certification is a comprehensive AWS-focused penetration testing course designed to take students from basic cloud concepts like AWS services and its components to teach the Pentesting & Red Team methodology. It covers the core AWS pentesting methodology, diving into over 20 common services and exploring techniques for enumeration, privilege escalation, and persistence.
The target audience, it is primarily aimed at Red Team professionals looking to audit AWS environments.
Before starting the course
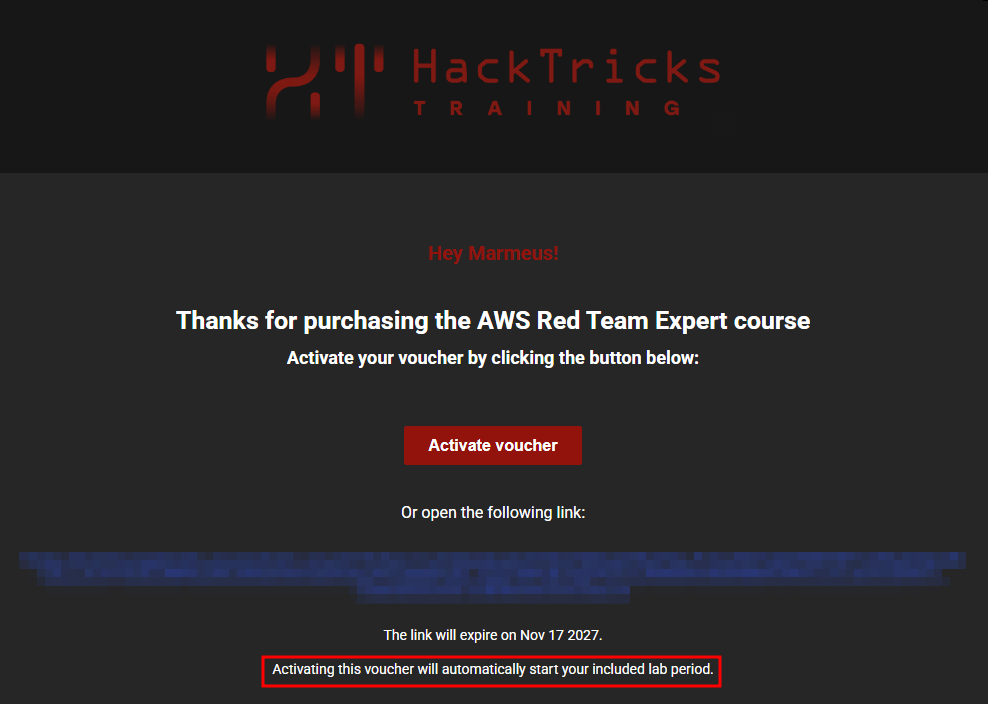
When you purchase the course, you receive an activation voucher. It is crucial to plan your start date carefully.
- The 60-Day Timer: The moment you purchase the course, you will receive an email like the following with the link to activate your course. Once activated, a 60-day countdown for lab access begins. Which means that both the laboratory environments and the course materials are activated at the same time upon voucher redemption (You can not access the course materials before activating the labs), and because the labs are time-limited, those balancing the course with a full-time job will likely require the full 60 days to complete the curriculum.
- Sequential Activation: If you purchase multiple HackTricks courses, do not activate them simultaneously, as the timers for both will run concurrently. If you have already done that, reach training support ASAP to disactivate any of the courses.
- Course Materials: You do not need deep prior AWS knowledge, but reviewing the syllabus beforehand to understand services like IAM, S3, Lambda, and Cognito will help you jump directly into the "hacking" portions. Current AWS Services explained in the course:
- IAM - Identity Access Management
- STS - Security Token Service
- KMS - Key Management Service
- Secrets Manager
- S3 - Simple Storage Service
- EC2 - Elastic Cloud Computing
- Lightsail
- Lambda
- API Gateway
- EFS - Elastic File System
- RDS - Relational Database Service
- DynamoDB
- ECR - Elastic Container Registry
- ECS - Elastic Container Service
- Elastic Beanstalk
- CodeBuild
- SQS - Simple Queue Service
- SNS - Simple Notification Service
- Cognito
- Step Functions
- EventBridge Scheduler
The labs
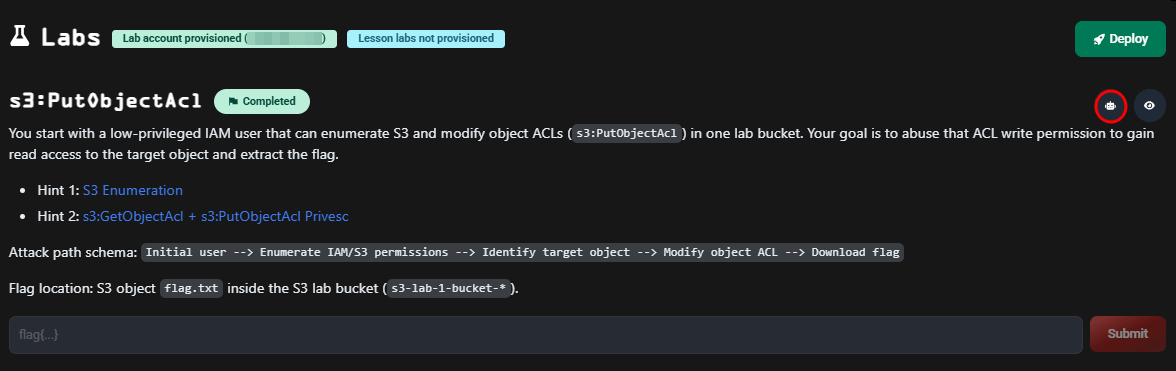
The heart of ARTE lies in its 50+ hands-on labs, where you can put in practice the knowledge stored at Cloud HackTricks Wiki, the labs range from simple 15-minute tasks to complex multi-hour challenges. Early labs focus on specific misconfigurations where you typically escalate privileges to retrieve a flag from Secrets Manager. The final labs focus on building the methodology that you will use during a real engagement.
To help students navigate these challenges, the course provides multiple support alternatives:
Integrated AI Chatbot: By far the best resource of the course, for each lab you can ask any doubt, guidance or errors you might encounter.
As an example you can use the following prompt:
Lab Walkthroughs: Detailed guide about how to solve the lab, though these are restricted to a total of five downloads per course. I recommend you to use them in the labs: Whitebox 2-1, Black box (I), Black box (II), Black box (III).
Discord: If despite all of that, your questions are not been solved, you can always ask in the Discord channel or open a ticket support.
To master the course methodologies and ensure exam readiness, I highly recommend prioritizing the White and Black Box labs. These scenarios provide the perfect environment to validate your toolset; identifying and troubleshooting any technical issues here will prevent unwelcome surprises or tool failures during the actual exam.
The Exam Experience
The exam is a 100% hands-on, real-world scenario where you must discover credentials, and escalate privileges and expand across the AWS environment within a 12-hour window with the objective of finding the three hidden flags (No report needed). Beyond the traditional route, the exam offers a 'contribution credit.' By providing a valid Pull Request to the Hacktricks Cloud GitHub repository that introduces new AWS exploits or techniques, you can successfully pass with one fewer flag than required.
As a real engagement, the exam is none linear, you may not find the flags in order, forcing you to take good notes about all the information you have recovered during the enumeration phase, because you are going to visit it. You might also get overwhelmed for the huge amount of information you are going to see. Remember that the labs provided the complete roadmap for success; so try to avoid rabbit holes.
My own exam started on a rough note. I was quite ill and hadn't slept the night before, which naturally led to some early-morning brain fog. I spent the first two hours stuck on a simple oversight that, in any other circumstance, would have been obvious. However, once I regained my composure and spotted the error, things moved quickly. I secured the first flag, and the final two followed just two hours later. This experience proved to me that the 12-hour window is more than generous. The exam isn't designed to trap you in endless rabbit holes or force a failure; it’s a fair challenge that rewards a clear head and the techniques you’ve already practiced.
Success Strategy and Tips
Everything it is documented in the Cloud HackTricks Wiki, but it is a good practice to create a list of most used commands, enumeration commands, filters and observations you find useful during the labs. This personal cheat sheet will be your most effective tool during the pressure of the exam. You can also check my own AWS Enumeration CheatSheet.
The exam follows a logical, cyclical methodology. Keep this loop in mind to stay on track:
- Analyse the entry vector to successfully retrieve initial AWS credentials.
- Map the effective permissions of the compromised principal to understand your current scope.
- Enumerate AWS resources accessible under your current permissions.
- Identifying misconfigured IAM policies or trust relationships that allows you to escalate privileges or lateral movement.
- Exploit the identified vulnerability to gain broader access.
- Repeat the process (Return to Step 2) with your newly acquired principal.
I also found this fork of aws-enumerator incredibly helpful. It quickly identifies which services a user can enumerate, saving you from tedious manual checks when dealing with principals tied to numerous services. Note that it specifically checks for "read" capabilities, so you will still need to manually verify update, delete, or create permissions once you have your targets.
Conclusion
Is the ARTE certification worth it? If you are serious about cloud security and red teaming, the answer is a resounding yes. While the price point is over €1,000, you can always ask your company to purchase it for you, but students have a 20% discount to make the investment even more accessible.
Finally, if you find ARTE too daunting or expensive, HackTricks offers the AWS Red Team Apprentice (ARTA), created to build a strong foundation in cloud security concepts and attack fundamentals.